Jennifer Marsh - Page 2
With a background in software engineering, Jennifer Marsh has a passion for hacking and researching the latest cybersecurity trends. Jennifer has contributed to TechCrunch, Microsoft, IBM, Adobe, CloudLinux, and IBM. When Jennifer is not programming for her latest personal development project or researching the latest cybersecurity trends, she spends time fostering Corgis.
by Jennifer Marsh | Apr 18, 2024 | Email Scams, Network Security, Phishing & Email Spam |
Cybercriminals use a variety of methods for initial access to victims’ networks and tactics are constantly changing. Ransomware groups are increasingly targeting boundary devices such as routers, firewalls, and the virtual private networks that sit between the Internet and business networks, with the first quarter of this year seeing a decline in attacks exploiting vulnerabilities for initial access. According to the ransomware remediation firm Coveware, remote access is now favored by ransomware groups. In Q1, 2024, Remote Desktop Protocol (RDP) compromise was the most commonly identified initial attack vector.
Phishing is still commonly used for initial access, although there has been a fall in phishing-based attacks by ransomware groups; however, it is common for ransomware groups to chain email phishing with RDP compromise and the exploitation of software vulnerabilities for more impactful attacks. What is clear from the data is threat actors are conducting more sophisticated attacks and are taking steps to cover their tracks. Coveware reports that the initial access vector was unknown in around 45% of attacks.
While ransomware groups may be concentrating on non-email attack vectors, phishing attempts by cybercriminals have increased significantly over the past year. A new analysis by researchers at the antivirus company Kaspersky found that phishing attempts increased by 40% in 2023, with threat actors increasingly using messaging apps such as Telegram in their attacks as well as social media networks.
Phishing is also becoming more sophisticated and increasingly personalized. There is growing evidence that threat actors are using generative artificial intelligence engines to craft new lures to use in their campaigns, especially spear phishing attacks. The near-perfect messages that GenAI creates can make it difficult for end users to distinguish phishing emails from genuine communications.
The problem for many businesses is threat actors are constantly evolving their tactics and are conducting increasingly sophisticated campaigns, yet email security defenses are not maintaining pace. Many Microsoft 365 users find that while Microsoft Defender and EOP block a good percentage of spam emails and many phishing threats, more sophisticated threats are not detected. Having a cybersecurity solution such as PhishTitan augments Microsoft 365 defenses and ensures sophisticated threats are blocked. For every 80,000 emails received, PhishTitan catches 20 unique and sophisticated phishing attacks that Microsoft’s expensive E5 premium security misses.
PhishTitan helps with post-delivery remediation, allowing security teams to rapidly remove phishing threats from the email system when a threat is reported, adds a banner to emails warning users about suspicious messages, and rewrites URLs to show the true destination to combat spoofing. The solution also includes time-of-click protection to combat phishing links that are weaponized after delivery, and AI- & LLM-driven anti-phishing analysis to identify previously unseen phishing threats.
The use of malware in email campaigns is also increasing. In 2023, 6.06 billion malware attacks were identified worldwide, up 10% from the previous year, with loaders, information stealers, and remote access trojans (RATs) the most common malware threats. While signature-based detection mechanisms once served businesses well, the rate at which new malware variants are released means many threats are not detected as malware signatures have yet to be uploaded to antivirus defenses. The key to blocking these zero-day threats is email sandboxing.
An email sandbox is an isolated environment where messages that meet certain criteria are sent after scans by antivirus engines have shown the messages to be free from malware. In the sandbox, messages are subjected to deep inspection to identify malware from its behavior rather than signature. Many malware variants have been developed to resist analysis or pass sandbox checks, such as delaying malicious actions for a set period. A slight disadvantage of email sandboxing is a small delay in email delivery, but it is important to ensure that messages are analyzed in detail and anti-sandboxing capabilities are defeated. There are, however, ways to get sandbox protection while minimizing the impact on the business.
Whether you are looking for a gateway spam filter or a hosted spam filter to improve protection against email threats or advanced phishing protection, TitanHQ can help. Give the team a call today for detailed information on TitanHQ products and advice on the most effective solutions to meet the needs of your business. You can take advantage of the free trials of TitanHQ products, which are provided with full support to help you get the most out of the trial.
by Jennifer Marsh | Apr 17, 2024 | Email Scams, Phishing & Email Spam |
A phishing campaign has been running since late March that tricks people into installing a new version of the remote access trojan, JSOutProx. JSOutProx was first identified in 2019 and is a backdoor that utilizes JavaScript and .NET that allows users to run shell commands, execute files, take screenshots, control peripheral devices, and download additional malware payloads. The malware is known to be used by a threat actor tracked as Solar Spider, which mostly targets financial institutions in Central Europe, South Asia, Southeast Asia, and Africa, with the latest version of the malware also being used to target organizations in the Middle East.
The malware has mostly been used on banks and other financial institutions. If infected, the malware collects information about its environment and the attackers then download any of around 14 different plug-ins from either GitHub or GitLab, based on the information the malware collects about its operating environment. The malware can be used to control proxy settings, access Microsoft Outlook account details, capture clipboard content, and steal one-time passwords from Symantec VIP.
Like many other remote access trojans, JSOutProx is primarily delivered via phishing emails. A variety of lures have been used in the phishing emails but the latest campaign uses fake notifications about SWIFT payments in targeted attacks on financial institutions and MoneyGram payment notifications in attacks on individuals, which aim to trick the recipients into installing the malware.
The latest campaign uses JavaScript attachments that masquerade as PDF files of financial documents contained in .zip files. If the user attempts to open the fake PDF file, the JavaScript is executed deploying the malware payload. The main aim of the campaign is to steal user account credentials, gather sensitive financial documents, and obtain payment account data, which can either be used to make fraudulent transactions or be sold to other threat actors on the dark web. Email accounts are often compromised which can be leveraged in Business Email Compromise (BEC) attacks to steal funds from clients. According to VISA, “The JSOutProx malware poses a serious threat to financial institutions around the world, and especially those in the AP region as those entities have been more frequently targeted with this malware.”
Since phishing is the main method of malware delivery, the best defense against attacks is advanced anti-spam software and end-user security awareness training. JSOutProx malware is able to bypass many traditional anti-spam solutions and anti-virus software due to the high level of obfuscation. The best defense is an anti-spam solution with AI and machine learning capabilities that can identify the signs of malicious emails by analyzing message headers and message content to determine how they deviate from the emails typically received by the business and also search for the signs of phishing and malware delivery based on the latest threat intelligence.
To identify the malicious attachments, an anti-spam solution requires sandboxing. Any messages that pass standard antivirus checks are sent to the sandbox where behavior is analyzed to identify malicious actions, rather than relying on malware signatures for detection. SpamTitan can extract and analyze files in compressed archives such as .zip and .rar files and in recent independent tests, SpamTitan achieved a phishing catch rate of 99.914%, a malware catch rate of 99.511%, with a false positive rate of 0.00%. SpamTitan from TitanHQ is delivered as either a hosted anti-spam service or an anti-spam gateway that is installed on-premises on existing hardware. SpamTitan has been developed to be easy to implement and use and meet the needs of businesses of all sizes and managed service providers.
Phishing emails target employees so it is important to teach them how to identify phishing emails. Due to the fast-changing threat landscape, security awareness training should be provided continuously to the workforce, and phishing simulations should be conducted to give employees practice at identifying threats. SafeTitan from TitanHQ can be used to easily create effective training programs that run continuously throughout the year and keep employees up to date on the latest threats and tactics, techniques, and procedures used by malicious actors. SafeTitan also delivers relevant training in real-time in response to security mistakes and phishing simulation failures. Check out these anti-spam tips for further information on improving your defenses against phishing and get in touch with TitanHQ for more information on SpamTitan email security and the SafeTitan security awareness training platform.
by Jennifer Marsh | Apr 16, 2024 | Email Scams, Phishing & Email Spam |
One of the most effective ways of getting employees to open malicious emails is to make the emails appear to have been sent internally and to use a lure related to salaries, as is the case with a recently identified campaign that is used to deliver a Remote Access Trojan called NetSupport RAT.
The campaign was first identified by researchers at Perception Point who intercepted an email that appeared to have been sent by the accounts department and purported to be a monthly salary report. The recipient is told to review the report and get back in touch with the accounts department if they have any questions or concerns about the data. Due to the sensitive nature of the data, the salary chart is in a password-protected document, and the employee is told to enter the password provided in the email if the enable editing option is unavailable. The user is prompted to download the .docx file, enter the password, and then click enable editing, after which they need to click on the image of a printer embedded in the document. Doing so will display the user’s salary graph.
The document uses an OLE (Object Linking and Embedding) template which is a legitimate tool that allows linking to documents and other objects, in this case, a malicious script that is executed by clicking on the printer icon. This method of infection is highly effective, as the malicious payload is not contained in the document itself, so standard antivirus scans of the document will not reveal any malicious content. If the user clicks the printer icon, a ZIP archive file will be opened that includes a single Windows shortcut file, which is a PowerShell dropper that will deliver the NetSupport RAT from the specified URL and execute it, also adding a registry key for persistence.
NetSupport RAT has been developed from a legitimate remote desktop tool called NetSupport Manager which is typically used to provide remote technical support and IT assistance. The malware allows a threat actor to gain persistent remote access to an infected device, gather data from the endpoint, and run commands. While the use of OLE template manipulation is not new, this method has not previously been used to deliver the NetSupport RAT via email.
The threat actor uses encrypted documents to deliver the malware to evade email security solutions, and the emails are sent using a legitimate email marketing platform called Brevo, which allows the emails to pass standard reputation checks. This campaign is another example of how threat actors are increasing the sophistication of their phishing campaigns and how they can bypass standard email security defenses, including Microsoft’s anti-malware and anti-phishing protections for Microsoft 365 environments.
While the lure and the steps users are taken through are reasonable, there are red flags at various stages of the infection process where end users should identify the email as potentially malicious. In order for that to happen, end users should be provided with regular security awareness training. TitanHQ offers a comprehensive security awareness training platform called SafeTitan, which includes training modules to teach employees how to identify the red flags in email campaigns such as this. The platform also includes a phishing simulator, that allows these types of emails to be sent to employees to test the effectiveness of their training. If they fail a simulation, they are immediately shown where they missed the opportunity to identify the threat, with relevant training generated instantly in real time.
Sophisticated phishing attacks require sophisticated anti-phishing defenses to block these emails before they reach end users’ inboxes. While standard antivirus checks can block many malicious payloads, behavioral analysis of attachments and files is essential. TitanHQ’s cloud-based anti-spam service – SpamTitan – performs a barrage of front-end checks of messages including reputation checks and Bayesian analysis, machine-learning algorithms analyze messages for potentially malicious and phishing content, scan attachments with twin antivirus engines, and messages are sent to a sandbox for deep analysis. In the sandbox, malicious behavior can be identified allowing even sophisticated phishing emails to be blocked by the cloud spam filter.
A hosted email filter is often the best fit for businesses, although SpamTitan is available as a gateway spam filter. The TitanHQ team will be happy to listen to your requirements and suggest the best option to meet your needs. Give the team a call today to find out more about improving your email defenses against sophisticated phishing and malware distribution campaigns and how to provide more effective security awareness training.
by Jennifer Marsh | Apr 15, 2024 | Email Scams, Phishing & Email Spam |
A sophisticated phishing campaign has been detected that is being used to deliver a variety of Remote Access Trojan (RAT) malware, including Venom RAT, Remcos RAT, and NanoCore RAT, as well as a stealer that targets cryptocurrency wallets. The campaign uses email as the initial access vector with the messages purporting to be an invoice for a shipment that has recently been delivered. The emails include a Scalable Vector Graphics (SVG) file attachment – an increasingly common XML-based vector image format.
If the file is executed, it will drop a compressed (zip) file on the user’s device. The zip file contains a batch file that has been created with an obfuscation tool (most likely BatCloak) to allow it to evade anti-virus software. If not detected as malicious, a ScrubCrypt batch file is unpacked – another tool used to bypass antivirus protections – which delivers two executable files that are used to deliver and execute the RAT and establish persistence. This method of delivery allows the malware to evade AMSI (Antimalware Scan Interface) and ETW (Event Tracing for Windows) antivirus protections.
One of the primary payloads is Venom RAT, which establishes a connection with its command and control (C2) server, transmits sensitive information gathered from the compromised device and runs commands from its C2 server. Venon RAT can download additional modules and malware payloads, including a stealer malware that targets folders associated with cryptocurrency wallets and applications including Atomic Wallet, Electrum, Exodus, Foxmail, and Telegram.
The sophisticated nature of this campaign and the obfuscation used to hide the malicious payloads from traditional antivirus software demonstrates the need for advanced email defenses and end-user training. Email security solutions that rely on malware signatures are easily bypassed, which is why it is important to use an anti-spam solution that incorporates sandboxing for blocking malware and AI and machine learning capabilities to identify malicious emails.
SpamTitan uses AI and machine learning algorithms to detect phishing emails that other solutions miss – including Microsoft’s basic and advanced anti-phishing mechanisms for Microsoft 365. SpamTitan includes Sender Policy Framework (SPF), SURBL’s, RBL’s, Bayesian analysis, and more, and the machine learning algorithms can detect email messages that deviate from the typical messages received by a business and can identify header anomalies, address spoofing, and suspect email body content. All inbound messages are subjected to standard and advanced malware checks, including scans using twin anti-virus engines and email sandboxing. If all anti-malware checks are passed, including unpacking and analyzing compressed files, messages are sent to the sandbox for behavioral analysis.
In the cloud-based sandbox, malicious actions are identified such as attempts to deliver additional files as is commonly seen in multi-stage attacks and C2 calls. In recent independent tests (Virus Bulletin), SpamTitan achieved a phishing catch rate of 99.914%, a malware catch rate of 99.511%, and a false positive rate of 0.00%. With phishing attacks becoming more sophisticated you need to have sophisticated defenses. With email security protection provided by SpamTitan and security awareness training delivered using TitanHQ’s award-winning SafeTitan security awareness training and phishing simulation platform you will be well protected from email-based attacks.
Give the TitanHQ team a call today to find out more about how you can improve your defenses against email-based attacks with sandboxing technology and how to add more layers to your defenses to block the full range of cyberattacks.
by Jennifer Marsh | Apr 14, 2024 | Email Scams, Phishing & Email Spam |
A relatively new malware variant dubbed Latrodectus is increasingly being used to gain initial access to business networks. Latrodectus is the Latin for Widow spiders, but the malware was so named because of a line in the code that mentions the word. The malware was first detected in November 2023, and detections have been increasing ever since, especially since February 2024. Analyses of Latrodectus malware have revealed strong similarities with the IcedID remote access trojan (RAT) and malware loader, and the infrastructure that supports the malware was previously used in IcedID campaigns. That strongly suggests that Latrodectus malware is the successor of IcedID and was most likely developed by the same threat actor.
Latrodectus malware is primarily a malware downloader and backdoor that is used to deliver a range of different payloads and execute commands on an infected device. Latrodectus is a modular malware capable of adapting to different environments, has extensive capabilities, is stealthy, and can bypass many cybersecurity solutions. The malware checks for the presence of debuggers, has anti-sandbox capabilities and encrypts communications with its C2 server. The malware gains persistence via auto-run keys and scheduled tasks.
Latrodectus malware is believed to be used by highly capable threat actors that specialize in gaining initial access to networks to sell on to other threat actors such as ransomware groups. The malware is primarily distributed in phishing emails, with the detected emails so far using Microsoft Azure and Cloudflare-themed lures, with either PDF file attachments or URLs embedded in emails. The malware has also been identified as being distributed via contact form spam.
If the PDF files are opened, the user is told that the document has been uploaded to the Microsoft Azure Cloud and they are required to download it. The user is then directed to a fake Cloudflare security check that adds legitimacy but also prevents email security solutions from following the link and prevents in-depth analysis in sandboxes. If the user proceeds, they will download a JavaScript file that appears to be the document indicated in the PDF file. If the file is executed, a script runs that downloads an MSI installer, which drops and executes the Lactrodectus DLL.
Due to the evasive capabilities of the malware, standard email security solutions are unlikely to identify the phishing emails as malicious, and even email sandboxing checks may be passed. An advanced anti-spam service is required that incorporates AI- and machine learning capabilities to identify the malicious nature of the email. SpamTitan Plus is an advanced email security solution with the highest coverage of anti-phishing feeds of any product on the market, incorporating coverage of 100% of all current market-leading anti-phishing feeds. The superior threat intelligence fed into the system and massive clickstream traffic from more than 600 million users and endpoints ensure the URLs used to deliver malware are detected and blocked. The machine learning capabilities of SpamTitan Plus allow the solution to predict and block novel phishing campaigns, including phishing attacks that use personalized URLs when targeting individuals. URLs are followed and are rewritten to identify the destination, and the solution features time-of-click protection to identify and block URLs that are weaponized after delivery.
As an additional protection, businesses should consider a web filtering solution. WebTitan from TitanHQ protects against the web-based component of cyberattacks. While SpamTitan Plus can block attempts to visit URLs embedded in emails and email attachments, WebTitan will block visits to URLs from general web browsing, redirects from malvertising, and non-email communications. WebTitan can also be configured to block downloads of files from the Internet associated with malware – JavaScript files for instance.
End-user training is also important to teach cybersecurity best practices and eliminate risky behaviors. SafeTitan is a comprehensive security awareness training platform with hundreds of training modules that can be easily configured to create and automate training courses relevant to individuals and user groups. The platform includes a phishing simulator for conducting realistic phishing simulations, using messages that have been created from genuine phishing attacks. The platform is the only behavior-driven security awareness training platform that delivers training in real time in response to simulation failures and security mistakes.
As cyber threats increase in sophistication, multiple cybersecurity solutions are required to provide multi-layered protection. TitanHQ solutions will ensure you are well protected from ever-changing cyber threats and sophisticated phishing and malware attacks.
by Jennifer Marsh | Mar 31, 2024 | Industry News, Network Security |
TitanHQ has added a new auto-remediation feature to its Microsoft 365 anti-phishing solution, PhishTitan, to better meet the needs of managed service providers (MSP) and M365 administrators.
According to Statista, more than two million companies worldwide use Microsoft 365, including more than 1.3 million in the United States. Given the number of companies that use Microsoft 365, it is naturally a big target for cybercriminals and nation-state actors. If threat actors can steal M365 credentials, they can access a treasure trove of valuable business data and gain a foothold for more extensive and damaging attacks. Microsoft offers protection against spam, phishing, malware, and business email compromise attacks, but the best level of protection is only available with its costly E5 premium license, which is prohibitively expensive for many small businesses. Even companies that can afford this costly license do not get cutting-edge protection against phishing and BEC attacks.
To consistently block sophisticated phishing attempts, BEC attacks, and zero-day threats, businesses need more advanced protection than Microsoft can offer, and many turn to PhishTitan from TitanHQ – an integrated Cloud Email Security Solution (ICES) that provides cutting-edge protection against the most damaging, sophisticated phishing threats, BEC, account takeover, VIP impersonation, and zero-day attacks. In recent Virus Bulletin Tests, the engine that powers PhishTitan achieved an exceptional spam catch rate of 99.983%, a malware catch rate of 99.511%, and a phishing catch rate of 99.914%, with zero false positives. PhishTitan was shown to outperform Microsoft’s highest level of protection. For every 80,000 emails received, PhishTitan blocks 20 more unique and sophisticated attacks than Microsoft’s E5 filtering option.
The latest update to PhishTitan adds a new auto-remediation feature, which allows administrators to tailor the management of malicious emails based on the severity level. When a threat is detected, a banner is added to the email that warns the user about the threat; however, auto-remediation allows administrators to apply rules to deal with these messages according to the threat level, such as automatically diverting the emails to the junk folder. This feature acts like a virtual SOC and minimizes the risk to end users, especially individuals who tend to ignore email banners.
Auto-remediation is just one of the new features PhishTitan has gained since its launch. PhishTitan has also received an update to protect users from the growing threat of QR code phishing attacks (QRishing). QR codes are problematic for many anti-spam and anti-phishing solutions, as they cannot decipher the URLs in QR codes and check the destination URL, which is why cybercriminals are increasingly using QR codes in their phishing emails. PhishTitan can analyze the URLs encoded in QR codes, assess the risk, and notify end users.
PhishTitan also supports allow-listing, which administrators can use to automatically white-list trusted senders to make sure that their emails are always delivered, and notifications can also be fed into Microsoft Teams. Since administrators can spend a considerable amount of time in the application, a dark mode has been added to improve the user experience, and many more updates are planned and will be rolled out soon.
“We are excited to introduce Auto Remediation, QR code protection, and many additional powerful new features to our valued customers. At TitanHQ, we collaborate closely with partners to develop tailored solutions addressing critical customer IT security challenges,” said TitanHQ CEO, Ronan Kavanagh. “PhishTitan provides MSPs with an unmatched value proposition, featuring effortless deployment and lucrative recurring revenue streams, ultimately delivering a positive return on investment.”
If you want to improve protection against email threats or have any questions about PhishTitan, give the TitanHQ team a call. TitanHQ also offers award-winning DNS filtering, spam filtering, email encryption, email archiving, security awareness training, and phishing simulation solutions, all of which are available on a free trial.
by Jennifer Marsh | Mar 29, 2024 | Phishing & Email Spam, Spam Software |
TitanHQ has claimed a Top 3 position in a recent Virus Bulletin email security test, achieving an exceptional 99.98% spam catch rate and 99.91% phishing catch rate for the cutting-edge filtering engine that powers the SpamTitan (email security) and PhishTitan (phishing protection) solutions, earning TitanHQ the prestigious VBSpam+ certification for the products.
Virus Bulletin is a security information portal and independent testing and certification body that has earned a formidable reputation within the cybersecurity community for providing security professionals with intelligence about the latest developments in the global threat landscape. Virus Bulletin conducts regular tests of security solutions to determine how well they perform at detecting and blocking threats, and for more than 20 years has been benchmarking cybersecurity solutions. Virus Bulletin’s public certifications cover all types of security threat protection, including anti-spam and anti-phishing solutions for enterprises.
In the Q1, 2024 tests, Virus Bulletin assessed nine comprehensive email security solutions, including TitanHQ’s email security suite which comprises SpamTitan and PhishTitan. The email security solutions were put to the test to assess how effective they are at blocking unsolicited and unwanted spam emails and malicious messages of all types. TitanHQ’s solutions achieved exceptional scores at blocking spam and phishing emails, with a spam catch rate of 99.983%, a malware catch rate of 99.511%, and a phishing catch rate of 99.914% with zero false positives. The final score for the Q1, 2024 tests was 99.983, cementing TitanHQ’s position as a leading provider of anti-phishing and anti-spam solutions for managed service providers and businesses.
“This test reaffirms TitanHQ’s unrivaled prowess in spam and phishing protection—we stand as the first choice for combating phishing attempts and spam infiltrations,” said Ronan Kavanagh, CEO at TitanHQ. “Our customers need not settle for anything less. With TitanHQ solutions, they receive unparalleled defense against phishing and spam and experience minimal false positives.
While there are many ways that cybercriminals and nation state actors breach company networks and gain access to sensitive data, phishing is the leading initial access vector. Despite phishing being such a prevalent threat, many businesses lack security solutions that can consistently identify and block these malicious messages, which results in costly compromises, data breaches, and devastating ransomware attacks. According to one study by researchers at CoreView on 1.6 million Microsoft 365 users, 90% lacked essential security protections that can combat threats such as phishing.
While Microsoft has security solutions that can block spam and phishing emails, they are unable to block advanced phishing threats. PhishTitan has been developed to work seamlessly with M365 and catch the phishing threats that M365 misses. Even Microsoft’s most advanced anti-phishing protection, the costly E5 premium security offering, fails to block many advanced threats. Testing has shown that for every 80,000 emails received, PhishTitan identifies and blocks 20 unique, sophisticated phishing attempts that Microsoft’s top solution misses, and many businesses cannot afford Microsoft’s top level of protection and are reliant on its basic anti-spam and anti-phishing protection.
If you want to improve your defenses against phishing and malware and block more spam emails, give the TitanHQ team a call and ask about SpamTitan and PhishTitan. Both email filtering solutions are available on a free trial, so you can put them to the test and see for yourself the difference they make.
by Jennifer Marsh | Mar 28, 2024 | Phishing & Email Spam |
A phishing campaign distributing StrelaStealer malware has expanded to Europe and the United States, with the attackers favoring the high-tech, finance, professional and legal services, manufacturing, government, energy, utilities, insurance, and construction sectors.
StrelaStealer malware was first identified in November 2022 and its primary purpose is to extract email account login credentials from popular email clients such as Microsoft Outlook and Mozilla Thunderbird, and exfiltrate them to its command-and-control server. StrelaStealer has previously been used to target companies in Spanish-speaking countries however, targeting has now been expanded to the United States and Europe, with attacks peaking in November 2023 and January 2023 with more than 500 attacks a day on companies in the United States and more than 100 attacks per day in Europe, according to tracking data from Palo Alto Networks Unit 42 team.
The campaign uses email as the initial access vector with the emails typically claiming to be an invoice. Early attacks used ISO file attachments that included a .lnk shortcut and an HTML file, which invoked the rundll32.exe process to execute the malware payload. The latest attacks use a different method, with .zip file attachments favored. These compressed files include Jscript files which, if executed, drop a batch file and base64-encoded file that decodes into a DLL file, which is executed using rundll32.exe to deploy the StrelaStealer payload.
Email sandboxing provides a vital layer of protection against malware, which can be difficult to detect using transitional signature-based email security solutions. Anti-virus solutions are generally signature-based, which means they can only detect known malware. Advanced email security solutions use sandboxing to analyze the behavior of files to identify and block novel malware threats. Suspicious files are sent to the sandbox for in-depth behavioral analysis. The control flow obfuscation technique used in this attack can make analysis difficult, even in sandboxed environments, with excessively long code blocks used that can result in timeouts when executed in some sandboxed environments. While sandboxing can delay email delivery, which is far from ideal for businesses that need to act on emails quickly, it is important to provide enough time to allow attachments to be fully analyzed, as StrelaStealer malware clearly demonstrates. The easiest way for businesses to sandbox email attachments is with SpamTitan Email Security.
StrelaStealer malware is actively evolving, and new methods are being developed to deliver the malware and evade security solutions. Combatting sophisticated phishing attacks such as this, requires a defense-in-depth approach to security, using multiple security solutions that provide overlapping layers of protection such as SpamTitan Email Security, PhishTitan phishing protection, and SafeTitan security awareness training. Give the TitanHQ team a call today for more information on affordable cybersecurity solutions that are easy to use and capable of blocking advanced phishing threats.
by Jennifer Marsh | Mar 27, 2024 | Phishing & Email Spam |
Phishing is one of the most common methods used to gain access to credentials; however, businesses are increasingly implementing multi-factor authentication (MFA) which adds an extra layer of protection and means stolen credentials cannot be used on their own to gain access to accounts. An additional authentication factor is required before access to the account is granted. While any form of MFA is better than none, MFA does not protect against all phishing attacks. There are several popular phishing-as-a-service (PhaaS) platforms that can steal credentials and bypass MFA including LabHost, Greatness, and Robin Banks. For a relatively small fee, any cybercriminal looking to compromise accounts can use the PhaaS platform and gain access to MFA-protected accounts.
A relatively new PhaaS platform has been growing in popularity since its discovery in October 2023 which has been causing concern in the cybersecurity community. Dubbed Tycoon 2FA, the PhaaS platform is being offered through private Telegram groups. Like many other PhaaS platforms, Tycoon 2FA uses adversary-in-the-middle (AiTM) tactics to steal MFA tokens, allowing access to be gained to accounts. The phishing kit uses at least 1,100 domains and has been used in thousands of phishing attacks.
Like most phishing attacks, initial contact is made with end users via email. The messages include a malicious link or a QR code. QR codes are popular with phishers as they communicate a URL to the end user and are difficult for email security solutions to identify as malicious. To ensure that the malicious URLs are not detected by security solutions, after clicking the link or visiting the website via the QR code, the user must pass a security challenge (Cloudflare Turnstile). The web page to which the user is directed targets Microsoft 365 or Gmail credentials. The user’s email address is captured and used to prefill the login page, and when the user enters their password it is captured and they are directed to a fake MFA page.
The phishing kit uses a reverse proxy server that relays the user’s credentials to the legitimate service being targeted in real-time and similarly captures the session cookie when the MFA challenge is passed. The user is unlikely to recognize that their account has been compromised as they are redirected to a legitimate-looking page when the MFA mechanism is passed. According to the researchers, many different threat actors have been using the kit for their phishing campaigns, with the Tycoon 2FA operators having received almost $395,000 in payments to their Bitcoin wallet as of March 2024. The price of the phishing kit is $120 for 10 days of usage which shows how popular the platform is with cybercriminals.
PhaaS platforms allow cybercriminals to conduct sophisticated attacks and bypass MFA without having to invest time and money setting up their own infrastructure they significantly lower the entry barrier for conducting MFA-bypassing phishing attacks. An advanced spam filtering service such as SpamTitan Plus will help to prevent malicious emails from reaching inboxes, and is an ideal spam filter for MSPs looking to provide the best level of protection for their clients. The SpamTitan suite of email security solutions combines phishing, spam, and antivirus filtering and independent tests show a spam block rate of 99.983% and a malware block rate of 99.51%.
PhishTitan from TitanHQ greatly improves protection against more advanced phishing campaigns such as those that use QR codes. Employees should be provided with regular security awareness training to help them identify and avoid phishing messages, and businesses should consider using phishing-resistant MFA rather than more basic forms of 2-factor authentication that use SMS or one-time passwords, which phishing kits such as Tycoon 2FA can easily bypass.
by Jennifer Marsh | Mar 27, 2024 | Phishing & Email Spam |
Business Email Compromise (BEC) attacks may not be as frequently encountered as phishing attacks but the losses to this type of attack are far greater. According to figures from the Federal Bureau of Investigation (FBI) Internet Crime Complaint Center (IC3), $2.9 billion was lost last year to BEC attacks – The second most expensive type of cybercrime.
BEC attacks usually involve impersonation, with the attacker posing as a trusted individual. Contact is established and the scammer tricks the victim into divulging sensitive company information or transferring a large sum of money. For instance, the scammer may pose as a contractor and request that bank details are changed for an upcoming payment. The scam is not usually detected until after the transfer has been made and the funds have been withdrawn from the attacker-controlled account.
BEC attacks can be difficult for email security solutions to identify, as the emails are often sent from a known and trusted email account that has been compromised in a phishing attack. BEC scammers research their targets and may have access to past conversations between the victim and the person they are impersonating and can therefore disclose information from past conversations in email exchanges to convince the target that they are who they claim they are. The scams may also be spread across multiple emails, with trust building during the exchanges.
One of the latest BEC campaigns to be identified involves the impersonation of U.S. government entities, such as the U.S. Department of Transportation, Department of Agriculture, and Small Business Association. Initial contact is made via email and a PDF attachment is sent that includes a QR code, which has links about fake bidding processes. The targeted individual is told to use the QR code to find out more information about the bidding process.
The PDF file explains that the QR code is included as complaints have been received that the bid button in the email does not work with some browsers and that the QR code will direct them to a document that should be downloaded as it is required to submit a bid. The emails and the PDF are crafted to appear to have been sent by the spoofed organization, and the website to which the user is directed resembles the official portal used by the spoofed government agency.
If the QR code is scanned, the user will be directed to a phishing site where they will be required to enter their Office 365 credentials, which will provide the attacker with access to their email account. Once access has been gained, the scammers can proceed to the next phase of the attack. They search the email account for messages related to banking or finance and use that information for their BEC attack and send messages to contacts that include fraudulent invoices or payment requests. The emails are sent from a trusted account, so the emails will likely be delivered and there is a good chance that the attack will be successful.
Security awareness training can help to raise awareness of the threat of these attacks with individuals involved in financial transactions in a company, and policies should be in place that require any requested change to banking information to be verified by phone using a previously verified phone number. It is also important to have an email security solution in place to block or flag potential BEC messages.
TitanHQ’s PhishTitan is an ideal choice. PhishTitan can identify and flag sophisticated phishing and BEC emails and can also read and follow the URLs encoded in QR codes. When a suspicious email is detected a banner is added to warn the user, and the emails can be auto-remediated and sent to the junk folder. PhishTitan improves Microsoft’s Office 365 spam filter. Independent tests by Virus Bulletin show the engine that powers T
itanHQ’s SpamTitan spam filter for Office 365 and the PhishTitan 0365 anti-phishing solution has a phishing catch rate of 99.914% with zero false positives. For every 80,000 emails received, PhishTitan identifies and blocks 20 unique, sophisticated phishing attempts that Microsoft’s top anti-phishing solution misses. The solution is also just a fraction of the cost of the average loss to a single BEC attack.
For more information about PhishTitan and how it can protect your business from advanced phishing and BEC attacks, give the TitanHQ team a call.
by Jennifer Marsh | Mar 26, 2024 | Industry News |
TitanHQ has announced it has signed a new partnership agreement with Equinox Technologies which will see TitanHQ’s cybersecurity solutions offered throughout Africa. Equinox Technologies is a pan-African, tech-enabled, business service provider that provides a range of services to more than 40 countries in Africa from its operational hubs in Abuja, Nigeria; Cape Town, South Africa; Nairobi, Kenya; and Tunis, Tunisia. Equinox Technologies helps businesses of all sizes expand and invest seamlessly across international borders through the provision of business-critical administrative, security, and compliance support. The services provided include enterprise mobility management, software engineering, IT operations, digital services, and cybersecurity.
The strategic alliance with TitanHQ will see Equinox Technologies act as a value-added distributor, packaging TitanHQ solutions with other products and services to meet its clients’ cybersecurity and compliance needs and better protect them from the rapidly evolving landscape of cyber threats. Under the new agreement, Equinox Technologies will become the exclusive distributor of TitanHQ solutions in Africa, further expanding TitanHQ’s global footprint.
Equinox Technologies will help its clients improve email security by offering TitanHQ’s cloud-based anti-spam service (SpamTitan), phishing protection solution (PhishTitan), and email encryption solution (EncryptTitan), protection from web-based threats through TitanHQ’s DNS filtering solution (WebTitan), threats that target employees with TitanHQ’s security awareness training and phishing simulation platform (SafeTitan); and help them meet their email retention and compliance obligations through TitanHQ’s email archiving solution (ArcTitan).
“This collaboration signifies Equinox Technologies’ commitment to fortifying its cybersecurity offerings,” said TitanHQ CEO, Ronan Kavanagh. “Together, Equinox Technologies and TitanHQ will be able to shield African companies from the constantly evolving landscape of cyber threats through a comprehensive suite of security solutions.”
by Jennifer Marsh | Mar 20, 2024 | Phishing & Email Spam |
Malware is often distributed via email or websites linked in emails, and advanced email security solutions such as SpamTitan Plus can protect you by preventing the messages from reaching inboxes. SpamTitan Plus uses dual antivirus engines to detect known malware and sandboxing to identify and block zero-day malware threats. SpamTitan Plus also rewrites URLs, uses predictive analysis to identify suspicious URLs, and blocks those URLs to prevent users from reaching the websites where malware is hosted. To get around email security solutions, cybercriminals use other methods for making initial contact with end users, and instant messaging services are a popular alternative.
Researchers at Cybereason recently identified a malware distribution campaign that distributes a Python-based information stealer via Facebook messages. The infostealer has been dubbed Snake and has been developed to steal credentials and other sensitive information. The campaign was first detected in the summer of 2023 and targets businesses. The messages use lures such as complaints and offers of products from suppliers to trick users into visiting a link and downloading a file. As is common with malware distribution campaigns, the threat actor uses legitimate public repositories for hosting the malicious file, such as GitHub and GitLab. The file to which the user is directed is a compressed file and, if extracted, will lead to the execution of a first-stage downloader. The first-stage downloader fetches a second compressed file, extracts the contents, and executes a second downloader, which delivers the Python infostealer.
Three different variants of the infostealer have been identified, all of which gain persistence via the StartUp folder. Each variant targets web browsers, including Brave, Chromium, Chrome, Edge, Firefox, Opera, and the Vietnamese CoC CoC browser, with the latter and other evidence suggesting that the campaign is being conducted by a Vietnamese threat actor. All three variants also target Facebook cookies. The gathered data and cookies are exfiltrated in a .zip file via the Telegram Bot API or Discord.
One way of blocking these attacks is to use a web filter to block access to instant messaging services that are not required for business purposes, including Facebook Messenger. With WebTitan it is possible to block Messenger without blocking the Facebook site, and controls can be implemented for different users to allow users with responsibility for updating the organization’s social media sites to access the platforms while preventing access for other users. It is also a good practice to use WebTitan to block downloads of executable files from the Internet to prevent malware delivery and stop employees from downloading and installing unauthorized software.
by Jennifer Marsh | Mar 14, 2024 | Phishing & Email Spam |
The file hosting service Dropbox is being abused in a novel phishing campaign that exploits trust in the platform to harvest Microsoft 365 credentials. The campaign targeted 16 employees of an organization who received an email from the no-reply[@]dropbox.com account, a legitimate email account that is used by Dropbox. The emails included a link that directed the recipients to a Dropbox-hosted PDF file, which was named to appear as if it had been created by one of the organization’s partners. If the PDF file was opened, the user would see a link that directs them to an unrelated domain – mmv-security[.]top. One of the employees was then sent a follow-up email reminding them to open the PDF file that was sent in the first email. They did, and they were directed to a phishing page that spoofed the Microsoft 365 login page. A couple of days later, suspicious logins were detected in the user’s Microsoft 365 account from unknown IP addresses, which were investigated and found to be associated with ExpressVPN, indicating the attacker was using the VPN to access the account and mask their IP address.
Multifactor authentication was correctly configured on the account but this appears to have been bypassed, with the logins appearing to use a valid MFA token. After capturing credentials, the employee is thought to have unknowingly approved the MFA authentication request which allowed the account to be compromised. The attacker gained access to the user’s email account and set up a new rule that moved emails from the organization’s accounts team to the Conversation History folder to hide the malicious use of the mailbox. Emails were also sent from the account to the accounts team in an apparent attempt to compromise their accounts.
Phishing attacks are becoming increasingly sophisticated and much more difficult for end users to identify. Security awareness training programs often teach users about the red flags in emails they should look out for, such as unsolicited emails from unknown senders, links to unusual domains, and to be wary of any requests that have urgency and carry a threat should no action be taken. Impersonation is common in phishing attacks, but in this case, the impersonation went further with the emails sent from a valid and trusted account. That means that the email is more likely to be trusted and unlikely to be blocked by email security solutions, especially as the emails include a link to a file hosted on a trusted platform. This was also a staged attack, with follow-up emails sent, which in this case proved effective even though the second email was delivered to the junk email folder. The login page to which the user was directed looked exactly the same as the genuine login prompt for Microsoft 365, aside from the domain on which it was hosted.
Many businesses have configured multifactor authentication on their Microsoft 365 accounts, but as this attack demonstrates, MFA can be bypassed. The sophisticated nature of phishing attacks such as this demonstrates how important it is for businesses to have advanced defenses against phishing. TitanHQ’s anti-phishing solutions use AI and a large language model (LLM) with proprietary threat intelligence currently not found in any other anti-phishing and anti-spam software solutions on the market. All emails are scanned – internal and external – for phrases and keywords that are unusual and could indicate malicious intent. All URLs are checked against various threat intelligence feeds to identify malicious URLs, and URLs are rewritten to show their true destination. The solution also learns from feedback provided by users and detection improves further over time. The curated and unique email threat intelligence data is unmatched in visibility, coverage, and accuracy, and TitanHQ’s anti-spam and email security solutions feature sandboxing, where attachments are subjected to deep analysis in addition to signature-based anti-virus scanning. When a malicious email is detected, all other instances are removed from the entire M365 tenant.
If you want to improve your defenses against sophisticated phishing attacks give the TitanHQ team a call. If you are a Managed Service Provider looking for an easy-to-use solution to protect your clients from phishing and malware, look no further than TitanHQ. All solutions have been developed from the ground up to meet the needs of MSPs to better protect their customers from spam, phishing, malware, and BEC attacks.
by Jennifer Marsh | Mar 6, 2024 | Security Awareness |
What would you say is the biggest cybersecurity threat in 2024? Ransomware is certainly a major concern, with attacks being reported with increasing frequency, and phishing attacks continue to cause headaches for businesses; however, a recent survey of Chief Technology Officers (CTOs) by STX Next has revealed the biggest perceived cybersecurity threat is neither of these. When asked about the biggest cybersecurity threat faced by their organization in 2024, 59% of CTOs said human error, 48% said ransomware, and 40% said phishing.
It is possible to implement a range of cybersecurity measures to combat threats such as ransomware and phishing to ensure that these attacks do not succeed. An email security solution can be implemented that will scan all emails for signs of phishing and will prevent the majority of malicious and unwanted messages from being delivered to inboxes. Email security solutions also scan emails for malware to prevent it from reaching employees. Security solutions can detect and block attempts by hackers to breach systems and implementing cybersecurity best practices will ensure that vulnerabilities are addressed before they can be exploited; however, employees are a weak point that many businesses are failing to address, and hackers know all too well that targeting employees is the easiest way to breach a company network.
Hackers can search for and exploit unpatched vulnerabilities in software and investigations of cyberattacks often show highly sophisticated attack methods have been used, but hackers have not required high levels of sophistication in most breaches. It is far easier to use social engineering to trick employees into providing access to accounts and systems and to take advantage of security mistakes by employees. Verizon’s 2023 Data Breach Investigations Report found the human element was involved in 74% of all cybersecurity breaches, with some studies suggesting the figure is closer to 95%.
Human error includes setting weak passwords that can easily be guessed, leaving systems unsecured, disclosing passwords in phishing emails, downloading malware onto their devices, sending emails containing sensitive data to incorrect recipients, installing unauthorized software, and more. It is not possible to stop employees from making mistakes, but if businesses provide security awareness training and teach employees security best practices, it is possible to reduce errors to a low and acceptable level. Security awareness training allows businesses to develop a security culture, where employees are constantly looking for threats and stop and think before they take any action that could potentially open the door to hackers.
The key to successful security awareness training is to provide it regularly. A once-a-year training session is better than nothing, but it won’t create a security culture and employees will not be sufficiently up-to-date on the new tactics that hackers are using to breach business networks. Training needs to be provided continuously throughout the year with employees instructed about the latest tactics hackers are using to target them so they can recognize threats and avoid them.
The SafeTitan Security Awareness Training platform makes it easy for businesses to create effective security awareness training programs. Courses can be developed that run continuously throughout the year, and the training content can be easily tailored to the organization, departments, job roles, and even individuals to ensure it is relevant and tackles the specific threats they are likely to face. The training content covers all aspects of security, teaches best practices, and makes employees aware of the threats they are likely to encounter. SafeTitan is a modular training platform with each computer-based training module lasting no more than 10 minutes, so it is easy to fit training into busy workflows. It is easy for businesses to monitor who is completing training and see how effective the training has been.
In addition to providing training, employees’ knowledge needs to be tested to make sure that the training material has been understood and is being applied. SafeTitan includes a phishing simulation platform that allows businesses to see how employees respond to simulated attacks and identify employees who are making mistakes. Those weak points can then be addressed before they can be exploited by hackers. SafeTitan is the only security awareness training platform that delivers training in real-time in response to employee errors. When an error is detected, such as a phishing test failure, training is delivered to individual employees in real-time when the additional training is likely to be most effective at changing behavior.
Employees are the first line of defense and it is important for the defensive line to be fortified, rather than solely concentrating on technical measures such as anti-spam gateways and spam filtering appliances. To find out more about the SafeTitan platform, give the TitanHQ team a call today. SafeTitan is also available on a free trial so you can see for yourself how easy it is to create and automate your training courses.
by Jennifer Marsh | Mar 5, 2024 | Phishing & Email Spam |
A new phishing kit has been identified that is being used to target employees of the U.S. Federal Communications Commission (FCC) and the cryptocurrency platforms Binance and Coinbase, as well as users of cryptocurrency platforms such as Binance, Coinbase, Caleb & Brown, Gemini, Kraken, ShakePay, and Trezor.
A phishing kit is a set of tools and templates that allows threat actors to conduct effective phishing campaigns. These kits are marketed on the dark web to hackers and allow them to conduct phishing campaigns without having to invest time and money into setting up their own infrastructure. Phishing kits range from simple kits that provide phishing templates and cloned login pages, to more advanced kits that are capable of adversary-in-the-middle attacks that can defeat multifactor authentication. These kits significantly lower the entry barrier for conducting phishing campaigns as they require little technical expertise. Pay a relatively small fee and sophisticated phishing campaigns can be conducted in a matter of minutes.
The new phishing kit is called CryptoChameleon and allows users to create carbon copies of the single sign-on (SSO) pages that are used by the targeted businesses. Employees are used to authenticating through a single solution, through which they authenticate with many business applications. The kit also includes templates for phishing pages to harvest the credentials of cryptocurrency platform users and employees, including pages that impersonate Okta, iCloud, Gmail, Outlook, Yahoo, AOL, and Twitter.
The phishing operation was discovered by researchers at Lookout and more than 100 high-value victims of this campaign have been identified to date. Threat actors using the kit have been contacting users via SMS, email, and phone calls to trick them into visiting a malicious site where their credentials are harvested. Users are redirected to a phishing site but before the content is displayed, they are required to pass an hCAPTCHA check. This helps with the credibility of the campaign, but most importantly it prevents automated analysis tools and security solutions from identifying the phishing site.
In the campaign targeting FCC employees, after passing the hCAPTCHA check, the user is presented with a login page that is a carbon copy of the FCC Okta page. The domain on which the page is hosted – fcc-okta[.com] – differs only slightly (1 character) from the legitimate FCC Okta login page. Login credentials alone are not normally enough to gain access to accounts as many are now protected by MFA. The captured login credentials are used to log in to the real account in real time, and the victim is then directed to the appropriate page where additional information is collected to pass the MFA checks. This could be a page that requests their SMS-based token or the MFA token from their authenticator app. Once the MFA check has been passed and the account has been accessed by the threat actor, the victim can be redirected anywhere. For instance, they could be shown a message that the login has been unsuccessful and they must try again later.
To target cryptocurrency platform users, messages are sent about security alerts such as warnings that their account has been accessed. These messages are likely to attract a rapid response due to the risk of substantial financial losses. In the campaign targeting Coinbase, the user is told they can secure their account and if they log in they can terminate suspicious devices. A similar process is used to obtain the credentials and MFA codes needed to access the account as the FCC campaign.
This is just one of many phishing kits offered on the dark web. Protecting against these phishing kits requires a combination of measures including an advanced spam filter, web filter, and security awareness training. For further information on cybersecurity solutions capable of combatting advanced phishing attempts, give the TitanHQ team a call.
by Jennifer Marsh | Feb 29, 2024 | Network Security |
Phobos ransomware may not be the most prolific ransomware group, but the group poses a significant threat, especially to municipal and county governments, emergency services, education, and healthcare organizations. The group issues ransom demands for millions of dollars and the group’s attacks have caused hundreds of millions of dollars in losses. Phobos is a ransomware-as-a-service operation where the infrastructure to conduct attacks and encrypt files is provided to affiliates – individuals who specialize in breaching company networks – in exchange for a percentage of any ransom payments they can generate. The affiliates benefit from being able to concentrate on what they do best, and the ransomware group makes up for the loss of a percentage of the ransom by conducting many more attacks than would be possible on their own.
The group engages in double extortion tactics involving data theft and file encryption. Threats are issued to publicly leak stolen data on the group’s data leak site and payment is required for the keys to decrypt data and prevent data exposure. Several ransomware variants are connected to Phobos based on the tactics, techniques, and procedures (TTPs) used in attacks, including Elking, Eight, Devos, Faust, and Backmydata ransomware. The latter variant was recently used in an attack in Romania that affected around 100 hospitals.
Affiliates use several methods to gain initial access to victims’ networks, with phishing one of the most common. The phishing attacks conducted by the group usually involve spoofed email attachments with hidden payloads, with one of the favored payloads being the Smokeloader backdoor trojan. Smokeloader gives the group initial access to victims’ networks, from where they use a variety of methods and legitimate networking tools for lateral movement, credential theft, privilege escalation, and data exfiltration. These include 1saas.exe or cmd.exe for privilege escalation, Windows shell functions for control of systems, and built-in Windows API functions to bypass access control and steal authentication tokens. Open source tools such as Bloodhound and Sharphound are used to enumerate the Active Directory, Mimikatz for obtaining credentials, and WinSCP and Mega.io for file exfiltration. Other methods used for initial access include the use of legitimate scanning tools such as Angry IP Scanner to search for vulnerable RDP ports, and then open source brute-forcing tools are used to guess weak passwords.
To improve defenses against Phobos ransomware attacks, businesses should follow the guidance in the recently published security alert from the U.S. Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of Investigation (FBI), and Multi-State Information Sharing and Analysis Center (MS-ISAC), which includes latest Indicators of Compromise (IoCs) and TTPs observed in recent attacks. The guidance can be found in the #StopRansomware section of the CISA website.
Mitigations are concerned with improving defenses against the initial access vectors – phishing and remote access software. An email security solution is required to block phishing emails, consider disabling hyperlinks in emails, and adding banners to emails from external sources. An email security solution should be used that has both signature and behavioral threat detection capabilities to identify malicious files. End user training should be provided to improve resilience to phishing attempts, web filtering to block malicious file downloads, phishing-resistant multi-factor authentication to prevent the use of compromised credentials from granting access, strong password policies to improve resilience to brute force attacks, and strict controls on RDP and other remote desktop services. Robust backup processes are required, including maintaining offline backups of data, and an incident response policy for ransomware attacks should be developed and tested to ensure the fastest possible recovery in the event of an attack.
by Jennifer Marsh | Feb 29, 2024 | Network Security |
A coordinated law enforcement operation – Operation Cronos – headed by the UK National Crime Agency (NCA) and coordinated by Europol seized the infrastructure of the notorious LockBit ransomware group earlier this month. 34 servers were seized in the Netherlands, Germany, Finland, France, Switzerland, Australia, the United States, and the United Kingdom, along with 200 cryptocurrency wallets, and the keys to decrypt the data of some of the group’s victims. Two LockBit actors were also arrested in Poland and Ukraine, and three arrest warrants and five indictments were issued by judicial authorities in France and the United States. The decryption keys allowed an automated decryptor to be developed, which was added to the No More Ransom website.
The group’s affiliate portal was seized along with its data leak sites and messages were uploaded for affiliates warning them that names and locations were known and they could receive a visit from law enforcement very soon. The NCA threatened to release the name of the group’s figurehead, LockBitSupp, and even added a countdown timer to the data leak site, as LockBit would do when adding victims to the leak site. However, the NCA did not disclose the details and instead added a statement confirming LockBitSupp’s real name, location, and financial worth were known. The NCA also added that LockBitSupp has engaged with law enforcement.
LockBit is a ransomware-as-a-service (RaaS) operation where affiliates are recruited to conduct attacks using LockBit ransomware. As payment for those attacks, affiliates receive a percentage of any ransoms they generate. LockBit engaged in double extortion tactics, where sensitive data was stolen in addition to file encryption. Payments are required to prevent the release of the stolen data on the group’s data leak site and to obtain the keys to decrypt data. LockBit then moved to triple extortion, where in addition to data theft and file encryption, Distributed Denial-of-Service (DDoS) attacks are conducted on victims to pile on the pressure and get them to pay the ransom.
LockBit has been in operation since September 2019 and rapidly became a major player in the RaaS market. At the time of the takedown, LockBit was behind 25% of all ransomware attacks and had around 180 affiliates conducting attacks. The next biggest player is Blackcat with an 8.5% market share. The LockBit group has extorted more than $120 million from organizations around the world and its attacks have caused billions of dollars of damage.
The law enforcement operation was significant and a major embarrassment for the group, potentially causing significant damage to the group’s reputation. However, it did not take long for LockBit to respond. A few days after the announcement about the law enforcement action, LockBit created a new data leak site and populated it with the names of 12 recent victims. A note was also added explaining that the FBI most likely exploited an unpatched PHP bug, which hadn’t been addressed out of laziness, which allowed access to be gained to its servers. LockBit claimed the takedown was conducted when it was because data was going to be released from an attack on Fulton County in Georgia, where one of Donald Trump’s lawsuits is being heard, and the release of that data could affect the upcoming Presidential Election.
Typically after a successful law enforcement operation, ransomware gangs rebrand but LockBit appears to be defiant and looks set to continue under the same name. LockBitSupp claimed that the attacks could not stop as long as he was alive, and the group would be updating its infrastructure to make it harder for any future law enforcement operations to succeed. A little more than a week after the law enforcement announcement, the LockBit group appears to be conducting attacks again using new infrastructure, a new data leak site, a new negotiation site, and a new encryptor. It is unclear how many affiliates have been retained but the group has announced that it is recruiting again and is looking for new pen testers, indicating some have decided to leave the operation. What is clear is the group is back and remains a significant threat.
by Jennifer Marsh | Feb 29, 2024 | Network Security |
There is growing evidence that cybercriminal groups are leveraging artificial intelligence in their cyberattacks, specifically large language models (LLMs) such as ChatGPT, despite the restrictions OpenAI has put in place. There are also LLMs that are being marketed directly to cybercriminals such as WormGPT. WormGPT is a blackhat AI tool that has been specifically developed for malicious uses and can perform similar tasks to ChatGPT but without any ethical restrictions on uses. The tool can be used for generating convincing phishing and business email compromise emails in perfect English, free from the spelling mistakes and grammatical errors that are often found in these emails.
It is not only cybercriminal groups that are using these AI tools. Nation state hacking groups are exploring how these tools can help them gain initial access to targeted networks. Recently published research from Microsoft and OpenAI confirmed that threat actors from Russia, China, Iran, and North Korea and using AI tools to support their malicious activities. Microsoft and OpenAI found the most common uses of LLMs by nation state actors were for translation, finding coding errors, running basic coding tasks, and querying open-source information. While it does not appear that they are using LLMs to generate new methods of attack or write new malware variants, these tools are being used to improve and accelerate many aspects of their campaigns.
The threat actor tracked by Microsoft as Crimson Sandstorm, which is affiliated with the Islamic Revolutionary Guard Corps (IRGC), a multi-service primary branch of the Iranian Armed Forces, has been using LLMs to improve its phishing campaigns to gain initial access to victims’ networks. Microsoft and OpenAI also report that the hacking group has been using LLMs to enhance its scripting techniques to help them evade detection. The North Korean APT group, Emerald Sleet, is well known for conducting spear phishing and social engineering campaigns and is using LLMs to assist with researching think tanks and key individuals that can be impersonated in its spear phishing campaigns. Threat groups linked to the People’s Republic of China such as Charcoal Typhoon and Salmon Typhoon have been using LLMs to obtain information on high-profile individuals, regional geopolitics, US influence, and internal affairs and for generating content to socially engineer targets. OpenAI says it has terminated the accounts of five malicious state actors and has worked with Microsoft to disrupt their activities, and OpenAI and Microsoft have been sharing data with other AI service providers to allow them to take action to prevent malicious uses of their tools.
It should come as no surprise that cybercriminals and nation state actors are using AI to improve productivity and the effectiveness of their campaigns and are probing the capabilities of AI-based tools, and while this is a cause of concern, there are steps that businesses can take to avoid falling victim to AI-assisted attacks. The best way to combat AI-assisted attacks is to leverage AI for defensive purposes. SpamTitan has AI and machine learning capabilities that can detect zero day and AI-assisted phishing, spear phishing, and business email compromise attacks and better defend against AI-0assisted email campaigns.
With fewer spelling mistakes and grammatical errors in phishing emails, businesses need to ensure they provide their workforce with comprehensive training to help employees recognize email and web-based attacks. The SafeTitan security awareness training and phishing simulation platform is an ideal choice for conducting training and phishing simulations and improves resilience to a range of security threats. TitanHQ’s data shows susceptibility to phishing attacks can be reduced by up to 80% through SafeTitan training and phishing simulations. Businesses should also ensure that all accounts are protected with multi-factor authentication, given the quality of the phishing content that can be generated by AI tools, and ensure that cybersecurity best practices are followed, and cybersecurity frameworks are adopted. The most important advice that we can give is to take action now and proactively improve your defenses, as malicious uses of AI are only likely to increase.
by Jennifer Marsh | Feb 28, 2024 | Phishing & Email Spam |
Cybercriminals are increasingly offering services that make it easy for anyone to conduct an attack. Skilled malware developers can concentrate on writing their malware and making it available for others to use for a fee, ransomware-as-a-service allows hackers who are skilled at breaching networks to conduct lucrative ransomware attacks without having to develop encryptors and pay for the infrastructure to their support attacks, and phishing-as-a-service provides a platform for conducting attacks to steal credentials and access accounts. These services benefit all parties and allow even more attacks to be conducted.
Phishing campaigns may appear simple, but they require a lot of time and skill to set up. Stephanie Carruthers, who leads an IBM X-Force phishing research project, said it takes her team about 16 hours to craft a phishing email, not including the time it takes to set up all the necessary infrastructure to send the email and steal credentials. Setting up the infrastructure is time-consuming and costly, and many businesses now have multi-factor authentication (MFA) to thwart attacks.
With phishing-as-a-service (PhaaS), anyone who wants to run a phishing campaign can simply pay a subscription and will be provided with all the tools they need to conduct attacks. They do not need to craft the phishing emails, they just need to set a few parameters and provide the email addresses for the campaign. PhaaS makes conducting sophisticated attacks simple and significantly lowers the bar for conducting campaigns.
Take LabHost, for example, a PhaaS platform that recently introduced functionality for targeting financial institutions and banks in North America and Canada. Since this new functionality was included in the first half of 2023, attacks have increased considerably. A monthly subscription is paid, and customers are provided with a turnkey phishing kit, which includes the infrastructure for hosting phishing pages, a content generator for creating phishing emails, and a portal for monitoring the progress of campaigns. Customers can choose to pay $179 per month to target Canadian banks, $249 per month to expand the targets to North America, and $300 a month to also target 70 financial institutions worldwide. Customers are also provided with phishing pages for collecting credentials or a variety of other companies, including music streaming sites, delivery services, and telecommunications companies.
Important to the success of any campaign is the ability to defeat multi-factor authentication. The LabHost phishing kit incorporates LabRat, a phishing tool that allows real-time management of phishing campaigns and allows adversary-in-the-middle attacks where two-factor authentication codes and cookies are obtained in addition to usernames and passwords. That means the additional security processes on the online portals of banks can be circumvented. The platform also allows SMS-based attacks to be conducted.
PhaaS allows unskilled hackers to conduct effective campaigns that they otherwise would not be able to conduct. Further, with the use of AI to craft convincing phishing emails, phishing emails are becoming much harder for humans and security solutions to detect, and even MFA and other security measures can be bypassed.
Defending against attacks is therefore challenging, and there is no single cybersecurity solution that will block all attacks. What is needed is a defense-in-depth approach, with multiple, overlapping layers of protection. Cybersecurity solutions are required to block the phishing emails. SpamTitan is an advanced email security solution with AI and machine learning capabilities for identifying novel phishing threats. SpamTitan blocks known malware through AV controls and unknown malware through sandboxing. The message sandboxing feature uses pattern filtering to identify malware from its behavior, which allows zero-day malware threats to be identified and blocked. Malware sandboxing is vital for email security since so many novel malware threats are now being released. SpamTitan is also capable of identifying even machine-crafted phishing content.
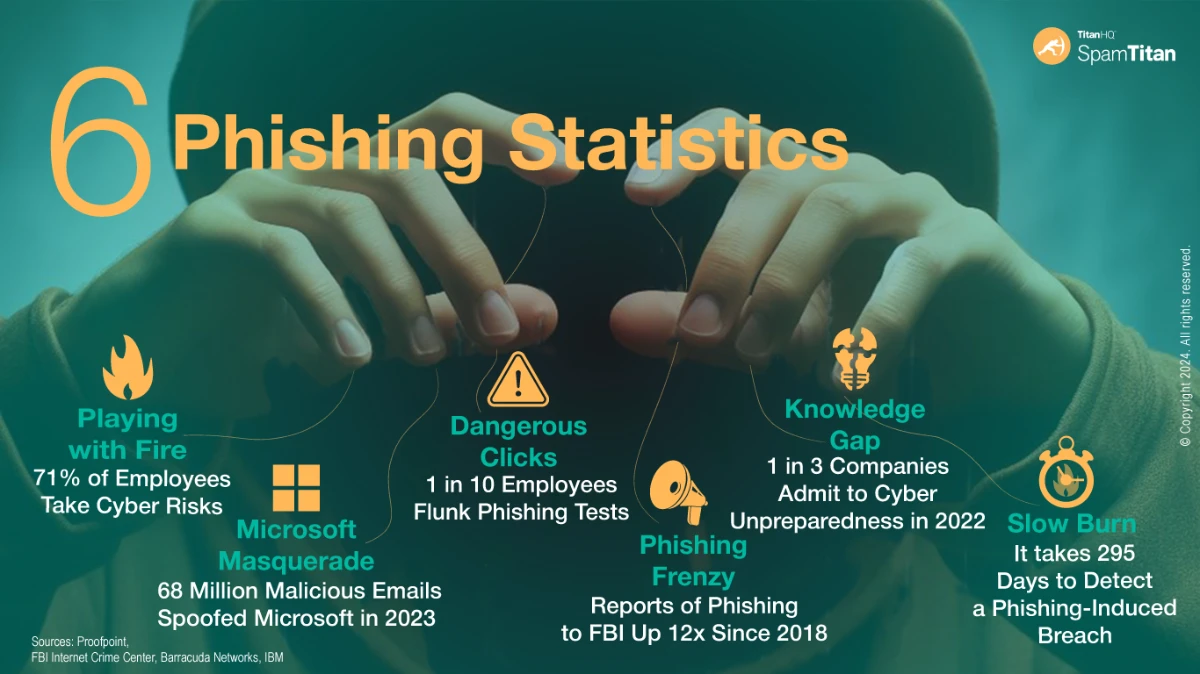
End user training is also vital, as no email security solution will block all email threats without also blocking an unacceptable number of genuine emails. End users should be trained on how to identify, avoid, and report phishing emails. The SafeTitan security awareness training platform makes security awareness training simple, and the constantly updated content allows businesses to respond to changing phishing tactics and conduct phishing simulations on the workforce to reinforce training and identify knowledge gaps.
Given the number of phishing kits that are capable of bypassing multi-factor authentication, simply enabling MFA on accounts is no longer sufficient to protect against unauthorized access. Phishing-resistant multi-factor authentication is required – FIDO/ WebAuthn authentication or Public key infrastructure (PKI)-based MFA – to block adversary-in-the-middle attacks that can be conducted through PhaaS.
If you want to improve your defenses against phishing and other cybercriminal services, give the TitanHQ team a call to discuss your options.
by Jennifer Marsh | Feb 26, 2024 | Phishing & Email Spam |
A massive email spamming campaign has been detected that is generating up to 5 million emails per day that direct recipients of the emails to a variety of scam sites. The emails are sent through hijacked subdomains and domains of trusted companies, which help these emails evade email security solutions and be delivered to inboxes. Companies that have had domains and subdomains hijacked include eBay, CBS, McAfee, MSN, and Symantec.
Email security solutions perform a range of checks on inbound emails, including reputation checks on the senders of emails. If a domain is trusted and has not previously been associated with spamming, these checks – using SPK, DKIM, and DMARC – are likely to be passed, resulting in the emails being delivered to end users. The use of these legitimate domains also makes it harder for end users to determine whether the messages are genuine. Security awareness training programs often teach end users to check the sender of the email and make sure that it matches the company being spoofed. If the domain is eBay, and the email uses eBay branding, end users are likely to think that the communication is genuine. These emails include links to websites that generate fraudulent ad revenue, and often several redirects occur before the user lands on the destination scam or phishing site.
The ‘SubdoMailing’ campaign was identified by researchers at Guardio Labs, with the legitimate domains typically hijacked through SPF record exploitation or CNAME hijacking. The former involves searching for domains that use the ‘include’ configuration option that points to external domains that are no longer registered. Those domains are then registered by the threat actor and the SPF records are changed to authorize the use of their own email servers. When those servers are used to send emails, they appear to have been sent by the targeted brand, such as eBay.
With CNAME hijacking, scans are conducted to identify subdomains of reputable brands with CNAME records that point to external domains that are no longer registered. The threat actor then registers those domains, SPF records are injected, and emails can be sent from their email servers to show that they have been sent by a legitimate company. By hijacking huge numbers of domains and subdomains, the threat actor is able to conduct massive spamming campaigns. The researchers identified more than 13,000 subdomains and more than 8,000 domains that were used in the campaign, with more than 1000 residential lines used and almost 22,000 unique IPs. The researchers developed a tool to allow domain owners to check whether their own domains have been hijacked and take action to stop that abuse. An advanced spam filter is required to block the messages that are set from these hijacked domains and subdomains – one that does not rely on SPF, DKIM, and DMARC for identifying spam emails.
by Jennifer Marsh | Feb 26, 2024 | Security Awareness |
One of the fundamental security awareness training errors made by many businesses is failing to check the effectiveness of their training. A training course is purchased or developed internally, employees receive training, and the training is provided again each year, but there are no assessments performed to determine whether the training has actually worked. It is often only when there is a successful phishing attack that training is discovered to have failed, and many businesses then blame the employee for falling for the phishing attempt, when the fault may lie with the employer.
The aim of security awareness training is to change users’ behavior, and that is achieved by teaching security best practices, making employees aware of the threats they are likely to encounter, showing them what they should be doing to identify and avoid those threats, and teaching them to report those threats to the security team. The process should not end there, as it is also necessary to determine whether the training has worked. Many employees will take the training on board, will change their behavior, and will become security Titans. Others may struggle to grasp certain concepts and require further training or different training approaches. If there is no monitoring or assessments, weak points will not be identified and risk will not be reduced.
Tips for Assessing the Effectiveness of Security Awareness Training
Assessing the effectiveness of security awareness training can be challenging, as there is no single metric that can be measured that provides a complete picture. The best approach is to use multiple metrics for measuring the effectiveness of a security awareness training program.
First, you need to have a baseline against which you can measure progress. You need to know the level of security awareness before training starts and you can measure progress over time. Pre-training assessments are useful and can be conducted via a questionnaire covering all security topics you intend to cover during training. These questionnaires will also allow you to develop training courses appropriate to each individual to ensure that specific knowledge gaps are addressed.
It is important to monitor participation and completion rates to see how whether employees are engaging and taking training seriously. If participation is poor, the importance of training may not have been conveyed, or employees may not have the time to fit training into busy workflows, and these factors will need to be addressed. If training content is not being completed, the training may be too long, not engaging enough, and boring. If employees are not engaged, then the training will not be effective.
Quizzes should be conducted after each training module to see if employees have understood the topic. If questions are answered incorrectly, then the employees concerned have not understood the training and need more help. These quizzes allow targeted intervention to address issues with individual employees on specific topics. These quizzes should be repeated over time to test knowledge retention. A quiz directly after a training session may be passed but testing again in a few weeks or months will allow you to measure whether information has been retained.
One of the most important tools is a phishing simulation platform. These platforms are used to send realistic but fake phishing emails to the workforce to test whether training is being applied. Phishing simulation data is one of the most important metrics for measuring the effectiveness of a training campaign through open rates, click rates, and reporting rates. These simulations should be conducted before training to get a baseline and after training to determine the effectiveness of security awareness training over time. If the click rate is falling and the reporting rate is increasing, then the training is working. Phishing simulations also allow you to identify knowledge gaps and provide targeted training specific to the threat that was incorrectly identified. It gives employees practice at applying their new knowledge so that when a real threat is encountered, it is more likely to be correctly identified.
You should also seek feedback on the training from your employees. The best approach is to provide anonymous questionnaires and to encourage employees to provide honest feedback. These questionnaires should include security questions to gauge understanding of security best practices, questions to determine how the employees feel about the training, any problems they have, and if they feel the training has been effective and relevant to their role. While the questionnaire should be anonymous, it is useful to know which departments the employees work in to allow you to tailor your training course appropriately.
Security Awareness Training from TitanHQ
Monitoring the effectiveness of security awareness training is easy with the SafeTitan security awareness training and phishing simulation platform. The platform allows users to conduct pre-training assessments, assessments after each training module, and further assessments over time. The phishing simulation platform allows simulations to be automated and provides detailed metrics that demonstrate the effectiveness of the training and show the return on your investment. The phishing simulator will also trigger additional training in response to a failed test, which is delivered immediately to explain the error that has been made and provide the necessary training at the point when the training is most likely to be taken on board.
Through the use of the SafeTitan platform and phishing simulator, businesses can not only improve resilience to threats, they can get detailed metrics to show just how effective training has been. Data from users shows that resilience to phishing can be improved by up to 80%. Get in touch with the TitanHQ team today to find out more and to arrange a free trial of the platform to see for yourself how easy it is to create training campaigns, run phishing simulations, and measure the effectiveness of security awareness training. TitanHQ also offers DNS filtering, email encryption, phishing protection, and email archiving solutions, and a cloud-based anti-spam service with unrivaled accuracy.
by Jennifer Marsh | Feb 26, 2024 | Phishing & Email Spam |
Cybercriminals are constantly devising new email campaigns for distributing malware. These campaigns usually impersonate a trusted entity and advise the email recipient about a pressing issue that requires immediate attention. The emails often have an attached file that must be opened to find out further information about the issue detailed in the email.
One recently detected campaign impersonates travel service providers such as booking.com and advises the recipient about a problem with a recent booking. One of the intercepted emails explains that an error has occurred with a booking that has resulted in a double charge to the user’s credit card which requires immediate attention. The email has a PDF attachment which needs to be opened for further information. PDF files are increasingly being used in email campaigns for distributing malware. The PDF files often contain a script that generates an error message when the file is opened that tells the user that the content of the file cannot be displayed, and they are provided with an option to download the file.
In this campaign, the PDF file contains a script that generates a fake popup message. If clicked, a connection is made to a malicious URL and a download of an obfuscated JavaScript file is initiated. The script downloads the next stage PowerShell payload, and on execution, drops a malicious DLL file on the device. The DLL file searches for certain critical system processes and attempts to forcibly stop them, makes changes to the registry that affect the Windows Antimalware Scan Interface (AMSI) and ensures that the malware is executed without being detected by security solutions. An analysis of the DLL file by researchers at Forcepoint shows the file is from the Agent Tesla malware family. Agent Tesla is a remote access trojan (RAT) that first appeared in 2014 and grew in popularity during the COVID-19 pandemic. Agent Tesla is provided under the malware-as-a-service model and is popular with initial access brokers, who specialize in gaining access to devices and accounts and then sell that access to other cybercriminals such as ransomware gangs.
Agent Tesla allows commands to be run on compromised systems and is capable of stealing sensitive information, such as login credentials stored in browsers. The malware can also take screenshots, log keystrokes, and perform other malicious actions. The malware uses multiple layers of obfuscation to ensure it is not detected by antivirus solutions. The malware is commonly used to gain initial access to business networks, primarily through phishing campaigns. In this campaign, by impersonating a popular travel service company there is a reasonable chance that the user may have used the service in the past or have a current booking and will therefore open the email. However, since the emails reference a charge to a credit card, that may be sufficient to get the user to open the attachment.
To protect against this and other malware distribution campaigns, businesses should ensure that they protect all endpoints with email security and antivirus solutions that are capable of behavioral analysis of files, as Agent Tesla and many other popular malware variants use obfuscation to bypass signature-based security solutions. Web filtering solutions provide added protection as they block connections to the malicious URLs that host malware and they can be configured to block downloads of executable files from the Internet. It is also important to provide security awareness training to the workforce to raise awareness of cyber threats and conduct phishing simulations to test the effectiveness of training.
TitanHQ offers a range of cybersecurity solutions for businesses and managed service providers to help them defend against cyber threats delivered via email and the Internet, including spam filtering with email sandboxing, web filtering, and security awareness training. Give the team a call today to find out more about improving your defenses against phishing and malware. All TitanHQ solutions are available on a free trial to allow you to test the products and see for yourself the difference they make.
by Jennifer Marsh | Feb 23, 2024 | Email Scams |
Small- and medium-sized businesses are being targeted in a phishing campaign that leverages the email service provider (ESP) SendGrid. SendGrid is a legitimate and well-known company that provides a customer communication platform for transactional and marketing email. SendGrid customer accounts are targeted to gain access to company mailing lists which can be used for a variety of email campaigns, such as phishing, spamming, and scams. In this campaign, the phishers compromise companies’ SendGrid accounts and use the ESP itself to send phishing emails. Emails sent through the SendGrid platform are likely to be trusted by email security solutions, especially as the compromised accounts will have been used to send communications in the past. SendGrid may even be whitelisted to ensure that the emails are always delivered to inboxes. SendGrid emails are also likely to be trusted by end users.
In this campaign, the emails use a security-themed lure and inform the recipients that they need to set up 2-factor authentication – a perfectly reasonable request since 2-FA will better protect accounts against unauthorized access. The users are provided with a link that directs them to a malicious website that spoofs the SendGrid login, and if credentials are entered, they are harvested by the scammer. The emails were routinely delivered to inboxes and evaded email security solutions because the SendGrid was trusted.
SendGrid performs stringent checks on new accounts so it is difficult for malicious actors to use SendGrid directly, instead they compromise business SendGrid accounts, often through phishing attacks. Twilio SendGrid detected the malicious activity linked to customer accounts that were being used for phishing, and its fraud, compliance, and cyber security teams immediately shut down accounts. To better protect SendGrid accounts, users are advised to log in to their account and set up 2-factor authentication to prevent compromised credentials from granting access to user accounts.
The campaign demonstrates that even emails from reliable sources may not be what they seem. Many companies provide security awareness training to their employees that teaches cybersecurity best practices and trains employees on how to recognize and avoid phishing. It is important to include these types of emails in training material, as ESPs are being increasingly targeted by cybercriminals due to the effectiveness of campaigns run through an ESP.
With SafeTitan, keeping employees up to date on the latest tactics used by phishers and other cybercriminals is easy. The training content is regularly updated with new phishing templates based on real-world attacks and the latest phishing trends, and phishing simulations can be conducted on employees to test how they respond to phishing attempts outside of the training environment. SafeTitan is the only security awareness training platform that delivers targeted training automatically in response to bad security practices by employees, ensuring training is provided at the moment when it is most likely to be taken on board.
by Jennifer Marsh | Feb 22, 2024 | Phishing & Email Spam |
A massive malware distribution campaign has been detected that uses phishing emails for initial contact with businesses and Google Cloud Run for hosting the malware. A variety of banking trojans are being distributed including Astaroth, Mekotio, and Ousaban. The campaign primarily targets countries in Latin America, and as such the majority of the phishing emails are in Spanish, but Italian versions have also been detected and there are indications that the campaign is spreading to other regions including Europe and North America.
The phishing emails used in this campaign appear to be legitimate invoices, statements, and communications from government and tax agencies and include a link that the recipient must click to view the attached invoice, statement, or demand. The link directs the user to services on Google Cloud Run, which is a popular service for hosting frontend and backend services and deploying websites and applications without having to manage infrastructure. Google Cloud Run has been used for hosting malware throughout 2023 but there was a massive spike in activity that started in September 2023 and has continued through January and February.
Over the past few months, Google’s service has been proving popular with cybercriminals for hosting malware as it is both cost-effective and is generally not blocked by security solutions. If a user clicks the email link, an MSI file is downloaded onto their device. MSI files are executable files, which in this case include embedded JavaScript that downloads additional files and delivers one or more banking trojans.
The banking trojans achieve persistence through LNK files in the startup folder that execute a PowerShell command on boot that runs the infection script. The banking trojans are capable of keylogging, clipboard monitoring, screenshots, credential theft, and traffic manipulation to direct users to cloned websites of financial institutions to capture banking credentials. The Astaroth banking trojan alone targets more than 300 financial institutions as well as cryptocurrency exchanges.
To protect against this and other malware distribution campaigns, businesses need to adopt a defense-in-depth approach and should implement multiple layers of protection. The first line of defense is a spam filter or email security solution to block the initial phishing emails. SpamTitan Plus is a leading-edge anti-spam service that provides maximum protection against malicious emails. The solution has better coverage, faster phishing link detections, and the lowest false positive rate of any product, which makes it the best spam filter for businesses and an ideal MSP spam filtering solution In addition to including all leading phishing feeds to ensure the fastest possible detection of new phishing threats, SpamTitan Plus uses predictive analysis to identify suspicious URLs that have not yet been detected as malicious.
A web filter, such as WebTitan, can be used to control access to the Internet. For example, blocks can be placed on websites and certain categories of websites down to the user level, the solution prevents access to all known malicious URLs, and can be configured to block file downloads from the Internet, such as MSI files and other executable files that are often used for malware delivery.
Cybercriminals often host malware on legitimate hosting platforms which are usually trusted by security solutions, which means malicious emails may be delivered to end users. It is therefore important to provide security awareness training for the workforce. Security awareness training raises awareness of the threats that employees are likely to encounter and teaches them security best practices to help them identify, avoid, and report cyber threats. Combined with phishing simulations, it is possible to greatly reduce susceptibility to phishing and malspam emails. Data from companies that use the SafeTitan security awareness training platform and phishing simulator shows susceptibility to phishing threats can be reduced by up to 80%.
If you are looking to improve your defenses against phishing and malware, give the TitanHQ team a call to find out more about these products and to help get you set up for a free trial to put these solutions to the test in your own environment.
by Jennifer Marsh | Feb 21, 2024 | Phishing & Email Spam |
A recent report from the Computer Emergency Response Team (CERT-EU) has provided insights into how EU organizations are being targeted by nation-state-sponsored actors and cybercriminal groups. The majority of nation-state activity has been linked to hacking groups in the Russian Federation and the People’s Republic of China, and while it is not always possible to determine the motives behind cyberattacks and intrusions, the majority of nation-state hacking activity is believed to be conducted to achieve cyberespionage objectives. The aim of these campaigns is to gain access to accounts/emails or servers where sensitive data is stored. Around 73% of all attacks within the EU are believed to be conducted for espionage purposes, with 16% of attacks conducted by hacktivists. Some of the hacktivism incidents are thought to be a front for nation-state activity.
In contrast to the United States, cybercriminal activity accounts for a low percentage of all malicious activity, with only 7% of intrusions attributed to cybercrime. CERT-EU reports that only a very limited number of cybercrime actors are conducting attacks within the EU, and the majority of that activity comes from ransomware groups. These groups gain access to internal networks, steal sensitive data, and encrypt files then demand payment to prevent the publication of the stolen data and for the keys to decrypt data.
In 2023, CERT-EU identified 55 ransomware operations that were active within the EU, and 906 victims were identified from data leak sites and open sources. It should be noted that not all ransomware attacks are reported and many companies quietly pay the ransom, so the true total could be substantially higher. Many of these attacks appeared to be opportunistic in nature rather than targeted. While there are many different ransomware groups, the most active in the EU were LockBit, Play, and BlackBasta, although in Q4, 2023 there was a large increase in attacks by the 8Base group, with NoEscape also highly active in the second half of the year. Ransomware groups attacked a wide range of sectors, with manufacturing the worst affected with 24% of attacks, followed by legal/professional services (14%), and construction/engineering (12%).
A variety of methods were used to gain access to targeted networks. 104 software products were targeted with these attacks often exploiting vulnerabilities in internet-facing products, involving trojanized software, fake software, and abuse of public repositories used for programming languages. Some of the most significant attacks of the year involved networking products, such Fortinet, Cisco, and Citrix products, as well as password managers such as 1Password or LastPass, content management and collaboration tools such as WordPress and Altassian Confluence, and cloud services. While many attacks used these methods for initial access, by far the most common method was spear phishing for both cybercriminal and nation-state threat actors.
Spear phishing attacks include malicious links to websites where credentials are harvested or malicious attachments. There was a significant increase in spear phishing attacks that used lures related to EU affairs, with it common to include decoy PDF files that were originally internal or publicly available documents related to EU policies, for example, documents relating to the Swedish Presidency of the Council of the European Union, EU – Community of Latin American and Caribbean States (CELAC) Summit, and the Working Party of Foreign Relations Counsellors (RELEX). These campaigns were directed at individuals and organizations involved in EU policies, and the emails often impersonated staff members of union entities or the public administration of EU countries to add credibility. Public administration entities were the most targeted, followed by entities in diplomacy, defense, transport, finance, health, energy, and technologies. While spear phishing is usually performed via email, CERT-EU notes some diversification of communications, with attacks also conducted via social media networks, instant messaging services, and SMS messages.
Entities in the EU should implement layered defenses against the most common initial access vectors. An advanced email security solution should be implemented that is capable of signature and behavioral analysis of emailed files, with extensive threat intelligence feeds, and AI/machine learning capabilities. SpamTitan anti-spam software has all of these features and more and will protect your business from all types of email-based attacks. SpamTitan is offered as a cloud-based anti-spam service or can be provided as an anti-spam gateway for on-premises environments. A web filter such as WebTitan will protect against the internet-based component of cyberattacks by blocking access to malicious sites, and security awareness training and phishing simulations should be conducted on the workforce using a solution such as SafeTitan. To protect against unauthorized account access, multi-factor authentication should be implemented and software should be kept up to date with the latest updates and patches applied promptly.
by Jennifer Marsh | Feb 20, 2024 | Phishing & Email Spam |
There has been a marked increase in email campaigns using malicious PDF files to distribute malware, rather than the typical uses of PDF files for obtaining sensitive information such as login credentials.
Increased security measures implemented by Microsoft have made it harder for cybercriminals to use macros in Office documents in their email campaigns, with PDF files a good alternative. Malicious links can be embedded in PDF files that drive victims to web pages where credentials are harvested. By using PDF files to house the links, they are less likely to be blocked by email security solutions.
Over the past few months, PDF files have been increasingly used to distribute malware. One of the currently active campaigns uses malicious emailed PDF files to infect users with DarkGate malware. DarkGate malware is offered under the malware-as-a-service model and provides cybercriminals with backdoor access to infected devices. In this campaign, emails are sent to targets that contain a PDF attachment that displays a fake image from Microsoft OneDrive that suggests there was a problem connecting which has prevented the content from being displayed. The user is given the option to download the PDF file; however, the downloaded files will install DarkGate malware.
In this campaign, clicking the link does not directly lead to the malware download, instead, the click routes through an ad network, so the final destination cannot be identified by checking the link of the download button. Further, since the ad network uses CAPTCHAs, the threat actors can make sure that the destination URL is not revealed to email security solutions. If the CAPTCHA is passed, the user will be redirected to the malicious URL where they can download the file. This is often a compressed file that contains a text file and a URL file, with the latter downloading and running JavaScript code which executes a PowerShell command that downloads and executes the malicious payload.
PDF files have been used in many other malware campaigns, including those that distribute the Ursnif banking Trojan and WikiLoader malware. Recent campaigns distributing these malware variants have used parcel delivery lures with PDF file attachments that contain a link that prompts the user to download a fake invoice. Instead of the invoice, a zip file is downloaded that contains a JavaScript file. If executed, the JavaScript file downloads an archive, extracts the contents, and executes the malware payload. Another campaign uses PDF files to install the Agent Tesla remote access trojan using Booking.com-related lures.
Not only do PDF files have a greater chance of evading email security solutions, they are also more trusted by end users than Office file attachments. Security awareness campaigns are often focused on training employees about the risks of phishing, such as clicking links in unsolicited emails and the risks of opening unsolicited office files. Malicious email campaigns using PDF files arouse less suspicion and end users are more likely to be tricked by these campaigns.
It is important for businesses to incorporate PDF files into their security awareness training and phishing simulation campaigns to better prepare employees for this growing threat. With SafeTitan, adding new content in response to the changing tactics, techniques, and procedures of threat actors is a quick and easy process. Get in touch with the TitanHQ team today to find out more about the SafeTitan security awareness training and phishing simulation platform and discover the difference the solution can make to your organization’s security posture.
by Jennifer Marsh | Feb 18, 2024 | Phishing & Email Spam |
A large-scale phishing campaign has been identified that has already targeted many thousands of organizations in the United States and could be expanded geographically. The purpose of the campaign is to distribute Bumblebee malware, a malware loader that was first identified in 2022 and is thought to be a replacement for the widely used BazarLoader malware loader. Bumblebee malware is used for gaining initial access to networks and has been used in many successful cyberattacks. The malware is rented out to cybercriminals or access to compromised networks is sold to cybercriminal groups such as ransomware gangs. The malware has been linked to several high-profile threat actors and notorious ransomware gangs, including the now-defunct Conti ransomware group.
Over the past four months, Bumblebee malware has not been detected but it has now returned with a massive campaign. A variety of lures are used in phishing emails, which incorporate social engineering techniques to trick the recipients into downloading and executing the malware. For instance, the latest campaign included thousands of emails using the subject Voicemail February, with messages indicating the user had missed a voice call. The emails instructed the recipient to download the recording, the opening of which triggered the infection process. Other emails used in the campaign have used Word documents with malicious macros with the emails spoofing trusted companies, such as the electronics firm Humane. Rather than include the document attached to the email, a OneDrive link was provided in the email from which the document could be downloaded. This was an effort to prevent detection by email security solutions, as OneDrive is a legitimate and trusted service. Previous campaigns have used DocuSign branded emails that trick users into downloading a zipped ISO file from OneDrive.The group is known to hijack email threads to make it appear that the emails are responses to previous conversations with contacts.
Multiple threat actors are believed to rent out the malware, including the initial access brokers who work with ransomware gangs. Bumblebee malware infections are often accompanied by other payloads, including Cobalt Strike, Meterpreter, Sliver, and shellcode, and often lead to ransomware attacks. To combat Bumblebee malware infections, businesses should implement robust defenses against phishing. An advanced email security solution is required with AI and machine learning capabilities that can detect novel phishing attempts. SpamTitan Plus uses a machine learning algorithm that can identify emails that deviate from those typically received by a business, links are rewritten and followed and the destination URL is assessed. All emails are subjected to antivirus scans and suspicious attachments are sent to a Bitdefender-powered sandbox for behavioral analysis.
Security awareness training should be provided to the workforce to improve resilience to phishing attempts by teaching security best practices and how to identify phishing attempts. SafeTitan is a comprehensive security awareness training platform and phishing simulator that is updated with new content regularly in response to changing phishing tactics, including those used in Bumblebee campaigns. It is also recommended to implement multi-factor authentication on accounts, perform daily backups and store them offline, implement next-generation antivirus technology on endpoints, and implement network hierarchy protocols and network segmentation to prevent lateral movement.
by Jennifer Marsh | Feb 18, 2024 | Network Security |
If disaster strikes and you discover your network has been encrypted with ransomware and sensitive data has been stolen, you are faced with two choices. Pay the ransom and hope that the attackers are true to their word and will delete the stolen data and provide the decryption keys to allow you to recover your data or attempt to recover from the attack on your own.
There will be several factors that will influence that decision. One of the first questions that must be answered is whether a viable backup exists of your encrypted data, and ideally, one that allows you to recover individual files rather than restoring systems to the date of the most recent backup. Backups are often created but are not tested, and it is only when they are needed that an organization discovers that the backups cannot be used to restore data. Restoring data from backups may result in significant data loss.
If files can be recovered, then it may not be necessary to pay the ransom; however, this is why many ransomware gangs steal data in addition to encrypting files. The exposure of data – publication on a data leak site – or the sale of that data is often far more damaging to a company than the losses due to file encryption. Data leaks can cause significant reputational damage and put organizations at risk of costly lawsuits and regulatory penalties. Determining what data has been stolen is critical to the decision about whether or not to pay the ransom.
For many companies, especially critical infrastructure entities, the ransom demand is far lower than the cost of downtime during the incident response and recovery phase. Backups may allow files to be recovered but that does not mean a quick recovery and extended downtime can be hugely expensive. Paying the ransom may be the most cost-effective option as recovery will often be far quicker.
Companies with cyber insurance policies may be able to claim the ransom payment; however, many insurers now exclude ransomware attacks so it is important to determine, as far as possible, whether the insurance company will pay out and how much will be paid. Some insurers have restrictions in their policies and paying the ransom may invalidate the insurance policy. Cyber insurance is expensive and if a claim against a policy is successful, it is likely that future premiums will increase.
The threat actor that conducted the attack may be on a sanction list, which means that payment may not be permitted. In the United States, the Office of Foreign Asset Control (OFAC) has sanctioned several individuals who have conducted ransomware attacks, and OFAC prohibits payments to sanctioned individuals. If a company makes a ransom payment to a sanctioned individual it is a serious criminal offence, punishable with a severe financial penalty and custodial sentences.
Law enforcement agencies generally advise against paying a ransom for several reasons. If ransoms are paid it encourages ransomware gangs to conduct more attacks and gives them the funds they need to continue and expand their malicious activities. There is also no guarantee that the ransomware group will provide the decryption keys, which means payment may be made and data will remain encrypted. Around 90% of all companies that pay a ransom following a ransomware attack are unable to recover all of their data, and less than a third are able to recover half of their data. Data is often corrupted and decryption keys often do not work.
Paying a ransom to prevent the publication of stolen data may result in your company being removed from a publicly accessible data leak site but it does not mean that the data will be deleted. It may still be sold or misused. There is also a risk that after paying the ransom, another ransom demand will be issued. Any company that is willing to make a payment could face further extortion attempts and multiple ransomware attacks. A study by Cybereason found that 78% of companies that paid a ransom went on to suffer a second attack, with 36% of those attacked by the same threat actor and 42% attacked by a different threat actor.
The decision about whether to pay a ransom is not straightforward, and all factors must be carefully evaluated, but paying a ransom is a gamble and it is one that may not pay off. It should therefore only be considered as the last resort when all other options have been explored and ruled out.
The best approach as far as ransomware is concerned is to take proactive steps and prepare for an attack. You must ensure that you have robust data backup systems in place, with backups stored securely where they cannot be encrypted. Those backups must be tested to make sure file recovery is possible in the event of an attack to keep all options on the table.
Given the number of attacks that are now being conducted, it is important to make sure you have robust defenses in place to protect against all initial access vectors, and that is an area where TitanHQ can help. TitanHQ has a suite of cybersecurity solutions that can improve your security posture and help you recover from an attack should disaster strike. Give the team a call today for advice on how you can improve your defenses against ransomware attacks.
by Jennifer Marsh | Jan 31, 2024 | Phishing & Email Spam |
Phishing has long been the most common way that cybercriminals gain initial access to business networks. A successful attack allows a threat actor to steal credentials and gain a foothold in the network, providing access to sensitive data and giving them the access they need to conduct a range of nefarious actions. Phishers must develop campaigns that are capable of bypassing email security solutions and use lures that are likely to fool end users into disclosing their credentials or opening malicious email attachments. In recent years, the entry barrier for conducting phishing campaigns has been significantly lowered through phishing-as-a-service (PhaaS), which has proven popular with would-be cybercriminals.
Phishing kits are offered that provide everything needed to launch successful phishing campaigns, without having to spend hours setting up the infrastructure, creating convincing emails, and incorporating anti-detection measures to ensure emails land in inboxes. A relatively new phishing kit is proving to be particularly popular. The Greatness phishing kit has been available since mid-2022 and lowers the bar for starting phishing campaigns, requiring a payment of just $120 a month to use the kit. The Greatness phishing kit allows emails to be customized to suit the hacker’s needs and add attachments, links, or QR codes to the emails. The kit makes it easy to generate and send emails and create obfuscated messages that can bypass many cybersecurity solutions and land in inboxes. The kit also supports multi-factor authentication (MFA) bypass by performing a man-in-the-middle attack to steal authentication codes and can be integrated with Telegram bots.
The kit has an attachment and link builder that creates convincing login pages for harvesting Microsoft 365 credentials and even pre-fills the victim’s email address into the login box, only requiring them to enter their password. The kit also adds the targeted company’s logo to the phishing page along with a background image that is extracted from the targeted organization’s M365 login page. As such, the Greatness phishing kit is aimed at individuals looking to target businesses and can be easily purchased through the developer’s Telegram channel. There were several spikes in Greatness phishing kit activity in 2023, with the latest detected in December 2023 and the increased activity has continued into 2024. Phishing kits such as Greatness significantly lower the barrier for entry to cybercrime and make it as easy as possible to start phishing, and the low cost of the kit has made it an attractive option for would-be cybercriminals. This phishing kit is used to target Microsoft 365 users, and the emails can be convincing and are likely to fool many end users.
The key to defending against phishing attacks is to implement layered defenses to ensure that a failure of one defensive measure does not leave the business unprotected. TitanHQ has developed a suite of cybersecurity solutions for businesses and the MSPs that serve them to improve their defenses against phishing, including AI-generated phishing emails and sophisticated phishing kits capable of stealing passwords and MFA codes.
TitanHQ’s PhishTitan provides advanced phishing protection and remediation for Microsoft 365. TitanHQ’s proprietary machine-learning algorithm integrates directly with Microsoft 365 and catches and remediates sophisticated phishing including AI-generated phishing emails, business email compromise, spear phishing, and phishing attacks that bypass MFA. The solution augments rather than replaces EOP and Defender and catches the phishing attempts that those defensive measures often miss.
PhishTitan uses AI and a large language model (LLM) with proprietary threat intelligence currently not found in any other anti-phishing solution on the market, and will scan attachments for malicious links and malware, rewrite URLs, apply banner notifications, and block malicious links. PhishTitna also provides time-of-click protection to combat the weaponization of links after delivery. The solution uses machine learning algorithms to scan the message body to assess email content and identify words, phrasing, and formatting of emails indicating a phishing attempt, and will learn over time and become even more effective.
PhishTitan is suitable for businesses of all types and sizes and has been developed from the ground up to meet the needs of MSPs. The solution can be set up in less than 10 minutes, and MSPs can add new clients in less than 6 minutes and start protecting them from highly sophisticated phishing attacks. For maximum protection, TitanHQ also offers WebTitan DNS filter to protect against web-based attacks, ArcTitan email archiving for security and compliance, EncryptTitan for email encryption, SafeTitan for security awareness training and phishing simulations, and the SpamTitan Suite of email security solutions. All products are available on a no-obligation, 100% free trial and product demonstrations are available on request. For more information on PhishTitan and other TitanHQ solutions, give the TitanHQ team a call today.
by Jennifer Marsh | Jan 30, 2024 | Phishing & Email Spam |
Phishing is most commonly associated with email; however, there are a variety of ways that cybercriminals can make contact with end users and other forms of phishing are becoming much more common. Smishing is the use of SMS messages for phishing which targets users via their smartphones, which tend to have far weaker security controls than laptops and PCs. Voice phishing is also common, where malicious actors trick people into disclosing sensitive information or installing malware over the phone. Phishing can also take place via social media networks and video conferencing platforms such as Microsoft Teams.
A campaign has recently been identified that uses Microsoft Teams group chat requests for phishing. A threat actor appears to be using a compromised account to send Teams group chat invites to thousands of individuals. The compromised User’s Teams account is likely to have been compromised in a phishing, credential stuffing, or brute force attack. This campaign aims to install malware on users’ systems – a malware variant called DarkGate. DarkGate malware was first identified in 2018 and is a remote access Trojan that can install a hidden virtual network computing (hVNC) module to provide remote access to a victim’s device. The malware has keylogging and information-stealing capabilities and can steal cookies and information stored in browsers, Discord tokens, and cryptocurrency wallets. The malware can also download other payloads such as ransomware.
In this campaign, if a user accepts the group chat request, the threat actor uses social engineering techniques to trick them into downloading a file to their device. The user is tricked into thinking that they are downloading a PDF file, but they download an executable file. The file – Navigating Future Changes October 2023.pdf.msi – has a double extension. On Windows systems, which are typically configured to hide known file extensions, the file will be displayed as Navigating Future Changes October 2023.pdf. If the user double-clicks on the file, the malware will be installed and will connect to its command-and-control server, giving the treat actor control over the user’s device.
Microsoft Teams has become a popular target for threat actors for malware distribution. There are around 280 million monthly users, and the default settings allow Microsoft Teams users to receive chat requests from external Microsoft Teams users. While most users will have antivirus software on their devices for detecting malware, DarkGate malware is stealthy and often evades antivirus software. There are several steps that businesses can take to combat these attacks. The most important of which is to disable External Access in Microsoft Teams unless it is absolutely necessary for day-to-day business use. This will ensure that users can only receive chat requests internally, which will greatly reduce risk.
Another important measure is to provide regular security awareness training to the workforce. Employees should be taught cybersecurity basics such as how to recognize a phishing attempt and should be made aware of the latest tactics used by cybercriminals in attacks on employees. Training should be provided continuously, with short training sessions conducted every month. When new phishing techniques are identified, short training modules can be pushed out to employees to make them aware of the threat. With the SafeTitan security awareness training platform this is easy. The platform has a wide range of CBT content, with training modules lasting no more than 10 minutes so they are easy to fit in to workflows.
If you do not currently provide regular security awareness training to your workforce, contact TitanHQ about SafeTitan. Product demonstrations can be arranged on request, and you can test the product for yourself in a free trial.
by Jennifer Marsh | Jan 29, 2024 | Phishing & Email Spam |
Alarmingly, 71% of Microsoft business users report that they suffer at least one compromised account each month. The biggest cause of account compromises is phishing. Phishing is the fraudulent practice of making contact with an individual and tricking them into taking an action that the attacker wants, which is usually to disclose their credentials to allow an attacker to remotely access their account. Phishing attacks usually involve impersonation, where the attacker claims they are an authority figure, such as the CEO of the company, a friend or colleague, or a representative of a reputable company.
The capturing of credentials usually occurs on a website with initial contact with the individual usually occurring via email, although phishing attacks are also conducted via SMS messages (smishing), telephone (vishing), social media networks, and instant messaging services.
Phishing targets members of the workforce, including employees and board members, and it is the responsibility of security teams and managed service providers to block as many phishing attempts as possible and ensure that if phishing attempts do bypass defenses, end users have been trained to recognize phishing attempts and report them. Security teams naturally concentrate on the former, as phishing will only succeed if an attacker can make contact. The problem is that cybercriminals are developing highly sophisticated phishing campaigns that are difficult for traditional email security solutions to identify and block.
Cybercriminals target Microsoft 365 credentials as they provide access to a wealth of sensitive data and to email accounts which can be used to conduct further phishing attacks internally and on the company’s customers and vendors. Once credentials have been obtained, they can be used for a much more extensive attack on a company. TitanHQ has received feedback from its managed service provider (MSP) customers that Microsoft 365 phishing is the number one problem to solve in the email security community.
TitanHQ already has products that can protect against phishing. There is the SpamTitan suite of products for email security, WebTitan for protecting against web-based attacks, including blocking access to the websites where credentials are obtained, and the SafeTitan security awareness and phishing simulation platform for educating the workforce on cybersecurity threats and testing resilience through simulated phishing emails.
What was needed, however, was a new solution that is specifically focused on phishing. “We therefore allocated resources and investment to develop a solution with new, cutting-edge, robust, fast phishing threat intelligence driven by a team of security specialists,” said TitanHQ CEO, Ronan Kavanagh. “We are pleased to be able to meet the market’s needs with a product that delivers.”
PhishTitan has been developed to help MSPs and businesses improve their phishing defenses for Microsoft 365, as Microsoft’s defensive measures – EOP and Defender – are failing to identify and block many phishing attempts. PhishTitan is a next-generation phishing protection and remediation solution for Microsoft 365, which integrates TitanHQ’s proprietary machine-learning algorithm directly with Microsoft 365 to augment EOP and Defender and catch and remediate the sophisticated phishing attacks that EOP and Defender miss.
PhishTitan has been developed from the ground up to meet the needs of MSPs and allow them to block more phishing attempts on their clients and remediate phishing attempts rapidly, without having to commit extensive resources to managing email security for each client.
PhishTitan is functionally rich, offering multiple integration options, and has granular policy controls, a full reporting suite, and provides comprehensive protection. Businesses can set up the solution themselves in around 10 minutes, and MSPs can add new clients in just 6 minutes.
PhishTitan Features
- AI-driven solution that is capable of identifying and blocking zero-day threats
- Scans and blocks malicious links
- Scans and neutralizes malware
- Detects unique and sophisticated phishing and BEC attacks over and above those detected by EOP and Defender
- Rewrites URLs and applies banner notifications
- Time of click protection to combat links that are weaponized after delivery
- Protection against data leakage of sensitive company information
- Instant remediation across an entire tenant
- Real-time visibility and reporting suite on emerging threats
- Phishing intelligence data that is unmatched in visibility, coverage, and accuracy.
If you are struggling to block phishing attacks on your M365 accounts or are a managed service provider who wants to improve phishing protection for your customers, give the TitanHQ team a call to find out more about how PhishTitan works and how it can improve your defenses against phishing. Product demonstrations can be arranged on request and PhishTitan is available on a free trial.
by Jennifer Marsh | Jan 26, 2024 | Phishing & Email Spam |
There has been a change in the distribution method of PikaBot malware, which is now being pushed in a malvertising campaign. Previously PikaBot was only distributed via phishing emails. PikaBot malware was first identified in early 2023 and is a modular malware Trojan that consists of two components: a loader and a core module. The malware allows the operator to gain remote access to compromised systems and execute a range of commands, including shell commands and fetching and running EXE or DLL files. The malware also allows downloads of additional malware payloads and post-compromise tools. The malware is known to be used by a prolific threat actor tracked as TA577, with infection leading to the deployment of Cobalt Strike.
The malvertising campaign uses Google Ads for AnyDesk, a remote desktop application popular with businesses. Google has security checks in place to prevent malicious adverts from being displayed and these are being bypassed by using a tracking URL with a legitimate marketing platform, with the custom domain for the redirect protected by Cloudflare. The malicious adverts are displayed when users search for popular software such as Zoom, Advanced IP Scanner, and WinSCP.
If the Ad is clicked by a user, they are directed to a spoofed AnyDesk download site that will deliver an MSI installer hosted on Dropbox. Checks are also performed before redirection to the malicious site, with redirection not occurring if fingerprinting checks determine the request is originating from a virtual machine. Before the MSI download is initiated, another check is performed to test whether the request is coming from a virtual environment. On download, Pikabot uses an injector to run anti-analysis tests and will only decrypt and inject the core module payload if these checks are passed, otherwise, execution is aborted.
The use of malvertising in malware campaigns is increasing and this initial access vector is often successful as most security awareness training programs concentrate on phishing. It is important to ensure that malvertising is covered in security awareness training sessions and that employees are told about the risks of downloading software and are made aware of the checks they should perform to make sure the source of the software is legitimate.
Businesses can further protect themselves against malware distribution via the internet with a DNS filter. The WebTitan DNS filter can be used to control the web pages that can be accessed by employees. Access can be restricted to whitelisted sites, and websites can be easily blocked by category. WebTitan is constantly updated by multiple threat intelligence feeds and will block access to all URLs known to be used for malware distribution. While this malvertising campaign involves many checks to determine if a web filter is accessing the content, which may result in the content being accessible, WebTitan can be configured to block the downloading of certain files from the Internet, including executable files such as MSI files. Not only will this help to prevent malware downloads, it will also allow IT teams to curb shadow IT – unauthorized software downloads by employees – which are a security risk.
The WebTitan DNS Filter and the SafeTitan Security Awareness Training Platform are both available on a free trial and product demonstrations can be arranged on request. For further information give the TitanHQ team a call.
by Jennifer Marsh | Jan 26, 2024 | Phishing & Email Spam |
Ransomware attacks hit record levels in 2023 and are set to increase further along with the phishing attacks that provide ransomware groups with initial access to business networks.
The ransomware remediation firm Coveware reports that ransomware groups are now much less likely to receive ransom payments, with only 29% of victims choosing to pay up to obtain the keys to decrypt their data and prevent their data from being added to data leak sites. At the start of 2019, 85% of victims of ransomware attacks paid the ransom.
There are several reasons for the fall in payments. First, businesses are better prepared and have incident response plans for attacks that minimize disruption and more effective backup strategies that allow them to restore data themselves. While they are unable to prevent the leaking of sensitive data if they choose not to pay the ransom, there is widespread mistrust that paying the ransom will actually prevent data from being leaked or sold.
Falling revenues from attacks mean ransomware actors need to increase the number of attacks they conduct in order to maintain their incomes. NCC Group reports an 84% increase in attacks between 2022 and 2023, and 2024 is likely to continue to see high numbers of attacks and the UK’s National Cyber Security Centre (NCSC) has warned that ransomware attacks are likely to increase.
The NCSC predicts that by 2025, and perhaps sooner, generative AI and large language models will be extensively used by cybercriminals and will allow them to craft phishing and spear phishing emails and develop new social engineering tactics to conduct more effective phishing campaigns. Since phishing is one of the most common initial access vectors in ransomware attacks, the NCSC predicts that AI will contribute to the global ransomware threat in the near term and other types of cybercrime that rely on phishing and social engineering.
The use of AI will make it more difficult for security professionals to identify and block phishing emails and social engineering attempts and it will be much harder for end users to differentiate between genuine emails and AI-generated phishing attempts. Generative AI tools also lower the barrier for would-be cybercriminals looking to conduct phishing and ransomware attacks, allowing novice and less skilled threat actors to conduct attacks successfully. This has already been the case with ransomware-as-a-service (RaaS), and generative AI-as-a-service may also start to be offered. Generative AI tools are also allowing threat actors to process and analyze the data stolen in these attacks more efficiently.
“Threat actors, including ransomware actors, are already using AI to increase the efficiency and effectiveness of aspects of cyber operations, such as reconnaissance, phishing, and coding,” explained NCSC. “Enhanced access will likely contribute to the global ransomware threat over the next two years.”
The NCSC paints a bleak picture but while AI tools can be used for offensive purposes, they can also be used by network defenders. TitanHQ’s cybersecurity solutions already use AI and machine learning tools for identifying phishing and other email threats. These tools are able to identify novel phishing threats, including those that are created using generative AI tools.
If you want to improve your defenses against malicious use of AI, speak with TitanHQ about how you can add advanced AI-driven detection capabilities to your cybersecurity arsenal and better defend your networks and data from increasingly sophisticated cyberattacks.
by Jennifer Marsh | Jan 25, 2024 | Phishing & Email Spam |
QR codes are a convenient way of transmitting information, especially URLs. They can be scanned with a smartphone and direct the user to a website. They are on flyers, posters, and other marketing material to quickly direct users to a website to find out more information, greatly improving the response to marketing campaigns. Use of these codes has grown and they are now found everywhere, even in restaurants to direct diners to menus. Unfortunately, QR codes are also perfect for scammers for stealing sensitive information and distributing malware, and QR codes are now being extensively used in phishing campaigns (quishing) in place of embedded URLs. The advantage of this is that they make it hard for users to check the destination of the URL before clicking and email security solutions are now designed to follow QR codes. According to Check Point, there was a 587% increase in QR code phishing attacks between August and September 2023 and recently detected 20,000 instances of QR code-based attacks over a 2-week period.
Campaigns have recently been detected that incorporate conditional redirection based on the user’s device, browser, screen size, and many other parameters, tailoring each attack to the individual via the same QR code. In one of these campaigns, users were directed to a credential harvesting page, with the redirection chain adjusted based on the fingerprinting of the user’s device. Similar campaigns are conducted to direct users to malware distribution sites. QR codes have also been used to direct users to deep fake YouTube videos, where celebrities appear to be endorsing investment schemes, usually related to cryptocurrency, where people are tricked into investing with a promise that they can rapidly double their money or get even better returns.
Email security solutions are designed to assess messages for phishing content, check embedded URLs to determine if they link to malicious websites, and scan email attachments to check for malware, but they are not suited to checking QR codes to determine where the user will be directed. Further, QR codes move the threat to a different device. QR code phishing emails are likely to be received on a company-owned laptop or PC, but the user is then required to switch to their mobile phone to scan the QR code, and mobile devices typically lack the same level of protection making it more likely that the attack will go undetected.
The best defense against these attacks is user education. Security awareness training should cover quishing to make employees aware of this increasingly popular tactic and the threat that QR codes pose. With SafeTitan it is easy to add new training content to your security awareness training programs and push out these training modules to all users. When any new threat is detected, you can add educational content to your training program and push that content out to all users, user groups, or individuals. All training modules last a maximum of 10 minutes, so they are easy to fit into busy workflows. SafeTitan also includes a phishing simulator that allows you to send out fake quishing emails to the workforce to see who opens the emails and responds.
For further information on security awareness training with SafeTitan and how you can improve your defenses against all types of cyberattacks, give the TitanHQ team a call.
by Jennifer Marsh | Jan 16, 2024 | Phishing & Email Spam |
Phishing is the fraudulent practice of sending messages, typically emails, that trick the recipient into doing something that they normally would not do, such as disclosing sensitive information or installing malware on their device. Phishers often include a link to a website that spoofs a well-known brand and victims are tricked into disclosing sensitive data or malicious files are attached to emails. Email security solutions are now much better at detecting malicious hyperlinks, and advanced email security solutions such as SpamTitan Plus can detect all known malware and have email sandboxing for behavioral analysis of suspicious emails to identify and block zero-day malware threats.
Cybercriminals Turn to Callback Phishing to Evade Cybersecurity Solutions
The first goal of a phishing attack is to get a message, be that an email, SMS, or instant message to an end user, and one of the ways that this is achieved is by sending emails with no malicious content – no hyperlinks or email attachments. Instead, the messages have a realistic call to action that requires immediate attention, and a phone number is provided in the email that the recipient must call to address the pressing problem that is outlined in the email. The phone line is manned by the threat actor who then talks the user through performing certain actions that provide remote access to their device.
Callback phishing typically involves an email warning the recipient about a charge for a product that is about to be taken, such as the expiry of a free trial or the end of a subscription term. The charge is excessive and the number provided in the email must be called to stop the charge. One such campaign that has recently been uncovered involves a fictitious charge for an antivirus subscription. In one of these attacks, the threat actor spoofs the antivirus software provider Norton. The email advises the recipient that the subscription period has come to an end and a charge for the next subscription period will be applied – $349.95. Naturally, such a high charge for a product would prompt many people to call the number to block it.
As with other callback phishing campaigns, the attacker tricks the recipient into downloading a program to their device that they are told is necessary to prevent the renewal of the subscription. The program gives the attacker remote access to the user’s device. Once access has been gained, the attacker can conduct a variety of nefarious activities.
Victim Transferred $34,000 to Attacker’s Account
In one of these scams, after access was gained to a victim’s device, the attacker transferred $34,000 from the user’s account. After providing the attacker with remote access to their laptop, the victim was instructed to perform other actions, one of which was entering their credentials into a phishing page. The victim was told that the payment for the antivirus software had already been taken, so a refund needed to be processed. The attacker then told the victim that an error had been made and a refund of $34,000 had been deposited in his account and immediate action was required to correct the error to avoid legal trouble.
The attacker remained on the phone while the victim called his bank, and while the victim was on the phone, the attacker transferred $34,000 from the victim’s Money Market account to his checking account. When the victim saw the $34,000 deposit, he assumed it to be the refund from Norton, and arranged the transfer to the bank account provided by the attacker. The attacker told the victim that in order not to arouse suspicion at the bank, he should inform the bank that the payment was for a vehicle. The victim was unable to see the malicious activity as the attacker had overlayed a blue screen on his laptop.
In this case, suspicions were raised and the funds were put into a suspense account at the recipient bank. U.S. Secret Service Special Agent Iris Joliff was able to obtain a seizure warrant from a judge allowing the money to be recovered; however, scams such as these are often only detected when the transferred funds have been withdrawn from the attacker-controlled account.
Improve Resilience to Callback Phishing with SafeTitan
Email security solutions may be effective at blocking malicious attachments and hyperlinks in emails, but they can rarely identify callback phishing scams as it is difficult to determine if a phone number is malicious. The most effective way that businesses can combat callback phishing is through security awareness training. Callback phishing should be covered in security awareness training sessions and also added to phishing simulation campaigns, to test whether the training has been understood and is being applied. SafeTitan from TitanHQ makes this easy, as callback phishing modules can easily be added to training courses and SafeTitan also includes a phishing simulator with phishing templates to test resilience to callback phishing and identify individuals who require further training in this area.
For further information on the SafeTitan platform and advice on how to further improve your defenses against phishing, give the TitanHQ team a call.
by Jennifer Marsh | Jan 14, 2024 | Industry News, Phishing & Email Spam |
TitanHQ is proud to announce the addition of a new solution to its cybersecurity portfolio that helps businesses combat the growing threat of phishing. PhishTitan provides powerful phishing protection for Microsoft 365 that is capable of catching and remediating sophisticated phishing attempts, including spear phishing attacks, business email compromise, phishing emails generated by artificial intelligence tools, and zero-day phishing threats that Microsoft’s native defenses for M365 fail to detect and block. It is these threats that pose the biggest threat since they are missed by Microsoft’s email security defenses and are difficult for employees to identify as malicious since they lack many of the red flags that employees are taught to look out for in security awareness training programs.
PhishTitan incorporates TitanHQ’s proprietary machine-learning algorithm, which integrates directly with M365. PhishTitan performs an AI-driven analysis of inbound emails (internal and external) which includes textual analysis, link analysis, and attachment scanning. Links are analyzed via multiple curated feeds that constantly update the solution to allow malicious websites linked to phishing and malware distribution to be identified and blocked. Phishing emails often include links that have been masked to hide the true destination URL. PhishTitan rewrites URLs to show the true destination. One tactic used by phishers to bypass email security solutions is to only weaponize links in emails after delivery. To protect against this tactic, PhishTitan checks inbound emails before delivery to inboxes and also offers time-of-click protection against malicious links in emails.
Attachments are scanned with twin antivirus engines, and suspicious email attachments are sent to the sandbox for behavioral analysis. Machine learning detection models scour the body of emails looking for tell-tale signs of phishing and adapt to constantly changing phishing tactics. The machine learning algorithms also learn from reports of phishing attempts by end users, which they can report with a single click using a TitanHQ-supplied Outlook add-in. PhishTitan can also be configured to apply banner notifications to external emails and protect against the leakage of sensitive company information.
The solution has been designed to meet the needs of businesses of all types and sizes and has been developed from the ground up to meet the needs of managed service providers (MSPs) to allow them to easily add advanced phishing protection to their service stacks. It takes around 10 minutes to set up the solution, and around 6 minutes for MSPs to onboard new clients.
The solution was trialed across the TitanHQ user database of more 12,000 customers and 3,000 MSPs in Q4, 2023, with TitanHQ customers reporting that the solution outperforms their existing anti-phishing solutions. TitanHQ is now pleased to start offering the new product to new customers. For more information on PhishTitan phishing protection Microsoft 365 contact TitanHQ today. PhishTitan is available on a 14-day free trial and product demonstrations can be arranged on request to show you how easy the product is to use and exactly what it can do.
“A staggering 71% of MS business users suffer at least one compromised account monthly. With this in mind, the overwhelming feedback from our customer base has been that phishing is the number one problem to solve in the email security community,” said TitanHQ CEO, Ronan Kavanagh. “We therefore allocated resources and investment to develop a solution with new, cutting-edge, robust, fast phishing threat intelligence driven by a team of security specialists. We are pleased to be able to meet the market’s needs with a product that delivers.”
by Jennifer Marsh | Dec 28, 2023 | Network Security, Phishing & Email Spam, Security Awareness |
The cyber threat landscape is constantly changing, with cybercriminals and nation-state actors developing new tactics, techniques, and procedures for use in attacks on businesses to steal intellectual property and sensitive customer data, and for extortion. Threat actors gain access to internal networks by exploiting human weaknesses through social engineering and phishing, exploiting vulnerabilities such as unpatched and misconfigured software, and using malware for remote access.
The latter has seen an increase in 2023, with Kaspersky reporting in its end-of-the-year statistics report that malicious file detections have increased by 3% from 2022, with an average of 411,000 malicious files detected each day. The biggest increase was malicious desktop files such as Word documents, Excel spreadsheets, and PDF files, which are used for distributing malware. More than 125 million malicious desktop files were detected in 2023, with documents such as Word files and PDF files seeing the biggest increase, up 53% from 2022.
The company attributed the large increase to the number of email phishing attacks using malicious PDF files. PDF files have become more popular due to the steps Microsoft has taken to block email attacks using Office documents and spreadsheets. In the summer of 2022, Microsoft started blocking Visual Basic Applications (VBA) macros in Office apps by default to stop malicious actors from using them to deliver malware. Macros are now blocked by default in all Office documents that are delivered via the Internet. Threat actors responded by switching to other file formats for delivering malware such as LNK, ISO, RAR, ZIP, and PDF files, with the latter commonly used to hide links to malicious websites from email security solutions. These links direct users to malicious websites where drive-by malware downloads occur and also to phishing sites that steal credentials. The most common malware types in 2023 were Trojans such as Magniber, WannaCry, and Stop/Djvu, with a notable increase in backdoors, which provide threat actors with remote access to victims’ devices and allow them to steal, alter, and delete sensitive data and download other malware variants such as ransomware.
These email-based attacks usually require some user interaction to succeed, such as opening a malicious file or clicking a link. Threat actors are adept at social engineering and trick users into taking the action they need but the availability of artificial intelligence tools has made social engineering even easier. AI has significantly lowered the entry barrier into cybercrime and can be used by anyone to create convincing phishing lures and social engineering tricks. Artificial intelligence tools are also being leveraged to develop new malware variants faster than before, which allows threat actors to defeat signature-based antivirus and antimalware solutions.
With cyberattacks increasing in both number and sophistication, businesses need to ensure they have appropriate defenses in place. To defend against attacks, businesses need to take a defense-in-depth approach to security and implement multiple overlapping layers of protection. Should one single component fail to detect a threat, others will be in place to provide protection. Endpoint detection solutions such as antivirus software are essential. These solutions work after malware has been delivered and can detect and neutralize the threat; however, multiple layers of security should be in place to make sure threats are not delivered, especially due to the increase in zero-day malware threats – novel malware variants that have yet to have their signatures added to the malware definition lists used by these solutions.
TitanHQ offers three layers of protection through SpamTitan Email Security, Web Titan Web Filtering, and SafeTitan Security Awareness Training. SpamTitan is an advanced email security solution that protects against all email threats, including known and zero-day threats. SpamTitan offers protection against malicious links in emails, and features dual antivirus engines and email sandboxing to protect against malware threats, with the latter used to detect previously unseen malware variants. SpamTitan also uses artificial intelligence and machine learning to predict new attacks.
WebTitan is a leading DNS filtering solution that allows businesses to carefully control the web content that can be accessed via wired and wireless networks. The solution blocks access to known malicious websites, and high-risk websites, and can be configured to block the file types that are commonly used for malware delivery, such as executable files. SafeTitan is a comprehensive security awareness training and phishing simulation platform for teaching employees security best practices and improving resilience to the full range of cybersecurity threats. The platform provides training in real-time in response to poor security behaviors, with training sessions triggered immediately when bad behaviors are detected. This ensures that training is delivered when it is likely to have the biggest impact.
To improve protection against the full range of cyber threats, give the TitanHQ team a call today. You can discuss your needs and explain the current security solutions you have, and the TitanHQ team will be more than happy to talk about the TitanHQ solutions that can plug the security gaps. All solutions are competitively priced and are available on a free trial to allow you to test them thoroughly before making a purchase decision.
by Jennifer Marsh | Dec 23, 2023 | Phishing & Email Spam |
A new callback phishing campaign has been detected that uses Google Forms to add credibility to the campaign. Callback phishing involves sending an email and tricking the recipient into calling a customer service helpline, where they are convinced to download software that provides the attacker with remote access to their device. Since the emails contain no malicious content, only a phone number, these emails are usually delivered to inboxes.
A typical campaign involves an email about an impending charge for a subscription for software or a service, payment for which is about to be taken shortly. The user is told that they must respond within 24 hours if they have any dispute and that the subscription will auto-renew if no action is taken. Companies typically impersonated in these attacks include Netflix, Hulu, Disney+, Masterclass, McAfee, Norton, and GeekSquad.
The impending charge is excessive, typically $50 to $500, and the only way to prevent the payment is to call the customer service number included in the email. Subscriptions for software, streaming platforms, and other services are often set to auto-renew by default, and many people end up paying for another term even if they have discontinued using that service. The lure is therefore plausible, and since the charge is excessive, the recipient is likely to make the call.
The phone number is manned by the threat actor who pretends to be customer support and helps the user block the charge; however, in order to do so, software must be downloaded onto the user’s device. The user is convinced to install the software, the threat actor appears to remove the offending software, and the payment issue is resolved; however, the threat actor has installed malware that provides access to the user’s device.
In late 2020/ early 2021, this method was used in BazarCall attacks, so named because they were conducted to deliver BazarLoader malware. The malware is used to download additional malware payloads to the user’s device, such as ransomware. A new version of this campaign has recently been detected that employs Google Forms to add legitimacy to the campaign. Google Forms is free to use and allows forms to be easily created for surveys and quizzes, which can be integrated with websites or shared. In the latest BazarCall campaign, Google Forms is used to create details of a fake transaction, complete with invoice number, payment method, payment date, and information about the product or service.
Google Forms includes the option for a response receipt in the settings, so when a form is completed, it is submitted to the entered email address – that of the target. Google sends the completed form from its own servers, which adds legitimacy to the campaign and increases the probability of the form reaching an inbox. Email security solutions trust the sender (noreply@google.com) and the messages contain no malware or phishing links, the email is guaranteed to be delivered. The form instructs the recipient to call the number within 24 hours if they have any dispute about the charge.
Google is aware of the campaign and is taking steps to improve detection and said that the campaign has so far been used for a small number of users; however, it is worthwhile updating your security awareness training to include this new method of attack. That is quick and easy to do and roll out with the SafeTitan security awareness training platform. SafeTitan also allows you to easily add this method of phishing to the phishing simulator, to see if your employees are likely to fall for callback phishing scams.
by Jennifer Marsh | Dec 18, 2023 | Phishing & Email Spam |
In the summer of 2023, a multinational law enforcement operation caused major disruption to the botnet and malware known as QakBot, aka Qbot & pinkslipbot. Now the malware is back and being used in a campaign targeting the hospitality industry.
QakBot was first detected in 2008 and was primarily a banking Trojan which was used to steal financial information from infected devices; however, the malware has evolved over the years and its capabilities have been significantly enhanced. Check Point researchers have described the malware as “a Swiss army knife” due to its extensive capabilities. QakBot can steal financial information, browser data, and has keylogging capabilities, allowing it to steal credentials and other sensitive information. Infected devices are added to a botnet that can be used for a range of nefarious activities, and the malware also serves as a downloader and can deliver other malicious payloads, including ransomware. QakBot has previously partnered with major ransomware groups including Egregor, REvil, Conti, and ALPHV/BlackCat.
At the time of the takedown, QakBot had been installed on more than 700,000 computers worldwide. According to the U.S. Department of Justice, the August takedown was “the largest U.S.-led financial and technical disruption of a botnet infrastructure leveraged by cybercriminals to commit ransomware, financial fraud, and other cyber-enabled criminal activity.” The law enforcement operation resulted in access being gained to the botnet’s encryption keys that were used for malware communication The botnet was hijacked and a custom Windows DLL was pushed out to all infected devices, which terminated the malware and disabled the botnet. These takedowns are, unfortunately, only temporary. As was the case with the takedown of the Emotet botnet, the threat actors simply rebuild their infrastructure.
QakBot malware is primarily distributed via phishing emails and the first QakBot malware campaign since the takedown was detected on Monday. The latest campaign uses an Internal Revenue Service (IRS) themed lure, where an IRS employee is impersonated. As is common in these campaigns, there is little body text in the emails, apart from the IRS logo and contact information. The emails contain a PDF attachment called GuestListVegas.pdf, and the subject line is “clients information”.
The recipient is told that they cannot preview the PDF file and must download it; however, the file they download is an MSI installer that will launch QakBot in the memory. Microsoft confirmed that this version of QakBot has not been seen before. While this appears to only be a relatively small campaign, distribution is expected to be significantly ramped up. In addition to this method of distribution, the QakBot operators have previously used OneNote files, Office files with malicious macros, Windows shortcut files, ISO attachments, and other executables, some of which have been known to exploit unpatched vulnerabilities.
Defending against attacks requires a combination of measures to block the initial access vector, the most important of which are an advanced spam filter – such as SpamTitan – security awareness training, and phishing simulations. A spam filter will block the majority of malicious emails to reduce the number of threats that are delivered to inboxes. By providing ongoing security awareness training to the workforce, employees will learn how to recognize, avoid, and report potential threats. Phishing simulations are an important part of the training process and allow employees to be tested to determine whether they are applying their training. When a phishing simulation is failed it can be turned into a training opportunity. With the SafeTitan platform, training is automated and delivered in real-time in response to failed phishing simulations.
For more information on advanced spam filtering and workforce cybersecurity training, give the TitanHQ team a call.
by Jennifer Marsh | Dec 16, 2023 | Email Archiving, Industry News, Security Awareness, Spam Software, Website Filtering |
TitanHQ products have received four “Top Solution Awards” from Expert Insights in Q4, 2023 in the Email Security, Web Filtering, Security Awareness Training, and Email Archiving categories.
Expert Insights is a leading business software review website that is used by IT decision-makers for researching the best business software solutions. The platform has more than 1 million readers a year and helps more than 85,000 businesses each month with their software purchase decisions. The website includes honest and impartial technical reviews and helpful guides to allow IT decision-makers to purchase with confidence.
Each Quarter, Expert Insights recognizes the world’s best B2B technology solutions through its awards program. The awards are based on Expert Insights’ independent technical analysts and editorial team, customer feedback, and industry recognition. In Q4, 2023, Expert Insights issued awards in over 40 categories, from authentication to zero trust security.
“We are thrilled to unveil our list of the ‘Top Solutions’ for Winter 2023, highlighting the extraordinary innovation in the B2B technology landscape,” said Craig MacAlpine, CEO and Founder of Expert Insights. “These awards celebrate leading solutions across more than 40 product categories, based on our own technical analysis and the engagement of thousands of enterprise tech professionals that use Expert Insights to research solutions each month.”
TitanHQ’s cybersecurity solutions were recognized and were named top solution in four categories:
- Email Security – SpamTitan
- Web Filtering -WebTitan
- Security Awareness Training – SafeTitan
- Email Archiving – ArcTitan
SpamTitan is a cutting-edge email security solution for blocking spam and protecting against email threats. The solution has artificial intelligence and machine learning capabilities and can block all known malware, zero-day malware threats, and phishing, spear phishing, and business email compromise attacks.
WebTitan is a leading DNS filtering solution that allows businesses to carefully control the web content that can be accessed via wired and wireless networks and allows businesses to restrict access to certain websites to improve productivity, reduce legal risk, and protect against phishing, malware, ransomware, and other online threats.
SafeTitan is a comprehensive security awareness training and phishing simulation platform for teaching employees security best practices and improving resilience against the full range of cybersecurity threats. The platform provides training in real-time in response to poor security behaviors, which are triggered immediately when those behaviors are detected to ensure that training is delivered when it is likely to have the biggest impact.
ArcTitan is an easy-to-implement “set-and-forget” email archiving solution that helps businesses meet their legal responsibilities for data retention and ensures that no email is ever lost, with lightning-fast search and retrieval.
“Our team is truly honored by Expert Insights’ acknowledgment of TitanHQ as the ‘Top Solution’ Provider in their Q4 2023 Awards.,” said TitanHQ CEO, Ronan Kavanagh. “This recognition across multiple categories underscores our commitment to empowering our partners and MSPs with cutting-edge technology, enabling them to deliver advanced network security solutions to their clients.”