titanadmin - Page 17
by titanadmin | Nov 4, 2015 | Spam Advice, Spam News |
Email spam may not be the first choice of hackers for making money, but there are plenty of online criminals who still use email to fool users into installing malware on their computers or revealing sensitive information.
This week, two new email spam warnings have been issued following reports that consumers have received emails that have aroused their suspicions. When checking the authenticity of the emails received, they discovered they were scams. The warnings were issued by the Better Business Bureau (BBB) in an effort to prevent the scams from claiming victims.
The latest email spam campaigns differ from each other, but use tried and tested techniques which have proven to be highly effective in the past.
Jury Duty Scam Email Discovered
Trust in authority figures is being exploited in a new email spam campaign in which users are urged to take action as a result of missing jury duty. A similar email is doing the rounds warning recipients of an impending court case. Should the recipient of the email ignore the request, the case will be heard in their absence and they will not be allowed to mount a defense.
The emails shock recipients into taking rapid action such as clicking a link or opening an email attachment. These two emails are clever in the fact they warn users of the need to respond to a judge or turn up in court, yet the crucial information needed to do so is not supplied in the email body.
Any email recipient believing the email is genuine is likely to open the attachment or click a link to find out which court needs to be visited. By doing so they are guaranteed to have their computer, laptop or mobile device infected with malware.
The BBB was alerted to the scams and issued a warning advising recipients of these emails to delete them immediately. Advice provided saying the U.S. Courts would not contact individuals about jury duty by email. Letters are mailed or telephone calls are made in this regard.
Church Leaders Warned not to Fall for Money Transfer Email Spam Campaigns
The second scam was recently reported by the finance director of Grace Bible Church, who received a request via email to transfer funds to a senior pastor. In this case, the email appeared to be official, having been sent from the senior pastor’s email account.
It is a good security practice to always check the authenticity of an email that requests a transfer of funds. In this case all it took was a quick phone call to the pastor in question to reveal that the request was bogus.
If it is not possible to contact the individual, deleting the email would be the best next course of action. If the request is genuine, the individual in question is likely to make contact again. Spammers tend to send these campaigns randomly. A second request is unlikely to be received if the first is ignored.
The Fight Against Email Spam is Getting Easier
Spam email campaigns are still an effective method of malware delivery. Social media posts and infected websites may now be the preferred method of infection, but users must still be wary about opening attachments or visiting links sent from people they do not know.
Awareness of the tell-tale signs of an email scam has improved in recent years. So has security software used to detect phishing campaigns. SpamTitan Technologies is one such company that provides a highly effective spam filtering solution. It boasts an exceptionally low false positive rate and catches over 99.98% of all spam emails.
Part of the reason why SpamTitan’s Award Winning Anti-Spam solution is so effective at catching email spam is in part due to the power of the AV engines used. Instead of using one class-leading AV engine, it uses two: Bitdefender and Clam Anti-Virus.
By installing this anti-spam solution, malicious emails used to phish for sensitive information can be blocked before they are delivered to an email inbox. Businesses looking to reduce the risk of end users infecting their desktop computers, laptops and portable devices with malware and viruses, will find SpamTitan’s Anti-Spam solutions for the enterprise highly cost-effective. Rather than purchasing a package that offers protection for far more IP addresses than are required, IT professionals can purchase a license that covers end users without wastage.
by titanadmin | Oct 23, 2015 | Spam News |
Softlayer Rated Biggest Spam Hosting ISP by Spamhaus
According to a new report by the not-for-profit anti-spam organization, Spamhaus, the biggest spam hosting ISP is Softlayer, the IBM-owned cloud computing provider. A reported 42% of the ISP’s outbound emails have been discovered to be spam.
The report, issued on Wednesday, shows the ISP to be the current biggest offender, found to be supporting spammers and hosting numerous malware operations. The extent of the company’s emails found to be spam is astonishing, making it the undisputed champion of spam. Spamhaus has recorded over 685 separate spam issues on Softlayer, almost three times as many as the ISP in second place, Unicom-sc, which has had 232 reported spam issues.
Typically, the biggest web hosting companies and internet service providers do not feature so highly in the spam list, as they tend to employ numerous measures to prevent their servers being used by spammers and internet criminals. While Softlayer has not featured so highly in the past, recently it has been rising up the rankings, even though it does make efforts to fight spammers and implements controls to prevent them from using its servers.
In recent years the company has increased efforts to keep spammers at bay, and has taken firm, decisive action when reports of spamming have been received. But this has not proved to be sufficient.
It would appear that the ISP is now being targeted by Brazilian cybercriminals who are using its services to send out high volumes of spam emails and host numerous malware-infected websites. Softlayer is understood to have relaxed its criteria and vetting processes recently in an effort to attract more business; which does appear to have been successful, albeit for the wrong kind of business.
Spamhaus also pointed out that it has received requests to have Softlayer removed from its listing, but will only do so when it is clear that all of the issues have in fact been resolved. Spamhaus pointed out that cyber-criminals from Brazil were so active that “many listed ranges were being reassigned to the same spam gang immediately after re-entering the pool of available addresses.” The report went on to say, “these specific issues would not be removed until Softlayer was able to get control of the overall problem with these spammers.”
Softlayer has responded to the new number 1 ranking, saying affirmative action is being taken to tackle the issue. Communications Director, Andre Fuochi, recently told Krebsonsecurity, “We are aggressively working with authorities; groups like The Spamhaus Project, and IBM Security analysts to shut down this recent, isolated spike.”
Unfortunately, while action is being taken, it is not fast enough to stop the spammers. As soon as accounts and websites are shut down, more are created. Users are able to provision and de-provision sites and applications cheaply and quickly, which is why the ISP is struggling to stop spam emails from being sent and malware sites from being created.
Cloudmark recently confirmed Spamhaus’s rating, saying the Softlayer network was the largest single source of spam in the world during the third quarter of this year. The spammers and scammers will always find a home somewhere, but to find it at a company owned by IBM must come as a major embarrassment. IBM is, after all, a major player in the software security market.
by titanadmin | Oct 21, 2015 | Spam News |
A bank phishing scheme operated by a Moldovan man has resulted in $3.55 million being transferred from the bank accounts of a Pennsylvania mining company – the Penneco Oil Company Inc. – according to federal prosecutors.
The perpetrator of the campaign, Andrey Ghinkul, 30, has been charged following his recent arrest in Cyprus. He is awaiting extradition to the United States, with a hearing scheduled for next week.
The phishing campaign was sent out to numerous companies, with a number of recipients reportedly opening the email, only to have their computers infected with Bugat malware. Bugat Malware is a little known form of malware, operating in a similar fashion to the well-known Trojan Zeus.
Bugat malware functions as a SOCKS proxy server, allowing hackers to directly download and execute programs on an infected host’s computer, or upload files to remote servers. In order to escape detection, the malware communicates encrypted data with its command, and by doing so fails to trigger many traffic inspection software warnings.
The malware has been used to log information entered during online banking sessions, with Firefox and Internet Explorer browsers so far exploited. With the information obtained, hackers are able to make fraudulent wire transfers and ACH transactions. So far, small to mid-sized businesses have been most commonly targeted.
While many organizations are now looking out for Zeus infections, this new form of malware can escape detection more easily. The attacks also show how cybercriminals are diversifying their attacks in order to gain access to financial account information and avoid detection.
The phishing campaign was used to send emails to a number of recipients in U.S companies, with the emails appearing to have been sent from medical providers, indicating the recipients had received a positive diagnosis for cancer.
Bugat Malware Bank Phishing Scheme Nest Hackers Over $10 Million
According to the FBI, Bugat malware has resulted in around $10 million in funds being transferred from U.S company accounts to hackers in Russia and Belarus.
The transfers from Penneco Oil’s accounts were made possible by the malware, which recorded bank passwords as they were entered on the infected computer. That information was then used to make the transfers. The first transfer of $2.2 million was made in August 2012, with the funds being received by a bank based in Krasnodar, Russia. A second transfer was made the following month, this time the recipient account was in Minsk, Belarus.
While the transfers did go through, action was swiftly taken by the bank – Indiana, PA-based First Commonwealth – and the funds were rapidly restored. Senior Vice President of Penneco, D. Marc. Jacobs, said the bank “worked to completely restore our funds almost immediately.” In this case, Penneco had all funds restored and the bank had to cover the cost.
Should Ghinkul be extradited, the case will be heard in Pittsburgh where another attempted victim was targeted. Sharon City School District nearly lost $999,000 to a Russian account. Fortunately, that transaction was successfully blocked.
by titanadmin | Oct 19, 2015 | Spam News |
A new iTunes email scam has been uncovered which attempts to trick users into revealing their credit card numbers, according to a recent report issued by Malwarebytes.
The latest iTunes email scam targets users of iTunes and offers them a refund for a purchase that has been made using their iTunes account, indicating they have been affected by an email scam already. In order to receive the refund, the users must provide their Apple ID, password, and credit card details so the refund can be processed.
Emails have been sent to iTunes account holders telling them that their account has been fraudulently used to purchase an app valued at £34.99 ($53), with the emails containing a fake receipt for the purchase. The app is question is provided by CoPilot Premium HD, a supposed navigation service. The receipt contains a link that the recipient of the email must click in order for their refund to be issued, if the purchase is not genuine.
There is of course no such app, and the high price is perhaps a warning that something is amiss. Unfortunately for users looking to protect themselves from fraud, the very actions they take to protect themselves will actually ensure they do become victims.
Not the Only iTunes Email Scam Recently Uncovered
This is not the only email phishing scam to have been sent to Apple users in recent weeks. Another email spam campaign attempts to get users to click a link to update their credit/debit card, which users have been informed in the email is about to expire. Users have been requested to click a link and enter their new card details, including the CSC code on the reverse of their card, as well as the new expiry date.
As with many email scams of this nature, the email is sent with a threat of account suspension if they do not comply. In this case, users have little time to respond. The email link is said to expire in one hour’s time if it is not clicked, reducing the time for users to verify if the email is in fact genuine.
They are provided with a link to store.apple.com which is seemingly genuine; however, hovering over the link will reveal that the link directs them to a different location.
There are other common tell-tale signs that the email is a fake, even though the correspondence does contain seemingly genuine Apple imagery and appears to have been sent from Apple’s customer service department. One of the most telling signs is the volume of spelling mistakes contained in the email. Any email sent by Apple is likely to have at least been run through a spell check before being used as a template for millions of Apple device owners. A sure sign that the email is not genuine.
The email contains spelling and grammatical errors such as informing the recipient that the link will “expire one hours after the email was sent.” iPhone “ore” iPads is another, and feature is spelled “feauter.”
The advice to all Apple users is to take time to carefully read any email sent from Apple, and to attempt to verify any request to provide ID numbers or financial information.
by titanadmin | Oct 16, 2015 | Spam News |
It has now been over a year since the U.S Postal Service was affected by a phishing campaign that resulted in the exposure of the personal information of 800,000 current and former workers, yet the postal service is still not effectively dealing with the phishing threat. Employees have been tested, and they are not identifying phishing emails.
Postal Service Employees are at Risk of Falling for Phishing Emails
The network data breach of 2014 occurred as a result of employees falling for spear phishing campaigns, which allowed criminals to gain access to postal service networks containing sensitive data. The data thieves were able to gain access to the network and exfiltrate data without meeting much in the way of resistance. It would appear that if a similar campaign was conducted again now, even more data may be exposed.
The Office of the Inspector General (OIG) recently took the decision to put postal service workers to the test, to determine whether lessons have been learned since last year. In total, 3,125 fake phishing emails were sent to employees of the U.S Postal Service to determine whether they were actually able to identify a potential phishing campaign.
There was some good news. 75% of workers were able to resist the temptation to click on the phishing links in the emails. The bad news was 25% did click. Unfortunately, all it takes is for one person to respond to a phishing email for criminals to gain access to data. 780 responses to fake phishing emails shows risk is not being effectively managed.
However, perhaps worse still, was the lack of compliance with policies that had been put in place in the wake of last year’s successful attack. For instance, the postal service’s Computer Incident Response Team should be alerted if a suspicious email is received by workers, yet only 7% of employees did so during the test.
The reason is perhaps quite easy to explain. Only 4% of staff had completed the Postal Service cybersecurity training course, so presumably were unaware of the policy of reporting suspicious emails, if they were in fact able to identify them as suspicious.
OIG Report Shows Postal Service is Not Dealing with the Phishing Threat
The OIG report on the cybersecurity test stated that awareness training does have a positive impact, and can substantially reduce the risk of employees responding to a phishing campaign. Research shows training can reduce security-related risks by as much as 70%.
Policies must of course be turned into procedures, and the staff must receive training. The OIG said, “When management does not require all employees with network access to take annual information security awareness training, users are less likely to appropriately respond to threats.”
One of the main problems for organizations trying to tackle the threat of phishing is the fact that criminal organizations and hackers are developing ever more complex and convincing campaigns to fool users into opening malware-infected attachments and visiting links to malware-infected websites. However, if training is not provided to the staff, even uncomplicated phishing campaigns could well succeed.
At present, only new members of staff and CIO office members are required to undergo annual cybersecurity training: That is not the most effective way of dealing with the phishing threat. However, in response to the OIG report, the Postal Service will be implementing new training policies by April 2016.
by titanadmin | Oct 14, 2015 | Spam News |
The Federal Trade Commission has issued a warning over a new gaming email phishing scam that targets video game players and takes advantage of their love of the games to get them to divulge their account information.
Gamers invest considerable time and money into buying add-ons and developing gaming characters; however, the fear of loss of their gaming account is seeing many fall for the latest scam.
Cyber Criminals Opt for Gaming Phishing Email Scam
Hardcore gamers are not difficult to find, having registered on forums and gaming websites, providing their email addresses and other information about their gaming habits. Once criminals obtain email addresses of gamers, they are sent fake emails from gaming companies suggesting they have been discovered to have sold gaming items or characters for real money, and by doing so have violated the rules of the game.
Consequently, the users are threatened with account suspensions, or in some cases, legal action. A number of emails have been received by gamers with threats that they will be sued for amounts up to $2,700 for repeated violations of gaming rules and regulations. The intention is not to get the users to part with that money, but to get them to reveal details of their bank accounts or credit cards used to make purchases.
Users are often fooled into responding out of fear of losing their accounts or being suspended or banned from their favorite games. The email campaigns can also be highly convincing, using templates that appear legitimate, often including company logos and names the users may be familiar with.
The scammers have been targeting users of some of the most popular online games, such as World of Warcraft and Diablo III, both produced by Blizzard Entertainment, although the scam is not restricted to players of these games. The volume of emails sent to gamers, and complaints received, has resulted in Blizzard emailing users to tip them off to what it called “rampant scams.”
The FTC has also got involved, issuing a warning of its own. According to the FTC warning, targets are advised that they should check the status of their accounts and challenge the suspension if they have done no wrong. They are supplied a link for this purpose and are required to fill in a ‘verification’ form.
They are then asked to enter information in order to confirm their accounts and identities, and must reveal account and financial information. The perpetrators of the scam then empty their accounts.
This is not the only technique used by online fraudsters to get users to reveal their credentials. Gamers are being sent spam emails asking them to login in order to receive free gifts and exclusive game add-ons, with users requested to click a link in the email to login in order to claim their prize.
It is not always essential that account details are entered in the online forms to which the users are directed to. The links contained in the emails can direct the users to malware-infected websites. Malicious software is automatically downloaded to the users’ computers, allowing the perpetrators to gain access to the device and trawl files looking for personal information such as bank account details, login names and passwords.
Gamers have been warned to always try to verify any such emails, and not to click on links, open attachments or use the contact details provided. All requests that are out of the ordinary should be independently verified with the company concerned, using the gaming website’s contact information.
by titanadmin | Oct 12, 2015 | Spam News |
There has been some good news reported recently that indicates email spam levels are now at the lowest point seen in the past 12 years. According to a report issued by Security company Symantec, spam emails fell to 49.7% of all emails sent in June this year. Spam email levels fell further still in July, dropping to 46.4% of total email volume. Symantec also reported that the volume of phishing campaigns also saw a fall in June.
A number of reasons have been cited for the fall in spam levels, including bringing a number of spammers to justice and closing down their criminal networks, in addition to shutting down a number of rampant botnet networks, many of which were located in the United Kingdom.
The botnets were identified by UK police forces which orchestrated a number of takedowns. UK and European internet service providers had been collaborating with the police and passed on information on suspected botnets, helping to reduce the effectiveness of the networks, ultimately leading to many being shut down.
While this is good news, this does not mean there has been a reduction in risk. Phishing schemes may have seen a small drop in June, but the number of malware variants now being discovered has increased dramatically. The variation in malware is causing a problem, as the malicious software is becoming harder to identify. The extent of the increase in variants is considerable. In just two months the number of malware types had almost doubled from 29.2 million in April to 57.6 million pieces of malware caught by Symantec in July. This is the second highest figure reported in the past 12 months, with only November 2014 seeing more malware attacks caught (63.6 million).
The attack landscape is constantly changing, with cybercriminals now diversifying their attack vectors. Ransomware for instance, is becoming more popular. Just under half a million attacks (477,000) were thwarted by Symantec in June, with the volume of ransomware having risen for two months in a row.
While cyber criminals based in the UK and United States may be diversifying attack vectors, hackers in other countries still favor email spam, with eastern Europe and China still seeing huge volumes of spam emails being sent. It is certainly not a time to let one’s guard down or become complacent about email spam.
Businesses Still Receiving High Volumes of Spam Emails
Overall, levels of spam may have fallen, but small to mid-sized companies are still seeing high levels of spam emails received, with the percentage of spam emails remaining above 50%. Spam email traffic to small to medium companies (those with one to 250 employees) stood at 52% in June.
Malicious emails are also still being used extensively to target organizations of all sizes. In June, malicious emails were being most commonly used against companies employing 1501-2500 individuals, with one in 164 emails recorded as being malicious in nature.
In July the figures had improved, with organizations employing 251-500 individuals the most common recipients of malicious emails, registering one email in 260 as being malicious in nature, closely followed by small organizations employing under 250 individuals, with one in 275 emails rated as malicious.
Spam emails were still being sent at high levels to particular industries, with mining and manufacturing industries receiving high levels of spam in June. Over 56% of emails received in the mining sector were spam, with the manufacturing, construction, retail and non-traditional service industries all registering spam email volumes of 53% or more in June.
The figures for July actually showed an increase in spam for some industry sectors. Mining had increased to 55.7%, with only very slight falls in spam levels in other industry sectors. Manufacturing, retail and construction all registered spam percentages above 53%.
Each of the other 6 industry sectors (Professional services, agriculture/forestry/fishing, wholesale, non-classifiable establishments, finance/insurance/real estate, and non-traditional services) all registered spam email percentages of between 51.9% and 52.5%, indicating email spam remains a major problem for most U.S. businesses.
by titanadmin | Oct 9, 2015 | Spam News |
The Ponemon Institute has released a new report detailing the cost of phishing attacks on U.S businesses, suggesting the average annual cost for U.S companies has now risen to $4 million. Ponemon calculated phishing attacks take an average of 23.7 days to resolve, and are having a huge impact on U.S organizations, with smaller companies often suffering the most.
Cost of Phishing Attacks & Cyber Crime Assessed
The report indicates that the biggest costs suffered as a result of cyber crime come from phishing campaigns and social engineering, which accounted for 16% of total cyber crime costs. Phishing and social engineering were found to have affected 59% of organizations, while botnets affected 66% and web-attacks were suffered by 76% of organizations.
The Ponemon study, conducted in conjunction with HP Enterprise, involved a representative sample of 58 private and public sector U.S organizations being surveyed on cyber crime and the costs of dealing with criminal attacks. The results of the study show that in the U.S, the mean annualized cost of cyber crime has risen to $12.7 million per year, with the highest total average cost of dealing with cyber crime being $15.42 million – more than double that of Germany in second place.
The study showed that organizations are having to pay between $1.6 million and $61 million per year to resolve cyber attacks. The cost of the dealing with those attacks was found to be higher for larger organizations, although the per capita costs were highest for smaller organizations.
The new 2014 Cyber Crime Report shows the cost of dealing with attacks has risen 19% in just 12 months, with the global average cost of cyber crime estimated to have exceeded $7.7 million. Some companies are having to cover costs of up to $65 million to resolve criminal attacks, which were shown to have increased in both frequency and severity during the past 12 months. Email attacks remain one of the biggest causes for concern, being one of the main methods used by criminals seeking access to computer networks.
Phishing Emails Are Proving to be Highly Effective
Earlier this year, communications company Verizon produced a report indicating phishing campaigns can be highly effective methods of attack, and suggested that all too often staff training efforts are not particularly effective. Many organizations are now providing staff with information on how to identify phishing emails, yet this information does not appear to be retained. The study found that 23% of individual who received a phishing email opened it, and an alarming 11% of recipients clicked on the link contained in the email or opened the attachment.
The provision of training manuals on phishing to employees can be effective, but retention of information tends to be poor. The Ponemon study did suggest that one of the best methods of training staff how to identify phishing emails is to provide examples, indicating the sending of simulated phishing emails was particularly effective at reinforcing training, providing up to a 37% return on investment.
With phishing emails representing such a substantial proportion of cyber security costs, and training proving not always particularly effective at substantially reducing the risk of attacks being successful, greater efforts should be put into intercepting phishing emails and preventing them from being delivered to recipients’ inboxes. For that, a robust and effective email spam filter is required.
by titanadmin | Oct 8, 2015 | Spam News |
Although many reports suggest that email spam is reducing, email spam and botnet infection is still a major issue for most U.S organizations and individuals – with criminal practices netting cybercriminal gangs billions of dollars every year.
Determining the infection levels and the volume of spam being sent was one of the missions of the Messaging, Malware and Mobile Anti-Abuse Working Group (M3AAWG). M3AAWG, is a global organization tasked with promoting cybersecurity best practices and fighting organized internet crime. M3AAWG was formed a decade ago by a number of leading internet service providers, with the goal of improving collaboration and sharing knowledge to make it harder for criminals to spam account users. By reducing the impact of email spam on individuals and organizations, ISPs would be able to better protect users, IPS’s email platforms and their reputations.
Quantifying Email Spam and Botnet Infection a Complex Task
It was discovered that quantifying email spam and botnet infection levels was a complex task; one that was only possible with collaboration between internet service providers. As a result of this collaboration, the organization has produced reports on the global state of email spam and botnet infection. Its latest analysis suggests that approximately 1% of computer users are part of a botnet network.
The data gathered by M3AAWG involved assessing 43 million email subscribers in the United States and Europe.,The data analysis showed that IPS’s typically block between 94% and 99% of spam emails. The company’s report suggests that on the whole, IPS’s do a good job of blocking email spam.
The figures look impressive but, considering the huge scale of email spam, billions of spam emails are still getting through to users, with financial organizations and other companies now being regularly targeted with spam and malware.
Email spammers are well funded, and criminal organizations are using email spam as a means of obtaining tens of billions of dollars each year from internet fraud. Spam emails are sent to phish for sensitive information, such as bank account information, credit card details and other highly sensitive data including Social Security numbers. Accounts can be emptied, credit cards maxed out and data used to commit identity theft; racking up tens of thousands of dollars of debts in the victims’ names.
In years gone by, email spammers concentrated on sending emails randomly to accounts with offers of cheap Rolexes, Viagra, potential wives and the opportunity to claim an inheritance from a long lost relative. Today, spammers have realized there are far greater rewards to be had, and emails are now sent containing links to malware-infected websites which can be used to compromise users’ PCs, laptops and Smartphones, gaining access to highly sensitive data or locking devices and demanding ransoms.
Some emails may still be sent manually, but the majority are sent using botnets. Networks of infected machines that can be used to send huge volumes of spam emails, spread malware or organize increasingly complex attacks on individuals and organizations. The botnets are available for hire, with criminals able to rent botnet time and use them for any number of reasons.
Many of the attacks are now coming from countries where there is little regulation and a very low risk of the perpetrators being caught. Countries in Africa, as well as Indonesia and the Ukraine house huge volumes of cybercriminals. They have even set up call centers to deal with the huge volume of enquiries from criminals seeking botnet time to orchestrate phishing and spamming campaigns. Tackling the problem at the source is difficult, with corruption rife in the countries where the perpetrators reside.
However, it is possible to reduce spam level, and the risk of employees falling for a scam or downloading malware by installing a robust email antispam filter, reducing the potential for spam emails and phishing campaigns getting through to individual accounts. According to Verizon, 23% of users open phishing emails and 11% open attachments and click on links. Stopping the emails from reaching users is therefore one of the best methods of defense against attacks.
by titanadmin | Oct 6, 2015 | Spam News |
Lawyers representing plaintiffs affected by spammy marketing practices by business networking website LinkedIn have reached a $13 settlement in a California court, with the LinkedIn email spam lawsuit likely to result in users of the website receiving a payout of around $10 per person.
Lawyers argued that the marketing practices used to attract new users breached California’s common law right of publicity and constituted unfair competition, with millions of users having had their privacy violated. The class-action lawsuit was filed in September 2013 and lasted two years before LinkedIn agreed to settle the case without admission of liability. LinkedIn claimed no wrongdoing and that its business practices broke no laws.
Alleged Spammy Marketing Practices used by LinkedIn to Attract New Users
Users of LinkedIn are permitted to import contacts from email accounts such as Gmail. Users electing to “Add Connections”, will generate an email that is sent to their contacts list inviting those individuals to connect and sign up for an account with the website.
Site users were asked before emails were sent to their imported email contacts, but they were not advised about a further two emails that were triggered if their contacts did not respond to the original email request within a fixed period of time. The follow-up emails were reminders that the invitation was still waiting for approval.
The lawyers claimed that LinkedIn had been “breaking into its users’ third-party email accounts, downloading email addresses that appear in the account, and then sending out multiple reminder emails.” The case centered on the fact that users were not advised that this would be the case. It was claimed that the website was using the names and likeness of users to drum up more business without consent, thus breaching the privacy rights of site members.
Last year, LinkedIn petitioned U.S. District Judge Lucy Koh requesting the case be dismissed, as users had in fact given their consent for contacts to be sent emails; however, Koh ruled that while consent had been provided for one email to be sent, users had not given LinkedIn consent to send any further emails if individuals did not respond to the initial request to join the website.
Other claims made against LinkedIn were rejected, such as the breach of federal wiretap law and claims of hacking users accounts. As a result, the case was required to be resubmitted.
LinkedIn Users Invited to Submit Claims for Compensation
The LinkedIn email spam lawsuit has now been settled, although users of the site are unlikely to receive much in the way of compensation. Any user who used the Add Connections feature of the website between September 17, 2011 and October 31, 2014 have now been invited to submit claims, and have until December 14, 2015 in order to do so.
Due to the volume of individuals affected, it is probable that the payout for each affected user will be around $10. LinkedIn has agreed to add further funds – $750,000 – if the volume of claims it receives results in individuals qualifying for a payout of less than $10 a head. Linked in will also be required to cover legal fees in addition to paying the $13 million settlement.
From the end of the year, all users of the “Add Connections” feature will be informed that by doing so, they are giving their consent for their imported email contacts will be sent one email, and up to two follow-up emails if no response is received from the initial request. There will also be a new option added which will allow invitations and reminder emails to be stopped.
by titanadmin | Oct 1, 2015 | Spam News |
The threat from phishing emails is causing Health IT professionals major headaches, and is one of the main data security concerns according to a recent HIMSS cybersecurity survey. The recent HIMSS survey was conducted on 300 healthcare IT security professionals and suggests that the increase in phishing emails is one of the main reasons why the healthcare industry is having to invest so heavily in data security. 69% of survey respondents believed that to be the case.
Phishing campaigns are now being devised that are difficult to identity, with cybercriminals investing considerable time and effort into creating highly convincing emails in an attempt to get healthcare employees to divulge their login credentials.
Threat from Phishing Keeps CISOs Awake at Night
Criminals may still be sending random email spam in an attempt to obtain credit card details and banking information, but healthcare providers are now being increasingly targeted for the high volume of Social Security numbers and other personal patient information held; data that can be easily used to commit identity theft and obtain far more than is possible with credit card numbers. According to HIMSS Senior Director of Research Jennifer Horowitz, phishing is now “the number one thing that keeps CISOs up at night.”
The survey showed that data security has become one of the main business priorities for healthcare organizations, with 87% of respondents claiming data security has increased in priority over the course of the last year. Out of the respondents that said data security is a main priority now, two-thirds believe phishing to be the main cause for concern, and the same volume of respondents claimed their organizations had already suffered a phishing or other online scamming attack.
Phishing is a technique used by cybercriminals to obtain personal information, and is used as part of a wider attack on a corporate network. If users can be convinced to visit a link to a website or open an attachment, malware is downloaded to their device. A third of survey respondents indicated they have already become the victim of such an attack this year.
One problem faced by the healthcare industry in particular is the tactics used by criminals frequently change. Phishing was a technique most commonly associated with mass spam emails sent by individuals in the hope that some email users would fall for the scams. It would appear that now individuals, or specific groups of individuals, are being targeted. Many criminals now opt for quality over quantity, and are devising campaigns to target individuals with access to the data they seek. These “spear phishing” campaigns can prove to be highly effective.
Tackling the Threat from Phishing Emails
Efforts are being made by healthcare organizations to reduce the risk of individuals falling for campaigns. Spam filtering can be effective at limiting the volume of emails that make it through to the inboxes of healthcare workers, and training is now being provided to staff to help individuals recognize the signs of a phishing email. However, it would appear that while training is sometimes provided, this is not subsequently tested in many cases. Phishing email exercises designed to test users’ ability to identify phishing campaigns are still not being used by the majority of healthcare organizations. Only a quarter claimed they are using exercises to test staff readiness to deal with the threat, and that is a recipe for disaster.
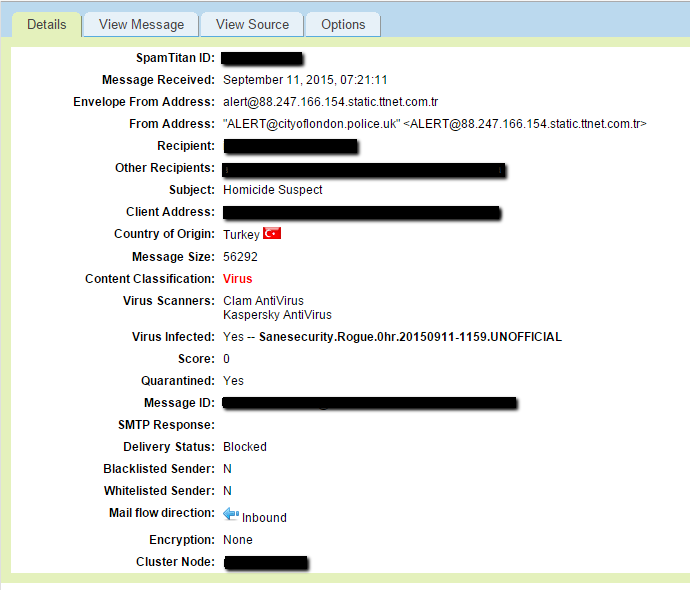
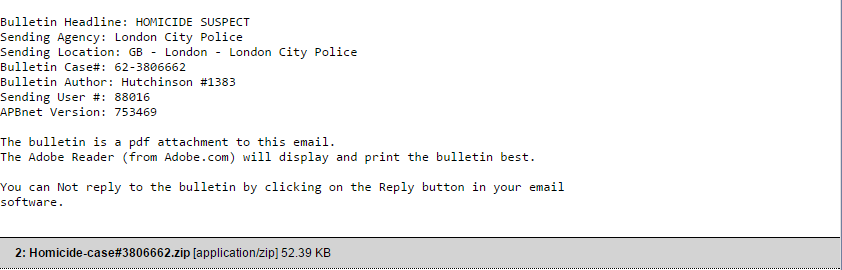
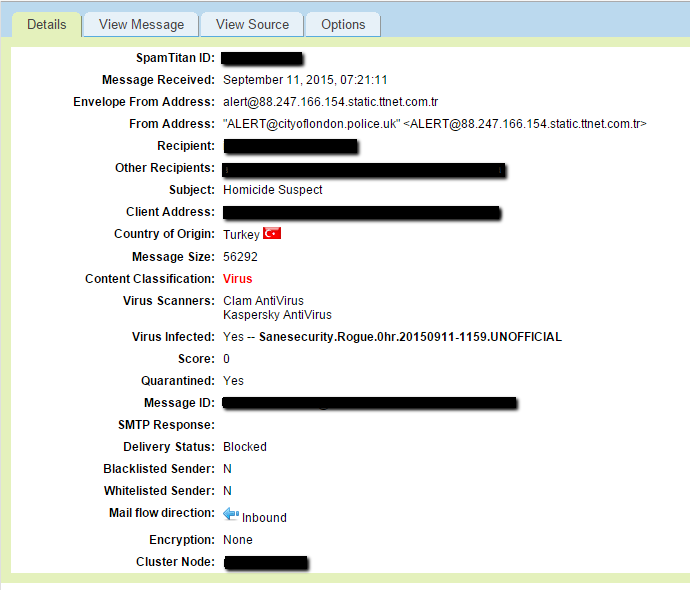
by titanadmin | Sep 15, 2015 | Spam Advice |
City of London Police are sending emails containing important information about a murder suspect. You must be vigilant, and if you see this individual, you should not approach him! The attachment sent via email contains his image, so you will know to avoid him and alert the police if you see him. Unfortunately, opening the attachment will make you a victim. You will not be murdered, but you may end up having your bank account emptied. Yes, this is a City of London Police email scam, and it attempts to convince the good, law abiding public to infect their devices with malware.
City of London Police Email Scam Warning!
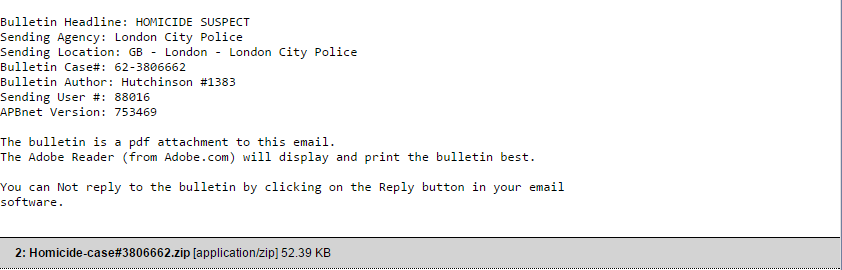
One of the latest email scams to be wary of, especially if you live in the UK, involves spam emails with the subject “London City Police.” Contained in the email is a bulletin detailing a murder suspect on the loose, together with a malware-infected attachment.
Fortunately for the wary, there is a clue in the subject that the email is not genuine. There is of course no “London City Police.” The police force in question is called “The City of London Police.” That said, the shock of receiving an email from law enforcement about a murderer on the loose may be enough to convince many to open the email and the attachment.
As one would expect, the email contains a stern warning, with the content phrased in such a way that it could in fact have been sent by the police force. A murderer on the loose in London is a serious matter, and this cunning email spam campaign has been devised to play on the fear that such a matter is likely to create.
How would the Police force have got your email address, and those of everyone else living in your area? That is something that many victims of this email scam may ponder after opening the attachment. Of course, by then it will be too late. Opening the attachment will result in malware being installed on the victim’s computer.
Fortunately, email scams such as this are easy to avoid, in fact, they would not even get to the point of being delivered to an inbox, if precautions have been taken, as explained by Steven Kenny, Customer Support Manager at TitanHQ.
Kenny pointed out that by using SpamTitan, computer users will be protected. He said, “This malware was blocked by SpamTitan before it had a chance to make it to users’ inboxes.” He went on to say, “The malware contained in the attachment was flagged as a virus. The attachment is a zip file, once executed; the malware goes to work.”
SpamTitan Blocked the City of London Police Email Scam
The image below is a screenshot of the City of London Police email scam, which was successfully blocked by SpamTitan.
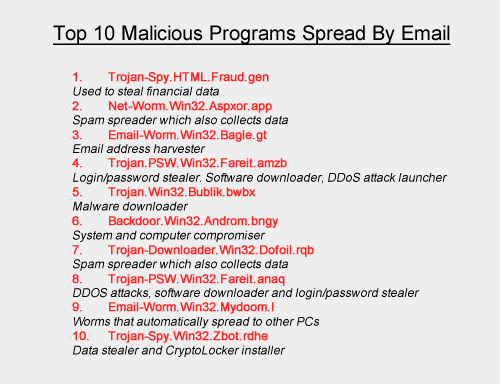
Current High Risk of Malware Infection
Malware poses a major risk to individuals, but businesses are especially at risk of infection. Employees may be wary of opening emails on their own devices, but are they as security conscious at work?
It is perhaps easier to believe that a work email address would be in the police database, rather than a personal email account. This may lead employees to believe that the email is genuine. Unfortunately, all it takes is for one employee to open an infected attachment, and their computer, and the network it connects to could be infected.
Since email is essential in business, protections must be put in place to ensure networks are not compromised as a result of the actions of employees. If malware is installed, the losses suffered can be considerable. It therefore can pay dividends to implement protection such SpamTitan spam filtering. This will prevent malware-infected emails from being delivered to employees’ inboxes.
by titanadmin | Sep 9, 2015 | Spam News |
A new Netflix phishing scam has been uncovered which works by telling users their Netflix accounts have been closed, requiring action to regain access to the service. Doing so will give your confidential login details to the scam operators.
Netflix has 62.27 million users, making it a highly attractive target for email scammers and spammers, and consequently Netflix phishing scams are common.
Latest Netflix Phishing Scam Convinces users to Reveal their Account Details
Recipients of the fake Netflix emails are required to click a link in order to reactivate their accounts. Unknown to the victims of this Netflix phishing scam, clicking on the link will direct them to a fake Netflix page, and by reactivating their accounts they will be giving the scammers their account names, passwords, and potentially other sensitive information.
Unfortunately for Netflix users, revealing passwords for one account may also mean other online accounts are compromised. Many users share their passwords across different websites, often using the same or similar passwords for Netflix, Facebook, and a host of other sites, including online banking portals.
TitanHQ recommends Netflix users ignore the email and delete it, and certainly do not to click on the link in the email. Phishing scams such as this usually direct users to a website that has been infected with malware, and clicking the link will result in that malware being downloaded, even if no information is entered on the page.
The best course of action is to login to your Netflix account as you would normally do, by typing in the URL or using your bookmark, and check your account status directly with Netflix. In all likelihood, it will still be active.
Further Information on the New Netflix Phishing Scam
Below is a screenshot of the latest Netflix phishing scam. The email appears genuine enough, although close inspection will reveal a few grammatical errors, such as missing apostrophes and misplaced exclamation marks. However, the email could be enough to fool the unwary, and especially individuals who tend to skim read emails and click first and think later.

This phishing campaign is similar to others that have been recently sent to users of other online services. Phishing emails are devised to give the recipient a legitimate reason for handing over sensitive information, usually via webpage.
These include, but are not limited to:
- Upgrading security settings
- Performing essential system maintenance
- Verifying account details to prevent fraud
- Claiming a refund for a bill that has been paid
- Giving money back for an incorrect charge
- Offering you a free gift or service
Email scams often deliver malicious programs – malware – that has been created to steal confidential data such as account login names and passwords. Phishing campaigns are launched on social media, although email is the most common way that these scams are delivered.
Generally speaking, phishing campaigns can be categorized in three types:
Off-the-Shelf Jacking Toolkits
Criminals can purchase malware online which can be used to scam users into revealing passwords, which can subsequently be used to empty bank accounts, rack up debts, or hold people to ransom (the latter is becoming increasingly common and is referred to as ransomware). Once access is gained to an account or computer, Ransomware is used to encrypt data. The users are then required to pay a ransom to the perpetrator of the scheme in order to get their data unlocked.
These campaigns are usually opportunistic in nature, and involve millions of spam emails being sent. It is a numbers game, and some users will click on the phishing links and compromise their computers and networks.
Zero-day Vulnerability Exploits
The net is also cast similarly widely with these email phishing campaigns; however, the malware delivered is more complex, and the hackers behind these schemes are considerably more skilled. Zero-day vulnerabilities are new security flaws that have been discovered in software that have yet to be discovered by the software vendor. Consequently, patches do not exist to deal with the threat. Malware is created to exploit these vulnerabilities, which is usually delivered via an infected email attachment, although it can be downloaded when users visit a phishing website.
Spear Phishing Campaigns
These are targeted attacks that are conducted on individuals, or in some cases, organizations. The perpetrators of these schemes are skilled, and invest considerable time and effort into creating convincing campaigns. Oftentimes extensive information is gathered on the targets prior to the phishing emails being sent.
These schemes similarly use zero day vulnerabilities, and these advanced persistent threats (APT) have been used in a number of high profile attacks, such as the recent Carbanak malware attacks which have made the headlines recently.
How to Avoid Becoming a Phishing Victim
The best defense against attack is to be vigilant. Security awareness training for employees is essential. Staff members must be alerted to the risk, the consequences of clicking on a phishing link, and told how to identify scams. They should be instructed to check links before clicking (by hovering the mouse arrow over the link to check the real address).
It is also essential to keep all software patched and up to date. This applies to operating systems, applications, web browsers and other software. Software should be configured to update automatically wherever possible. Organizations should also develop concise patch management policies. Continuous security audits should be conducted and multi-layered network security controls developed.
There are a number of ways that spam and phishing emails can be prevented from being delivered to users, such as using a spam filter. Web filtering is particularly useful in prevent users from visiting known malware and phishing sites.
by titanadmin | Aug 26, 2015 | Spam News |
In 1998, ICANN issued the first domain names and IP addresses. There were not many top level domains (TLDs) to choose from. Each country had its own domain suffix, but the choice was limited to .com, .org, .net, .edu, .mil and .gov. Over the years, a few more options have been introduced such as .me, .mobi, .tv and .biz, but the suffix that has caused the most controversy is .xxx – a TLD intended for websites containing images of a sexual nature.
The .xxx TLD was seen as a method of introducing a red light district to the Internet, cleaning it up aside from a dirty corner that could be policed and easily blocked. Some purveyors of pornography allegedly welcomed the move, while others were opposed to it.
There were protests, but the new TLD was released in December 2011, and ICM Registry – a Fort Lauderdale for-profit business – was assigned responsibility for allocating the TLDs. Incidentally, the contract for this was quite lucrative. ICM Registry expected to make in the region of $200 million per year out of the deal.
Sometimes a good idea on paper doesn’t always work out so well in practice. For instance, some companies had spent a long time building up a brand name. They operated their domain on the .com domain, had bought up the .net, .mobi, .org versions and all other TLDs to protect their brand. They did not like the idea of having to do that again with the XXX version, and neither would they be willing to move their main site over to the .xxx TLD.
Few were in favor of the new XXX TLD
Pornographers were not the only objectors to the introduction of the .xxx TLD. The Bush Administration was opposed to the release. In fact ICANN was asked to withdraw support for the proposal. Criticism of the proposal mounted and ICANN came under a considerable amount of pressure. The American Department of Commerce, that has power over ICANN, received over 6,000 complaints about the introduction of the .xxx TLD. Even politicians who had originally backed the idea in the year 2000 changed their mind a decade later. Naturally, conservative groups also applied pressure to block the proposal. It was not enough. The TLD was released – with a delay of a month – and a swathe of new porn websites were subsequently launched.
Unsurprisingly, there has not been a reduction in the number of .com porn websites on the Internet. The new domain has seen even more created. Go figure!
ICANN was subsequently sued on the grounds that it had created a monopoly and that the introduction of the TLD forced businesses to spend even more money registering domain names to protect their brands from being piggybacked. After a couple of years, the lawsuit was dropped.
Controls put in place to protect trademarks
ICM regulators created the new TLD in order to clean up the Internet apparently. The .xxx TLD was seen as a way to make it easier for people wanting to view pornography to find it (it wasn’t exactly difficult, it must be said – type “porn” into a search engine for example) and as a way of promoting a responsible attitude toward it. It would, in theory at least, eventually lead to a dedicated area where pornographic websites could be housed.
However, trademark and patent protection advocate Inventa pointed out that opposition to the new .xxx TLD was virtually universal. No one wanted it apart from ICANN (and ICM Registry).
As for the fears that domain-sitters and entrepreneurs would take advantage, there were controls to prevent this. Eligibility criteria needed to be met. A company owning the trademarked .com version of a website could purchase the corresponding .xxx TLD to use as an adult domain or to prevent others from using it. Amazon.xxx, for example, could only be bought by Amazon.com. The ICM Registry reserved it for them. If there was no trademark, the domain name could be bought by anyone.
Was it worth all the effort?
ICM Registry would be inclined to agree, but as for making the Internet a safer place for children, cleaning up some porn, and having a dedicated online red light district, that clearly hasn’t worked. The biggest names in Internet porn still use their dotcom websites and have not made the switch to XXX domains. People interested in viewing pornography do not need an .xxx TLD to be able to find it, and don’t care what the name of the website is let alone the TLD, provided it gives them what they are looking for.
It is no easier to block pornographic websites than it was before the release. Simply blocking access to XXX suffixed websites will make no discernable difference to the amount of porn that is viewable online.
Until laws are passed to force porn websites to use the XXX domain – which would be incredibly difficult to implement – the move has not been particularly effective.
The only way to block effectively access block pornography from being displayed is to use a web filter such as SpamTitan Technologies. By using real-time classification, URL filtering, blocklists, keyword filters and other tools, SpamTitan Technologies web filtering solutions prevent the websites from being viewable. Something very important for schools, universities, colleges, charities, and corporations.
Any organization believing written policies on allowable uses of the Internet are sufficient to stop inappropriate use, should bear in mind that surveys have revealed that 20% of men and 13% of women have admitted to downloading pornographic content while at work. A recent pool of 500 Human Resources professionals indicated two thirds had discovered pornographic content on work computers, and the majority of porn is viewed during office hours (between 9am and 5pm).
If you want to stop employees accessing pornography in the workplace, the only effective way of doing so is with a robust web filtering solution.
by titanadmin | Aug 18, 2015 | Spam News |
Former employees of Kaspersky Labs have tipped off the media to an alleged practice of faking malware. It is claimed the company used fake malware to get rival anti-virus companies to flag the programs as malicious, potentially tarnishing their reputations with numerous fake positives.
For obvious reasons, the tip-offs have come from anonymous individuals who claim to have worked for Kaspersky Labs, yet their identities naturally cannot be verified. They could in fact be employees of rival anti-virus companies. It is therefore difficult to determine whether there is any truth in the allegations. Kaspersky Labs denied the allegations, in fact Eugene Kaspersky has been quite vocal on social media and has spoken out on Twitter, vehemently denying the accusations.
In an effort to find out more, we contacted Kaspersky Labs to find out further details. We received a reply as follows:
Kaspersky Denies Fake Malware Claims
“Contrary to allegations made in a Reuters news story, Kaspersky Lab has never conducted any secret campaign to trick competitors into generating false positives to damage their market standing. Such actions are unethical, dishonest and illegal.” Kaspersky went on to say, “Accusations by anonymous, disgruntled ex-employees that Kaspersky Lab, or its CEO, was involved in these incidents are meritless and simply false. As a member of the security community, we share our threat intelligence data and IOCs on advanced threat actors with other vendors, and we also receive and analyze threat data provided by others. Although the security market is very competitive, trusted threat data exchange is a critical part of the overall security of the entire IT ecosystem, and we fight hard to help ensure that this exchange is not compromised or corrupted.”
Interestingly though, there does appear to be a grain of truth in the accusations, with the anti-virus software giant confirming that harmless malware was in fact created and uploaded. However, this was part of a test of its own software systems, not an attempt to discredit rivals. The statement issued explained the experiment:
“In 2010, we conducted a one-time experiment uploading only 20 samples of non-malicious files to the VirusTotal multi-scanner, which would not cause false positives as these files were absolutely clean, useless and harmless. After the experiment, we made it public and provided all the samples used to the media so they could test it for themselves. We conducted the experiment to draw the security community’s attention to the problem of insufficiency of multi-scanner based detection when files are blocked only because other vendors detected them as being malicious, without actual examination of the file activity (behavior).” The story was reported at the time in the media.
Kaspersky also explained that “After that experiment, we had a discussion with the antivirus industry regarding this issue and understood we were in agreement on all major points.” Further information on cascading false positives can be found here.
“In 2012, Kaspersky Labs was among the affected companies impacted by an unknown source uploading bad files to VirusTotal, which led to a number of incidents with false-positive detections. To resolve this issue, in October 2013, during the VB Conference in Berlin, there was a private meeting between leading antivirus vendors to exchange the information about the incidents, work out the motives behind this attack and develop an action plan. It is still unclear who was behind this campaign.”
False positives are common in the internet security industry. What is not known, and probably never will be, is who creates the bad samples that lead to false positives. As Ronan Kavanagh, CEO at TitanHQ, points out,“Kaspersky is an excellent product, we have never had an issue with it, quite the opposite in fact. Of course we have seen false positives, we were targeted by bad samples as were many other security vendors but we would have no visibility on who carried out these attacks. The critical thing is that as an industry we work together in fighting back”.
Have you discovered false positives when you have run your software security programs?
by titanadmin | Jul 29, 2015 | Spam News |
The threat to corporate data security is higher than ever, with hackers and other cyber criminals devising ever more complex ways of gaining access to company secrets, employee data, and protected health information. IT security teams now need to monitor and track new threats like never before. Phishing emails must be blocked, employees must be prevented from visiting malicious websites, audits must be conducted to check for malware and viruses, and systems protected against keyloggers and Trojans.
The volume of new malware now being discovered is enough to keep IT security professionals awake at night, with many fearing the security of their systems. IT budgets are strained enough as it is, and the rapidly changing threat landscape is placing those budgets under even greater strain.
What Information are Cyber Criminals Trying to Obtain?
Individual hackers may attempt to break through security defenses for any number of reasons, in fact their aims are not always financially motivated. A grudge may be held against an ex-employer. Business practices may be deemed to be questionable. A company’s carbon footprint may even make it a worthy target for attack. Often the aim is to sabotage, with unscrupulous business competitors willing to employ hackers to enable them to gain a competitive advantage.
However, in the majority of cases, cyber criminals attack companies for the data they hold, which can be sold on to the highest bidder on Darknet websites or used to obtain goods, services, or cold hard cash. Data carries a high value on the black market as it can be used for a myriad of different types of fraud.
Healthcare data can be used to fraudulently obtain medical services. Insurance data used to make bogus insurance claims. Social Security numbers can be used for identity theft or to file false tax returns, and credit card details used to rack up thousands of debts in victims’ names. Corporate secrets such as product development information can be obtained and sold to competitors. The theft of that information can be used by competitors to devastating effect.
Some cyber criminals are not interested in stealing data, just in preventing companies from accessing it. If ransomware can be installed, criminals are able to encrypt an entire system and hold the company to ransom. They will only release the security keys to unencrypt data if a ransom is paid.
How Are Criminals Obtaining the Data?
Spam emails and phishing campaigns (via email, social media networks and over the telephone) are common, although one of the biggest threats to data security comes from malware. If malware can be installed on computers or servers, it can record and exfiltrate data to the hacker’s control centers. All communications can be intercepted and all keystrokes recorded. This enables hackers to obtain login names and passwords: Those used to access internal systems or online bank accounts. It is not just corporate data that is at risk. Any information stored on clients and customers can also potentially be obtained by the attackers.
Common Hacking Techniques Used to Gain Access to Data
Some of the techniques used by hackers to gain access to data include:
Cross Site Request Forgery (CSRF)
Even apparently safe websites can allow hackers to install malware or access sensitive data. This type of attack involves legitimate websites sending requests to other sites. Twitter has suffered cyber attacks involving this method, resulting in logins and passwords of site users being obtained.
Web 2.0 Application Exploits
These attacks are difficult to prevent as they are often not identified by standard anti-virus defense mechanisms. They can exploit vulnerabilities in Adobe Flash, XML, JavaScript, JSON and Xpath to deliver malware and malicious code.
Cross-Component Attacks
Take two innocent looking sections of malware code that have been installed on a website. Individually they do no harm, and can easily evade detection. However, when two appear on the same webpage they interact and infect visitors’ devices with malware.
SQL Injection
One of the most popular techniques for hacking involves the insertion of meta-characters or SQL commands into input fields on a website. The commands are able to execute back-end SQL code.
Cross-Site Scripting
Hackers can embed code in URLs which can be used to execute Javascript code on visitors’ devices when the links are clicked.
All Companies are at Risk, and the Majority Have Already Been Impacted by Malware
If you think only small to medium sized organizations are at risk from malware (due to IT security budgetary constraints) think again. Even the world’s largest corporations are at risk from malware. Earlier this year, Apple was targeted by hackers and suffered a serious malware attack. Full details of the extent of the attack were not disclosed, but a number of Apple Mac computers were compromised by the attackers.
How could the hackers install malware on the computers of such a security conscious company with exceptionally deep pockets? Via a perfectly legitimate website! Users had visited a software development website, with the hackers gaining access via an unpatched Java bug.
The biggest social media sites are not immune to attack either. Twitter suffered a malware attack that exposed the confidential accounts of approximately 250,000 users. This is believed to have happened as a result of the same unpatched Java vulnerability.
No Company is Immune to Cyber Attacks
Around this time last year, a medical equipment manufacturer called Neurocare was targeted by cyber criminals. In that attack, all employees of the organization were affected. In that case, it was not the company’s systems that were attacked directly. The malware came via the company’s payroll processor.
These are all very large companies. But last year hackers used malware to pull of an even bigger and bolder campaign, launching an attack on the International Monetary Fund (IMF). As you could well imagine, the IMF has rather robust security controls in place, yet even they proved no match for the hackers. The attackers just went for the weakest link: IMF employees.
That attack involved spear phishing. Individuals working for the IMF were targeted with a highly convincing campaign which allowed malware to be installed on their computers. That attack was highly sophisticated in nature, and is believed to have been orchestrated by a team of hackers who had received backing from foreign governments. Highly confidential data was exfiltrated in the attack.
Phishing Campaigns Have Proved to be Highly Effective
This year, Kaspersky Labs reported a sizable increase in phishing attacks involving Apple IDs. Two years ago, the average number of attacks per day was just 1,000. Only 12 months later that figure had jumped to 200,000 per day.
Even security firms are not immune to phishing scams. RSA, a prominent American computer and network security company, suffered a phishing attack that was caught by the company’s spam filter. The emails were quarantined, yet were opened from within, unleashing a Trojan that harvested data from employee accounts. RSA’s SecurID tagsix was compromised in that attack.
RSA should not be singled out of course. Even bigger companies have suffered at the hands of phishers. An estimated 20% of Fortune 500 companies have become victims of these campaigns. Even the world’s largest corporations have been hit in recent months. IBM has been affected, and bigger companies still. Microsoft and Google are also victims of phishers.
Beware of Blended Threats Delivered Through Spam Email
The web may now carry the highest risk of malware distribution, but email is still commonly used to deliver malicious software. It remains one of the commonest attack vectors used by phishers. Email spam can be used to attack any device capable of receiving and opening email. This means tablets and Smartphones are vulnerable to attack, not just laptop computers and desktops.
One of the biggest threats comes from blended attacks. These are spam emails that contain links to malicious websites, or even legitimate websites that have been infected with malware. These threats are more difficult to deal with. They require a different form of defense that uses a combination of standard email anti-spam controls along with web security defenses.
Spam may not be the favored choice of hackers these days, but it still represents a serious threat to businesses. Dealing with the emails can waste an extraordinary amount of time and money. Spam can take up huge amounts of bandwidth that affects all employees in a company. Dealing with spam adds significant amounts to operational budgets.
The messages by themselves may not be dangerous, but links to malicious websites can represent a serious problem, especially if staff members have not been warned how to identify malicious links. Infected attachments also place computer systems at risk. Both methods can be used to deliver malware, which has potential to cause a serious amount of damage.
A number of defenses can be used to reduce the risk of malware attacks. Anti-virus software is a must, as is a separate anti-malware shield and scanner. Anti-spam controls are vital, as they can prevent the delivery of phishing emails to employees. Web filtering solutions are also highly beneficial. If a spam email gets through to an endpoint user, the software can prevent a malicious website from being visited.
Unfortunately, there is no single control that can be used to prevent all attacks. The solution is to use multi-layered security defenses and to keep them updated.
by titanadmin | Jul 20, 2015 | Spam Advice |
A spam filter is one of the best ways to reduce email spam risk; however regardless of whether you choose this important email security measure, there are a number of steps you can take to reduce email spam risk, keep your devices protected, and your valuable data out of the hands of spammers and scammers.
11 Spam Filtering Essentials to Reduce Network Security Risk
Listed below are 11 spam filtering essentials that you can implement to reduce spam volume and the risk of cyber attacks.
1. A Real-Time Block List (RBL) is essential
Spam is commonly sent from a known spam server – one that has been blacklisted, or is known to be used by email spammers. Using a Real-time Block List (RBL) is one of the best protections, that will prevent malicious emails from being delivered to inboxes. This one email security feature has been shown to reduce spam email delivery by 70–90%, and it only takes a few minutes to implement.
Even if you use a spam filter this measure is important. It will reduce the load on your spam filter, email server, and network. An RBL works by blocking messages before they are downloaded, which will also help to save bandwidth. There are a number of ways to do this, although zen.spamhaus.org is one of the best. It is widely regarded as being the best at spam blocking, is updated frequently and importantly boasts a very low false-positive rate.
2. Recipient Verification will block spam sent to invalid email addresses
Spammers like to bombard companies with emails in the hope that some will get through, or that a catch-all is in place and all will be delivered. Common email addresses used are webmaster@, info@, admin@, sales@ etc. etc. These email addresses are commonly used by companies and there is a good chance that they will be delivered to someone. However, you can use Recipient Verification (RV) to reject the bulk of these emails, and only have properly addressed emails delivered.
To do this, use Microsoft Active Directory integration or upload a CSV file of valid email addresses to your spam filter and mail server. This technique will prevent speculative emails from being downloaded and will similarly reduce the load on your spam filter and mail server, and save bandwidth. This method of spam prevention will take longer to complete than setting up your RBL, but it is a worthwhile investment of your time as it will result in a major reduction in spam delivery.
3. Configure your server to require correct SMTP handshake protocols
This is one of the most effective methods of blocking spambots and it will stop the majority of spambot emails from being downloaded and delivered. This is a fairly quick task to complete, and should only take you a few minutes. You will need to set your configuration to require a HELO (EHLO) with a Fully Qualified Domain Name. However, it is important to note that it may be necessary to add some of your suppliers to a whitelist to ensure that their messages do not also get blocked. Not all of your suppliers and contacts will have their own email servers configured correctly, so genuine emails may be caught and blocked. Individual organizations will find this step particularly beneficial. MSPs less so, or not at all.
By using the above three spam prevention methods – which incidentally can be used on virtually all email servers – you will make a considerable bandwidth saving, and dramatically reduce the number of spam emails that are downloaded. This will also help to protect your network from malware. If you allocate just 30 minutes to do all three, it will save weeks of your time, which can be better spent on other cybersecurity tasks.
4. Regularly scan for viruses
A basic security measure is use is a robust and powerful anti-virus program, regardless of whether you use spam filtering. If you don’t implement spam filtering, this measure is especially important, as you are more likely to have viruses delivered to email inboxes.
Even with spam filtering in place, it is also important to have anti-virus software installed and, of course, AV engine and virus definitions need to be kept up to date. Software should be configured to update definitions automatically.
With spam filtering in place, it should be possible to stipulate the update frequency. Be aware that a different anti-virus can be employed to protect endpoints. Using the same AV engine for mail servers and endpoints means that if for any reason your AV software does not detect a virus, all endpoints could potentially be affected. By using a different AV engine for endpoints and mail servers, you maximize the probability of a virus being detected. Fortunately, competition is fierce in this market, so you should not have to pay top dollar to have two different engines in use.
The following steps will apply if you have a spam filter. These will apply no matter which spam filter is used, be that open source, commercial or even cloud-based spam filtering.
5. Certain attachments carry higher risks so block them!
Executable files – those with a .exe suffix – are particularly risky. Fortunately, it is not necessary to run the risk of a user double clicking on them. The best option is to block these file types and other risky file types if they are not typically needed by staff members. Be aware that spammers are sneaky. It is common knowledge that .exe files are risky, so they mask them with other extensions: PDF, XLS, DOC files for example. To counter this, block by MIME type, not by file extension.
6. Take Action to Block Phishing Emails
Phishing emails can easily fool employees into clicking on links that direct them to URLs loaded with malware. There are a number of URLs that are recognized as phishing websites and it is possible to block these quickly and easily. To do this, use SURBL and URIBL lists to check for website domains that frequently appear in unsolicited emails.
7. Ensure that your spam pattern library is regularly updated
You may find that your spam pattern library cannot be configured manually, as this may be hard-wired into your spam filter. Spam signatures are based on a huge database containing recently added spam, as well as past signatures, with the spam-fighting community adding to the database on a daily basis. There are many different resources that can be used, although if you want to ensure you have a fully up to date database of spam signatures, SpamAssassin is arguably the best choice.
8. Bayesian filtering will recognize more spam and block less ham
A Bayes engine is used by most spam filtering engines and can be trained to recognize spam, and differentiate it from ham (i.e. not spam). It is therefore important to use a regularly updated spam pattern library, which will assign incoming emails with a score, in addition to using feedback provided by end users. The Bayes engine learns what is spam and what is not, and will apply the lessons learned to new emails that are received, constantly improving its detection rates to ensure all spam is caught, and false positives are reduced.
9. Stipulate the spam score that is right for your company
As a system administrator you have the power to decide what spam score is right for your company. This will depend on how much risk you want to take. You will find that spam filters will usually allow you to dictate how aggressive they are, although you may find this requires a certain degree of tweaking to ensure that spam doesn’t get through and ham doesn’t get accidently blocked. A spam score is assigned by a number of factors, although the type of attachments and the email content are the two main ways that the spam score is calculated. This process is not particularly time consuming, but bear in mind that the first two weeks after your spam filter has been installed is when this task will need to be completed. Be sure to use your trial period to tweak your spam filter to ensure that spam is blocked and the number of false positives are kept to a minimum.
10. Get your end users working for you
Your spam filter will not always get things right, and some spam and junk emails will slip through the net from time to time. It is therefore useful to instruct end users to manually mark any spam and junk emails received, should they get delivered to their inboxes. End users can help to train your Bayes engine to recognize new spam emails and correct false positives.
11. Provide email security awareness training to employees
Nowadays it is essential that all staff members receive security awareness training. They must be taught how to identify spam emails, phishing campaigns, and potential viruses. They must also be informed of the correct actions to take if they do discover a phishing scam or suspect that an email may contain malware or a virus. Also instruct them on the correct actions to take if they do accidentally open a suspicious attachment.
Is it the job of a system administrator to train employees how to protect themselves and their computers? Arguably it is not, but it can save a lot of headaches down the line. Even a little training can go a very long way. Unfortunately, this is an area of email security that is all too often forgotten.
What is essential, is that employees are aware of the risks of falling for a phishing campaign or downloading malware. In some cases, it could spell the end of a company, and along with it, their jobs. You can always use CryptoLocker to scare employees into paying attention.
Training could well make all the difference. Besides, if you do provide training and employees still take risky actions and infect the network, you will have a clean conscience and can say it is not my fault! And be justified in saying it.
by titanadmin | Jul 15, 2015 | Spam News |
LinkedIn is a social networking website aimed at professionals, which helps them develop contacts, network, get new business, and find new employment opportunities. One of the main purposes of the site is to build up new contacts, making the site perfect for criminals looking to phish for information. The information that can be gathered can be used against individuals – or organizations – to conduct highly convincing spear phishing campaigns.
What is a Spear Phishing?
You may be aware of phishing, a technique used by criminals to get computer users to reveal their login names, passwords, credit card details and other highly sensitive information. Phishing is like using a trawl net behind a boat. The aim is to catch as much as possible. Sooner or later something will swim into the net. With phishing, spam emails are sent out in the millions in the hope that someone will respond. It is a numbers game, and the unwary will be caught.
Spear phishing on the other hand is not random. Individual victims are targeted. Spear phishing campaigns are often very convincing, and emails are sent containing information that is likely to fool a specific individual – or small group of individuals- into revealing passwords, login credentials, security codes or other information. These campaigns are also highly effective at getting users to click links to malicious websites, or open malware-infected email attachments.
How does Spear Phishing Work?
In order to convince users to install malware or reveal their sensitive information, those individuals must be convinced to take a specific action. To increase the chances of that happening, the criminals behind the campaigns need some nuggets of information. These could be gained from social media websites. People reveal a wealth of information about themselves on Twitter and Facebook, and some leave their accounts open for anyone to see.
LinkedIn is similarly being used by hackers to gain information about users, with the data harvested being utilized in future phishing and spamming campaigns. Data is collected on users, and used to devise phishing emails containing malicious software or links to malware-infected websites, or fake websites which convince users to enter in their sensitive details.
LinkedIn Used by Scammers to Gather Sensitive Data
One of the latest scams identified involves the creation of fake LinkedIn contacts. Accounts are created by scammers, and then used to make connections with people in similar industries. Unfortunately, connecting with these individuals will allow them to obtain a wealth of information on you, such as your employment and education history, phone numbers and whatever information you add to your profile. In many cases, you will be supplying your entire CV to a hacker by accepting them as a contact. Fake LinkedIn contacts are now a major problem as they pose a big security risk.
This means that every contact must be vetted and assessed before you agree to a connection, and who has the time to do that?
How to Spot Fake LinkedIn Contacts
Fortunately, there are some common tells, and a little research (even a couple of minutes) can reveal fake LinkedIn contacts.
No photograph has been added
LinkedIn is all about making professional contacts. Photographs are therefore essential. People like to see who they are connecting with. If no photograph has been added, treat the account with extreme suspicion. Would the CEO of a mining company really be that concerned about someone finding out what he or she looks like?
Stock Photographs Used
Stock photographs can be purchased from image libraries for cents. Complete a quick Google image check against the user’s name and photo. If they are interested in business networking, their photo is likely to appear on other websites. If it appears under a different name, you will know the account is a fake.
Stolen Photographs Used
A photo search can reveal quite a lot of information about the genuineness of a contact. If your prospective contact is a librarian, it is perhaps unlikely they will also be a Ukrainian heavyweight boxing champion (Not necessarily of course!)
Numerous fake accounts have been created with the individuals claiming to be directors of companies. By day, they are the CEO of two or three different companies, by night they supplement their income by producing internet porn (Images have been taken from adult sites and used for LinkedIn). Unlikely perhaps, that CEOs would feel the need to do this.
Some fake LinkedIn accounts are very convincing
Not all fake LinkedIn accounts are suspicious. Many have extensive contacts, and a realistic profile. However often times that information has been lifted from other websites. Sometimes a photo will not have been used elsewhere online, but frequently the text has. One way of checking is to cut and paste small section of their profile and pasting it in Google. It may reveal that the data has been copied from a legitimate LinkedIn account or other social media site.
What is the Risk of Connecting with Fake LinkedIn Contacts?
There are a number of reasons why criminals go to the trouble of creating fake LinkedIn contacts. Spammers can use LinkedIn to obtain email addresses. Criminals can gain information to launch phishing campaigns and information can be gathered to commit identity theft. If a scammer can convince you they are genuine, they may create a fake job for you and get you to reveal some very sensitive information.
Of course the only way to be sure that you are not accepting fake LinkedIn contacts is to only connect with people you know, but that kind of defeats the whole purpose of the website. The answer is therefore to conduct a rudimentary check to make sure the person you are about to share information with is in fact genuine.
by titanadmin | Apr 12, 2015 | Spam News, Spam Software |
Ireland may not produce many highly innovative cybersecurity companies, but Galway-based SpamTitan technologies is bucking that trend. The company has recently been rising up the ranks and has now taken its place among the best cybersecurity companies in the world, according to the latest Cybersecurity Ventures report.
Only four Irish companies have made it into the Q2 2015 edition of the Cybersecurity Ventures Cybersecurity 500 list: Netfort, PixAlert, VigiTrust and SpamTitan Technologies, with SpamTitan now having ascended to position 123.
This is a major achievement, with the company having previously been placed at 393 for the previous quarterly report. The massive jump in position has been attributed to the hard work put in by all members of staff, who are committed to providing the best possible service in the fight against cybercrime. The company can now be considered one of the best, and also one of the hottest new prospects in the world of cybersecurity.
Each quarter, Cybersecurity Ventures publishes its new top 500 list, which features companies from all around the world. Experts in the field of cybersecurity assess companies for the efforts made, as well as determining each company’s potential. CISOs, VCs and a host of security professionals provide their input for the reports.
Many similar reports tend to focus on the size of the company, turnover and profits achieved. This list is different as it is more concerned with potential and innovation. Founder and CEO of Cybersecurity Ventures, Steve Morgan, said, “We do not think a list of the largest cybersecurity companies is useful to our target audience of cyber and IT security decision makers, evaluators, and recommenders”. He went on to say, “They already know who the biggest vendors are. Instead, we give a nod to the hottest and most innovative companies.” It is, after all, these companies that really need the recognition.
The list contains all of the hottest new prospects and top performers, with the ranking based on each company’s merits and prospects. Ronan Kavanagh, CEO of SpamTitan Technologies is proud of the rise in position, and the value of the list. After hearing of the new position in the top 125 cybersecurity companies, he said, “We recognize the importance of being included on such a significant industry list as the Cybersecurity 500.” He went on to say, “At SpamTitan, our staff are assisting our customers on a daily basis in dealing with the constant threat of cyber attack, and this is now as important for the smaller businesses as it is for the fortune 500 company. We are delighted to be working with Cybersecurity 500 in highlighting the need for vigilance and raising awareness for all businesses.”
For further information, and to find out the full list of top 500 companies, visit www.Cybersecurity500.com
by titanadmin | Mar 23, 2015 | Spam Advice |
The administration of usernames and passwords is time consuming business, although there is some good news for system administrators. Both Yahoo and Google have now produced alternatives. Google’s Authenticator and the On-Demand passwords from Yahoo look like they could well be viable solutions, but at the present moment in time, they are not universal. It is probable in the short to medium term that passwords will be required as the last line of defense against cyberattacks. It is essential that the last line holds strong, so two-step verification must be implemented.
Since you are going to have to carry on using passwords for the immediate future, it is a good idea to make some changes that will make administration tasks a lot easier, more straightforward and less time-consuming. Furthermore, we recommend making some changes to ensure your last line of defense is particularly strong. It may be tested.
Improve the strength of your passwords
You can use a Single Sign On (SSO) session to gain access to everything. Many people do. Even cybercriminals. SSO makes life easier because you can access everything you need to with the one password. Unfortunately, a hacker or cyber-criminal only needs to compromise one password in order to gain access to everything as well.
If you decide to use an SSO approach, you had better be sure your password is secure. We advise you to use different passwords for each system and to make sure that each of those is secure. It is better to be safe than sorry.
Regardless of whether you opt for multiple passwords or go for the SSO approach, you need to make it as hard as possible for your password to be guessed. This applies to all network users not just IT staff.
Password controls should be used: Minimum character limits should be implemented, along with other controls to ensure only strong passwords are created.
Furthermore, you should help employees create stronger passwords. Research conducted by Carnegie Mellon University’s CUPS (CyLab Usable Privacy and Security) Laboratory has shown that the addition of numbers to passwords can help improve security, but they determined it is far easier to guess passwords when these are added to the end of a password. This is where many people add them. They use their normal password with the characters and numbers added to the end. It is easy to remember that way, it is accepted by the password controls.
Even when passwords do not contain numbers or symbols they can be more secure than short passwords containing numbers and symbols. “AGoodExampleOfASecurePassword” is easy to remember and doesn’t need to be written down. Write it down and there is a chance it will be found. It is actually much better than using “E&”F*$G” for example. That would be very hard to remember, especially if you have more than one password like that to commit to memory and you need to change it every month. You would need to write it down, which is a major risk.
Additionally, a long password is more secure than using any 6-digit code. That said, make sure at least one capital letter is used (preferably more) and a number and a symbol, and that they are not just added to the end.
Avoid using structural passwords
It is tempting to keep using structural passwords. Many companies use a password such as the individual’s initial and the first four digits of their surname plus four digits at the end. The problem is that if the structure is determined, it makes it easier to work out the passwords for the entire organization, including individuals with full system privileges. If they are simply too practical to give up, only use them for individuals with low-level privileges.
Enforce password changes regularly
The longer a password is used; the more opportunities an attacker has to crack it. If you enforce a change every month or two, this is much more secure than keeping the same password for a year. Since new passwords are difficult to remember, why not take advantage of one of the many password managers that exist, such as Dashlane or LastPass. They are also good at helping with password creation, especially for creating longer passwords (and remembering highly complex ones). For greater security use an offline password generator.
It is also worthwhile checking the strength of your password. Take advantage of the Password Assistant if you use a Mac. CUPS found that password strength meters are effective at ensuring secure passwords are created.
Be careful about your use of social media
Could your password be guessed by anyone with access to your Facebook account? Have you used your pet’s name and published that name on Facebook? Your password strength meter will not know if you have used your dog’s name as your password with an exclamation mark at the end. It will not know what you have published via social media.
Assume your social media accounts may be compromised, and never choose a password using your name, a pet’s name, house name, date of birth, or any other information that is accessible through your social media accounts.
Make your passwords ultra-secure and do your bit to protect your organization
If you use the above controls to ensure your passwords are secure, your organization will be better protected. If a security breach occurs, make sure that it is not your account that a hacker uses to gain access to your system.
by titanadmin | Mar 11, 2015 | Spam Advice, Spam Software |
Passwords are used to prevent unauthorized individuals from accessing accounts, services and software. They keep data and networks secure, they prevent bank accounts from being plundered and ensure only one person can access sensitive information. If passwords are obtained by a criminal, this excellent security measure is worth absolutely nothing.
The daily news is full of stories about companies that have had their security perimeter breached and usernames and passwords stolen. Keyloggers are installed that obtain passwords, and accounts are bombarded by robots trying combination after combination until the right sequence of numbers and letters is found. Dark net marketplaces list passwords for sale by the thousand, and username and password combos can be purchased for just a couple of dollars a set.
How do passwords actually get stolen?
There are many techniques that are used and a myriad of ways that passwords can be obtained. Some of the most common methods are details below:
Keyloggers – Installed on users’ computers via malicious websites and infected email attachments. They record keystrokes and transmit the information to a hacker’s command and control server
Phishing – Users give passwords away by responding to phishing campaigns
Hacking – Security vulnerabilities in websites are exploited and the Active Directory or LDAP database is stolen
Social Engineering – People give their login credentials to bogus callers, fake customer service personnel, or via IT support scams
Is it so easy for hackers to steal passwords?
Sometimes it can be, but oftentimes security controls prevent a username and a password from being obtained. Passwords are often hashed to prevent this. A login name is obtained, and the number of characters in a password, but not the actual password itself as it is often encoded. The hacker must decode the passwords before they can be used.
What is Password Encoding?
There is a big difference between encoding and encrypting. If data are encrypted, they cannot be unlocked without a security key. This is why ransomware is so effective. Once encrypted, data is inaccessible unless a security key is entered. Security keys cannot be guessed.
Encoding is different. The single data field is encoded using an algorithm that hashes the password. When a password is entered, the hashing algorithm checks the text against the stored hashed version of the password. If the two match, access to an application is granted.
So how are passwords guessed?
In UNIX, a hashed password is stored in an LDAP system, but the type of algorithm that was used to encode the password is also stored. The hacker can work out the password if they have a dictionary of hashed values corresponding to the algorithm used.
The dictionary can be searched to find out if there is a match. These dictionary attacks will not reveal every password, but they can identify some of the most common words used for passwords.
A dictionary can be created by running common words through the algorithm. If you run the word “password” through an MD5 encoding algorithm, the hash it produces will be the same as any other system that uses MD5 encoding. This is how passwords are often guessed. It is not a hacker sitting at a computer entering in different combinations one after another in the hope he or she gets lucky. They can quickly run hashed passwords through their dictionary. Many will be revealed.
This is why it is essential that common passwords are always avoided. “Password”, “123456”, “bigguy”, “administrator” etc. It is also why it is important to use more than a few characters. How long would it take a hacker to compile a list of hashed two digit passwords? By the time you get up to 6 or 8 digits, the possible combinations are too numerous to compute. Since hashing allows up to 255 characters, it is not realistic for a super dictionary to be created. However, since many people use common words, and most use 5 or 8 digit passwords, a surprising number can be very rapidly guessed.
If you also use a common word you are asking for trouble, and if you also share passwords across multiple accounts, everything will be compromised if one is guessed.
by titanadmin | Mar 9, 2015 | Spam News |
Facebook hacking is rife and, if it happens to you, you are not alone. Unfortunately, there is no one to blame other than yourself. Facebook hacking is caused, in the vast majority of cases, by poor security practices and a lack of security awareness.
Facebook accounts get hacked because:
- Passwords are stolen in phishing attacks
- Two-factor account authentication is not used
- Passwords are shared across multiple sites
- Keyloggers have been installed on a computer used to access Facebook
If a hacker manages to obtain one password, chances are that same password is used on other sites. Criminals sell passwords online, and there are plenty of would be purchasers. Hackers even buy them on exchanges. Sharing passwords across sites is therefore very bad news, especially on sites that have poor security practices.
Fortunately, on Facebook at least, if you are hacked you can report it easily and should be able to recover your account.
A blocked Facebook account does not necessarily mean you have been hacked!
Facebook does frequently block user accounts. It does this as a security precaution, which is good for all users and offers some peace of mind. How often are accounts blocked? About 600,000 times a day, according to TechCrunch!
That is an awful lot of compromised accounts, yet do bear in mind that Facebook has over a billion users. So 600,000 represents just 0.06% of the total. Which is 6/10,000 if you prefer fractions to percentages.
When Facebook blocks an account is because the account has potentially been compromised. According to Facebook, this occurs when “we are not absolutely confident that the account’s true owner is accessing the account and we either pre-emptively or retroactively block access.”
This means that there is suspicious activity, Facebook often errs on the side of caution and blocks access. That could indicate an account has been hacked, or that action is being taken to prevent the account from being hacked. The good news is that when this happens, only the real owner can get the account unblocked. In theory at least.
When the figures of the number of blocked accounts emerged, the story was widely misreported in the media. Facebook was accused of a “shocking lack of security,” but the compromised account definition had not been read by many Facebook users, and even some reporters. Also bear in mind, that those 600,000 blocked accounts will include many false positives.
Determining exactly how many Facebook accounts have been hacked is rather difficult, unless you work for Facebook and have access to that data. It is possible however to come up with a fairly reasonable estimate, based on research conducted by security and market research firms. Their data can be used to get a reasonable estimate.
Take Statista’s figures for example. It conducted surveys on individuals who had been hacked, and 66% said they had had their Facebook accounts compromised. Then combine that with study data from Pew Research. The company determined that the volume of “internet users have had an email or social networking account compromised or taken over by someone else without permission” was 22%.
Using a simple calculation an estimate can be obtained: There are 1 billion Facebook users. 22% of individuals claim to have had an account hacked, and Statista says 66% of those were Facebook accounts. That works out at 145 million users, which should be a fairly reasonable estimate.
Fortunately, Facebook security is robust. A mobile phone is required as part of the account recovery process, so you would need to have lost that as well in order for your challenge question to be used to login. SSL certificates prevent network snooping, and the brute force approach will be prevented by Facebook’s security controls. But phishing scams are likely to leave your account open.
Fortunately, there are ways that you can protect yourself, and your Facebook account.
It can be difficult to avoid phishing scams, and all too easy to fall for one. One of the best defenses is to use Antispam software. SpamTitan’s software will prevent phishing campaigns from being delivered to your inbox. Parental controls at home, and web filtering controls at the office are excellent ways of blocking malicious links.
Unfortunately, not all access points have the above controls, so you will have to rely on common sense and become more security aware. For example:
- Never click on a link that appears to take you to an unfamiliar site.
- Never open email attachments sent from unfamiliar senders.
- Use different passwords – don’t share them between websites
- Use complex passwords, containing characters, capitals, and numbers
- Don’t share everything about your life on social media
- Change passwords regularly, certainly every 6 months
- Don’t reuse passwords
- Keep your anti-spam software, virusguard, and anti-malware programs updated, and scan regularly
- Set your account recovery options and security questions as if they were passwords
And remember, just because you have friends and family on Facebook, don’t let it create a false sense of security. You can never be sure how security conscious they are! Complacency is likely to leave you vulnerable to hackers.
If your Facebook account has been hacked, let us know. We want to hear your stories!
by titanadmin | Feb 15, 2015 | Spam News |
Phishing emails may not account for a high percentage of total email traffic, but they are becoming more prevalent. In fact, since 2014 the growth of these malware spreading emails has tripled, according to a new report issued by Kaspersky Labs.
Kaspersky determined that the percentage of phishing emails in total email traffic is now 0.0071%. Compare that to spam emails which accounted for 66.34% of all email traffic in the first quarter of 2014, and the figure seems very small. However, the damage that can be caused by the emails is considerable. For some companies, the damage can be catastrophic. When phishing emails lead to financial losses, funds can rarely be recovered.
Phishing emails are becoming increasingly common, but spam appears to have declined a little. A fall of 6.42% was registered since the last quarter of 2013.
Social Media Overtakes Email as Main Method of Phishing Campaign Delivery
Phishing campaigns are frequently delivered to potential victims via email. A link to a malicious website is sent – often randomly – to individuals in the hope that they are fooled into clicking. That link will take the person to a website where they are required to enter confidential data such as login names and passwords. Oftentimes, visiting the website will result in malware being downloaded to the visitor’s computer.
Spam emails are still favored by cyber criminals in some countries such as China and South Korea; however, social media has now overtaken email as the main method of delivery of phishing campaigns according to Kaspersky.
This may not come as a surprise. Rather than hackers sending the campaigns to new victims, victims of phishing campaigns share the links voluntarily (and unwittingly) via Twitter and Facebook pages. Infecting new computers could not be any easier.
Infected email attachments are still a popular method of malware and virus delivery. If these attachments are opened, the user will install malware and viruses on their device.
Top Ten Malicious Programs Spread by Email
Even with the rise in popularity of social media for malware delivery, spam emails are still responsible for spreading a huge volume of malware. In Quarter 2 of 2014 alone, Kaspersky Labs were able to block an incredible 528,799,591 malware attacks. The volume of different types of malware is also astonishing. During the same period, Kaspersky Labs detected and blocked 114,984,065 unique potentially unwanted objects.
Many of the viruses and malicious programs are camouflaged to look innocent. Take the most popular malicious program used by cyber criminals as an example. Trojan-Spy.HTML.Fraud.gen appears to be a standard HTML page containing a form for online banking. When data is entered, the information is transmitted to hackers who are then able to use the information to gain access to users’ bank accounts.
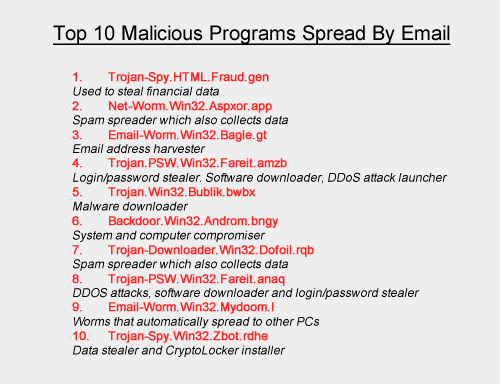
Cybercriminals Earning over $100 Billion a Year
Cybercriminal attacks are increasing in frequency and severity, and this is unlikely to change given the huge sums of cash that can be obtained. According to recent estimates by the FBI, the proceeds of cyber crime are in the region of $100 billion per year. The bad news is that criminals are devising ever more sophisticated ways of attacking organizations, and many of those organizations are ill-prepared to deal with the risks. Oftentimes even basic security measures against cyber attacks are found to be lacking. This is due to extremely limited IT security budgets, which hamper efforts to deal with all the threats.
Many organizations do not have clear and concise IT security policies in place, and do not place an individual in overall charge of cybersecurity. Sometimes there is not even a dedicated IT security professional employed and many organizations are still not providing all members of staff with security awareness training.
A failure to employ the appropriate staff, allocate sufficient budgets to IT security and train the staff can prove very costly indeed. Lost and stolen data, system downtime and drained bank accounts result in far heavier losses than the cost of implementing security measures to prevent attacks. Even the cost of new IT security staff will pay dividends in the long run.
Staff Security Awareness Training is Critical
Spam emails and phishing campaigns generally have one of two main aims: To trick users into revealing sensitive information or to fool people into downloading and installing malicious software and code. The latter allows hackers to take control of computers and infiltrate networks.
Spam and phishing emails can be very convincing, yet there are a number of tell-tale signs that emails are not all they appear to be. By providing training to staff members on these tell-tale signs, the risk of employees falling for a scam can be drastically reduced.
Email Security Solutions Must be Employed to Protect Sensitive Data from Attack
Can you be sure that staff members will be vigilant and security aware? Unfortunately, even with training, employees will make mistakes. They are human after all. It is therefore important to install security solutions that will limit the volume of spam emails that are delivered to employees’ inboxes.
One of the best solutions is a spam filter such as SpamTitan Anti-Spam. This data security solution has now been employed by IT security professionals in over 120 countries around the world. They benefit from being able to block over 99.7% of spam emails.
Since SpamTitan uses two separate anti-virus engines (Bitdefender and Clam AV) the catch rate is particularly high. Furthermore, SpamTitan includes an anti-phishing module as standard that filters out emails containing links to known malicious websites. This further reduces the risk of an employee accidentally clicking on a link and downloading malicious software. Consequently, SpamTitan is one of the best investments to protect against cyber attacks.
by titanadmin | Nov 13, 2014 | Spam Advice |
You may be trying to reduce your company’s carbon footprint, but what efforts have you made to reduce your company’s data footprint?
If your company is attacked and hackers gain control of your servers, they will not be able to gain access to data that are not stored on your systems. If you use cloud archiving, you can migrate old data that you are not legally permitted to delete and keep your company information safe and secure. It is possible to reduce your company’s data footprint without incurring major expenses.
Use the cloud to reduce your company’s data footprint
The cloud offers many advantages to companies. It is not just a matter of protecting data from attack. Data need to be stored somewhere and the hardware required is expensive. Space must be dedicated to storage, which could be much better purposed. A server room doesn’t make most companyies any money. An extra telemarketing operation based in the same space would. It would arguably expose the company to less risk.
The huge cost of data storage can be avoided
Data storage requires hardware, and that hardware costs a lot of money to purchase, keep supplied with power, and kept cool. Hardware can also malfunction spontaneously, or as a result of power spikes and cooling issues. It is no surprise that the cloud has proved so popular. It eliminates the cost of purchasing and maintaining rooms of computer equipment.
Amazon realized this and started its Amazon AWS business. Small businesses especially would benefit, as they would not need to buy expensive hardware. Large companies could make huge savings, reducing staff costs as well as equipment costs.
Cloud services benefit all
There were a number of things that all came together to allow Amazon AWS – and cloud computing in general – to be offered to businesses. Virtualization was critical, as were Microsoft Hypervisor and VMware. Companies such as Amazon were able to use a single server to run multiple systems and to divide those among its customers. Standardization resulted in data being transferred to the cloud. After all, it didn’t make sense to have a separate device for every function and, if those devices could be housed in a huge data center with the cost covered by someone else, that made a lot of sense.
Of course, it is not just the cost of the equipment and the running cost that can be saved. Computers require software and software is licensed. Every license adds to the cost. For cloud service providers it makes sense, as they can get a lower license cost by buying hundreds or thousands of licenses. The same goes for equipment purchases. Amazon AWS gets a much better price on its tens of thousands of computers than a company that only requires one.
Staff costs are reduced because one dedicated individual can service many hundreds of servers. They can also be given tools to do this to reduce the time it takes. This is not an option for SMBs.
Is it possible to reduce your company’s data footprint and stay secure?
Unfortunately, no data protections are 100% secure. If you want to reduce your company’s data footprint, you will not reduce your level of risk to zero. It doesn’t matter where data are located, there will be a possibility that the data can be accessed. The aim is to maximize security and reduce risk as far as possible, but you will never get that risk down to 0%.
Cloud storage however is likely to be as close to 0% as you are likely to get as a small business owner. The protections put in place to secure cloud data are considerable. Cloud service providers must ensure their customers’ data are protected, because a data breach could potentially destroy all faith in their business. As a result, highly sophisticated multi-layered security defenses are used. The data are protected by teams of personnel, 24/7. The resources available to cloud service providers are many orders of magnitude greater than those available to a SME. In short, the cloud will give you the best security you are likely to be able to get.
Cloud archiving and backups also ensure that state and federal regulations are satisfied. SOX and HIPAA require data to be backed up and stored off site. Those backups must also be secured. If data is encrypted and stored in the cloud, even if a security breach does occur, the data will not be accessible by the hacker. Use a cloud service provider that encrypts data at rest and in motion, and you will have the best security you can get. You will just need to make sure your encryption keys are not stolen.
Backup your data but maintain an email archive for GDPR compliance
With your data backed up and secured in the cloud you will be protected against data loss, but what about accessing your data? With a backup you will be limited. If you need to access certain files, or search for data elements, you will need an email archive. An email archive is a store of data that you can use whenever you need to. You can recover or access email data as and when required without having to restore everything as you would need to do if you only had a backup.
An email archive will certainly be of benefit to companies that retain EU citizens´ personal data on email. Following the enactment of the General Data Protection Regulation (GDPR), EU citizens now have the right to request access to personal information, correct or complete it where necessary, and delete it (the “right to be forgotten”) when there is justifiable cause. Companies that rely solely on backed up data may face a logistical nightmare to respond to data access requests within the thirty days allowed.
Furthermore, a cloud-based email archiving solution is more likely to protect data from loss, theft or unauthorized disclosure as required by GDPR. With audit logs and real-time monitoring, companies will be able demonstrate their efforts to comply with the EU regulations – a mitigating factor should a data breach occur.
ArcTitan – The convenient and cost-effective email archiving solution
You may want to reduce your company’s data footprint, but some data needs to be accessed and searched often. Email for example. You can create a backup of your PST files, but restoring them means restoring the whole email account and that can take hours. On top of that, all mail items will be restored, even those that are no longer required.
An email archive is the logical solution. Individual emails can be accessed and restored when needed. If you ever need to access files stored in an email account, or access old emails, you can with an email archive: Quickly and easily. The archive is tamper-proof, ensuring a permanent copy of each original email is retained – Something that is essential for compliance and to meet eDiscovery requirements.
ArcTitan allows data from Google Docs, Office 365, MS Exchange, Zimbra and Lotus to be restored, as well as individual emails. Searches can be performed to find the required email or document. Plain text queries can be made from a desktop, laptop, mobile phone or tablet. The data does not need to be retrieved first, as the search can be performed and then the individual file or email accessed.
All emails stored securely on Replicated Persistent Storage on AWS S3 and are automatically backed up. ArcTitan features single instance storage, which means that only one copy of of the email is stored. This is achieved through de-duplication of messages. Not only does this reduce storage space, it means searches are much faster. When you search, instead of returning multiple copies of the same email, your list will only include unique emails, which makes finding the email you need much faster. How fast? You can search up to 30 million emails a second, and emails are automatically sent to the archive at a rate of around 200 a second.
Move your data to the cloud and you can lower your operational costs, improve data security, and access your data whenever you need to. You can reduce your data footprint without violating state and federal regulations, and still maintain access. Store your backed up data in an encrypted file in the cloud, and maintain access to your old emails by creating an email archive in the cloud.
Some of the Main Features of ArcTitan
- Scalable, email archiving that grows with your business
- Email data stored securely in the cloud on Replicated Persistent Storage on AWS S3
- Lightning fast searches – Search 30 million emails a second
- Rapid archiving at up to 200 emails a second
- Automatic backups of the archive
- Email archiving with no impact on network performance
- Ensure an exact, tamperproof copy of all emails is retained
- Easy data retrieval for eDiscovery
- Protection for email from cyberattacks
- Eliminate PSTs and other security risks
- Facilitates policy-based access rights and role-based access
- Only pay for active users
- Slashes the time and cost of eDiscovery other formal searches
- Seamless integration with Outlook
- Supports single sign-on
- Save and combine searches
- Perform multiple searches simultaneously
- Limits IT department involvement in finding lost email – users can access their own archived email
- Compliant with regulations such as HIPAA, SOX, GDPR, Federal Rules of Civil Procedure, etc.
by titanadmin | Oct 16, 2014 | Spam Advice |
Is archiving old emails worthwhile?
For a business, archiving old emails is essential. It can save time, money and also prevent legal issues.
Even so, many companies do not archive old emails and use backups instead. This is a mistake. The purpose of a backup is to allow lost data to be recovered in the event of a system failure, accidental deletion, fire, or cyberattack. Any time data is lost, it can be restored from a backup tape. A backup is therefore an important failsafe.
Backups are not typically saved for a long period of time. Backup tapes are used again and should not be kept indefinitely. If you store backups for legal reasons and have thousands of tapes, you will be spending a small fortune on the wrong technology.
The reason? Backups are not designed to be searchable. If a file is present in a backup it can be restored, but searching for information in a backup file can be difficult and time consuming. Finding information can really be a chore.
An archive is different because email archiving allows fast searches to be conducted. If you sent an email on a particular date, to a particular person, it would be a relatively easy task to obtain this from a backup. However, if you sent an email containing information about a report, or you can only remember certain words, finding that email in a backup could be very difficult indeed. Fortunately, an email archive can easily be searched. Just use a particular word or search term and you will be able to find the missing email in next to no time at all.
Legal requirements for storing data (HIPAA, SOX, GDPR, etc.)
There are legal requirements relating to stored data. Many industries are required to keep data for a long period of time. If a legal request is made to supply data under the Federal Rules of Civil Procedure, finding the required information can take an extraordinary amount of time. It may be necessary to search through many different daily backup tapes to find the required information.
The same scenarios apply if a company works in a regulated industry and is legally required to store data under the Healthcare Insurance Portability and Accountability Act (HIPAA) or Sarbanes-Oxley Act (SOX). Outside of regulated industries, companies storing the personal data of EU citizens on email have to comply with data access requests within thirty days under the General Data Protection Regulation (GDPR). This could be a logistical problem for many EU-facing companies without a searchable email archive.
An email archiving solution that automatically copies emails as they pass through the mail server also complies with legal requirements stipulating an electronically stored information must be “immutable” – i.e. presented in its original form without alteration. Indeed, GDPR insists that mechanisms must be put in place to prevent the accidental or deliberate alteration or deletion of emails as well as to prevent loss, theft or unauthorized disclosure. Back up tapes do not fulfill this requirement.
Email archiving can save you money
- Due to the security risk, backups are often encrypted. To find information, data must be unencrypted, sifted through, restored, and encrypted again. This takes time. In an email archive, information can be obtained much more quickly.
- The more storage space you need the more it will cost. Using backup tapes is an expensive way of storing old data. Email archiving on the other hand allows storage space to be used much more efficiently. Archiving systems can remove duplicates and that can save a considerable amount of space.
- It is easy to move an archived email from one location to another. Migration is simple, even when moving to an updated server.
- Space is at a premium, especially when it comes to email. Email is usually housed on a server that has limited space. Limits have to be set on individual mailboxes, which means many users end up deleting emails when they have reached their storage limit. Busy professionals don’t have time to do this and typically delete huge volumes of emails – including many that are important. IT departments then get requests a few days later asking for a hastily deleted email to be restored from a backup tape. An efficient archiving system eliminates this headache.
- Old emails need to be checked to identify data leakage. When an insider is found to have stolen data it is essential to check email accounts to find out what has been stolen. When audits have to be conducted, it is far easier with archived email than obtaining data from backups.
The flexibility provided by an email archiving system is essential for businesses. It makes old emails much easier to locate, information can be retrieved rapidly, and it is a more cost efficient method of storing old data than backups. If you have yet to implement an efficient archiving system, now is the time to do so. In the long run it will save you a lot of time, effort, and money.
by titanadmin | Aug 20, 2014 | Spam News |
Cyber criminals are using phishing to lure web visitors into revealing their sensitive data. Internet surfers are presented with a baited hook, which draws them into revealing login names, passwords, security keys and other valuable data.
The technique can be employed by individuals with little to no hacking skill, luring users to a malware-ridden website in exchange for payment. There are plenty of would-be criminals looking to make a quick buck, and since the campaigns can be so effective, online thieves and criminals are increasingly using this technique to make money.
Many online criminals use phishing in random campaigns sent via email. There is little skill involved. It is simply a numbers game. If enough emails are sent, sooner or later someone will respond and fall for the bait. However, we are now seeing much more sophisticated campaigns launched.
It used to be easy to spot a phishing email. They were littered with grammatical errors and spelling mistakes. Images were used that were clearly fake, and the emails would only fool the most unsuspecting computer user. They claimed victims, nonetheless, but only a few.
Some of the phishing emails now being sent are extremely convincing and very difficult to identify. Even well trained, security-conscious IT professionals have fallen for some of the scams. The reason? They work by exploiting traits in human behavior and use techniques that are particularly effective at drawing the required response.
Human Traits Successfully Being Manipulated by Hackers
Cyber criminals are exploiting human behavior to get users to click on links to malicious websites or open attachments. They rely on common traits that are all but guaranteed to get the desired response. The male of the species, for instance, is easily tricked into opening an apparent JPEG file if he is promised a glimpse of bare female flesh. An offer of sex from an unknown admirer can also work particularly well.
Not everyone is motivated by sex. For others the promise of financial gain does the trick. Criminals exploit greed to get users to click on a link. A money making scheme, or a hot stock tip, can entice many people to click on a link. Curiosity is also exploited. Major news events, conspiracy theories, celebrity news, and information on natural disasters have all been used by email spammers and scammers to get people to visit a malware site or open an email attachment.
Even the sense of duty has been exploited. Emails are sent from the accounts of work colleagues, bosses, civil authorities or law enforcement officers. These are effective at fooling users into complying with requests.
By exploiting human traits and evoking emotions, recipients of these scam and spam emails swallow the hook, and often the line and sinker too.
Spear Phishing: Effort Put in is Rewarded with More Victims
The sending of millions of mistake-ridden emails results in very few individuals falling for the scams. When email spam filtering software is employed, the filters will prevent these emails from even being delivered.
However, a little research goes a long way. Phishers who invest time into researching victims can see the time they spend on the campaign really pay off. A search on social media will reveal a considerable amount of information on an individual. Employers can be found on LinkedIn, Facebook can be used to find out friends’ names, and Twitter exploited to find out a user’s interests. With this information, highly effective campaigns can be developed.
These phishing campaigns are referred to as spear phishing. As the name suggests, the hacker goes after one fish. These campaigns can be incredibly effective as they exploit trust. If an email is sent that appears to be from a friend or colleague, it is far more likely to be opened. But how is this possible?
SMTP Weaknesses Are Exploited by Phishers
Unfortunately, the SMTP protocol contains a security weakness. Hackers can exploit this weakness to mask the true sender of an email and the return address. To the casual viewer it appears that the email has been sent from a known individual, and even replying to the mail appears to direct it to the correct mail recipient.
Fortunately, a spam or phishing email is not dangerous. It requires an action to be taken by the recipient. Deleting such an email will delete the risk. Only opening the attachment, downloading it, or visiting a link contained in the email will result in the delivery of malware, a virus or the installation of malicious code.
Unfortunately, while most employees know never to double click on a file with a .exe extension, file extensions can be all to easily masked. They can be made to appear as a PDF file or JPEG, or other supposedly innocent file type. Without training, users are likely to open these attachments, and unwittingly activate the executable file.
The way to prevent users from clicking on links and opening attachments is to provide them with security awareness training. Teach staff members how to identify phishing campaigns, and they can check the genuineness of emails before they take action. Developing a culture of security awareness is therefore essential in the fight against cyber crime.
Blocking the emails with a spam filter is even better. That way, the email will never be downloaded and delivered. Unfortunately, from time to time emails do slip through the net. When that happens, employees must know how to react.
Training is therefore important even if a robust and reliable spam filter is used. After all, it is best to be shown how to deal with a phishing email that never arrives than to fall for the first one that gets past a spam filter.
by titanadmin | Aug 6, 2014 | Spam News |
The news is full of reports of data breaches that have been suffered by companies and even governments. Numerous media reports detail how hackers have managed to obtain tens of thousands of confidential records, or in some cases, tens of millions or more. However, it is rare that a hacker is caught and brought to justice for the crimes committed.
Recently, a hacking group in Russia was reported to have stolen a staggering 1 billion passwords. If that was not shocking enough, the authorities know the individuals are located in central Russia. They are also in their early 20s. If they have been identified, why have they not been arrested?
Bringing hackers to justice is complicated
In this case, there are problems because it is the United States that wishes to take action. The crimes were committed against Americans but some countries are unwilling to turn over their own citizens to other countries. In this case, should the criminals be tried in Russia or in the United States? Where should justice occur, where the crimes were committed or in the country most affected by the crimes? Should hackers be extradited?
If there is no treaty in place between two countries, hackers will be tried and sentenced (or not) in their own countries. The United States has tried to get five Chinese hackers extradited and brought to the United States to face trial. They worked for the Chinese military. China is unlikely to take any action, and certainly will not release them to the United States. The individuals are believed to be behind attacks on Alcoa, U.S. Steel and Westinghouse, as well as on other U.S. firms. The criminals were indicted, but that is as far as the U.S. got. They are very likely working on new hacks against U.S. companies.
In some cases, hackers do not need to be extradited. The FBI has previously tricked hackers into coming over to the United States voluntarily. By doing so the tricky issue of extradition has been avoided. The FBI set up a job interview for two hackers using a fake Seattle company. The pair, Alexey Ivanov and Vasily Gorshkov, arrived for the interview and were promptly arrested. The latter received a sentence of 3 years, the former got 48 months.
Spam email kingpin sent 30% of all junk emails!
If you are a cybercriminal or spammer and you have launched attacks on Americans, it is a wise move never to visit the country. However, some just can’t resist. When visiting a car show in Las Vegas in 2010, Russian super-spammer, Oleg Nikolaenko, was arrested and charged for his crimes. He had used a botnet to send the spam emails. That botnet included a staggering half a million computers. Even more staggering was the volume of emails he sent. An estimated 10 billion per day. He is awaiting trial.
Hackers are very good at hiding their real identities and consequently can be difficult to locate. It can be even harder to bring them to justice.
It should come as no surprise to hear that many successful hackers are based in countries that offer protection against extradition to the United States. Unless there are international laws signed, and more cooperation between countries to tackle the global problem of cybercrime, they are unlikely to be tried and sentenced for their offenses.
by titanadmin | Jun 3, 2014 | Spam Software |
There is good news for users of SpamTitan Technologies’ anti-spam solutions. The company’s innovative solutions for dealing with email spam have been awarded VBSpam+ certification from Virus Bulletin. The Virus Bulletin anti-spam software tests are widely regarded to include some of the email security industry’s most rigorous tests, and the results are trusted by industry professionals and users alike.
The anti-spam award is only issued to companies whose spam solutions are shown to be effective in practice. Any product that fails to block sufficient volumes of spam emails will not receive accreditation. SpamTitan has performed consistently will in Virus Bulletin Tests, and this is the 28th consecutive time that the company has received an anti-spam ranking from the bi-monthly tests run by Virus Bulletin.
In contrast to previous tests, Virus Bulletin has assessed products on two counts this time around. Spam catch rates were examined in addition to the number of false positives. Overactive anti-spam products that block genuine emails can cause many headaches for businesses. Any email that is incorrectly blocked could potentially mean the loss of a client. It is therefore essential for an anti-spam solution to have a very low false positive rate.
When tested in May 2014, SpamTitan registered 0 false positives. In March when the test was last run, SpamTitan also registered a false positive rate of 0. These results were among the best recorded for all email spam solutions tested by Virus Bulletin. In fact, SpamTitan has only recorded one false positive result since November 2013, demonstrating the consistency of the product. It continues to deliver industry-leading standards of spam-detection. Users of the product also benefit from an extremely competitive pricing model.
SpamTitan Demonstrated a Spam Catch Rate of 99.81%
The May 2014 test for spam blocking saw SpamTitan register a catch rate of 99.81%, with only a slight drop registered since the test was last performed in March, when 99.85% of spam emails were blocked. The consistent results and superior spam-blocking also saw the company receive its fourth VBSpam+ award for exceptional performance. This earned the company a position in the Top 5 anti-spam products under test. The spam-catching percentages achieved over the past months have also been very high, with the lowest rating being 99.73% (January 2014.)
CEO of SpamTitan Technologies, Ronan Kavanagh, was proud of the high ranking and spoke of the importance of having an independent third party conduct performance tests. He pointed out that the Virus Bulletin test results can be trusted as they have no bias. Organizations looking to deploy an anti-spam solution can therefore rely on the results and choose accordingly. Companies already using anti-spam software can also view the results to assess how well their chosen product fares against the competition.
An anti-spam solution must be effective, as any spam emails that get past the filter could potentially result in a phishing email being delivered to an employee. The high catch rate shows the quality of the product that uses not one but two different anti-virus engines to ensure dangerous emails prevented from being downloaded and delivered to end users.
by titanadmin | May 29, 2014 | Spam News |
eBay customers have started to receive emails advising them to change their passwords. Their user names and passwords have been obtained by hackers, and a new password must be set for security reasons.
Unfortunately for many eBay account holders, the requests to change passwords have not been sent by eBay, but by phishers. The emails contain a link to a website which looks like eBay, but it isn’t. It is a fake website devised to get users to reveal their current passwords. This sneaky phishing campaign is likely to catch out many eBay account holders.
Data breach was suffered, but not identified for 2 months
In late February/early March, three employees of eBay had their login credentials compromised in a cyberattack. The cybercriminals used the login credentials to access a database containing the names of 233 million site users. Phone numbers, addresses, email addresses, dates of birth, and customer names were stolen, along with encrypted passwords.
In early May, eBay became aware of the breach, two months after it occurred. The company then waited a couple of weeks to make the announcement. The delay was because eBay didn’t realize that account information had actually been stolen. It took the best part of a month to realize data were actually stolen in the attack. Fortunately, PayPal information was not compromised and neither was any financial information.
A breach that does not involve bank account details or credit card information being exposed can still be serious and, in this instance, eBay account holders are at risk.
Passwords may have been encrypted but hackers I’ll be able to guess some as they have a lot of personal data. Dates of birth for example. They are often used as passwords. Since email addresses were obtained, the victims that have not had their passwords guessed are now being spammed with phishing campaigns.
Most customers will be aware of the exposure of their data and as a result, they may believe the phishing emails to be genuine. If they do, they will inadvertently reveal their passwords when they attempt to change them.
Investigations launched into the eBay data breach
Investigations into the eBay data breach have now been launched by state attorneys general in three States – Connecticut, Illinois and Florida. In Europe investigations are also being conducted. The attorney general of New York has spoken out about his expectations. He believes credit protection services should be offered to breach victims without charge. At the present moment in time, eBay has no plans to offer any risk remediation services to customers.
eBay has been criticized for the slow identification of the breach, as well as the slow response when it was discovered. Initially there were no victims, then there were 145 million. eBay finally settled on 233 million accounts.
It may not be a problem for spammers to send 233 million emails, but for eBay that has taken some time. The company tweeted news of the breach, but email notifications took a considerable amount of time to be sent. This may have resulted in more individuals responding to the phishing requests.
eBay breach victims must exercise caution
A data breach of this magnitude, affecting a company as large as eBay, is worrying. How good were the security measures it had in place? Why was the phishing campaign not identified before three people responded? Why were the phishing emails not blocked and prevented from being delivered? Only time will tell.
Since information has been compromised, and hackers are now attempting to guess passwords based on the personal data they have acquired, it is a wise security precaution for account holders to login to the site directly and change their passwords. They should not respond to an email, as it may be a phishing campaign.
by titanadmin | May 26, 2014 | Spam News |
Unfortunately, all it takes to lose swathes of customers and destroy the reputation an ISP is for a single email spammer to get a block of your IP addresses blacklisted by a number of ESPs and RBLs. It is a nightmare scenario, yet it is one that could all too easily play out.
Customers using any of the blacklisted domains would have their outbound emails blocked and, if they cannot send emails, they will leave in their droves for another provider. Perhaps even worse than losing those valuable customers will be the comments they invariably post all over the Internet. Negative feedback can seriously damage a company’s reputation and it can take a long time for a damaged reputation to be restored.
There are steps that can be taken to at least temporarily fix the situation. The IP addresses affected could be swapped, and netblock could be used as a temporary fix. Unfortunately, recovering blacklisted IP addresses is a very slow process. During this time, other IP address blocks could be lost.
Managing risk is difficult. It is possible to set limits on the number of emails that can be sent by a particular domain. Alerts can be configured to identify a domain that is being used to send spam, and it may be caught in time to prevent blacklisting. IP netblocks can be changed should it not be possible to prevent a domain being blacklisted by ESPs and RBLs.
The process of undoing the damage caused by spammers is a nightmare as well. New domains must be warmed up, and efforts made to ensure they are operated within acceptable ESP limits. Otherwise they will just get blacklisted again and the process must restart.
Fortunately, there is a solution that can be adopted by MSPs and ISPs that can prevent blacklisting. Install the latest version of SpamTitan!
SpamTitan v6.3 includes outbound email filtering
SpamTitan will prevent spam emails from being delivered to inboxes; however, version 6.3 also includes a sophisticated and powerful outbound email filter that can be used to prevent spam emails from being sent from accounts. If a domain is hijacked and used to send spam emails, or is used by an individual within your organization, the emails will be blocked and the ESP will not be alerted.
SpamTitan v6.3 uses the same identifiers to clean and filter outbound email as it does for incoming spam. System administrators can set rate limits by email address, IP address range, or domain.
If an organization needs to send a high volume of emails, to avoid inadvertently causing problems with an ESP, a pool of IP addresses can be used to send email and these can be rotated. This allows risk to be effectively managed. Damage to the reputation of IP addresses and the business itself can be easily prevented.
Any MSP providing multiple client domains can implement SpamTitan v6.3 and ensure that emails are sent safely, while the risk of blacklisting is kept to a bare minimum. The Anti-Spam solution will also ensure that incoming emails are cleaned and spam is quarantined, while the Anti-phishing module will protect against malicious attachments.
by titanadmin | Apr 24, 2014 | Spam Advice, Spam Software, Website Filtering |
If you are a network decision maker, what should be your main focus? Which issues should demand your attention? This post covers five important considerations if you want to protect your critical assets.
The current threat landscape has become very serious
If you work in a large corporation, chances are you will not need to be reminded about the seriousness of the current threat landscape. However, if you work in an SME, the severity of the current situation may not be so apparent. According to the results of the 2012 Verizon Data Breach Investigations Report (DBIR), the main threat of data theft comes not from hackers intent on profiting from selling stolen data, but from hacktivist groups. In 2011, hacktivists were behind 58% of data breaches. Hackers were involved in 81% of all data breaches reported throughout the year.
One of the main issues in 2014 are what Verizon calls “low and slow attacks.” These are authentication attacks, web exploits and social engineering-based attacks. Malware is evolving and carries a much higher risk than when many companies deployed their security systems. The threat landscape is constantly changing and you must stay alert to the changing risks.
Corporate data is one of your biggest assets – Protect data like you protect your financial assets
Company data is incredibly valuable to cybercriminals. Credit card numbers (with expiry dates, holder names and CSCs) sell for up to $6 a set. If hackers obtain several hundred or several thousand, they can make a tidy profit. If Social Security numbers can be obtained, in particular those of minors, they can sell for up to $200 a set, especially if accompanied by medical records. Bank account information is also valuable. Account information can be sold for up to 10% of the balance of the account. As for proprietary company data, to the right person that could be sold for millions of dollars. Data is highly valuable and criminals will attempt to steal it. You must therefore ensure it is appropriately protected.
End users are actually the first line of defense
Firewalls and other systems designed to repel DDoS attacks and stop malware from being installed may be seen as the first line of defense; however, your end users are actually the first line. They are also the weakest link in the security chain, and cybercriminals know it. Many criminals target end users as it is easier to get them to download malware or reveal login credentials than to break through a firewall.
If you want to keep your network secure you must provide training and make end users more security aware. They must be instructed how to identify phishing campaigns, be shown good practices to adopt when surfing the Internet or using email. Social media best practices must also be taught, especially if access to the websites is not blocked.
Application and platform management policies need to be developed
In order to protect networks and connected devices from being infected with malware and viruses, policies must be developed covering the permitted uses of computer equipment, applications, Smartphones and other BYOD devices.
Even some companies that have adopted BYOD have not issued staff members with detailed policies on the allowable uses of their devices in the workplace. SpamTitan recently conducted a research study that showed a third of organizations have not covered the use of messaging and collaboration tools in their corporate policies. Make sure the use of Smartphones, tablets, portable storage devices, collaboration tools, email, Social media, and web 2.0 applications are all covered. This will help to ensure staff do not take unnecessary risks.
Prohibition didn’t work – Neither do blanket bans
Total bans on the use of Smartphones, laptops, social media, or online shopping at work will not prevent end users from bringing their devices to work or using the Internet for personal use. Controls such of these may actually have a negative impact on staff happiness and productivity. Many employers believe the reverse is the case and issue total bans. Controls must be implemented to prevent theft of data, but carefully consider blanket bans. They may sometimes be effective at protecting networks, but they are rarely good for the business.
by titanadmin | Mar 27, 2014 | Spam Advice, Spam News |
The World Cup will take place later this year, and Brazil is now completing the final preparations as the host of this year’s tournament. The World Cup generates huge global interest from football fans as well as those that would not normally watch a soccer game. Criminals take advantage of this and use the hype surrounding the World Cup to launch their scams. We have already seen World Cup spam emails caugh by our spam filters, and a great many more World Cup spam emails will appear over the coming weeks.
There will be many promotional campaigns launched by companies of all sizes. The major global brands invest heavily in World Cup promotions and sponsorship deals, taking advantage of the huge audiences the games attract. It is a great opportunity to get a brand noticed and a great time for scammers to go unnoticed.
It can sometimes be difficult to distinguish scams from real promotional campaigns, although a good gauge is “if it sounds like it is too good to be true, it probably is”.
Some of the scams that have been uncovered so far have been listed below. Be wary of these and other potential scams.
Malware delivery via World Cup spam emails
Email spam is not all about cheap watches and Viagra. Criminals use bulk emails to convince the unsuspecting to divulge their personal information with the aim of committing identity theft. Many websites pose as legitimate sites offering goods for sale. When a credit card is entered, the transaction appears to be processed, but the card details are used by criminals to obtains good of their own.
One of the most common scams involves the sale of cut price match tickets. FIFA sells tickets directly and via a number of authorized retailers, but tickets are in short supply. A stadium may hold 80,000 people, but tickets sell out very quickly.
Tickets are bought by touts and sell for as much as $30,000 including travel and accommodation. Many people are happy to pay this. Unfortunately, they will not get a real ticket. FIFA only releases them for sale in April. Any early purchaser will have fallen for a scam. FIFA has announced that only individuals who buy a ticket through an authorized retailer will be allowed to see the game. Investigations are underway in 130 countries after scams and black market ticket vendors have been discovered.
Perhaps more worrying are the scams that convince people to click on a link to a malicious website containing malware. If the user can be convinced to download a file or take an action online, malware will be delivered to their computer, tablet, or mobile phone.
One of the latest scams informs email recipients that they have won World Cup final tickets. All they need to do is click a link to a website where they are told they can print their tickets. Unfortunately, clicking the link to print will deliver a particularly nasty malware called VBS.Dinihou. This is a worm allows a criminal to download files to their computer without authorization. It also infects any USB drive plugged into the computer.
Brazil is home to one of the world’s largest cybercriminal groups
Russia, Ukraine, China and Vietnam are all known to be home to many cyber-criminal gangs, yet one of the world’s largest is based in Brazil, according to a recent report in The Guardian newspaper.
Many Brazilians are unhappy about the World Cup being hosted in the country due to the huge expense involved in staging such a tournament. The cost is astronomical and many believe that those costs will not be recovered, let alone any profit made. They feel the money should have been spent improving services for locals, not for tourists who will visit over a 4-week period. Cybercriminals have taken up their cause and are disrupting the sale of tickets.
Anonymous has also made announcements that it will be active during the World Cup and may attack FIFA and World Cup sponsors. Banks in Brazil were targeted by Anonymous in 2012, and cybersecurity protections in the country are poor. Many companies will be targeted and will be able to put up little resistance to the attacks.
World Cup fans are also being sent spam and phishing emails. Links to websites containing malware are being sent, along with file attachments containing viruses and malware. Any World Cup spam emails should be treated as suspicious and attachments not opened unless they can be confirmed as genuine. Fall for one of these scams and you could suffer major financial losses, and have your computer infected with a virus or malware. Worse still, the network that your computer connects to could be compromised.
Is malware really so bad? What does malware actually do?
Criminals use malware to achieve a number of aims. Not all criminals want to steal bank account and credit card data. Listed below are some of the common uses of malware.
Financial fraud
Not all criminals are after money, but a large percentage certainly are. If a hacker or cybercriminal is able to gain access to credit card number, the card can be used to make online purchases or fake cards can be created and used until the card is blocked. Bank account details can be used to make transfers. Entire accounts can be emptied before the victim even becomes aware of any losses. Malware is used to log keystrokes, which will reveal online banking credentials and other account logins and passwords.
Identity Theft
Personal information can be used to create fake IDs. With a fake ID, loans, credit cards and store cards can be obtained. With a stolen identity, criminals can run up thousands, or even tens of thousands of debts. In some cases, the losses can be even higher. One girl in the U.S. discovered she was the proud owner of a million-dollar yacht when she turned 18. On paper at least. In reality all she had was the debt. Malware allows files to be downloaded and control of devices to be obtained by hackers. Any data stored on the device, or accessible through it, can be stolen.
Botnets
Even a powerful computer cannot perform the necessary calculations to crack billions of passwords quickly. It would take years for a computer to be used to decode every possible combination of password. However, botnets on thousands of computers make the task much quicker. Botnet infections are also used to send out millions of spam emails. Email spammers do not use their own computers for this.
Data Loss
Sabotage is a common aim and it is often indiscriminate. Many viruses and malware delete or corrupt files, and even wipe entire hard drives. This may not occur immediately. Viruses lay dormant for weeks or months until a set date: Valentine’s Day is common. Kaspersky Labs, one of the AV engines used by SpamTitan, has identified a number of such viruses, including “The Wiper”, “Shamoon”, “Narilam”, “Maya”, “Groovemonitor” and “Dark Seoul”. These will delete data from computers or may wipe the entire hard drive.
How can you protect yourself from viruses, malware and scams?
- Don’t open emails from people you do not know
- Do not visit links contained in emails if you are not sure that they are genuine
- Delete emails containing attachments unless you are sure that they are legitimate
- Use an Anti-Spam solution such as SpamTitan to block spam emails and malware
- Keep AV definitions up to date
Perform software upgrades promptly and install patches as soon as they are released.
by titanadmin | Mar 23, 2014 | Spam Advice, Spam News, Spam Software, Website Filtering |
How long are computer viruses active before they are discovered? A few months? A year? In the case of the Russian Snake Virus, Uroboros, it has been stealing data for 8 years. It has been detected, but that doesn’t mean that the threat is over. The virus will be present on many systems, and will continue to steal data as it is incredibly difficult to detect.
Where did the virus come from?
It has been called the Russian Snake Virus, as many researchers believe the virus was created in Russia. Snake because some believe the Russian government had a hand in its creation. Why? Because of the sophisticated nature of the virus. A malicious program as complex as Uroboros is believed to have required state sponsorship. Foreign governments have been known to create viruses before. China was behind the APT1 virus. Links have been uncovered that tie the virus to the Chinese military. However, so far no link has been proven between the Russian government and Uroboros.
The virus was not created to steal data from individuals. The creators had other loftier aims. The International Business Times reported that the virus was created to steal government secrets and strike at telecoms systems.
The exact targets have not all been announced by the researchers who discovered the virus, but another link to Russia comes from the fact that Ukraine was attacked 14 times by Uroboros. It would appear that the Department of Defense of the United States was also attacked by the Russian Snake Virus in 2010.
The virus is currently being analyzed by UK firm BAE and German company Gdata. As for the level of sophistication, it is reportedly equivalent to Stuxnet. For anyone unaware of Stuxnet, it was developed and used by the U.S. and Israel to destroy Iranian nuclear reactors. It caused them to spin out of control until they were destroyed. Very James Bond, but in this case very real.
Uroboros is a rootkit and hides inside kernel-level processes. Because of this it has remained undetected. Anti-Virus engines do not scan there, allowing it to remain undetected for so long.
The analysis of Uroboros by BAE is secret and, while more is now known, since the virus is part of an ongoing operation few details have been released. The virus is still in operation and may be attacking or monitoring foreign government systems right now. What is known is Uroboros targets a vulnerability in Windows in addition to software running on the Windows platform. The virus has managed to continue working despite new security features being incorporated into the operating system.
How does Uroboros work?
From the information released so far it is known that Uroboros hijacks a running process. It hides inside of processes that are part of Windows so evades detection. Because of this, AV engines do not detect it. The AV software assumes it is part of Windows, and fails to flag the virus or hijacked service as being malicious. The virus is understood to inject DLLs into the running process.
It sends data at the user and kernel level. When a user fires up their browser, the virus launches a GET request and obtains instructions from the hacker’s command and control center. Since hundreds of legitimate requests are usually made, the GET request from the virus remains hidden. The use of HTTP also allows it to bypass firewalls. Uroboros is not always active either. It may be for a short period of time before going to sleep. It is told to do this by the hacker in control of the virus, and may sleep for months if required.
One question that has not been answered is how the Russian Snake Virus infects a computer. According to BAE, Uroboros is installed by a USB plugged into a computer, but it may also be installed via a phishing email. It is known to hack network processes, and monitor and intercept inbound and outbound traffic. It is capable of exfiltrating data and logs and can receive inbound commands.
A security vulnerability in Oracle Virtualbox has been exploited by the virus, allowing access to be gained to the kernel memory. It updates a variable indicating Windows was started in WinPE mode. Unsigned DLL files can then be loaded. These files do not have their owner and integrity verified. The Russian Snake Virus is capable of mounting virtual and physical drives, and different versions exist allowing it to be installed on different operating systems.
How can an attack of this nature be avoided?
Unfortunately, with malicious software such as the Russian Snake Virus it is difficult to totally protect a computer. There are steps that can be taken to reduce the likelihood of infection:
- The virus may be transmitted via phishing and spam emails: Block these using Anti-Spam software
- Issue training on anti-phishing strategies to employees
- Ban the use of all USB drives in your organization
- Keep software systems up to date with patches and, better still, upgrade Windows to the latest version
- Use diskless devices such as Chromebooks as much as possible
- Ensure packet-level inspections read HTTP traffic to look for signals that malware or viruses are communicating with command and control servers
- Data encryption can be used to protect stored data, but unfortunately not the memory
The Russian Snake virus: A risk for everyone or just foreign governments?
At present, the virus is believed to be used to attack foreign governments. Unfortunately, when details are released they can be used to create variants. Non state-sponsored hackers may not have been able to create the virus, but the techniques used to exploit computers and networks can be copied. This may already have occurred.
The next few years may see a number of different versions of the virus discovered, which may be used for many different reasons. Specific data may be targeted and stolen, or systems sabotaged. Only time will tell.
The discovery shows the lengths that some individuals and groups will go to in order to steal data, and why it is essential to implement multi-layered security systems to protect computers and computer networks, and always to use controls to prevent phishing emails from being delivered, and responded to.
by titanadmin | Feb 18, 2014 | Spam News |
The expert researchers at Kaspersky Labs have been hard at work this winter uncovering new malware threats, viruses and malicious code that threatens computers, mobile phones, servers, and corporate networks. However, what has recently been discovered is very worrying indeed. A new and highly malware named the Careto virus.
This is not a run-of-the-mill virus. It is nasty, very sophisticated, and consequently, probably the work of government-backed hackers. The Careto virus came from a previously known location, one that has produced a similar virus not so long ago. Kaspersky discovered the new virus and took rapid action to neutralize the threat.
Kaspersky Labs has already produced a detailed description of their discovery after conducting a detailed forensic analysis. That said, some techniques used to explore the nature of the virus were not particularly sophisticated and could be performed by any IT professional.
Kaspersky used “strings” – a Linux program that can be used to explore executable files – to extract text from the file. What they found was a series of instructions in Spanish, together with the name assigned to the new virus: Careto.
The name “Careto” is colloquial Spanish for “ugly face”, the corresponding name in English being “ugly mug”. It doesn’t translate as disaster, but it might as well do. This virus wreaks havoc.
Hidden inside this virus is a rootkit and a bootkit. The malware is particularly nasty and versatile, containing a Linux version, Mac OS X, and it is presumed it would also work on Android phones and the iOS system. It is very sophisticated in nature, and because of its complexity it has been suggested it is not the work of a bored, skilled teenager coding away in a bedroom. The complexity suggests that a considerable amount of time and effort has been put in to developing the virus. The Careto virus is capable of working on multiple systems at once, which Kaspersky suggests makes it the work of a team of hackers, not one individual.
Kaspersky investigated the Careto virus and started monitoring command-and-control (C&C) servers that were known to be used by hackers. This enabled the researchers to determine that the virus is proving to be effective. It has already infected over 380 computers, with those infections discovered in 31 countries around the world. The Careto virus appears to have been used to target specific organizations, and has been discovered in government organizations around the world, in particular, foreign embassies. Oil companies, gas companies, private equity firms, and research institutions have also been targeted.
The virus is primarily being spread by spear phishing campaigns. The targets have been sent links to fake versions of popular newspapers, including The Washington Post, as well as the Spanish Newspapers, El Pais, El Espectador, Publico and El Mundo.
The link contained in the phishing email has been masked, with users fooled into thinking they are actually visiting the genuine periodicals. The virus has also been discovered to have been used to infect computers via a security vulnerability in Adobe Flash (The 2012 version). Flash is used on a number of (typically older) websites to display advertising and video files.
Users may be wary of double clicking on emailed executable (.exe) files, but what about harmless picture files such as JPEGs. The executable file was found to reside in apparent JPEG files. The names, chef.jpg, waiter.jpg and dinner.jpg having been used to make them appear innocent.
What Does the Careto Virus do?
The types of individuals targeted thus far gives a clue as to what the Careto virus does. Its aim is to collect highly sensitive information, which it does by intercepting all communications channels used on the victims’ computers.
It “listens” in on Skype calls, chat sessions, and records and exfiltrates data from the infected device. Passwords are stolen, and encryption keys, bank account numbers, email addresses, phone numbers, and all manner of sensitive information obtained by hackers. This data is sent to the hackers’ command and control servers, one of which was discovered to reside on one of the IBM-owned Softlayer cloud service provider’s servers.
Unfortunately for the infected, detecting the virus is difficult. This is because it has stealth rootkit capabilities, cyber-espionage modules and other functionalities to help it avoid detection. After discovering and analyzing the virus, Kaspersky was able to track infected computers.
Fortunately, AV definitions have now been updated to spot the Careto virus, which incidentally, is blocked by SpamTitan Anti-spam software. SpanTitan is able to prevent this nasty virus from being delivered to your inbox.
by titanadmin | Feb 12, 2014 | Spam Advice, Spam News |
The Sochi Winter Olympics is a major event in the sporting calendar, and we are looking forward to witnessing the spectacle of winter sports as much as everyone. However, as with any major sporting event, the Winter Olympics has attracted the interest of cyber criminals. Major sporting events tend to see spammers and scammers take advantage of the media frenzy, and Sochi Winter Olympics spam campaigns have already been discovered.
Sochi Winter Olympics Spam Warning Issued by US-CERT
The high threat level has prompted the United States Computer Emergency Response Team (US-CERT) to issue an alert warning of online scams and phishing campaigns, in particular emails with the subject of “Winter Olympics” or “Sochi”. Spammers are aware that these emails are likely to be opened by winter sports enthusiasts.
Sochi Winter Olympics spam emails are expected to be sent in the millions, and phishing campaigns have been devised with attachments related to winter sports schedules, medal winners and alike. It doesn’t stop there. Many emails will contain links to fake websites enticing users to click for up to date Sochi news. However, those links will direct the unwary to sites that are loaded with malware. Clicking the link will result in malware being downloaded to the visitor’s computer or mobile device.
US-CERT says links to unfamiliar websites should be avoided. However, there is worse news for any individual traveling to Russia to view the winter sports spectacle in person. NBC anchor, Brian Williams, recently announced that ”visitors to Russia can expect to be hacked.”
The news report warned of a high risk of cyber-attacks on innocent sports lovers who take internet-enabled devices on their travels. He said cyber-attacks are “Not a matter of if, but when.” Based on the news report, users can all but guarantee they will have their devices hacked, simply by turning them on in Russia.
Visit Russia and you will be hacked?
An NBC reporter, Richard Engel, investigated the risk as part of the report. The NBC test involved turning on a laptop computer and mobile to show how easy it was for hackers to take advantage. Once the devices were turned on and connected to Russian networks, they were attacked in minutes. Engle said, “Before we even finished our coffee the bad actors had hit.” He said that information had been stolen and malware downloaded, and issued a stern warning saying visitors were “entering a minefield the instant they log on to the Internet.”
However, the test was not all it appeared to be. It involved the reporters visiting a fake Olympics website, such as those used by phishers. These websites contain malware and automatically download it to the visitor’s device. The risk appears not to be as high as the report made it sound. According to internet security expert, Robert Graham, the test was conducted on devices that were likely not to even have basic controls to prevent malware from being installed, such as up to date antivirus software.
In fact, internet users in the United States, UK, or any location around the world would be infected by malware by visiting such sites. If the test was conducted from the United States, it would likely produce similar results.
Graham decided to put this to the test, and set out to deliberately get his phone hacked. As it turned out, it was not quite as easy as the reporters suggested. The security features installed on his phone prevented malware from installing. He persevered and disabled the security software installed on his Android Smartphone. He also masked his IP address to make it appear that he was actually in the Russian Federation. After finally finding a virus, he was issued with a warning on his phone, which he had to ignore to finally get his device infected.
That is not to say that internet users – visiting Russia or staying at home – should not be wary. Quite the opposite. It is essential to be security aware, not take unnecessary risks, and implement controls to block Sochi Winter Olympics spam and phishing emails. Basic security controls must be installed on all internet enabled devices to prevent cyber-attacks, and it is essential to be vigilant, avoid unfamiliar links, and not open attachments unless certain of their authenticity.
Whether you visit Russia or stay at home, it would be a wise precaution to use a VPN to access sensitive websites – online banking websites for example. Installing a spam filter will also help to protect against phishing campaigns.
What is a high risk country? These days there are no low risk countries. It is the websites you visit, not the country you live in, that determines the risk of cyber attack!
by titanadmin | Oct 30, 2013 | Spam Advice, Spam News |
If you can be certain of one thing in life apart from death and taxes, it is the impossibility of winning a lottery that you have not bought a ticket for. Surprisingly, some people do fall for scams like these.
Over the past few weeks we have received reports of emails and letters being sent advising the recipients they have almost become a Euro millionaire: Their numbers have been drawn and a prize of €915,810 has been won.
The reason the emails have been sent to people who have not even bought a ticket is because these campaigns are sent randomly. The perpetrators of the campaign do not know who has bought a ticket, but a percentage of lottery ticket holders will receive the email if enough are sent.
A holder of a ticket may respond even if an email address was not provided when buying a ticket. Hope gets the better of common sense sometimes. The thrill of potentially having won over €900,000 helps in this regard.
The Spanish lottery scam nets criminals millions of Euros
A check for this sum is not issued for security reasons. The money can only be claimed by supplying bank information. The lottery company must use a bank transfer to provide the winnings. Sometimes, the lucky winner will have to cover some “administrative costs” in order to receive their prize. A charge of a few Euros is nothing compared to a €915,810 payout. Those charges are often more than just a few Euros, but the money is still paid.
This particular scam, or variants of it, are commonly sent by Nigerian criminal gangs. In the case of the postal version, a Nigerian postmark would be a giveaway. The letters are naturally all emailed from Spain. In fact, Spanish criminals have also started using this type of scam to defraud victims. The Guardia Civil recently took down a large gang of criminals who were running scams of this nature. Millions of Euros were recovered.
If you receive an email telling you that you have won a large sum of money, here are some easy ways to tell if the email is not genuine:
- You did not buy a lottery ticket
- You did not supply an email address
- You have never heard of the company you are asked to contact
- The email contains grammatical errors and spelling mistakes
- You are given a strict, and short, time limit for claiming your prize
- You are asked to supply sensitive information to verify your identity
- You need to pay an administration fee in order to claim your prize
- You are asked to click on a link contained in the email to confirm your identity
We wish you the best of luck. And if you want to win a prize, remember to buy a ticket and check the numbers personally!
by titanadmin | Sep 23, 2013 | Spam News |
Security technologies are some of the most advanced technologies, but security itself must be combined with good business and user practices to work effectively. No matter how advanced and well implemented the technology is, it is only as good as the methods used in using and managing it.
-
Acceptable use policy – what network activities are allowed and which ones are not
To protect employees, customers and suppliers all members of staff should be given a copy of the company’ s policy for acceptable use of IT resources including Internet and email. Often this forms part of the contract of employment. Having an acceptable usage policy in place helps protect the organization from exposure to malware and web threats as well as helping in disputes with employees.
-
E-mail and communications activities
To help minimize problems from e-mails and attachments, informing user behavior is key. Robust email and web security, coupled with appropriate user training and security procedures, are absolutely essential to the protection of corporate data, financial and other electronic assets. Without adequate solutions and controls, cybercriminals can exploit gaps in security defenses and cause serious damage to an organization.
For example:
- On Christmas Eve and again on December 26th, 2012, cybercriminals used malware installed on a local PC at Ascent Builders to transfer $900,000 from the company’s Bank of the West account. The theft was followed shortly after by a major distributed denial-of-service (DDoS) attack on the bank, presumably to conceal the theft of funds.
- In December 2012, cybercriminals added 11 bogus employees to the payroll of Niles Nursing, Inc. by using the company controller’s login credentials. Using ACH payments from Niles’ bank account, the criminals initially transferred $58,000 in funds to these individuals, who were to wire the funds to contacts in Russia and Ukraine. In total, approximately $170,000 was stolen from the firm.
- A study conducted for the UK Cabinet Office found that the loss of intellectual property – much of it the result of malware and other forms of cybercrime – costs British organizations upwards of £9.2 billion annually.
To help protect networks against threats such as viruses, worms, and Trojan horses, companies need to implement anti-virus protection on all company devices – specifying what anti-virus software is installed and what interval they are scheduled to run at. In addition, the anti-virus software and the virus pattern files must be kept up-to-date. Virus-infected computers must be removed from the network until they are verified as virus-free. System Admins are usually responsible for creating procedures that ensure anti-virus software is run at regular intervals and computers are verified as virus-free. Any activities with the intention to create and/or distribute malicious programs into the company (e.g. viruses, worms, Trojan horses, e-mail bombs, etc.) should be clearly stated as prohibited, in accordance with an Acceptable Use Policy. Any employee found to have violated this policy may be subject to disciplinary action, up to and including termination of employment.
To help safeguard the network from unauthorized users, current corporate policies surrounding network security often neglect the most critical and weak security component: the human element. An organization’s overall security is only as strong as its weakest link – the user. Environments with disparate sources of identity information have different approaches for organizing user entries, security practices and access control. Internal identity issues can be complicated and need clarifying in a policy format.
-
Password policy, to help employees select strong passwords and protect them
A complex security system won’t matter if a hacker or phisher gets a hold of an employee’s password. If you take a laissez-faire approach to creating and protecting passwords these type of security breaches are more likely to happen. Smart password practices require next to no budget. They don’t need to take up much time either when formalized in a company policy. Password policy is often overlooked, but it’s a very important part of keeping secure in an online world.
-
Encryption policy, to provide guidance on using encryption technology to protect network data
A common scenario occurs when a company with a security policy in place directs the use of encrypted USB storage and distributes these devices to its users. After time it becomes apparent the company is still at risk from a data breach because users continue to use unencrypted USB keys. This company had a security policy in place and they issued encrypted devices yet still there’s a data breach that they must deal with. An encryption policy will not work unless users understand their role in protecting company data. It’s important to have an encryption policy but it’s just as important to have an encryption policy that can be enforced and is easy for the end user to adhere to. The hard part in this process is that it often requires a behavior change, the secret to success is showing employees how they benefit from tighter network security. Cybercrime and phishing attacks most commonly originate with an employee clicking a link to a website hosting malware, opening a file attached to an email that contains malware, or simply just giving up corporate information when asked via a phishing email or website. Such information can then be used as the basis for a sophisticated phishing attack or may be sufficient to get the scammer what they need. There is no silver bullet, but these threats can be mitigated against by training the workforce to identify, prevent, and report such attacks in a timely manner.
by titanadmin | Jul 14, 2013 | Spam Advice, Spam Software, Website Filtering |
Phishing is not a problem that must only be dealt with by consumers. Businesses are being targeted based on the financial organizations they use, according to the latest research conducted by Kaspersky Labs. The Anti-Virus software provider has been investigating the evolution of phishing. The study looked at the attacks that had taken place between May 2012 and April 2013. The survey revealed that phishers are changing tactics, and are attempting to obtain bank account information. If business bank accounts can be obtained, so much the better. They usually contain much more money than personal accounts.
Hackers often target businesses they despise. Their intention is not always to make money but to cause harm. If bank accounts can be obtained they can be sold to cybercriminals. Accounts are plundered, and sometimes businesses go bust as a result. You may not have offended any hackers, but that doesn’t put you in the clear. Some hackers are involved in organized crime and they will not care who they target as long as money can be obtained.
If a bank is targeted and you lose funds, can you sue them?
A bank is attacked and a business loses money from its account. Can a business sue a bank for a cyberattack? Some are now trying.
EMI has filed a lawsuit against Comerica, in which it claims that the financial institution failed to implement appropriate security defenses which directly led to one EMI employee falling for a phishing campaign. An employee was tricked into revealing EMIs bank account details. As a result, over $500,000 was rapidly transferred out of EMIs accounts. Protections were not in place at the bank to stop this.
Unsurprisingly, the bank has claimed that this was the fault of EMI. It is EMIs responsibility to ensure its employees are trained, and do not fall for phishing campaigns. The bank could have done nothing to prevent that employee from falling for the phishing scam. EMI could have taken action though. It is unlikely that the lawsuit will result in the bank having to cover the losses of EMI.
Phishing prevention starts with staff training
If you want to protect your company’s bank balance, and stop phishers making transfers, the first step to take is to provide all staff members with cybersecurity training. One response to a phishing email is all it takes to see a bank account emptied. It therefore makes a great deal of sense to instruct members of staff about phishing emails. In the above case, the provision of such training may have saved $500,000.
The FBI estimates that these schemes, and other cyberattacks, net online criminals around $100 billion a year. These funds are obtained from large corporations and individuals, but small businesses are now being increasingly targeted. They lack the security software used by large corporations and their bank accounts contain more money than consumer accounts.
Unfortunately for SMEs, the same protections are needed as those used by large corporations. Unfortunately, IT budgets are not nearly as large. SMEs must therefore choose the best protections to put in place that will offer the greatest protection for the least outlay. Many do not even employ dedicated cybersecurity staff, so the products they choose must be easy to install, operate and maintain.
To protect against phishing, businesses must concentrate not on protecting their network with firewalls, but protecting end users. They are the ones who will be targeted by a phishing attack.
There are two methods that can be used in this regard (apart from staff training): The use of a spam filter to prevent phishing emails from being delivered, and a web filter to stop users visiting phishing websites.
The number of phishing attacks has increased significantly over the course of the past year. Because the tactic is proving to be so profitable, 2013 and 2014 are likely to see even more attacks take place. Any business that fails to take action to address the risk is likely to become a victim. Maybe not today, maybe not tomorrow, but soon.
by titanadmin | Mar 10, 2013 | Spam News |
Cyber criminals often take advantage of major news stories to launch new spam and phishing campaigns. Email subject lines containing news headlines are more likely to be opened by email users. A percentage of individuals who open the emails will click on the links contained in those emails or open the attachments.
One of the latest email scams uses the death of Hugo Chavez to get users to open spam and phishing emails. Unfortunately, curious individuals are likely to end up compromising their computer, and even the network to which it connects.
The latest spam campaign takes advantage of users’ curiosity with a good old conspiracy theory. In this case, the theory is that the FBI or CIA were behind the death of Venezuelan president, Hugo Chavez.
Researchers at Kaspersky Labs intercepted one of these spam emails and investigated. The email directed users to a website containing malicious software. Visiting the link would result in the user’s device being infected using the BlackHole 2.0 exploit pack. This would happen without the users’ knowledge. In this case, the malware was widely known. According to Kaspersky Labs, when the link was clicked “The payload dropped was not disclosed; however, 8/46 antivirus programs were able to detect the exploit code.”
The Aim of Many Spam Emails is to Infect Devices with Malware
Kaspersky Labs AV engine is used by SpamTitan to detect emails containing malware or malicious links. The anti-virus giant keeps its virus definitions database up to date and checks for the signatures of the latest malware and viruses to be discovered. The company has already identified a number of Hugo Chavez email scams doing the rounds, all of which have the purpose of delivering malware to unsuspecting email users.
The emails take advantage of people’s curiosity and direct users either to fake websites or genuine websites that have been hijacked and loaded with malware. Oftentimes the emails contain attachments containing malicious code. Opening those attachments will similarly result in users’ systems being compromised.
The latest emails are nothing new. Spammers and hackers often take advantage of major news events to get their malicious emails opened. Major sporting events, celebrity news, weddings, deaths, elections and natural disasters usually spawn a wave of new spam emails. Cyber criminals are devising ever more complex campaigns to fool users into installing malware or revealing their sensitive information.
Unfortunately, the problem is likely to get worse. As long as it proves profitable to send these spam email campaigns and phish for information, there will be criminals who are more than happy to commit time to developing the campaigns.
Fortunately, it is possible to lower the risk of becoming a victim of the spammers by following some simple rules and being vigilant.
Guidelines to Avoid Becoming a Victim of a Phishing Attack
- If you don’t know the sender of the email, don’t open it. Mark it as junk or delete it
- Never open an attachment sent by someone you do not know
- Never click on a link in an email unless you are sure it is genuine
- Never unsubscribe from an email newsletter or service that you have not subscribed to – Doing so will just confirm to hackers that your email address is valid. This will likely see you targeted by even more spammers
- If you receive a special offer that you are interested in, visit the website of the vendor directly to check the validity of the offer. DO NOT use the link contained in the email
- Ensure your anti-virus and anti-malware definitions are up to date
- Develop a culture of security awareness in your organization – The majority of security breaches come as a result of employees falling for a phishing campaign or responding to spam emails
- Install a robust spam filter to prevent spam from ever reaching inboxes
- Use web filtering to prevent users from visiting known malware and phishing websites
by titanadmin | Jan 22, 2013 | Spam Advice, Website Filtering |
Being forewarned is being forearmed, which is why SpamTitan has issued five network and email security predictions for 2013. Over the course of the next 12 months, mobile applications and social media networks are likely to have a major impact on businesses, especially small to medium-sized enterprises. However, both have potential to introduce new security risks. These will need to be addressed.
Last year the volume of cyberattacks increased, as did the variety of new malware identified. More sophisticated cyberattacks were conducted in 2013 than in previous years, and they have proven to be even more damaging.
Last year was difficult for IT security professionals. Unfortunately, the coming year is unlikely to be any easier. If you want to keep your network secure and your data protected, a considerable effort will be required over the next 12 months!
SpamTitan Network and Email Security Predictions for 2013
1. Social media monitoring will become essential to keep networks secure and staff productive
The popularity of social media websites is growing, and people are now spending an extraordinary amount of time connecting with people online, sending messages, reading and writing posts, uploading photographs, friending and poking. People crave interaction so this should be no surprise. With even more social media sites to choose from, and the use of the sites now ingrained, employees will want to use the sites more frequently at work. It is up to employers to harness the power of social media and prevent abuse.
Managers who have yet to tackle the issue of social media website use at work will need to take action in 2013. Whether it is implementing a ban or policies covering usage, the issue will not be able to be ignored any more. Since employees will use the sites even if a ban is implemented, we expect more companies to start adopting ways to curb usage, as well as taking action to address the network security risks the sites pose.
2. BYOD is here to stay and the trend will continue
BYOD is driven by employees, not by employers. Employees want to bring their own devices to work, and employers can reap the benefits. The problem that must be addressed is how to manage the considerable security risks. Many companies will decide the risks posed by the devices outweigh the benefits, and many will look to harness the power of web tools and cloud based applications.
We expect security polices will need to be put in place by organizations in 2013. Employees who are permitted to bring their own devices to work are likely to have more restrictions put in place on the use of those devices. Additional security measures to enforce policies will also be installed.
3. Cybercriminals will start to use social media as the main way of profiling targets
As the use of social media networks grows and consumers spend more time on the sites, cybercriminals will start to use the websites as a way of identifying and profiling their targets for spear phishing campaigns. Malware attacks via Facebook and other social media platforms are also likely to increase over the next 12 months. Criminals will also become more skilled at using social media networks to obtain the information necessary to defraud their targets.
Email spam volumes should continue to fall as criminals find it harder to profit from spamming campaigns. The past 2-3 years have seen spam volume decline and this is likely to continue in 2013. 3 years ago, the volume of spam emails stood at around 90% of all emails sent. Now the figure is around 70%. We expect the total to fall to around 60% this year.
4. Phishing attacks will primarily be conducted via social media websites
Phishing campaigns have been found to be highly effective on Facebook and Twitter. These two social media platforms were the most popular with phishers last year, and that is likely to continue in 2013. Social media campaigns can be conducted rapidly, and require little outlay. As the threat grows, we expect organizations to take action and implement defenses to reduce the risk of their employees falling for phishing schemes. They will be given little choice if they want to keep their networks protected.
5. Market consolidation to continue and businesses will increasingly consider alternative solution providers
The information security industry is likely to see even more market consolidation in 2013. Smaller companies will merge, with numerous takeovers expected. Last year, Trustwave bought out M86 Security, and Eleven GmbH was acquired by Commtouch.
However, end user businesses should find they can stay competitive if they concentrate on niche products. Specialist products will continue to be developed and fine-tuned, offering consumers more powerful security solutions for specific areas of network security.
Do you agree with our network and email security predictions for 2013? We expect, as an IT professional, you will have your own security predictions for 2013. What do you think the next 12 months have in store for IT security pro’s?