Spam Software
Spam software is a network security 101 basic protection that should be in place at every organization. Spam software filters out productivity-draining spam messages and prevents phishing emails and other email-based threats from being delivered to employees’ inboxes.
Research conducted by the intelligence software and anti-phishing training company PhishMe shows that 91% of cyberattacks start with a phishing email. Phishing emails aim to get the recipient to divulge sensitive information such as bank account information or login credentials. However, over the course of the past 12 months, cybercriminals have increasing used spam email to distribute ransomware. In Q3, 2016, PhishMe reported that 97% of phishing emails were being used to deliver ransomware or ransomware downloaders. Spam email is now the number one vector used to deliver malware and ransomware.
Spam email campaigns are also becoming more sophisticated and it is becoming much harder to distinguish spam from genuine emails. Many of the latest campaigns contain no spelling mistakes, are grammatically correct and use imagery from well-known brands with smart, professional layouts.
Cybercriminals are also using social engineering techniques to fool end users into clicking malicious links and opening infected email attachments. Without spam software to quarantine those emails, they will be delivered to inboxes and employees are likely to be fooled into taking the requested actions.
Fortunately, advanced spam solutions can now filter out more than 99% of spam emails, with SpamTitan preventing more than 99.9% of spam emails from being delivered. This category contains up to date information on spam software, new threats that are now blocked and advice for organizations on improving defenses against email threats.
by titanadmin | Mar 26, 2025 | Phishing & Email Spam, Security Awareness, Spam Software |
Phishing, and especially email phishing, is the most common attack vector used by cybercriminals and attacks continue to increase year after year. The latest data suggests that around 1.2% of all emails are malicious, which equates to around 3.4 billion malicious emails a day. Threat actors use email to distribute malware, drive traffic to malicious sites to harvest credentials and perform a wide range of scams, including business email compromise, the costliest type of cybercrime, often resulting in millions in losses.
While there are many ways that businesses can be attacked and many steps that can be taken to improve security, ensuring your defenses against email attacks are up to scratch is the best way of improving your security posture. Fortunately, TitanHQ has three easy-to-implement solutions that can greatly improve your defenses against the growing email and phishing threat, all of which are available on a free trial so you can put them to the test to see the difference they make.
Block More Threats with an Advanced Email Filtering Service
SpamTitan is an advanced spam filtering service that is quick and easy to implement, provides exceptional protection against all forms of email attacks, and does not require a degree in cybersecurity to use and maintain. The ease of use of the solution is one of the reasons the solution is popular with businesses from small mom-and-pop stores to large enterprises.
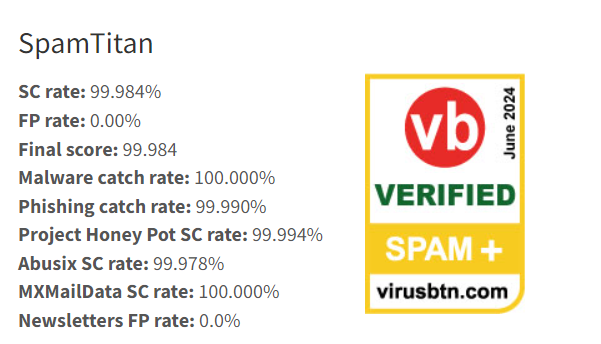
The SpamTitan cloud-based anti-spam service provides cutting-edge protection through a barrage of front-end tests, AI and machine learning-powered detection, twin antivirus engines, and email sandboxing. Suspicious files are sent to the sandbox to be safely detonated and subjected to in-depth behavioral analysis, helping to detect and block zero-day malware threats. In independent tests by VirusBulletin in Q3 2024, SpamTitan was rated in joint first place for detection, sole first place in Q4 2024 with a 100% malware catch rate, 100% phishing catch rate, and a 99.98% spam catch rate, and in February 2024, SpamTitan achieved a perfect score across the board, blocking all threats in the test.
Provide Effective Security Awareness Training to Your Workforce
Technical safeguards will block the vast majority of email threats, but it is inevitable that some threats will reach their intended targets. All it takes is for one employee to respond to a phishing email for a company to suffer a costly data breach or ransomware attack. It is vital that human defenses are strengthened by providing comprehensive security awareness training. The most effective training programs run continuously, with employees given training regularly throughout the year. Only through regular training will you be able to develop a security culture, where employees are constantly looking for potential threats and are conditioned to report suspicious emails to the security team.
The SafeTitan security awareness platform includes an extensive library of enjoyable and engaging training modules on all aspects of security, with each module lasting no longer than 10 minutes for maximum engagement. The platform makes it easy to create training programs for the workforce, tailored for different roles in the organization, and automate those programs so they run continuously throughout the year. Training should be reinforced using phishing simulations, which can be easily created and automated through the SafeTitan platform. When employees fail a phishing simulation, relevant training is generated in real-time to ensure it is delivered when it is likely to have the maximum effect on changing employee behavior.
Improve Microsoft 365 Security with PhishTitan
PhishTitan is an advanced cloud-based anti-phishing solution for Microsoft 365 powered by the same engine behind the award-winning SpamTitan anti-spam service. The solution has been developed to be integrated seamlessly with Microsoft 365 to augment Microsoft’s EOP and Defender protections and catch the threats that these solutions often miss to give true defense-in-depth security. Like SpamTitan, PhishTitan adds layers of analysis and machine learning models to provide cutting-edge protection against phishing. PhishTitan scans all internal and external emails, rewrites URLs to detect links to malicious sites, automatically blocks phishing links in emails to prevent clicks, and provides time-of-click protection by inspecting and evaluating URLs in real-time to detect changes to the destination URL after the emails have been delivered.
PhishTitan adds banners to emails from external sources, helping to combat spoofing and alerting the recipient to take extra care, and also incorporates protection against QR code phishing – quishing – which is growing in prevalence and capable of defeating many email security solutions. The platform also includes an auto-remediation feature, allowing administrators to rapidly remediate threats from users’ inboxes, including cross-tenant features for detection and response by MSPs. One of the main complaints from Microsoft 365 users is the number of phishing emails that bypass defenses; however, with the additional layers of protection provided by PhishTitan, businesses will be better protected against phishing threats.
If you want to improve your defenses against email threats, give the TitanHQ team a call or take advantage of a free trial of TitanHQ solutions to put them to the test in your own environment.
by titanadmin | Mar 4, 2025 | Phishing & Email Spam, Spam Software, Website Filtering |
There has been a surge in infostealer malware infections, with detections up almost 60% from the previous year. Infostealers gather system information, stored files, and sensitive data and exfiltrate the information to their command and control server. Once installed, they can remain undetected for long periods of time, exfiltrating sensitive data such as usernames and passwords by logging keystrokes, with some variants capable of taking screenshots and capturing audio and video by taking control of the microphone and webcam.
The majority of infostealers are used to attack Windows systems; however, a new infostealer called FrigidStealer has been identified that is being used to target Mac users. FrigidStealer is capable of stealing saved cookies, password-related files in the Safari and Chrome browsers, and login credentials, along with cryptocurrency wallet credentials, Apple Notes containing passwords, documents, spreadsheets, text files, and other sensitive data from the user’s home directory. The gathered data is added to a compressed file in a hidden folder in the user’s home directory and is exfiltrated to its command and control server.
The threat actor behind the campaign distributes FrigidStealer under the guise of important web browser updates on compromised websites. The threat actor injects malicious JavaScript into the HTML of the webpage which generates a fake browser update notification to website visitors. The notifications warn the user that they must update their browser to continue to view the page, with the displayed notification tailored to the browser in use.
The notifications look professional, include the appropriate logos for either Google Chrome or Safari, and contain an update button that the user must click to proceed. Clicking the button will trigger the download of an installer (DMG file), which must be manually launched. The user is required to enter their password to get around macOS Gatekeeper protections. If the password is entered, the file is executed and FrigidStealer is delivered.
A similar campaign is being conducted targeting Windows users. The Windows campaign uses similar techniques, although it tricks the user into downloading and executing an MSI installer, which delivers one of two different info stealers, Lumma Stealer or DeerStealer. The threat actor is also targeting Android devices in a similar way, delivering an APK file that contains the Marcher banking Trojan.
With infostealer infections soaring, businesses need to make sure they have the right security solutions in place and should be providing regular security awareness training to the workforce. Employees should be instructed to never download browser updates when prompted to do so on websites or run any suggested commands on their devices, as the updates and commands are likely to be malicious.
A web filter is strongly recommended for controlling access to the Internet and blocking visits to malicious websites. The WebTitan DNS filter can used to protect users on or off the network and is constantly updated with threat intelligence on new malicious websites. If an attempt is made to visit a known malicious website, that attempt will be blocked. The web filter can also be configured to block file downloads from the internet by file type, allowing IT teams to prevent employees from downloading executable files.
While this is a web-based campaign, information stealers are commonly distributed in phishing emails, either through malicious attachments or embedded hyperlinks. TitanHQ’s SpamTitan cloud-based anti-spam service is a powerful AI-driven email security solution with email sandboxing and advanced threat detection capabilities. SpamTitan outperformed all other tested solutions in recent tests by VirusBulletin, blocking 100% of phishing emails and 100% of malware.
by titanadmin | Feb 28, 2025 | Industry News, Phishing & Email Spam, Spam Software |
TitanHQ’s SpamTitan and PhishTitan solutions achieved perfect scores in the Virus Bulletin tests in February, blocking 100% of phishing emails, 100% of spam emails, and 100% of malware, with a 0% false positive rate. The unbeatable test scores in the latest round of tests follow impeccable scores in Q4, 2024, when the engine that powers the SpamTitan and PhishTitan solution ranked top out of all tested email security solutions with a 100% phishing and malware detection rate, and a 0.00% false positive rate. The high scores in Q4, 2024 saw TitanHQ ranked in 1st place for overall score, beating all other market-leading anti-spam software solutions including the anti-spam solutions from Mimecast, N-Able, Fortinet, Sophos, and others. In the previous quarter, TitanHQ ranked joint first. The strong performance in the tests earned TitanHQ its third consecutive VBSpam+ award.
Virus Bulletin is a highly respected security information portal and certification body that has earned an excellent reputation among the information security community by providing independent intelligence about the latest global threats. Virus Bulletin has been conducting regular benchmarking tests of security solutions for more than 20 years, with the test results giving IT security professionals invaluable information on the most effective security solutions to deploy to stop malware and phishing threats.
The latest round of tests was conducted over 16 days in February, with the SpamTitan and PhishTitan solutions blocking all threats and spam emails. The final results for Q1, 2025 are due to be announced at the end of March, with TitanHQ on track to earn its fourth consecutive VBSpam+ certification. “We’re excited to have significantly exceeded the industry benchmark in these interim results,” said Ronan Kavanagh, CEO at TitanHQ. “We’re now on track to receive a fourth consecutive VB+ award in Q1. These results highlight our relentless dedication to delivering top-tier email security, and we will continue safeguarding our clients against emerging cyber threats.”
The exceptional detection rates have prompted many managed services providers to migrate to TitanHQ from other solutions, keen to ensure their clients get the very best protection. Not only does TitanHQ deliver immediate and substantial threat mitigation, all solutions have been developed from the ground up to meet all the needs of MSPs, ensuring exceptional protection with minimal management overhead.
The SpamTitan spam filtering service includes a spam filter for incoming mail, an outbound spam filter, email sandboxing, dual antivirus engines, malicious link detection, and machine learning-based detection, ensuring exceptional protection from the full range of email threats. The next-generation email sandbox detects malware based on its behavior, allowing novel malware threats to be detected that signature-based detection misses while only causing minimal delays to message delivery. In the tests, TitanHQ was in the green for all speed tests.
If you want the very best in threat protection and exceptional value for money, why not make the switch to TitanHQ. Give the team a call today to find out more or take advantage of the free trial and see the difference TitanHQ solutions make.
by titanadmin | Feb 27, 2025 | Spam Software |
Phishing is still the leading technique used by cybercriminals, and the availability of LLMs for crafting perfect phishing emails and the abuse of legitimate services for sending emails ensures that cybercriminals get a sufficiently high success rate.
Cybercriminals’ tactics are constantly evolving and they are increasingly able to defeat traditional security measures. One recent report suggests that 70% of phishing emails successfully pass DMARC authentication checks, with more than 50% of phishing emails passing through businesses’ email security defenses.
Not only is phishing the most popular technique, attacks are increasing. To a large extent, the increase in attacks has been driven by the availability of phishing kits. Phishing kits provide cybercriminals with everything they need to perform successful phishing campaigns aside from the email addresses to target, and they can easily be purchased on cybercrime forums. The phishing kits open up phishing to a broad range of individuals, allowing them to conduct campaigns with ease, monitor performance, and automate campaigns and credential theft.
Phishing kits are offered on cybercrime forums and Telegram, with the Darcula phishing-as-a-service platform being one of the most comprehensive tools. When the phishing kit was released last year, it used around 20,000 domains that spoofed well-known brands and has since been used to conduct phishing campaigns in more than 100 countries. Now a new version of the platform is about to be released with even more features to make conducting phishing campaigns even easier.
What is particularly concerning about this platform is its ability to create DIY phishing kits to target any brand. Any user of the kit can simply provide the URL for the brand they want to target and the kit will generate all required templates for the attack, including cloning the legitimate site for the phishing landing page. The kit also includes pre-made templates for capturing passwords, credit card numbers, and for MFA entry prompts.
The latest version also includes a user-friendly dashboard, IP and bot filtering, performance measurement metrics to determine the effectiveness of phishing campaigns, automated credit card theft and digital wallet loading, and the removal of technical skills requirements, making it as easy as possible to conduct extensive phishing campaigns.
With AI tools helping to make phishing campaigns more effective and new phishing kits being developed to remove the need for any technical skills, phishing attacks are likely to continue to increase and businesses need to ensure that they have appropriate defenses in place.
The good news is TitanHQ can help. TitanHQ offers two solutions for protecting corporate email accounts from phishing and malware, the SpamTitan spam filtering service and the PhishTitan anti-phishing solution for Microsoft 365. The engine that powers both of these solutions is regularly tested for effectiveness by Virus Bulletin. In Q3, 2024, TitanHQ ranked joint first for protection, in sole 1st place in Q4, 2024, and in the latest tests in February, achieved perfect scores for phishing detection, malware detection, and spam detection, scoring 100% in all three areas with a 0.00% false positive rate.
The exceptional scores for phishing detection and malware blocking have prompted many MSPs to make the switch to TitanHQ to ensure they can give their clients the very best in protection and increasing numbers of SMBs are choosing TitanHQ as their antispam software and anti-phishing partner.
In addition to these technical solutions, TitanHQ offers a comprehensive security awareness training and phishing simulation platform to help businesses improve their human defenses by eradicating poor security practices and teaching employees how to identify phishing emails.
While it is bad news that phishing attacks continue to increase, with TitanHQ as your security partner, your business will be well protected. Give the TitanHQ team a call today to find out more or take advantage of a free trial of TitanHQ solutions and put them to the test.
by titanadmin | Feb 27, 2025 | Phishing & Email Spam, Security Awareness, Spam Software |
Cybercriminals have extensively used ransomware in their attacks on businesses, government entities, and critical infrastructure, and while these attacks often make headline news and cause massive disruption, there is a much more common malware threat – Information stealers.
Information stealers are malware that is silently installed on devices that can remain undetected for long periods of time. These types of malware have many different capabilities and can serve as downloaders for other malicious payloads, but their main function is information theft. Information theft is achieved in several ways, depending on the malware variant in question. These malware types often have keylogging capabilities and can record keystrokes as they are entered on the keyboard, allowing sensitive information such as usernames and passwords to be captured. They can often record audio from the microphone, take control of the webcam and record video, and take screenshots. They can also steal browser histories, cookies, and other sensitive information.
The information stolen from the victim allows the threat actor to conduct follow-on attacks, access accounts and steal further sensitive data, access and drain financial accounts, or commit identity theft and other types of fraud. Information stealers can also provide a threat actor with access to a device, and that access is often sold to specialized cybercriminal groups such as ransomware actors. Many hackers now act as initial access brokers, using information stealers to gain access before selling that access to other cybercriminal groups.
Information stealers such as Lumma, AgentTesla, FormBook, Redline, and StealC have been increasingly used in recent years, especially last year. Check Point observed a 58% increase in attacks from the previous year, and a report from the threat intelligence firm KELA suggested that lists of credentials obtained from information stealers are being shared on cybercrime forums. The credential lists included billions of logins that had been captured from infected devices, which, according to KELA, included around 4.3 million devices, of which around 330 million credentials had been stolen. An estimated 40% were corporate credentials.
The breach notification service, Have I Been Pwned (HIBP), has recently added 284 million compromised accounts to the service. The credentials were identified from chats on a Telegram channel called ALIEN TXTBASE, with the data obtained from information stealer logs. HIBP founder Troy Hunt said the stealer logs included 23 billion rows of data with 493 million unique website and email address pairs and around 284 million unique email addresses. Hunt said 244 million passwords were not previously known to the HIBP service, with 199 million already in its database.
The extent to which these malware variants are used, and the increase in use in 2024, clearly demonstrates the importance of advanced malware protection and the sheer number of compromised credentials suggests many businesses have been infected with information stealers. The problem for businesses is that these malware variants can be difficult to identify, as new versions are constantly being released. Traditional antivirus software is signature-based, which means it can only detect known malware. When new malware is identified, a signature of that malware is obtained and fed into antivirus software. If a malware signature is not in the software’s definition list, it will not be detected. There are several ways that these information stealers are distributed, with email being one of the most common. They can also be downloaded from the internet from malicious websites in drive-by downloads or installed along with pirated software or doctored versions of legitimate software installers.
Defending against information stealers requires a combination of measures – a defense-in-depth approach, with multiple overlapping layers of security. Given the high volume of infections stemming from email, businesses need a spam filter to block malicious emails. Antispam software will block many malicious emails; however, an antispam server must have advanced antimalware defenses. That means traditional signature-based detection and advanced behavioral detection to ensure previously unseen malware is identified and blocked.
SpamTitan uses dual anti-virus engines for detecting known threats and a next-generation email sandbox for behavioral analysis. If standard checks are passed, suspicious messages are sent to the sandbox – a safe environment where they are detonated and their behavior is analyzed. This vastly improves the detection rate, and in recent independent tests, SpamTitan outperformed all other tested email security solutions and had a 100% malware detection rate.
Security awareness training needs to be provided to the workforce to ensure that employees have the skills to recognize and avoid threats, no matter where they are encountered. Through training, employees should be conditioned to always report potential threats to their security team, and businesses can promote security best practices and eradicate risky behaviors. TitanHQ offers businesses a comprehensive training and phishing simulation platform – SafeTitan – that has been shown to be highly effective at improving employees’ security awareness.
Many malware infections occur via the Internet, and while training can reduce risk, a technical security solution is required to block threats. WebTitan is a DNS-based web filter that is used to block access to known malicious websites, assess websites in real-time for malicious content, block certain file downloads from the Internet, and restrict the sites and web pages employees can access.
With these three security solutions in your arsenal, you will be able to significantly improve your security posture and block information stealers and other threats. Give the TitanHQ team a call today to find out more or take advantage of a free trial of these solutions.
by titanadmin | Feb 16, 2025 | Security Awareness, Spam Software |
A phishing campaign has been identified that targets corporate Facebook credentials and has so far involved more than 12,000 messages to users worldwide. The campaign has primarily targeted enterprises in the European Union (45.5%), United States (45%), and Australia (9.5%) with the phishing emails sent using a legitimate Salesforce automated mailing service. When emails are sent via this service, a sender email address can be specified; however, if no address is supplied, the emails appear to have been sent directly from Salesforce from the noreply@salesforce.com email address, per the terms of service. As such, any recipient of the email may mistakenly believe that the emails are official.
The emails include fake versions of the Facebook logo, which recipients should be able to identify as fake; however, the emails are well-written, and the subject matter is sufficiently concerning to warrant a click. The emails warn the recipient about a copyright infringement claim that has been filed under the Digital Millennium Copyright Act (DMCA) against the user’s personal account, indicating material has been shared via their account that is in violation of copyright laws.
The messages include the date of the complaint, that it was reported by Universal Music Group, and is due to the unauthorized use of copyrighted music. The recipient is told they must respond to the claim by the close of business if they wish to contest the claim. The date of the required response is only 24 hours after the complaint date, therefore an immediate response is required. As is common with phishing attempts, there is a threat – permanent restrictions on the user’s Facebook account. The message includes a button to click to contest the claim, but rather than direct the user to a login page, they are directed to a fake support page, where they are provided with further information on the restrictions that have or will be applied. Several variations of that email have been identified, including warnings that Facebook surveillance systems have identified a copyright issue and, as a result, limitations have been placed on the user’s account.
Those restrictions include the disabling of personal ad accounts and audiences, blocking the management of advertising assets or people for businesses, and preventing the user from creating or running ads and managing ad accounts. In order to have those restrictions removed, the user must click the button to request a review, which directs the user to a spoofed Facebook login page. If credentials are entered, they will be captured and used to log in to the user’s account. The campaign, identified by Check Point Research, targets business users, many of whom will rely on Facebook for advertising and customer contact, therefore the consequences of an account restriction could be serious, and certainly serious enough to warrant filing an appeal. What is unclear is how the threat actor uses the compromised accounts. Potentially they could be used for further scams, which could cause considerable reputational damage to the business.
Protecting against these types of phishing campaigns requires a combination of email security and user awareness. An email security solution can prevent these messages from reaching inboxes, thus neutralizing the threat, but security awareness training should also be provided to workforce members to help them identify and avoid phishing attempts. In this case, Facebook admins for the business should be warned about the campaign and instructed to log in to Facebook directly via their web browser if they receive any copyright infringement notices purporting to have been sent by Facebook. If there is a problem with their account, it will be apparent when login into their account.
With the SafeTitan security awareness training platform from TitanHQ, it is easy to create and automate security awareness training programs and roll out new training content in relation to specific threats, only providing that training to the individuals who are likely to be targeted. Phishing simulations can easily be created to test awareness of these phishing scams, with relevant training automatically delivered in response to clicks on phishing emails.
TitanHQ’s anti-spam software, SpamTitan, provides excellent protection against phishing, as demonstrated by recent tests by VirusBulletin. The cloud-based anti-spam service outperformed all other antispam solutions in the latest round of tests, blocking 100% of phishing emails and 100% of malware, earning SpamTitan the top spot for overall score. If you are not happy with your anti-phishing defenses or feel you are paying too much for protection, give the TitanHQ team a call and ask about SpamTitan. If you have yet to provide regular security awareness training to your workforce, why not sign up for a free trial of Safetitan and put the product to the test on your workforce?
by titanadmin | Feb 3, 2025 | Phishing & Email Spam, Security Awareness, Spam Software |
Investigations of cyberattacks have identified an increasing number of incidents that started with email bombing. A high percentage of cyberattacks involve phishing, where emails are sent to employees to trick them into visiting a malicious website and disclosing their credentials, or opening a malicious file that installs malware. Email bombing is now being used to increase the effectiveness of phishing campaigns.
With email bombing, the user is sent a large number of spam emails in a short period of time, such as by adding a user to a large number of mailshots, news services, and spam lists. The threat actor creates a genuine spam issue then impersonates a member of the IT department and claims they can fix the problem, with content often made via a Microsoft Teams message. If the user accepts, they are tricked into installing remote access software and granting the threat actor remote access to their device. The threat actor will establish persistent access to the user’s device during the remote access session. What starts with an email bombing attack often ends with a ransomware attack.
There are several measures that you should consider implementing to prevent these attacks. If you use Microsoft Teams, consider restricting calls and messages from external organizations, unless there is a legitimate need to accept such requests. If so, ensure permission is only given to trusted individuals such as business partners. The use of remote access tools should be restricted to authorized personnel only, and steps should be taken to prevent the installation of these tools, including using a web filter to block downloads of these tools (and other executables) from the Internet.
An spam filter should be implemented to block spam and unwanted messages. Advanced spam filters such as SpamTitan use AI-guided detection and machine learning to block spam, phishing, and other malicious emails, along with email sandboxing to identify novel threats and zero-day malware. In the Q4, 2024, tests at VirusBulletin, the SpamTitan spam filtering service blocked 99.999% of spam emails, 100% of phishing emails, and 100% of malware with a 0.000% false positive rate, earning SpamTitan top position out of all anti-spam software under test.
Businesses should not underestimate the importance of security awareness training and phishing simulations. Regular security awareness training should be provided to all members of the workforce to raise awareness of the tactics used by cybercriminals. A cyberattack is much more likely to occur as a result of a phishing or social engineering attempt than the exploitation of a software vulnerability. Businesses that use the SafeTitan security awareness training platform and phishing simulator have reduced susceptibility to email attacks by up to 80%. For more information on TitanHQ cybersecurity solutions, including award-winning anti-spam solutions for managed service providers, give the TitanHQ team a call or take advantage of a free trial of any of TitanHQ’s cybersecurity solutions.
by titanadmin | Jan 28, 2025 | Phishing & Email Spam, Security Awareness, Spam Software, Website Filtering |
A new malware variant called PLAYFULGHOST has been discovered that is being distributed via phishing emails and websites that appear high in search engine listings through black hat search engine optimation (SEO) tactics.
PLAYFULGHOST was analyzed by Google’s Mandiant Managed Defense team, which confirmed the malware had extensive information-stealing capabilities. They include keylogging, taking screenshots, recording audio, copying information from the clipboard, stealing QQ account information, and collecting information on the installed security solutions and system metadata. The malware can also block mouse and keyboard inputs, clear Windows event logs, delete caches and profiles from web browsers, erase profiles and delete local storage for messaging apps, and the malware has file transfer capabilities and can download additional payloads. The malware achieves persistence in four ways –registry keys, scheduled tasks, establishing itself in a Windows service, and through entries in the Windows Startup folder. In short, PLAYFULGHOST is a highly capable and very dangerous new malware variant.
An analysis of the distribution methods identified SEO poisoning, where websites are promoted so they appear high in the search engine listings for search terms related to Virtual Private Network solutions, including the legitimate LetsVPN solution. If a user visits the webpage, they can download the LetsVPN installer; however, it has been trojanized to silently load PLAYFULGHOST in the memory via an interim payload. Phishing is also used to distribute the malware. While multiple lures could be used in this campaign, intercepted emails had code-of-conduct-related lures to trick the recipient into opening a malicious RAR archive that includes a Windows executable file that downloads and executes the malware from a remote server.
If infected with the malware, detection can be problematic since the malware runs in the memory, and multiple persistence mechanisms can make malware removal challenging. It is vital that infection is prevented and that requires multiple measures since the malware is distributed in different ways. To protect against malware delivery via SEO poisoning and malvertising, businesses should use a web filter and provide regular security awareness training to the workforce. The WebTitan DNS filter is a web filtering solution that protects against web-delivered malware in a variety of ways. WebTitan is fed extensive up-to-the-minute threat intelligence on malicious websites and domains and will prevent users (on and off the network) from visiting those malicious websites. That includes visits to websites through web browsing and redirects through malvertising.
WebTitan can be configured to block certain downloads from the Internet by file extension, such as installers and other executable files. In addition to preventing malware delivery, this feature can be used to control shadow IT – software installations that have not been authorized by the IT department. WebTitan can also be used to control the web content that employees can access, by blocking access to web content that serves no work purpose along with risky categories of websites.
Security awareness training is vital for making employees aware of the risks of malware downloads from the Internet. Employees should be instructed not to download software from unofficial websites, warned of the risks of malvertising, and told not to trust a website simply because it is positioned high in the search engine listings. Employees should also be warned of the risk of phishing, be taught how to identify a phishing attempt, and be conditioned to report suspicious emails to their security team. A phishing simulator should also be used to reinforce training and identify individuals who are susceptible to phishing so they can be provided with additional training. TitanHQ’s SafeTitan security awareness training and phishing simulation platform makes this as easy as possible, automating the delivery of training and phishing simulation exercises.
TitanHQ offers two powerful anti-phishing solutions – PhishTitan for Microsoft 365 users and SpamTitan anti-spam software. Both are powered by the same advanced engine that was recently assessed by VirusBulletin, and confirmed to block 100% of malware, 100% of phishing emails, and 99.999% of spam emails in Q4 tests. The incredibly strong performance earned TitanHQ top spot out of all the leading solutions under test. The strong anti-malware performance was due to twin (signature-based) antivirus engines and cutting-edge behavioral protection with email sandboxing.
With new, stealthy malware variants constantly being released, and cybercriminals developing highly sophisticated AI-based phishing campaigns, businesses need to ensure they have cybersecurity solutions capable of identifying and blocking the threats. With TitanHQ as your cybersecurity partner, you will be well protected against ever-evolving cyber threats. Give the TitanHQ team a call today for further information on bolstering your malware and phishing defenses or put these solutions to the test in a free trial.
by titanadmin | Jan 26, 2025 | Internet Security, Phishing & Email Spam, Spam Software |
Cybercriminals are increasingly conducting a type of social engineering technique dubbed ClickFix to gain persistent access to victims’ networks. ClickFix attacks involve social engineering to trick the victim into installing malware. ClickFix attacks were first identified in early 2024, and the use of this tactic has been increasing. These attacks take advantage of users’ desire to quickly resolve IT issues without having to inform their IT department. Resolving issues can take time, and usually involves raising a support ticket with the IT department. In ClickFix attacks, the threat actor warns the user about a fake IT issue, often providing some evidence of that issue, and offers a quick and easy solution.
The aim of these attacks is to trick the user into running a PowerShell command, which will ultimately deliver malware to their device. Campaigns have been conducted by threat actors distributing the Lumma information stealer, the Danabot banking trojan/information stealer, the AsyncRAT remote action trojan, and the DarkGate loader, although any number of malware variants could be delivered using this technique. Multiple threat groups have been observed using this technique.
The methods used to get the user to run the malicious PowerShell command are varied, with the deception occurring via email, the Internet, or a combination of the two. Threat actors have been observed conducting phishing ClickFix attacks involving emails with HTML attachments disguised as Microsoft Word documents. The attachments display a fake error message, the resolution of which requires copying and executing a malicious PowerShell command.
Malicious links have been distributed in phishing emails that direct users to sites impersonating software solutions such as Google Meet and PDFSimpli, the Chrome web browser, social media platforms such as Facebook, and transport and logistics companies. Threat actors also use stolen credentials to compromise websites where they create pop-ups, which appear when visitors land on the site warning them about a fictitious security issue. Fake CAPTCHA prompts are often used, where the user is told they must verify that they are human before being allowed to proceed. As part of the verification process, a command is copied to the clipboard, and the user is told to press the Windows key + R, then CTRL + V, and then enter, thus executing the script and triggering a malware download. Security researchers have identified multiple threat actors using this technique, including Russian espionage actors in targeted attacks on Ukrainian companies and many different financially motivated cybercriminal groups.
To defend against Clickfix attacks, businesses need to implement multiple mitigations to prevent these attacks from succeeding, the most important of which are security awareness training, an advanced spam filter, and a web filtering solution. Regular security awareness training should be conducted to improve understanding of the phishing and social engineering techniques used by threat actors, including specific training content to teach employees how to identify and avoid clickfix attacks. TitanHQ offers a comprehensive training platform called SafeTitan that allows businesses to easily create security awareness training programs tailored to individuals and user groups, and rapidly roll out additional training material when a new threat is identified. SafeTitan also includes a phishing simulator to test employee responses to simulated clickfix attacks.
An advanced spam filter is essential for blocking malicious emails. TitanHQ’s SpamTitan suite of solutions includes a spam filter for Office 365, a gateway spam filter, and the most popular choice, a cloud based anti spam service. SpamTitan conducts an extensive array of tests to identify spam and malicious emails, including reputation checks, checks of embedded hyperlinks, email sandbox behavioral analysis, and AI/machine learning to identify the threats that bypass many email security solutions. In recent tests, SpamTitan outperformed all other tested email security solutions with a 100% malware and phishing catch rate, and a 99.999% spam catch rate.
Web filtering solutions should be used to protect against the web-based component of clickfix attacks since initial contact is not always made via email. The WebTitan DNS filter prevents access to known malicious websites, such as the attacker-controlled webpages used in clickfix attacks. WebTitan can also prevent downloads of certain file extensions from the Internet and can also be used to control the categories of websites that employees can visit.
With regular security awareness training, email security, and web security delivered through SafeTitan SpamTitan, and WebTitan, businesses will be well protected from Clickfix attacks. Call TitanHQ today to find out more or take advantage of a free trial of these solutions.
by titanadmin | Jan 25, 2025 | Phishing & Email Spam, Security Awareness, Spam Software |
A new AI chatbot has been released specifically for use by cybercriminals that has been developed to assist with malware development, phishing campaigns, and business email compromise attacks. The new chatbot is called GhostGPT, and follows the release of WormGPT, WolfGPT, and EscapeGPT which are also aimed at cybercriminals and lack the restrictions of ChatGPT and other publicly available chatbots which will not generate responses to queries related to criminality. GhostGPT is thought to connect to a jailbroken open-source large language model (LLM), ensuring queries are not subject to censorship. The tool is offered on Telegram and for a fee, the tool can be immediately used.
There is growing evidence that cybercriminals are using AI tools for malware development, phishing/spear phishing, and business email compromise and there is considerable interest in these tools in the cybercriminal community. These tools can open up new types of attacks to low-skilled cybercriminals, as well as help skilled cybercriminals conduct attacks at an accelerated rate and bypass security solutions. These tools can be used to write malware code with extensive capabilities, dramatically reducing the time required for malware development. Phishing emails can be crafted in multiple languages with perfect grammar and spelling. AI tools are being used to slash the time taken to research individuals for spear phishing and BEC attacks and can even generate emails likely to be of interest to recipients. A recent study demonstrated that humans are not good at identifying AI-generated phishing emails. The researchers found their AI-generated emails had a 54% click rate.
These tools allow rapid development of malware from scratch and cybercriminals can easily spin up multiple malware versions capable of defeating signature-based detection. Phishing and BEC emails can easily fool targeted individuals as they lack the common signs of malicious emails that employees are taught to look for and the level of personalization of emails can be increased with little effort, making it easy for cybercriminals to scale up their spear phishing and BEC campaigns.
Malicious use of LLMs is a genuine cause for concern. Businesses need to respond to these fast-evolving threats by improving their cybersecurity defenses. Since these attacks are predominantly conducted via email, robust email defenses are a must. To defeat AI-generated phishing emails, businesses need to ensure they incorporate AI in their defenses and email security solutions need more than signature-based detection to identify and block malware.
SpamTitan, TitanHQ’s spam filtering service, incorporates AI and machine learning algorithms to identify the malicious AI-generated emails that many spam filtering solutions fail to block. SpamTitan also includes a next-generation email sandbox, where emails are sent for extensive analysis to identify threats from their behavior rather than their signature. In the Q4, 2024, tests by VirusBulletin, the engine that powers SpamTitan and TitanHQ’s Microsoft 365 anti-phishing solution – PhishTitan – ranked first for overall score, outperforming all other leading email filtering solutions under test. TitanHQ achieved a 100% malware catch rate, 100% phishing catch rate, and 99.999% spam catch rate, with a 0.000% false positive rate.
The high percentage of individuals fooled by ai-generated phishing emails highlights the importance of conducting regular security awareness training. Employees must be kept aware of the latest threats and tactics used by cybercriminals, and training should be reinforced with phishing simulations. Phishing simulations have been proven to make training more effective and highlight the individuals who are failing to apply their training to the emails they receive on a daily basis. The SafeTitan security awareness training platform and phishing simulator make it easy to spin up training courses, keep employees up to date on the current threat landscape, and automate phishing simulations.
Speak with the TitanHQ team today to discuss your options for improving your defenses against phishing and malware. TItanHS’s solutions are available on a free trial and product demonstrations can be arranged on request.
by titanadmin | Dec 31, 2024 | Phishing & Email Spam, Spam Software |
Various analyses indicate there has been a significant increase in phishing attacks in 2024, with one study revealing that 94% of organizations experienced at least one phishing attack in 2024, two percentage points higher than the previous year. The majority of those organizations suffered bad consequences as a result of those attacks.
Phishing attacks are not only increasing in volume, they are also increasing in sophistication and AI tools are making phishing attempts much harder to identify. AI tools are being used to slash the amount of time taken to conduct research for spear phishing attacks, including using these tools to create lures that the targeted individuals are likely to respond to. AI tools are being used to create grammatically perfect emails, even matching the writing style of the impersonated company or individual. There has also been an increase in multi-channel attacks, where phishers combine email, text messages, and the telephone in their scams.
In the United States, the Federal Bureau of Investigation’s Internet Crime Complaint Center publishes annual reports about complaints about cybercrime, with this year’s report showing almost 300,000 reports of phishing-related cybercrime, not including cyberattacks such as ransomware attacks that started with phishing emails. Across the Atlantic, in the UK it was a similar story, with the Information Commissioner’s Office also reporting and increase in complaints related to phishing.
With the increase in attacks, use of AI tools, and rising data breach costs, it is no surprise that phishing is one of the biggest causes of stress for cybersecurity professionals. With the New Year rapidly approaching, now is the perfect time to ease the stress by enhancing your defenses and strengthening your email security posture, and one of the best ways to do that is with an improved email security solution capable of identifying and blocking even sophisticated threats.
At TitanHQ, we are continuously making improvements to the engine at the heart of our antispam software (SpamTitan) and anti-phishing solution (PhishTitan) to improve detection and usability. The latest release is the most powerful yet with AI and machine learning capabilities and email sandboxing for exceptional malware detection. The engine has been shown to be highly effective in independent tests by the highly respected independent computer security company VirusBulletin.
VirusBulletin put the engine that powers the SpamTitan and PhishTitan solutions to the test along with 10 leading email security solutions and awarded it joint first place for overall score in the Q3, 2024 tests, and first place in the Q4,2024 tests. For the third consecutive quarter, TitanHQ achieved a 100% malware catch rate, and the phishing catch rate increased from 99.99% in Q2 to 100% in Q4, with a Q4 spam catch rate of 99.99% and a 0.00% false positive rate. The strong performance has earned TitanHQ its third consecutive VBSpam+ award. SpamTitan and PhishTitan are very competitively priced and it is easy to switch from alternative email security solutions. Given the amazing catch rates, ease of use, and competitive pricing, it should come as no surprise that record numbers of companies are making the switch to TitanHQ to improve their phishing defenses.
Technical defenses are important for blocking threats, but it is also important that your workforce is trained to recognize phishing and other security threats. The workforce needs to be provided with regular training sessions to reinforce security best practices and make them aware of the threats they are likely to encounter. Through regular training, you can develop a security culture and ensure that employees will be able to detect, avoid, and report any threats landing in their inboxes.
The easiest way to improve security awareness is with a comprehensive training platform such as SafeTitan. SafeTitan is an easy-to-use training platform with hundreds of training modules covering all aspects of security that is used by businesses to teach security best practices and raise awareness of common and not-so-common threats. Training courses can easily be created for different users, job roles, and threat levels, and the training can be automated to provide hands-off training continuously throughout the year. The platform can be configured to automate the delivery of relevant training in response to security errors, and the phishing simulator can be used to conduct internal campaigns to reinforce training and identify areas where training needs to be improved.
Why not get 2025 off to the perfect start by improving your phishing defenses with TitanHQ? Give the team a call today to discuss these solutions in more detail and take advantage of a free trial of these solutions to see for yourself the difference they make to your phishing defenses.
by titanadmin | Dec 29, 2024 | Phishing & Email Spam, Spam Software |
Detections of the Remcos remote access trojan (RAT) have increased recently with threat actors adopting new tactics to deliver this popular commercially available malware. The Remcos RAT is offered under the malware-as-a-service model, where purchasers can use the malware to remotely control infected devices and steal sensitive data.
The Remcos RAT is primarily delivered via phishing emails with malicious attachments, with each of the two main variants delivered using distinct methods. One of the variants is distributed in phishing emails using Microsoft Office open XML attachments that exploit a Microsoft Office memory corruption remote code execution vulnerability (CVE-2027-11882) to execute an embedded script that downloads an intermediate payload that will in turn deliver the Remcos RAT. The vulnerability does not affect newer Office versions, such as Microsoft 365, only older versions prior to Office 2016.
Lures commonly used include fake purchase orders, where the email claims to include purchasing specifications in the attached Excel file. If opened, the spreadsheet is blurred and the user is told the document is protected, and to enable editing to view the file. In the background, the vulnerability is exploited to deliver and execute an HTA file, triggering the processes that lead to the installation of the Remcos RAT. When delivered, the Remocos RAT is injected into a legitimate Windows executable (RegAsm.exe).
The second variant uses a VBS attachment with an obfuscated PowerShell script to download files from a remote server and inject code into RegAsm.exe. Since the final payload is injected into legitimate Windows processes, the malware is often not detected by security solutions. Once installed, persistence is maintained via registry modifications to ensure the malware remains active after a reboot. Lures used to deliver this variant include payment confirmations, with details included in the attached DOCX file.
The highest number of infections have occurred in the United States and India, and there has been a sharp rise in infections in recent months showing that the campaigns are proving effective. A combination of technical measures and security awareness training will help to prevent Remcos RAT infections. Phishing campaigns such as this show why it is important to stay on top of patching and ensure that all systems are kept up to date, and to migrate from software that has reached end-of-life to supported software versions. Endpoint security software is important; however, detection of the Remcos RAT can be difficult since files are not written to the hard drive.
The primary defense is an advanced email security solution. SpamTitan, TitanHQ’s spam filtering service, is an ideal choice as it includes reputation checks, SPF, DKIM, & DMARC, machine-learning algorithms to identify anomalies in emails, and email sandboxing, where attachments are sent for extensive analysis including pattern filtering. In recent tests by VirusBulletin, the engine that powers SpamTitan scored highest out of all 11 tested email security solutions, with a 100% malware and phishing catch rate.
It is important to keep the workforce up to date on the latest security threats and to teach and reinforce security best practices. The SafeTitan security awareness training platform makes this easy for businesses and MSPs, allowing effective security awareness training programs to be created that are tailored to individuals and user roles. The training can be automated to be delivered regularly to employees, as can phishing simulations using the SafeTitan phishing simulator to test the effectiveness of training. Businesses with Microsoft 365 would benefit from the PhishTitan platform. Based on the same engine that powers SpamTitan, PhishTitan helps to protect Microsoft 365 environments from the advanced threats that Microsoft fails to block, add banners to emails from external sources and helps security teams rapidly mitigate phishing threats.
by titanadmin | Dec 23, 2024 | Industry News, Spam Software |
TitanHQ’s email security solutions achieved first place in Q4 performance tests by the leading security information portal, testing, and certification body, VirusBulletin. The security engine that powers TitanHQ’s SpamTitan email security and PhishTitan anti-phishing platform for Microsoft 365 was put to the test alongside 10 other market-leading email security solutions and achieved the highest overall score out of all 11 solutions, building on the joint 1st overall score in the Q3, 2024 round of tests, 2nd position in the Q3 tests, and 3rd position in the Q1, 2024 tests.
The top position was achieved with a 100% phishing catch rate, a 100% malware catch rate, and a 0.00% false positive rate. This was the third consecutive quarter that TitanHQ’s solutions had a perfect score for catching malware and the third consecutive quarter that TitanHQ has been awarded the VBSpam+ award for outstanding performance. “We are thrilled to have significantly outperformed our main competitors and surpassed the industry average,” said TitanHQ CEO, Ronan Kavanagh. “Our unwavering commitment to providing unmatched email security is evident in these results, and we remain dedicated to protecting our clients from evolving cyber threats.”
Over the past two decades, VirusBulletin has tested, reviewed, and benchmarked enterprise-level security solutions to determine how effective the solutions are at blocking real-world threats. VirusBulletin has a formidable reputation for providing businesses with invaluable independent intelligence about the rapidly evolving threat landscape, and businesses look to performance tests when selecting security solutions to make sure they perform as well as the vendors’ claim. For the Q4, 2024 tests of enterprise-level anti-spam software, TitanHQ’s cloud-based anti-spam service was put to the test alongside solutions from Bitdefender, Fortinet, Mimecast, N-able, Sophos, Rspamd, SEPPmail, Net at Work, and Zoho. The tests ran for 16 days in November 2024 and included evaluations of almost 107,000 emails, of which 105,228 were spam and 1,315 were legitimate emails. 1,045 of the emails contained a malicious attachment and 16,825 contained a link to a web page hosting phishing content or malware.
Virus Bulletin Q4, 2024 Test Scores
| Metric |
TitanHQ Score |
| Malware catch rate |
100.000% |
| Phishing catch rate |
100.000% |
| Spam Catch (SC) rate |
99.999% |
| Project Honey Pot SC rate |
99.998% |
| MXMailData SC rate |
100.000% |
| Abusix SC rate |
99.999% |
| False Positive (FP) Rate |
0.000% |
| Newsletters FP rate |
0.0% |
| Final Score |
99.999% |
“With only two spam samples missed – one of which was from the unwanted category – no false positives of any kind, and a final score value of 99.999, SpamTitan showed the best performance in this test, ranking top for final score,” explained VirusBulletin. “Needless to say, a well-deserved VBSpam+ certification is awarded.”
Virus Bulletin 2024 Test Scores
| Test Period |
Phishing catch Rate |
Malware Catch Rate |
Spam Catch Rate |
Position |
| Q1 |
99.91% |
99.95% |
99.98% |
3rd |
| Q2 |
99.99% |
100% |
99.98% |
2nd |
| Q3 |
99.98% |
100% |
99.98% |
1st (Joint) |
| Q4 |
100% |
100% |
99.99% |
1st |
The test results confirm that TitanHQ is a leading enterprise spam filter provider; however. TitanHQ’s spam filtering service and anti-phishing solution for M365 are suitable for use by businesses of all sizes. While incredibly powerful and feature-rich, they are easy to implement and use. The solutions have also been developed from the ground up to meet the needs of MSPs to help them better protect their clients from rapidly evolving threats. “We’ve seen a remarkable influx of new MSP customers migrating from other solutions, consistently highlighting TitanHQ’s ability to deliver immediate and substantial threat mitigation,” said Kavanagh.
If you want industry-leading email protection from spam, phishing, and malware, give the TitanHQ team a call today to find out more about getting started with SpamTitan and PhishTitan. Product demonstrations can be arranged on request and all TitanHQ solutions are available on a free trial.
by titanadmin | Dec 18, 2024 | Industry News, Spam Software |
TitanHQ has announced that the latest version of SpamTitan (Skellig 9.07) has been launched, offering significant enhancements to improve detection, usability, and overall security. The new version of SpamTitan Skellig builds on previous versions that have been demonstrated to provide exceptional protection against malware, phishing, and spam, as evidenced by recent independent tests by VirusBulletin.
In Q3, 2024, SpamTitan achieved joint first place for overall score in the phishing, spam, and malware detection tests, and in Q4, 2024, performed even better beating all other industry-leading competitors to achieve the top spot with an overall score of 99.999%, including a malware and phishing catch rate of 100%, a spam catch rate of 99.999%, and a false positive rate of 0.000%, earning SpamTitan its third consecutive VPSpam+ award.
The latest release of the SpamTitan Skellig engine includes numerous security updates, including significant improvements with enhanced Domain and Display Name anti-spoofing protection and updated anti-spoofing screens. The settings for Domain and Display Name anti-spoofing have been separated to make it easier to see which features have been enabled and the update makes MSP’s lives easier as these split options are available at the customer level, so there is no need to drill down to each domain-level setting. The update will reduce the time that needs to be spent managing security defenses. Further, the update provides greater flexibility and control for inbox protection, since Display Name anti-spoofing is independent of user policies. That means it is possible to upload a custom list of Display Name/email pairs for more targeted protection. To improve usability, changes have also been made under the cover for Quarantine Reports to ensure they are delivered more reliably and on-time
TitanHQ is committed to making continuous security improvements to improve detection and simplify security management to make its products easier and less time-consuming to use, ensuring users have complete control of how protections are applied. The new version will be updated automatically for current users, and if you are yet to try our spam filtering service, give the TitanHQ team today for help getting you started with a free trial.
by titanadmin | Nov 26, 2024 | Phishing & Email Spam, Spam Software |
It is all too easy to place too much reliance on multifactor authentication (MFA) to protect against phishing attacks. In theory, if an employee is duped by a phishing email and their credentials are stolen, MFA should stop the threat actor from using those credentials to access the account, as they will not have the necessary additional authentication factor(s). The reality is somewhat different. While MFA can – and does – block many attacks where credentials have been obtained, it is far from infallible. MFA has made it much harder to compromise accounts but, in response, threat actors have developed new tactics to bypass MFA protections.
For example, there is a scam where an employee is contacted by an individual who claims to be from their IT department. The scammer tells them there is an issue with their account and they need to update their password. They are directed to a site where they are prompted to enter their password and enter the MFA code sent to their phone. The threat actor uses that information in real-time to access their account. Multiple campaigns have targeted IT helpdesk staff, with the threat actor impersonating an employee. They provide information to verify their identity (obtained in an earlier phase of the campaign) and ask to register a new device to receive their MFA codes.
Phishing-as-a-service toolkits (PhaaS) capable of defeating MFA are advertised on hacking forums and Telegram channels that can be purchased or rented. They involve an adversary-in-the-middle (AitM) attack and use a reverse proxy between the victim and the legitimate portal for the credentials being sought. The user is directed to a login page that appears exactly as expected, as the user is logging into the genuine site. What is unknown to the user is the attacker sits between them and the site and captures credentials and the session cookie after MFA is successfully navigated. The attacker then has access to the account for the duration of the session cookie and can register a new device to receive future codes.
PhaaS kits are a serious threat and are proving popular with cybercriminals. Take the Rockstar 2FA kit for example, which is advertised for $200 for a 2-week subscription. The kit includes everything a phisher needs, including MFA bypass, login pages for targeting specific credentials, session cookie harvesting, undetectable malicious (FUD) links and link redirectors, a host of phishing templates, and an easy-to-use admin panel that allows tracking of phishing campaigns. The phishing URLs available are also hosted on legitimate services such as Google Docs Viewer, Microsoft OneDrive, and LiveAgent – sites commonly trusted by email security solutions. This is just one phishing kit. There are many being offered with similar capabilities.
The take-home message is that MFA, while important, can be bypassed. For maximum protection, phishing-resistant multifactor authentication should be used – e.g. smartcards or FIDO security keys. These MFA tools can be expensive to implement, so at the very least ensure that you have some form of MFA implemented and implement several other layers of defenses. An advanced spam filtering service such as SpamTitan is essential, as it can block phishing emails to ensure they do not reach end users. Review sites often rate SpamTitan as one of the best spam filters for business due to how easy the solution is to use and its excellent detection rate. In November 2024, in tests by Virus Bulletin, SpamTitan blocked 100% of malware and 100% of phishing emails out of a test involving around 125,000 messages. Previous assessments had a catch rate of more than 99.99%, demonstrating the reliability and accuracy of the solution.
Another layer of protection can be provided by a web filter, which will block attempts to visit known malicious websites, such as those used for phishing and malware distribution. WebTitan provides time-of-click protection, as does TitanHQ’s PhishTitan product – an anti-phishing solution specifically developed to protect M365 accounts against phishing by augmenting Microsoft’s controls to catch the phishing emails that EOP and Defender miss.
Technical defenses are important, but so too is workforce training. Through regular security awareness training and phishing simulations, employees can be taught cybersecurity best practices and how to identify and avoid scam emails. If you want to improve your defenses against phishing and malware, give the TitanHQ team a call and have a chat about your options. All TitanHQ solutions are easy to use, are available on a free trial, and full product support is provided during that trial.
by titanadmin | Sep 28, 2024 | Phishing & Email Spam, Security Awareness, Spam Software |
New SEO poisoning, phishing, and deepfake techniques have been identified in campaigns for malware delivery, credential theft, and financial fraud this month. It is important to ensure you have appropriate defenses in place and you update your training programs to raise awareness of these new tactics.
SEO Poisoning Used to Deliver Wikiloader Malware Masquerading as the GlobalProtect VPN
Early in September, Palo Alto Networks reported that its virtual private network, GlobalProtect, was being spoofed in a campaign to deliver Wikiloader (WailingCrab) malware – A malware variant used for delivering other malware payloads onto infected devices. The threat actors behind Wikiloader campaigns sell access to other cybercriminals. An infection with Wikiloader could lead to all manner of other infections.
This campaign was focused on the higher education and transportation sectors and like many malware distribution schemes used search engine (SEO) poisoning to get malicious websites to appear high in the search engine listings for key search terms targeting those sectors. The campaign claimed to offer a download of GlobalProtect and used a combination of cloned webpages and cloud-based git repositories and delivered a file – named GlobalProtect64.exe – offering the VPN. The file delivered was a trojanized version of a share trading application, that sideloaded a malicious DLL that allowed the execution of shellcode that delivered Wikiloader from a remote server. On execution, the user was told that GlobalProtect could not be installed due to missing libraries.
This was a marked change from other campaigns that have distributed Wikiloader, which has previously been delivered via phishing emails. This is the first time that GlobalProtect has been spoofed to deliver Wikiloader. The change in tactics is believed to be due to a different initial access broker starting using Wikiloader.
Threat Actors Increasingly Using Archive Files for Email Malware Distribution
One of the most common ways of delivering malware is via phishing emails with malicious attachments. For years, the most common method involved emailing Microsoft Office documents that contained malicious macros. If the files are opened and macros are allowed to run, a malware download will be triggered. A variety of file attachments are now used for malware delivery, including PDF files, which allow links, scripts and executable files to be incorporated into the files. To hide malicious files from email security solutions, they are often added to archive files.
According to a recent analysis by HP security researchers, 39% of malware deliveries came from archive files in Q2, 2024, up from 27% the previous quarter. The researchers noted that in addition to using the most popular and well-known archive formats such as.zip, .rar, and .7z, more obscure archive files are increasingly being used. The researchers identified around 50 different archive file formats in Q2. Threat actors are also moving away from documents and are instead favoring script languages such as VBScript and JavaScript for malware delivery, with the scripts hidden in encrypted archive files to evade email security defenses.
End users are less likely to identify obscure archive formats and script files as malicious, as security awareness training has tended to focus on malicious documents containing macros. Security awareness training programs should inform employees about the different file types that may be used for malware delivery and safeguards should be implemented to reduce the risk of malware downloads, such as advanced spam filter software and web filters for blocking malware downloads from the Internet.
Deepfakes Increasingly Used in Attacks on Businesses
Deepfakes are increasingly being used in attacks on businesses on both sides of the Atlantic, and these scams have proved to be highly effective in financial scams. According to a survey conducted by Medius, around half of UK and US businesses have been targeted with deepfake scams and around 43% have fallen victim to the scams. Deepfake scams use artificial intelligence to alter images, videos, and audio recordings, making it appear that respected or trusted individuals are requesting a certain action.
The individuals deepfaked in these scams include executives such as the CEO and CFO, as well as vendors/ suppliers. For example, a deepfake of the CEO of a company was used in a video conference call with the company’s employees. In one of these scams, an Arup employee was tricked into making 5 fraudulent transfers to Hong Kong bank accounts before the scam was detected. These scams highlight the importance of covering deepfakes in security awareness training.
TitanHQ Solutions That Can Help Protect Your Business
TitanHQ has developed a range of cybersecurity solutions for businesses and managed service providers to help defend against increasingly sophisticated cyberattacks.
- SpamTitan Email Security – An advanced AI-driven cloud-based anti-spam service with email sandboxing that has been recently shown to block 99.98% of phishing threats and 100% of malware in independent performance tests.
- PhishTitan Microsoft 365 Phishing Protection – A next-generation anti-phishing and phishing remediation solution for Microsoft 365 environments that augments native M365 defenses and blocks threats that EOP and Defender misses
- WebTitan DNS Filter – A cloud-based DNS filtering and web security solution providing AI-driven threat protection with advanced web content controls for blocking malware delivery from the Internet and access to malicious websites.
- SafeTitan Security Awareness Training – A comprehensive, affordable, and easy-to-use security awareness training and phishing simulation platform that delivers training in real-time in response to security mistakes.
For more information on these solutions, give the TitanHQ sales team a call today. All TitanHQ solutions are available on a free trial and product demonstrations can be arranged on request.
by titanadmin | Sep 24, 2024 | Security Awareness, Spam Software |
The primary defense against spam and malicious emails is anti-spam software, through which all emails must pass to be delivered to inboxes. A spam filter performs a variety of checks to ensure that the email is genuine and does not contain any threats, and if you use an advanced spam filtering service such as SpamTitan you will be well protected.
SpamTitan incorporates SPF, DKIM, and DMARC to identify and block spoofing, AI and machine learning algorithms to identify spam and malicious messages based on how they deviate from the genuine emails a business usually receives, and the solution performs checks of message headers and the message body including Bayesian analysis to identify unsolicited and malicious messages. SpamTitan also incorporates email sandboxing to identify malicious attachments based on their behavior. The Bitdefender-powered email sandbox service identifies the zero-day malware threats that antivirus controls miss. In recent independent tests, the engine that powers the SpamTitan and PhishTitan solutions scored second-highest in the tests with a phishing catch rate of 99.990%, a malware catch rate of 100%, and a false positive rate of 0.0%.
While these advanced antispam solutions can protect your business and block the majority of threats, spam filters for incoming mail will not block 100% of threats without also blocking an unacceptable number of genuine emails. That means that your corporate email filter may not catch all malicious and unwanted messages, which is why it is important not to totally rely on your enterprise spam filter for protection.
Cybercriminals are constantly developing new tactics to defeat spam filters and get their messages in inboxes where they can be opened by their intended targets. One tactic that has been increasing is callback phishing, where the emails contain no malicious links or attachments, only a phone number. The malicious actions take place over the phone, such as convincing the user to download software that provides remote access to their device. Spam filters cannot easily determine if a phone number is malicious, although the AI content detection mechanisms of SpamTitan can identify these types of threats.
Cybercriminals are increasingly leveraging legitimate third-party infrastructure for sending their spam and malicious emails, such as exploiting web forms with backend SMTP infrastructure, legitimate online services such as Google Drive, Dropbox, and SharePoint for hosting malware and phishing content, and services such as Google Forms for hosting fake quizzes for capturing sensitive information. All of these methods can be difficult to identify as they use legitimate services that are generally trusted by email security solutions. Then there are other forms of phishing that no email security solution can block, as the phishing occurs on social media pages and links are sent via instant messaging services and SMS. These “smishing” attacks bypass standard technical defenses and often reach their intended targets.
The reality is that no matter how good your technical defenses are, threats will be encountered by employees. An advanced spam filter like SpamTitan will help to reduce the number of malicious and unwanted messages that arrive in inboxes but without comprehensive security awareness training, employees may respond to the malicious messages that sneak past your spam filter, are encountered via the Internet, or are sent via SMS or instant messaging services.
This is why TitanHQ strongly recommends providing regular security awareness training to the workforce to train individuals how to recognize and avoid threats such as malware and phishing and to teach cybersecurity best practices to eradicate risky behaviors. This is also an area where TitanHQ can help. TitanHQ offers a comprehensive security awareness training platform (SafeTitan) that makes it easy for businesses to create security awareness training programs for the workforce, with those campaigns tailored for different departments and roles and the different threats that each is likely to encounter.
The training courses are modular, with each element lasting no more than 10 minutes, which makes it easy to fit training into busy workflows. Through regular training, reinforced with phishing simulations conducted through the platform, businesses will be able to improve their human defenses. If malicious messages do make it past your perimeter defenses or if employees encounter threats online or elsewhere, they will have the skills to recognize and avoid those threats.
Give the TitanHQ team a call today to discuss improving your defenses through advanced spam filtering, web filtering, and security awareness training. TitanHQ solutions are available on a free trial to allow you to put them to the test before making a purchase decision, and demonstrations can be arranged on request.
by Jennifer Marsh | Aug 28, 2024 | Spam Software |
Phishing is the name given to a type of cyberattack where the threat actor uses deception to trick an individual into taking an action that benefits the threat actor. A lure is used to get the targeted individual to respond and these attacks typically create a sense of urgency. Urgency is required as phishers need users to act quickly rather than stop and think about the request. The faster the response, the less time there is to identify the scam for what it is. There is often a threat to help create a sense of urgency, such as negative consequences if no action is taken.
Phishing can take place over the phone, SMS, and instant messaging platforms, but email is the most common way of getting the phishing lure in front of an employee. It is now common for businesses to provide security awareness training to the workforce to raise awareness of phishing threats and to have a spam email filter in place to detect and quarantine these malicious emails before they reach inboxes; however, even with robust defenses in place, some malicious emails will arrive in inboxes and employees are often tricked into responding.
Security awareness training programs teach employees to stop and think before taking any request in an email, which is the last thing phishers want the recipients of their emails to do. One of the ways they can get a quick response is to make the recipient believe that the email has been sent from an internal email account, either through spoofing or by using a compromised internal email account. Some of the lures used in phishing attempts that the majority of employees will at least open and read, are detailed below.
HR Themed Phishing Emails
One of the ways that phishers increase the chance of a user responding is to use Human Resources (HR)-themed lure, as any communication from the HR department is usually taken seriously by employees. These phishing attempts include the types of notifications that HR departments often send via email, examples of which include:
- Changes to working hours
- Updates to working practices
- Dress code changes
- Upcoming training/cybersecurity training sessions
- Annual leave notifications
- Payroll information requests
- Tax matters
- Healthcare and wellness benefit updates
- Employee rewards programs
- Notifications about disciplinary procedures
IT Department Notifications
Notifications from the IT department are also common as employees typically open these emails and act quickly. These include:
- Internet activity reports
- Security alerts
- The discovery of unauthorized software
- Changes to access rights
- Requires software installations
Notifications from Board Members
Phishers often impersonate the CEO or other executives, as they know that employees will want to respond quickly and are unlikely to question requests from these authority figures. CEOs are commonly impersonated in business email compromise attacks, where the threat actor tries to get an employee to make a wire transfer to their account, purchase gift cards, or divulge sensitive information. These emails may include a hyperlink to a website where the user is told they must enter their login credentials, a hyperlink to a website where a file download takes place, or the emails may include an attachment. Common file types used in these email campaigns include PDF files, HTML attachments, Office files, and compressed files. These files may contain malware or malicious scripts, or may be used to hide information from spam filtering software. For example, PDF files are commonly used that contain malicious links. By adding the link to the PDF file, there is less chance that spam filtering software will find and follow the link.
How to Defend Against These Common Email Threats
Defending against email attacks requires advanced anti spam software and regular security awareness training for the workforce. SpamTitan from TitanHQ is an advanced cloud-based anti-spam service that performs comprehensive checks for spam and malicious emails, including an inbound spam filter and outbound filtering with data loss prevention. SpamTitan performs reputation checks of the sender’s domain and email account, recipient verification, anti-spoofing checks, and alias recognition, and allows geoblocking to prevent the delivery of emails from certain locations (overseas, for instance).
SpamTitan also incorporates extensive content filtering mechanisms, including rewriting URLs to identify the true destination, URL checks to identify malicious content, anti-phishing measures including machine learning algorithms to detect suspicious content that deviates from the standard emails typically received, Bayesian analysis to identify spam and phishing, OLE detection, dual antivirus engines, and email sandboxing. Sandboxing is key to blocking malware threats, including previously unseen malware. With SpamTitan in place, the vast majority of threats will not arrive in inboxes. In recent independent tests, SpamTitan had a 99.99% spam detection rate, a 99.98% phishing detection rate, and a 100% malware detection rate, with zero false positives.
TitanHQ also offers a comprehensive security awareness training platform called SafeTitan. SafeTitan makes it easy for businesses to create and automate security awareness training programs for the workforce, and tailor programs for different departments and user groups. The content is fun and engaging and is delivered in modules of more than 10 minutes, which makes security awareness training easy to fit into busy workflows. SafeTitan also includes a phishing simulator for assessing the effectiveness of training and for giving employees practice at identifying phishing attempts, including the types of phishing attempts mentioned in this article that often fool employees.
SpamTitan and SafeTitan, like all TitanHQ solutions, are easy to implement, use, and maintain, and are available on a free trial. For advice on improving cybersecurity at your business and for further information on TitanHQ solutions, call the team today and take the first step toward improving your security posture.
by titanadmin | Jul 28, 2024 | Spam Software |
Phishing is one of the most common ways that cybercriminals gain initial access to networks. A single response to a phishing email can be all it takes to compromise an entire network. These attacks can be incredibly costly. According to the 2024 Cost of a Data Breach Report from IBM, the average cost of a data breach that starts with phishing has risen to $4.88 million. According to the Federal Bureau of Investigation (FBI), phishing was the leading reason for reports of cybercrime to its Internet Crime Complaint Center in 2023.
The best way to gain access to an internal network is to ask someone with access (an employee) to provide that access. That is essentially what phishing is about. Phishing involves deception to gain access, tricking employees into disclosing their credentials or installing software that provides remote access, such as malware or a remote desktop solution. Social engineering techniques are used to convince the employee to take an action that benefits the attacker. That action may be required to fix a problem, such as preventing an avoidable charge to an account, correcting a security issue before it is exploited, or recovering a missing package.
Phishing often involves the impersonation of a trusted entity, which could be the CEO, HR department, colleague, vendor, lawyer, government entity, or a trusted business. Emails may impersonate a trusted individual or company, provide a plausible reason for clicking a link in an email or opening a file attachment. When links are included in emails, they often direct the user to a website that requires them to log in. The log-in box presented will be familiar as it will be a carbon copy of the brand that is being spoofed. When the credentials are entered, they are captured and used to remotely log into that user’s account. Alternatively, they may be directed to a web page and told they must download and open a file, which unbeknown to them, contains a malicious script that silently installs malware.
Phishing targets human weaknesses so one of the best solutions for combatting phishing is end user training. Training the workforce on how to identify a phishing attempt and providing an easy way for them to report potential phishing attempts is vital. Security awareness training should cover cyber threats and how to identify and avoid them, as well as teach cybersecurity best practices and why they are important. If a threat actor can get phishing content in front of an employee, whether that is via email, SMS message, social media, an instant messaging platform, or over the phone, they will be more likely to recognize that threat for what it is and take the appropriate action. Security awareness training is about strengthening your defensive line.
Training can be provided in a one-time training session, but that is unlikely to be effective. If your child wants to drive, you would not pay for a 1-hour lesson and expect them to pass their driving test. Multiple lessons are required along with a lot of practice, and as experience builds, they will become a better driver and learn how to react to situations they have not seen before. It is the same with security awareness training. Providing training frequently will build knowledge and understanding and that knowledge can then be tested and employees given practice at recognizing phishing attempts by using a phishing simulator.
The best defense against phishing is to ensure that no phishing attempt ever reaches an end user; however, in practice that is a major challenge. The aim should be to make it as difficult as possible for attackers to reach end users by implementing technical solutions that can recognize phishing attempts and block them before they are delivered. The primary technical defense is anti-spam software.
Anti-spam software can be provided as a cloud-based anti-spam service or an anti-spam gateway for on-premises email systems, through which all inbound and outbound emails must pass. A spam filter for incoming mail is essential for blocking the majority of phishing threats, but an outbound spam filter is also important for identifying phishing attempts from compromised internal mailboxes.
An anti-spam server must be capable of identifying and blocking malware threats. Spam filters include anti-virus software that scans for known malware signatures, but that is no longer enough. Malware is constantly changing and can easily defeat signature-based detection measures, so email sandboxing is also required. Sandboxing uses pattern filtering and behavioral analysis in a safe environment to identify malware by what it attempts to do. Since phishing attempts are becoming more sophisticated, often not including any malicious content in the emails – such as callback phishing – an anti-spam solution should have AI and machine learning capabilities, to predict phishing attempts by how they deviate from the standard messages received by a business.
Technical defenses will reduce the number of threats that employees encounter, and security awareness training will prepare the workforce in case a threat is not blocked. Further technical defenses should also be considered to combat phishing. Multifactor authentication is important for preventing unauthorized access in the event of an employee disclosing their credentials. With multifactor authentication, a username and password are not enough to grant access to an account. Since multifactor authentication can be circumvented with some of the more advanced phishing kits used by cybercriminals, robust MFA is required, often referred to as phishing-resistant MFA.
No single anti-phishing measure is sufficient on its own. Layered defenses are key to mounting a good defense against phishing, and this is an area where TitanHQ can help. TitanHQ can offer cutting-edge anti-spam software (SpamTitan) that has been shown to block 100% of known malware and, through sandboxing, block novel malware threats, and has a phishing and spam detection rate of over 99.99%. To block phishing threats in Microsoft 365 environments and to help security teams with remediation, TitanHQ offers the PhishTitan solution, and security awareness training and phishing simulations can be created and automated with the SafeTitan platform.
Give the TitanHQ team a call today to find out more about these anti-phishing measures and the team will help you with improving your defenses and getting started on a free trial of these solutions.
by Jennifer Marsh | Jun 29, 2024 | Industry News, Spam Software |
For the second consecutive quarter, TitanHQ’s SpamTitan and PhishTitan solutions earned the #2 spot in the VBSpam+ awards, with a 99.99% phishing catch rate. For more than 20 years, the Virus Bulletin information security portal has been conducting fully independent benchmarking tests of cybersecurity solutions, including email security, anti-malware, and anti-phishing solutions. In the phishing and malware tests, Virus Bulletin fired a barrage of threats and spam at security solutions, but it is not sufficient to just be able to block malware, phishing, and spam. Email security solutions need to be able to block those threats without also blocking genuine emails so Virus Bulletin also sent a range of genuine emails to the email security solutions to make sure they were not overblocking and preventing genuine messages from being delivered quickly.
SpamTitan is provided as a cloud spam filter or gateway spam filter and incorporates machine learning and AI-based detection and sandboxing technology for predictive and behavioral analysis to identify zero-day threats. PhishTitan is TitanHQ’s inline phishing protection solution for Microsoft 365, which improves the Microsoft 365 spam filter. For every 80,000 emails sent to Microsoft 365 accounts, PhishTitan catches 20 threats that Microsoft’s most advanced security offering misses (E5 premium). PhishTitan auto-remediates these phishing threats. The same anti-spam, anti-malware, and anti-phishing engine powers both SpamTitan and PhishTitan.
The technological superiority of these solutions was demonstrated in the Virus Bulletin tests. In the Virus Bulletin Q1,2024 benchmarking tests, SpamTitan & PhishTitan achieved an impressive second place in the round of testing with a 99.914% phishing catch rate with a 0.000% false positive rate and a malware catch rate of 99.511%. TitanHQ achieved an overall final score of 99.983%
In the Q2, 2024 benchmarking tests, Virus Bulletin assessed 12 leading email security solutions and TitanHQ performed even better, achieving a phishing catch rate of 99.990%, a malware catch rate of 100.000%, and a false positive rate of 0.000%, resulting in a second-place spot for the second consecutive quarter with an overall final score of 99.984%. TitanHQ was pipped to the top spot by just 0.004% and outperformed email security providers such as Sophos, FortiMail, Mimecast, N-able, SpamAssassin, and Zoho Mail. The test ensures that TitanHQ collects another VBSpam+ certification for Q2, 2024. The scores clearly demonstrate that TitanHQ provides powerful and effective anti-spam and anti-phishing solutions for businesses and Managed Service Providers which are capable of blocking ever-evolving cyber threats. The benchmarking tests cement TitanHQ’s position as a leader in the cybersecurity industry.
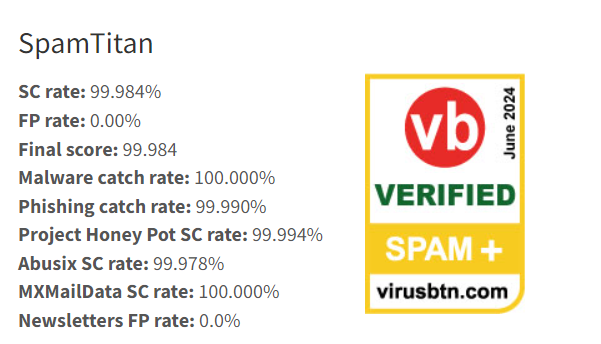
“This test reaffirms TitanHQ’s unrivaled prowess in spam and phishing protection—we stand as the first choice for combating phishing attempts and spam infiltrations,” said Ronan Kavanagh, CEO at TitanHQ. “Our customers need not settle for anything less. With TitanHQ solutions, they receive unparalleled defense against phishing and spam and experience minimal false positives.”
Ronan Kavanagh explained that the company is attracting an unprecedented number of new Managed Service Provider customers who have decided to make the switch from other solutions to TitanHQ, not only because of the impressive level of protection provided, but also the low management overhead, ease of use, and the MSP features of both SpamTitan and PhishTitan, which were developed from the ground up to meet the needs to MSPs. “Their resounding feedback echoes the sentiment: TitanHQ delivers immediate and substantial threat mitigation. These independent test results validate our ongoing efforts, ensuring our customers benefit from top-tier protection against phishing, spam, and viruses at a compelling value proposition.”
by Jennifer Marsh | Jun 24, 2024 | Spam Software |
Email security solutions are used for blocking threats before they reach end users, including phishing and spear phishing emails, malware, spam, and other unwanted emails. Email security solutions have been an essential cybersecurity measure for decades and have been helping businesses to keep inboxes free of threats and to detect and block insider threats such as the theft of sensitive company data and personally identifiable information by employees.
One area where many email security solutions fail to perform well is the detection of malware. Email security solutions traditionally use anti-virus engines for detecting malware threats and they are constantly updated with new signatures when novel malware variants are detected. While these threat intelligence feeds ensure that email security solutions can detect known malware variants, there is a delay between a malware variant being detected and the signature being uploaded to the malware definition list. That delay may be a few minutes, hours, or days and cybercriminals exploit that window of opportunity.
While these signature-based defenses were sufficient for many decades, new malware variants are constantly being released with small changes that are sufficient to defeat signature-based detection methods. Cybercriminals are automating that process and are using large language models (LLMs) to accelerate the release of new malware variants.
Signature-based detection is still essential, but another feature is now required – one that can detect novel malware variants even if they have never been seen before. That feature is email sandboxing. An email sandbox is an isolated environment, often in the cloud, where emails are sent for deep analysis. When an email passes frontline checks and scans using anti-virus engines, they are sent to the sandbox for deep inspection.
The sandbox is designed to appear to be a genuine endpoint to trick the malware that it has reached its intended destination. The malware executes and performs its initial routines, such as connecting to its command-and-control center and reporting system information. Those actions are detected, the malware is quarantined, and the security team is alerted about the attempted attack. If the checks are passed, the email is released and delivered to the intended recipient. Without this vital security feature, many malicious emails will be delivered to end users.
While there are clear benefits to email sandboxing, there is one disadvantage and that is sandboxing message delivery delays. Time must be allowed for deep analysis, especially as some malware variants delay malicious actions to defeat sandboxes. That means that there is a delay in delivering messages that have been sent to the sandbox and are found to be clean. That delay could be around 20 minutes in some cases, which is far from ideal. To reduce delays to a minimum, it is possible to whitelist certain trusted senders to ensure that their messages are never sent to the sandbox and adjust the rules of the email security solution to limit the emails that are sent to the sandbox.
SpamTitan from TitanHQ uses dual anti-virus engines for signature-based detection and a Bitdefender-powered email sandbox for detecting novel malware variants. In addition to performing reputation checks to identify untrusted senders, SpamTitan includes pattern filtering that allows security teams to specify their own terminology for blocking messages, geo-filtering to block emails from certain geographical regions where the company does not operate, and AI and machine learning algorithms for predicting new phishing threats and assessing how emails deviate from standard messages usually received by the business.
SpamTitan is a multi-award-winning email security solution that can be provided as a hosted email filter or as a gateway spam filter to be installed on existing hardware as a virtual appliance. It has been developed to be quick and easy to install and use, works seamlessly with Microsoft 365 to improve protection, and is an ideal email security solution for Managed Service Providers to provide advanced email security to customers.
If you do not have a sandbox for email with your email security solution, now is the time to consider changing to a more advanced email security solution. Give the TitanHQ team a call for more information and to help get you set up on a free trial.
by Jennifer Marsh | Apr 29, 2024 | Phishing & Email Spam, Spam Software |
Phishing typically involves impersonation of a trusted individual or brand. In email phishing, the sender’s email address is often spoofed to make it appear that the messages have been sent from a legitimate domain, the emails often include the spoofed company’s logo, the color scheme used by that company, and the messages themselves are often very similar to the official emails sent by that brand.
It stands to reason that the most commonly impersonated brands are large tech companies, as more people are familiar with those companies and use their products and services. It should not come as a surprise to hear that the most impersonated brand in Q1, 2024 was Microsoft, which was impersonated in 38% of all phishing attacks, according to data from Check Point Research, up from 30% of attacks in the previous quarter. Google was the second most impersonated brand and was impersonated in 11% of phishing attacks, up from 8% in Q4, 2023.
Phishing attacks impersonating Amazon fell from 9% in Q4, 2023 to just 3% in Q1, 2024. The fall in attacks can be explained by fewer online sales after the holiday period, with phishers favoring other brands at the start of the year. There was an increase in attacks impersonating LinkedIn to target job seekers in response to an increase in job hunting in the New Year. LinkedIn rose to third place and was impersonated in 11% of attacks. Another seasonal increase was a rise in attacks impersonating Airbnb, which made it into the top 10 most impersonated brands, likely due to the increase in holiday bookings in the New Year.
Cybercriminals often change tactics and respond to seasonal changes, such as increasing attacks impersonating delivery firms and online retailers in the run-up to the holiday season, and piggyback on the popularity of major news stories and sporting events. This year is an Olympics year, and the European Football championships will be held in Germany in June. Lures related to these events are certain to be used as interest grows over the coming weeks as the events draw closer.
What is clear from phishing data is attacks are becoming more numerous and more sophisticated. According to tracking data by the Anti-Phishing Working Group (APWG), there were more than five million phishing attempts reported in 2023, the highest total ever recorded by APWG. Attacks against social media platforms showed a marked increase as the year drew to an end and accounted for almost 43% of all phishing attacks.
QR code phishing is also increasing. QR codes are used to send traffic to malicious URLs, and they are highly effective for phishing. Email security solutions typically check embedded hyperlinks against lists of known malicious domains, with many following hyperlinks and assessing the sites that users are redirected to. Many email security solutions, however, lack the capability to read QR codes, so the messages often end up in inboxes where they can be opened by end users.
It is not only email phishing that is increasing. Vishing – voice phishing attacks continue to rise and there was a major increase in Business Email Compromise (BEC) attacks, which the APWG data shows increased by 24% compared to the previous quarter. As phishing attacks increase in number and sophistication, businesses need to ensure that their defenses are capable of blocking these threats and that their employees are trained to be on high alert and constantly look for the signs of phishing in all communications.
One of the most important protective measures for businesses is to have an effective Office 365 spam filter. The anti-spam and anti-malware protections put in place by Microsoft and included with all licenses (EOP) are effective at blocking spam and known malware, but it is not so effective at blocking zero-day phishing and malware threats, many of which land in users’ inboxes. The more advanced protection that is provided with Microsoft’s E5 premium license improves phishing detection considerably, yet even this measure does not block many sophisticated phishing attempts. As such, many businesses are keen to improve the Office 365 spam filter and look for a third-party cybersecurity solution.
An increasing number of businesses are signing up for advanced AI- and machine learning-driven protection from TitanHQ to improve protection for Microsoft 365 environments. The engine that powers two of TitanHQ’s most popular cybersecurity solutions – SpamTitan and PhishTitan- has VBSpam+ certification from Virus Bulletin and in Q1, 2024 tests, was found to have a spam catch rate of 99.983%, a phishing catch rate of 99.914%, a malware catch rate of 99.51%, and a false positive rate of 0.00%. Overall, the engine got a 99.983% overall score.
SpamTitan is a cost-effective, easy-to-use email security solution for stopping phishing attacks, spam, malware, and ransomware. The solution features AI-based phishing protection via the newest zero-day threat intelligence, double malware protection with two antivirus engines, a next-generation sandbox for analyzing the behavior of messages to identify zero-day threats, and the solution is easy to integrate with Microsoft 365 to improve protection.
PhishTitan is a cloud-based, next-generation phishing protection and remediation solution that has been developed for use with Microsoft 365 that can identify and block the advanced phishing threats that Microsoft misses. PhishTitan has a high detection accuracy and uses AI to assess the content, tone, and meaning of emails to identify unusual, suspicious, and malicious messages. The solution also adapts to constantly evolving phishing tactics.
URLs in phishing emails are rewritten to identify their true destination, are compared to an extensive range of intelligence feeds, and the solution provides time-of-click protection against malicious links in emails. The solution also learns from user feedback to further improve accuracy and applies banners to emails warning about potentially malicious content and can be used by IT teams to automate the remediation of phishing emails from inboxes.
Phishing attacks are getting more sophisticated and tactics are constantly changing, but with the advanced protection provided by SpamTitan and PhishTitan that significantly improves the Microsoft 365 spam filter, businesses will be prepared. Give the TitanHQ team a call for more information, to arrange a product demonstration, or to sign up for a free trial to put the solutions to the test.
by Jennifer Marsh | Mar 29, 2024 | Phishing & Email Spam, Spam Software |
TitanHQ has claimed a Top 3 position in a recent Virus Bulletin email security test, achieving an exceptional 99.98% spam catch rate and 99.91% phishing catch rate for the cutting-edge filtering engine that powers the SpamTitan (email security) and PhishTitan (phishing protection) solutions, earning TitanHQ the prestigious VBSpam+ certification for the products.
Virus Bulletin is a security information portal and independent testing and certification body that has earned a formidable reputation within the cybersecurity community for providing security professionals with intelligence about the latest developments in the global threat landscape. Virus Bulletin conducts regular tests of security solutions to determine how well they perform at detecting and blocking threats, and for more than 20 years has been benchmarking cybersecurity solutions. Virus Bulletin’s public certifications cover all types of security threat protection, including anti-spam and anti-phishing solutions for enterprises.
In the Q1, 2024 tests, Virus Bulletin assessed nine comprehensive email security solutions, including TitanHQ’s email security suite which comprises SpamTitan and PhishTitan. The email security solutions were put to the test to assess how effective they are at blocking unsolicited and unwanted spam emails and malicious messages of all types. TitanHQ’s solutions achieved exceptional scores at blocking spam and phishing emails, with a spam catch rate of 99.983%, a malware catch rate of 99.511%, and a phishing catch rate of 99.914% with zero false positives. The final score for the Q1, 2024 tests was 99.983, cementing TitanHQ’s position as a leading provider of anti-phishing and anti-spam solutions for managed service providers and businesses.
“This test reaffirms TitanHQ’s unrivaled prowess in spam and phishing protection—we stand as the first choice for combating phishing attempts and spam infiltrations,” said Ronan Kavanagh, CEO at TitanHQ. “Our customers need not settle for anything less. With TitanHQ solutions, they receive unparalleled defense against phishing and spam and experience minimal false positives.
While there are many ways that cybercriminals and nation state actors breach company networks and gain access to sensitive data, phishing is the leading initial access vector. Despite phishing being such a prevalent threat, many businesses lack security solutions that can consistently identify and block these malicious messages, which results in costly compromises, data breaches, and devastating ransomware attacks. According to one study by researchers at CoreView on 1.6 million Microsoft 365 users, 90% lacked essential security protections that can combat threats such as phishing.
While Microsoft has security solutions that can block spam and phishing emails, they are unable to block advanced phishing threats. PhishTitan has been developed to work seamlessly with M365 and catch the phishing threats that M365 misses. Even Microsoft’s most advanced anti-phishing protection, the costly E5 premium security offering, fails to block many advanced threats. Testing has shown that for every 80,000 emails received, PhishTitan identifies and blocks 20 unique, sophisticated phishing attempts that Microsoft’s top solution misses, and many businesses cannot afford Microsoft’s top level of protection and are reliant on its basic anti-spam and anti-phishing protection.
If you want to improve your defenses against phishing and malware and block more spam emails, give the TitanHQ team a call and ask about SpamTitan and PhishTitan. Both email filtering solutions are available on a free trial, so you can put them to the test and see for yourself the difference they make.
by Jennifer Marsh | Dec 16, 2023 | Email Archiving, Industry News, Security Awareness, Spam Software, Website Filtering |
TitanHQ products have received four “Top Solution Awards” from Expert Insights in Q4, 2023 in the Email Security, Web Filtering, Security Awareness Training, and Email Archiving categories.
Expert Insights is a leading business software review website that is used by IT decision-makers for researching the best business software solutions. The platform has more than 1 million readers a year and helps more than 85,000 businesses each month with their software purchase decisions. The website includes honest and impartial technical reviews and helpful guides to allow IT decision-makers to purchase with confidence.
Each Quarter, Expert Insights recognizes the world’s best B2B technology solutions through its awards program. The awards are based on Expert Insights’ independent technical analysts and editorial team, customer feedback, and industry recognition. In Q4, 2023, Expert Insights issued awards in over 40 categories, from authentication to zero trust security.
“We are thrilled to unveil our list of the ‘Top Solutions’ for Winter 2023, highlighting the extraordinary innovation in the B2B technology landscape,” said Craig MacAlpine, CEO and Founder of Expert Insights. “These awards celebrate leading solutions across more than 40 product categories, based on our own technical analysis and the engagement of thousands of enterprise tech professionals that use Expert Insights to research solutions each month.”
TitanHQ’s cybersecurity solutions were recognized and were named top solution in four categories:
- Email Security – SpamTitan
- Web Filtering -WebTitan
- Security Awareness Training – SafeTitan
- Email Archiving – ArcTitan
SpamTitan is a cutting-edge email security solution for blocking spam and protecting against email threats. The solution has artificial intelligence and machine learning capabilities and can block all known malware, zero-day malware threats, and phishing, spear phishing, and business email compromise attacks.
WebTitan is a leading DNS filtering solution that allows businesses to carefully control the web content that can be accessed via wired and wireless networks and allows businesses to restrict access to certain websites to improve productivity, reduce legal risk, and protect against phishing, malware, ransomware, and other online threats.
SafeTitan is a comprehensive security awareness training and phishing simulation platform for teaching employees security best practices and improving resilience against the full range of cybersecurity threats. The platform provides training in real-time in response to poor security behaviors, which are triggered immediately when those behaviors are detected to ensure that training is delivered when it is likely to have the biggest impact.
ArcTitan is an easy-to-implement “set-and-forget” email archiving solution that helps businesses meet their legal responsibilities for data retention and ensures that no email is ever lost, with lightning-fast search and retrieval.
“Our team is truly honored by Expert Insights’ acknowledgment of TitanHQ as the ‘Top Solution’ Provider in their Q4 2023 Awards.,” said TitanHQ CEO, Ronan Kavanagh. “This recognition across multiple categories underscores our commitment to empowering our partners and MSPs with cutting-edge technology, enabling them to deliver advanced network security solutions to their clients.”
by Jennifer Marsh | Nov 23, 2023 | Network Security, Spam Software |
Malware sandboxing for email is now vital for email security. Suspicious files that pass AV checks are sent to the sandbox where they are safely detonated and subjected to behavioral analysis.
Email-based Cyberattacks are Increasing
Email is one of the most common initial access vectors used by cybercriminals. Initial access to victims’ networks is gained via two main methods: email attachments and embedded URLs. The first attack type involves emails with attachments that contain malicious code, such as macros. If the files are opened and the code is allowed to execute, it will trigger the download and execution of malware from a remote server, or in some cases, malware will be executed in the memory (fileless malware).
The other method, which is now more common since Microsoft started blocking macros in Office documents by default if they are received via the Internet, is for phishing emails to be sent that contain malicious URLs. These URLs may be added to the message body or be hidden inside documents. These URLs point to an Internet site that hosts malware which is silently downloaded when the link is visited or the user is tricked into installing the malware.
Businesses need to ensure they have adequate defenses to block email-based attacks. The first line of defense is an email security solution that will scan the message headers, message body, and attachments and perform reputation checks on the sender. Email security solutions use blacklists of malicious domains and IP addresses and will block messages from these domains and IPs if they have previously been used for phishing, scams, or malware distribution. Checks will be performed on URLs and the messages are searched for the signatures of spam and phishing content – words and phrases commonly used by threat actors. If these checks are failed, the messages will be quarantined.
To block malware, email security solutions scan email attachments using anti-virus engines, which search for the signatures of malware – specific parts of the malware code that have been identified in previous malware analyses. The anti-virus software is regularly updated, and new signatures are added when new malware variants are identified. While these scans will block all known malware if the signature for malware is not in the definition list, the file will not be classed as malicious, and the message will be delivered to the end user. Unfortunately, new malware variants are being released faster than ever before to get around signature-based detection. To block unknown malware another method is required – malware sandboxing for email.
Malware Sandboxing for Email
Advanced email security solutions include malware sandboxing for email. If an email attachment passes the standard checks and anti-virus scans, it is sent to a sandbox where the behavior of the file is analyzed. A sandbox is an isolated, secure environment where files can be opened and analyzed without risk. Any checks of the environment that are performed by malware when it is executed are often passed as the sandbox is created to look exactly like a real endpoint. Any actions performed by files when they are opened are analyzed in detail and if any checks fail, the file and email will be quarantined and all other copies of that email will be removed from the email system. These checks may take a few minutes to perform, so there will be a slight delay in delivering genuine emails.
SpamTitan, TitanHQ’s award-winning email security solution, includes a powerful next-gen sandbox that is powered by Bitdefender. The malware sandboxing service uses powerful emulation tools to ensure that files are inspected using real-time intelligence along with comprehensive detection techniques, which provide advanced threat protection and zero-day exploit detection. To avoid unnecessary email delivery delays, SpamTitan has strong machine learning, static analysis, and behavior detection technologies which ensure that only files that require further analysis get sent to the sandbox. If all sandbox checks are passed, the message will be delivered. If one or more checks are failed, the message will be quarantined, and the results passed to Bitdefender’s Global Protective Network. If that threat is encountered again, it will be recognized and will be quarantined immediately and will not need to get sent to the sandbox to be detonated again.
With SpamTitan malware sandboxing for email, businesses will be well protected against zero-day malware threats that would otherwise be delivered to inboxes. For more information give the TitanHQ team a call. SpamTitan with malware sandboxing for email is also available on a 14-day free trial.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Nov 20, 2023 | Network Security, Spam Software |
Implementing your own sandboxing technology for email can be complex and costly. SpamTitan Email Security has an inbuilt sandbox, so all the hard work is done for you. You get the full cybersecurity benefits of a sandbox at a very low cost.
What are the Benefits of an Email Sandbox?
Email sandboxing is no longer a ’want’ it is now a ‘must-have.’ Cybercriminal groups are conducting huge numbers of attacks, nation-state actors are targeting businesses to steal their proprietary data, and these attacks are getting far more sophisticated and can easily evade standard security solutions. The consequences of a successful cyberattack are severe. IBM’s 2023 Cost of a Data Breach Report indicates that the average cost of a successful attack and data breach has risen to $4.45 million in the United States. It is no surprise that many small to medium-sized businesses fold within 6 months of a successful attack.
As has been the case for many years, one of the easiest ways to gain initial access to a company’s network is via email. Employees are targeted as they can be tricked into disclosing their credentials or installing malware. Email security solutions such as spam filters and secure email gateways are capable of blocking many threats, but they are failing to block zero-day malware threats. Traditional email security solutions are reliant on signature-based detection methods for blocking malware. When a malware threat is detected and analyzed by security researchers, the signature for that malware variant is added to the definition list. Email security solutions use signature-based detection methods to block 100% of known malware.
The problem comes with new malware, for which no signature has been defined. Without a signature, malware will not be identified as malicious if it is encountered. If a novel malware variant is attached to an email, the email will most likely be delivered and can be opened by an end user and new malware variants are now being released at an incredible rate. While signature-based detection has served businesses well, additional protection is now required – email sandboxing.
With an email security solution that has an email sandbox, inbound messages will first be subjected to standard checks. An email sandbox is then used to safely analyze the behavior of files in an environment where no harm can be caused. If malware is executed, it will be detected based on its behavior rather than a signature. The threat will then be blocked, and no harm will be caused.
SpamTitan Email Sandboxing Technology for Email
With SpamTitan, the initial checks include AI-based and machine-learning detection, which is capable of detecting previously unseen phishing threats. All attachments are scanned with two antivirus engines to ensure 100% of known malware threats are detected and blocked. The sandbox provides an extra layer of protection. When initial checks are passed, suspicious messages are sent to the sandbox for deep analysis. File attachments are safely detonated, their behavior is analyzed, and the results are checked against an extensive array of online repositories. The process usually takes just a few minutes, or in some cases, a maximum of 20 minutes.
If a threat is detected it is reported to the Bitdefender Global Protective Network – Bitdefender’s cloud threat intelligence service. If that threat is detected again by SpamTitan or any device connected to the network, it will not need to be sent to the sandbox again and all devices will be protected against that threat. The latest malware variants often include code that checks for running security solutions and whether it has landed on a real endpoint. If a virtual environment is detected and the malware determines it is in a sandbox, it will not perform its malicious actions and may delete itself to prevent analysis. To get around this, the email sandbox emulates a real endpoint and analyzes files by leveraging purpose-built, advanced machine-learning algorithms. The sandbox incorporates anti-evasion and anti-exploit techniques and performs aggressive behavior analysis. Every evasion attempt by malware is properly marked and the files are flagged.
The sandbox analyzes a broad range of targets, including documents, spreadsheets, and executable files, and is capable of identifying and blocking polymorphic malware and other threats that have been developed for undetectable attacks. With email-based cyberattacks increasing in number and sophistication, businesses need to ensure they have advanced defenses. With SpamTitan sandboxing technology for email you get advanced threat protection at an affordable price. To find out more, call the TitanHQ team today or take advantage of a free 14-day free trial of SpamTitan.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Nov 15, 2023 | Network Security, Spam Software |
What is Sandboxing in Cybersecurity?
Sandboxing in cybersecurity terms refers to an isolated virtual machine that is used for testing code and analyzing files. Since the sandbox is isolated from other systems and networks, unverified code, untested programs, email attachments, and files downloaded from the Internet can be executed or detonated safely. Code is executed and files are opened and their behavior is analyzed to determine if they are safe or if they may cause damage to data or systems. In the sandbox, the activities that can be performed are restricted so they can’t cause any real damage. If code is executed in the sandbox and it is determined to be malicious, it will be deleted or quarantined for further analysis. Sandboxing is also used for checking URLs. For instance, some web browsers will first open a URL in a sandbox where permissions are set to the lowest privilege levels. If any attempt is made to perform an action that is not permitted, access to the URL will either be blocked or the user will receive a warning.
Why is Sandboxing Important?
In software development, new code may have unintended consequences, such as causing other systems to malfunction, which in a production environment could cause unacceptable and costly downtime. A sandbox allows code to be fully tested to ensure it is safe. A security sandbox protects against malicious code that has been deliberately written to cause damage and/or provide access to systems and data. For example, ransomware is malicious code that encrypts files to prevent them from being accessed. A threat actor then demands payment for the keys to decrypt files. If that code was allowed to execute on the network, data could be permanently lost, or a ransom would need to be paid to recover files.
Cyberattacks on businesses have been increasing and are now being conducted more frequently than ever before. The average ransom demand in data theft and ransomware attacks is now more than $1.5 million, and data from Rapid7 suggests more than 1,500 organizations fell victim to ransomware attacks in the first half of 2023, with more than 20 new ransom groups emerging. Cybercriminals also still use backdoors, keyloggers, banking trojans, and information stealers to gain access to networks and steal sensitive data. To make matters worse, new malware and ransomware variants are constantly being released and these evade security solutions that rely on signature-based detection. It is vital that all files and applications are thoroughly tested before being allowed anywhere near the network and sandboxing allows even previously unseen malicious files to be identified and neutralized.
Email Sandboxing
Email security solutions often use sandboxing for attachments and URLs. With email attachments, they will first be scanned using standard anti-virus engines to determine if they contain known malware or malicious code. These AV checks will only detect known malware. New malware variants that have not been encountered before cannot be detected, as standard AV solutions search for signatures of known malware. Email sandboxing is used to detect new malware, often referred to as zero-day threats. Files that are determined to be clean after AV scanning are sent to the sandbox for behavioral analysis. Email security solutions may also use a sandbox for testing embedded URLs in messages and will follow the links and check the destination and assess whether it contains any threats.
Email Sandboxing from TitanHQ
SpamTitan is a multi-award-winning email security solution from TitanHQ that offers advanced threat protection at an affordable price. SpamTitan blocks phishing, malware, spam, viruses, and other malicious email threats and includes a Bitdefender-powered email sandbox. Emails that pass the initial barrage of checks, including antivirus scans, are sent to the sandbox where they are safely detonated, and their behavior is analyzed. The SpamTitan sandbox combines the latest threat analysis with powerful emulation tools to ensure that files are inspected using real-time intelligence along with comprehensive detection techniques, ensuring businesses are protected against zero-day threats. For more information on SpamTitan Email Security, give the TitanHQ team a call today.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Nov 10, 2023 | Network Security, Spam Software |
Sandboxing is the use of a virtual environment for testing code and safely opening untrusted files. The sandbox is an isolated and secure environment that emulates a legitimate endpoint; however, there are no connections to the business network, the sandbox environment contains no real data, and if dangerous code is executed, no harm will be caused.
Advantages of Email Sandboxing
Sandboxing is important because of the sheer number and complexity of threats faced by businesses. Cybercriminal groups are conducting increasing numbers of attacks, new groups are constantly being formed, and their attacks are becoming much more sophisticated. The cost of these attacks and the resultant data breaches are also spiraling. According to the 2023 Cost of a Data Breach Report from IBM, on average, data breaches cost $4.45 million to resolve in the United States and $10.93 million for a healthcare data breach.
Many of these threats come from email. Emails are used to send attachments containing malicious code that downloads malware that provides a cyber actor with access to the network. Links to malicious websites are also distributed via email where malware is downloaded. While businesses have a degree of protection if they have anti-virus software installed, most anti-virus solutions can only detect known malware variants – Malware that has previously been analyzed and had its signature added to the solution’s malware definition list. Antivirus solutions will not detect new malware variants nor fileless malware, which is executed in the memory with no files downloaded to the disk.
Sandboxing provides an additional layer of protection against zero-day malware and ransomware attacks and will allow malicious files to be identified, detected, and quarantined before they can do any harm, even if they have not previously been encountered. In the sandbox, malware is identified by the actions it tries to perform, not by any signature.
Disadvantages of Email Sandboxing
While there are clear benefits, there are some disadvantages of email sandboxing. Businesses may want to add email sandboxing to their cybersecurity arsenal, but email sandboxes can be complicated to set up and run, and they can require a considerable amount of resources and can be expensive to run. Another of the disadvantages of email sandboxing is analyzing file attachments takes time and messages cannot be delivered until all checks have been performed. It is therefore inevitable that there will be email delivery delays.
As with any cybersecurity solution, there is the potential for false positives. An email attachment may be determined to be malicious when it is actually harmless. In such cases, important business emails may be blocked or deleted. The last main disadvantage is malware often contains code that determines if it has landed on the targeted endpoint or if it is in a virtual environment. If the latter is detected, the malware may delete itself or not perform any of its programmed malicious actions. Considering the cost of a successful cyberattack, the advantages of email sandboxing outweigh the disadvantages, provided the right sandboxing solution is chosen.
SpamTitan Email Security with Sandboxing
SpamTitan is an award-winning email security solution from TitanHQ that provides advanced threat protection at an affordable price. The solution is easy to implement and use and protects thousands of SMBs and managed service providers (MSPs) by blocking spam, viruses, malware, ransomware, and links to malicious websites from your emails. SpamTitan’s ATP defense uses inbuilt Bayesian auto-learning and heuristics to defend against advanced threats and evolving cyberattack techniques and features an integrated email sandbox tool that is part of Bitdefender’s Global Protective Network.
SpamTitan uses advanced intelligent technologies, such as AI, to predict and prevent advanced threats and the sandbox accurately mimics a real endpoint to trick malware into determining it has reached its intended target. As with any sandbox, there are delays in delivering emails but this is kept to a minimum. SpamTitan has multiple layers of security and sophisticated sandbox technology, which means only specific and dangerous emails will be sandboxed. Even if a legitimate email lands in a sandbox, the delivery delay will be, at most, twenty minutes. While there may be false positives on occasion, no emails are deleted. They are quarantined to allow administrators to check the validity of the results.
If you want to improve security and get the advantages of email sandboxes while eliminating the disadvantages, give the TitanHQ team a call today. SpamTitan is also available on a free 14-day trial to allow you to test the product and sandbox in your own environment before making a purchase decision.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Nov 5, 2023 | Network Security, Spam Software |
Multiple layers of security are required to protect against increasingly sophisticated email attacks. A malicious file sandbox for email should be one of those layers to ensure your business is protected against zero-day and stealthy malware threats.
Email: The Most Common Initial Access Vector Used by Cybercriminals
There are many ways that cybercriminals can attack businesses, but email is the most common initial access vector. Most employees have email accounts which means they can be easily reached, and social engineering techniques are used to trick employees into opening malicious attachments or visiting links in emails. Cybercriminals have become adept at exploiting human weaknesses in defenses.
One of the main aims of email campaigns is to deliver malware to provide persistent access to victims’ networks. Executable files may be attached to emails and hidden using double file extensions to make the files appear to be legitimate documents, PDF files, or spreadsheets. Office files may be attached that have malicious macros which, if allowed to run, trigger the download of a first-stage malware payload. The problem for businesses is these campaigns are becoming much more sophisticated, they often bypass standard email security defenses, and they land in inboxes where they can be opened by employees.
Defending against sophisticated email attacks requires a defense-in-depth approach, which should include a spam filter/secure email gateway, a web filter, multifactor authentication, an endpoint detection and response solution, and security awareness training for employees. To improve protection further and defend against new and stealthy malware threats, it is important to have a malicious file sandbox for email.
What is a Malicious File Sandbox?
A malicious file sandbox is an isolated virtual environment where untrusted, suspicious files can be detonated securely without risking network or data security. The sandbox is used for analyzing emails, documents, application files, and other executable files to determine their true nature. When an email is received, it must first pass through a spam filter which looks for the common signatures of spam and phishing emails, performs reputation checks on the sender, analyzes the message content, and scans email attachments using antivirus software. The spam filter will filter out the majority of spam and phishing emails and all known malware variants using the antivirus software.
The problem is many email attacks are stealthy and have been developed to be undetectable, and cyber actors are skilled at getting their emails past email defenses and into inboxes. One way this is achieved is by using polymorphic malware, which cannot be detected by standard email security solutions and antivirus software. A malicious file sandbox is needed to protect against these novel threats.
When suspicious files are received that pass the front-end checks, they are sent to the sandbox for in-depth analysis of their behavior. The malicious file sandbox is configured to look like a real target environment to ensure that when an email is sent to the sandbox any malware acts as it would in the wild and is tricked into determining that it has landed on the endpoint of its intended target. No harm can be caused in the sandbox as the environment is isolated and not set up locally. If malware is detected, a report is generated of any malicious intent or unexpected actions, and actionable insights are provided to allow the threat to be blocked.
The SpamTitan Malicious File Sandboxing Service
SpamTitan is an award-winning anti-spam and anti-phishing solution from TitanHQ that is used by thousands of businesses and managed service providers to protect against email-based attacks. The solution leverages artificial intelligence and machine learning algorithms to detect novel threats and predict new attacks, reputation checks are conducted using SPF, DKIM, and DMARC, users are protected from malicious links in emails, and the solution has dual antivirus engines that scan for known malware.
SpamTitan also includes a Bitdefender-powered malicious file sandbox for blocking zero-day malware threats. The sandbox analyzes a broad range of targets, including emails, documents, application files, and other executable files, and leverages purpose-built, advanced machine-learning algorithms, aggressive behavior analysis, anti-evasion techniques, and memory snapshot comparison to detect sophisticated threats and delivers advanced threat protection and zero-day exploit detection. The sandbox also extracts, analyzes, and validates URLs within files.
The sandbox is not located on the endpoint so there are no performance implications, and strong machine learning and behavior detection technologies ensure that only files that require further analysis are sent to the Sandbox. If a malicious file is detected, the sandbox informs Bitdefender’s cloud threat intelligence service to ensure the threat is instantly blocked globally and will not need to be set to the sandbox for analysis again. The sandbox allows businesses to identify and block malicious files such as polymorphic malware and other threats that have been developed for use in undetectable attacks.
The SpamTitan malicious file sandbox delivers best-in-class detection, advanced anti-evasion technologies, innovative pre-filtering, and MITRE ATT&CK framework support. If you want the best protection from dangerous malware, you need a malicious file sandbox for email, and with SpamTitan you get that and more at a very affordable price. For more information on the capabilities of SpamTitan and details of pricing, give the TitanHQ team a call. SpamTitan is also available on a free 14-day trial to allow you to test the product in your own environment before making a purchasing decision.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Oct 28, 2023 | Spam Advice, Spam Software |
Message sandboxing is a security feature of spam filters, secure email gateways, and other email security solutions where inbound messages are sent to a secure and isolated environment where the messages are subjected to behavioral analysis. File attachments are detonated and analyzed for malicious properties and actions, such as attempted file downloads from the Internet, command-and-control center callbacks, and attempts to write code to the memory.
What is a Sandbox?
In the technology sense, a sandbox is a contained virtual environment that is separate and isolated from other applications, operating systems, data, and internal networks. Sandboxes have several uses. In software development, a sandbox is used for testing new code, where it can be observed for unexpected compatibility issues, allowing software developers to troubleshoot the code without causing any harm to live systems and data.
In cybersecurity, a sandbox is used to open untrusted files, follow potentially malicious links, and analyze suspicious code and malware. If malware was installed and executed on a standard machine, the threat actor would be given remote access, malware may exfiltrate sensitive data, or in the case of ransomware, encrypt files. Since the sandbox is a secure environment, any malicious action has no consequences, and files can be studied in safety.
A sandbox is a virtual environment that is often configured to mimic a genuine endpoint. One of the first actions taken by malware is to explore the environment it is in to check whether it is on a genuine device. If not, it is likely not to run any malicious routines and may self-delete to prevent analysis. By configuring the sandbox to mirror a genuine endpoint, the malware can be tricked into performing its malicious routines, which are detected and logged. The intelligence gathered is fed into the email security solution, and all users of that solution, locally and globally, will be protected from that malware sample in the future.
Why is Message Sandboxing Necessary?
Traditional email security solutions check message headers, perform reputation checks of senders, scan email attachments with antivirus engines, follow embedded hyperlinks, and examine the content of the message for known spam and phishing signatures. For many years, these checks alone have been sufficient and ensure that more than 99% of spam and phishing emails are detected and blocked along with all known malware.
Email attacks have been getting much more sophisticated in recent years and new malware variants are being released at never-before-seen rates. A malware phishing campaign, for instance, will not just use one iteration of malware, but many, with each sample differing sufficiently to defeat signature-based detection mechanisms. Cybercriminals are using automation to spin up masses of samples and AI is being used to develop novel phishing methods.
AI and machine learning capabilities are now required in email security for blocking these zero-day threats, and email message sandboxing is necessary for detecting novel malware threats. Advanced email security solutions leverage AI, machine learning, and email sandboxing and protect against the rapidly evolving threat landscape. Without these features, many malicious messages will be delivered.
How to Set Up Message Sandboxing
The easiest way to get started and set up message sandboxing is to use SpamTitan Email Security. SpamTitan has been developed to be easy to set up and use by businesses of all sizes, from small offices and coffee shops to small and medium-sized businesses and large enterprises. Being cloud-based, there is no software to install, just a small configuration change to your MX record (information on how to do this is provided). The solution can be accessed through a web-based interface, and the solution can be configured in just a few minutes.
Users benefit from spam and phishing detection rates of more than 99.99%, a very low false positive rate and a Bitdefender-powered email sandbox. The email sandbox leverages advanced machine learning algorithms, aggressive behavior analysis, anti-evasion techniques, and memory snapshot comparison to detect zero-day threats.
Without an email sandbox, you are likely to be exposed to many malicious messages. With sandbox email protection, you have much better control of the content that reaches user inboxes.
by Jennifer Marsh | Oct 15, 2023 | Phishing & Email Spam, Spam Software |
Do you know how to sandbox email attachments? If you have yet to start using a sandbox for email, you will be exposed to advanced malware and phishing threats. The good news is it is quick and easy to improve protection with a sandbox, and it requires no advanced techniques or skills, but before presenting an easy email sandboxing solution, we should explain why email sandboxing is now a vital part of email security
Email Sandboxing Detects Advanced and Sophisticated Threats
A hacker writes the code for a new malware variant or generates the code using an AI tool, and then sends that malware via email. A traditional email security solution will not block that malware, as it has not detected it before and it doesn’t have the malware signature in its definition list. The email would most likely be delivered, and the intended recipient could open it and infect their device with malware. From there, the entire network could be compromised and ransomware could be deployed.
How could a new, previously unseen threat be blocked? The answer is email sandboxing. When a file passes initial checks, such as AV scans, the attachment is sent to an email sandbox where its behavior is analyzed. It doesn’t matter if the malware has not been seen before. If the file performs any malicious actions, they will be detected, the threat will be blocked, and if that threat is encountered again, it will be immediately neutralized.
Email sandboxing is now an essential part of email security due to the sheer number of novel malware variants now being released. That includes brand new malware samples, malware with obfuscated code, polymorphic malware, and known malware samples that differ just enough to avoid signature-based detection mechanisms. Without behavioral analysis in a sandbox, these threats will be delivered.
The Easy Way to Sandbox Email Attachments
Setting up an email sandbox need not be complicated and time-consuming. All you need to do is sign up for an advanced cloud-based email security solution such as SpamTitan Email Security. SpamTitan is a 100% cloud-based email security solution that requires no software downloads or complex configurations. Just point your MX record to the SpamTitan Cloud and use your login credentials to access the web-based interface. You can adjust the settings to suit your needs, and the setup process is quick, easy, and intuitive, and generally takes around 20-30 minutes.
The solution is fed threat intelligence from a global network of more than 500 million endpoints, ensuring it is kept up to date and can block all known and emerging threats. You will be immediately protected from known malware and ransomware threats, phishing emails, spam, BEC attacks, and spear phishing, and you will benefit from email sandboxing, where suspicious emails are sent for deep analysis to identify zero-day phishing and malware threats.
The SpamTitan email sandbox is powered by Bitdefender and has purpose-built, advanced machine learning algorithms, decoys and anti-evasion techniques, anti-exploit, and aggressive behavior analysis. If a file is analyzed in the sandbox and found to be malicious, SpamTitan updates Bitdefender’s Global Protective Network, ensuring that the new threat is blocked globally.
Email sandboxing doesn’t need to be complicated. Just use SpamTitan from TitanHQ. SpamTitan is available on a free trial, with customer support provided throughout the 14-day trial to help you get the most out of the solution. We are sure you will love it for the level of protection provided and how easy it is to use.
by Jennifer Marsh | Oct 10, 2023 | Phishing & Email Spam, Spam Software |
Businesses are now targeted by advanced persistent threat actors looking for proprietary data, financially motivated threat actors looking to steal sensitive data and conduct extortion attacks, and hacktivist groups that aim to disrupt business operations.
Many of these attacks see initial access to internal networks and accounts gained via email. Credential phishing and malware phishing attempts serve a similar purpose and allow threat actors to obtain initial access to allow them to achieve their objectives, whether that is to gain persistent access for espionage purposes, to steal data, use ransomware, or wipe devices.
Email techniques such as phishing and spear phishing for credential theft or the use of malspam emails for delivering malware can be sophisticated and difficult for end users to detect. Further, advances in artificial intelligence have led to generative AI solutions that are capable of producing flawless phishing emails and generating novel social engineering techniques to trick users into taking the required actions – following a link, disclosing sensitive data, or downloading and executing malware.
Spam filters and secure email gateways have long protected businesses against these threats, but increasingly sophisticated techniques are now used that can bypass the protections of traditional email security solutions and reach end users. To combat these threats email security solutions have had to adapt. Cutting-edge email security solutions such as SpamTitan Email Security have AI and machine learning capabilities that are capable of detecting advanced and sophisticated attacks, in addition to DMARC, SPK, and DKIM reputation checks, and blacklists of known malicious IP addresses and domains.
One of the biggest threats comes from malware, either attached to emails or downloaded from URLs that are linked in email messages. For many years, antivirus engines have been effective at detecting and blocking malware threats, and while they still provide a degree of protection, AV engines are signature-based. When a new malware sample is detected, a unique signature is detected and added to a malware definition list. When a new file is received, it will be checked against all known signatures. If that signature is detected, the file will be quarantined or deleted.
New malware samples, which are being released at an incredible rate, will not be detected as malicious, as their signature has yet to be created and added to the list. These files will therefore not be detected as malicious and will be delivered to inboxes. To protect against this, advanced email security solutions use email sandboxing.
Email sandboxing involves creating an isolated, protected environment for analyzing suspicious emails. If front-end checks are passed, the email is sent to the sandbox for deep analysis. The sandbox is a protected environment where no harm can be caused, and files can be safely analyzed for malicious behavior.
TitanHQ’s Email Sandbox Service
In response to growing threats, TitanHQ added a next-generation email sandbox to its SpamTitan Email Security solution in 2019 to better protect users against malware, spear-phishing, advanced persistent threats (APTs), and to provide security teams with insights into new threats.
TitanHQ’s email sandbox service incorporates award-winning machine learning and behavioral analysis technologies, allowing security teams to safely detonate suspicious files in a secure environment that mirrors production endpoints. Malicious actors are tricked into thinking their malicious payloads have reached their intended target, and the malicious activities are detected. The sandbox analyzes documents, spreadsheets, application files, and executable files, and can detect malware, including polymorphic malware, and other sophisticated threats that have been developed for use in undetectable targeted attacks.
The TitanHQ email sandbox service leverages purpose-built, advanced machine learning algorithms, decoys and anti-evasion techniques, anti-exploit, and aggressive behavior analysis, and all results are checked against an extensive array of online repositories. The analysis takes from a few seconds to a few minutes, and if a malicious file is detected, the results will be uploaded to a cloud threat intelligence service and all users will be protected. If that threat is detected on any device globally, it will not need to be sent to the sandbox again and will be instantly neutralized.
SpamTitan email sandbox service greatly increases the detection rate of elusive threats in the pre-execution stage, including APTs, targeted attacks, evasion techniques, obfuscated malware, custom malware, and ransomware, allows security teams to quickly integrate advanced emulation-based malware analysis, and protects against a rapidly evolving threat landscape.
You can put the SpamTitan email sandbox service to the test today by signing up for a 100% free trial and instantly start protecting your business with sandbox technology.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Oct 5, 2023 | Phishing & Email Spam, Spam Software |
Sandboxing is a security feature that protects against malicious code. Rather than execute potentially unsafe code in a standard environment, it is sent to the sandbox – an isolated environment where no harm can be caused.
How Does a Sandbox Work?
A sandbox is an important cybersecurity tool for protecting host devices, operating systems, and data from being exposed to potential threats. The sandbox is a highly controlled system that is used to analyze untrusted applications, files, or code. The sandbox is isolated from the network and real data, and there are only essential resources that are authorized for use. It is not possible for a sandboxed file to access other parts of the network, resources, or the file system, only those specifically set up for the sandbox.
Sandboxes can have different environments. One of the most common implementations uses virtualization. A virtual machine (VM) is set up specifically to examine suspicious programs and code. Some sandboxes include emulation of operating systems to mimic a standard endpoint. Some malware samples perform checks of their environment before executing malicious routines to make sure they are not in a VM. If a VM is detected, the malware will not execute malicious routes and may self-delete to prevent analysis. By emulating a standard endpoint, these checks can be passed to allow analysis. Some sandboxes have full system emulation, which includes the host machine’s physical hardware as well as its operating system and software. These sandboxes provide deeper visibility into the behavior and impact of a program.
In email security, files, attachments, URLs, and programs are sent to the sandbox to check whether they are benign or malicious. The analyses can take between a few seconds to a few minutes, and if any malicious activity is detected, the file will be either quarantined and made available for further study or it will be deleted. Any other instances of that file will be removed from the email system, and any future encounters will see the file, attachment, URL, or program deleted.
SpamTitan Email Sandboxing
SpamTitan Email Security includes a Bitdefender-powered email sandbox to ensure users are protected against zero-day threats. All emails are subjected to a barrage of checks and tests, including scans using two different antivirus engines. SpamTitan features strong machine learning, static analysis, and behavior detection technologies to ensure that only files that require deep analysis get sent to the sandbox. This is important, as deeper analysis may take several minutes, so verified clean and safe messages will not be unduly delayed.
Files that are sent to the sandbox for deep analysis are executed and monitored for signs of malicious activity, with self-protection mechanisms in place to ensure every evasion attempt by a piece of malware is properly marked. The sandbox has purpose-built, advanced machine learning algorithms, decoys and anti-evasion techniques, anti-exploit, and aggressive behavior analysis. All results are checked across known threats in an extensive array of online repositories. If a malicious file is detected, the sandbox updates the Bitdefender’s cloud threat intelligence service – the Bitdefender Global Protective Network – and the sandbox will never have to analyze that threat again as it will be blocked globally.
If you want to improve protection against zero-day threats, give the TitanHQ team a call to find out more about SpamTitan. SpamTitan is available on a free trial to allow you to test it out in your own environment before making a purchase decision.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Oct 1, 2023 | Phishing & Email Spam, Spam Software |
What is sandbox security? In an IT sense, sandbox security refers to the use of an isolated environment for testing potentially malicious or unsafe code. The sandbox is an environment that resembles the organization’s real environment. The sandbox is made to look like it is a legitimate rather than a virtual environment; however, the sandbox is totally isolated from other systems and contains no real data.
A sandbox is used for malware analysis, testing potentially unsafe code, or as a guest environment with a tightly controlled set of resources, with no ability to inspect the host system or gain access to the networks, therefore not exposing any threats to real systems or data. For example, if a file needs to be opened and it is unclear whether it contains malicious code, it is opened in a sandbox. Security teams can assess the behavior of the file to determine if it is benign or malicious, and if it is the latter, no harm will be caused.
Sandboxes are commonly used for testing new code to determine whether it is safe and compatible with other systems, without actually putting those systems at risk. The sandbox is used to perform troubleshooting to identify any problematic parts of the code. One of the main benefits of sandbox security is blocking cyberattacks, and sandboxing has become indispensable for email security.
Email Sandboxing
Email sandboxing is the use of a sandbox environment for inbound email, which can be used to protect against phishing and malware threats. When an email is received that contains an attachment or a hyperlink, these can be evaluated in the sandbox before the message is released for delivery to the end user’s inbox. Phishing is one of the most common ways that malicious actors gain initial access to internal networks. Emails are often sent that contain hyperlinks to URLs that host phishing kits that steal credentials or sites hosting malware. These emails can be sent to a sandbox where the links can be followed, and the content of the URLs assessed. If a file download is triggered, the file can be analyzed to determine its behavior.
The same applies to email attachments. An email attachment such as a Word document or Excel spreadsheet may contain a malicious macro or other malicious code, which could provide a threat actor with remote access to the device and network. By opening the attachment in the sandbox, the behavior of the file can be analyzed safely. If found to be malicious, all other instances of that malware can be removed and if the file is received again, it will be automatically deleted. Security teams can also safely study malware to determine the nature of the threat and learn important information about the adversary and their intentions.
Why Is Email Sandboxing So Important?
Traditional email security solutions are effective at detecting and blocking known malware threats. They use one or more antivirus engines for scanning email attachments for known signatures of viruses and malware. If these signatures are detected, the threat will be blocked. The problem with signature-based detection is the signature must be known. While virus definition lists are updated on a daily or even hourly basis, new malware threats are constantly being released. If a new malware variant is received for which there is no signature, it will not be detected as malicious and will be delivered to an inbox where it can be executed.
Sandbox security plugs this security gap. If an attachment passes AV checks, it is sent to the sandbox for deep analysis of its behavior, allowing zero-day malware threats to be detected and blocked. Cybercriminals do not just use one version of a malware sample, they use many different versions, each differing sufficiently to evade AV checks. Without sandbox security, organizations are at risk of infection with these malware variants.
TitanHQ’s SpamTitan Email Security solution features dual antivirus engines for detecting known malware threats, and a Bitdefender-powered email sandbox for detecting zero day malware and phishing threats and provides security teams with valuable insights into new threats to help them mitigate risks. Give the TitanHQ team a call to find out more about how SpamTitan with sandbox security can improve your security posture. SpamTitan is also available on a free trial to allow you to put the product to the test and see for yourself the difference it makes.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Sep 27, 2023 | Phishing & Email Spam, Spam Software |
https://www.spamtitan.com/blog/email-sandboxing-key-blocking-malware-threats/Email security solutions with email sandboxing block more malware threats than traditional spam filters, even novel malware variants that have yet to be identified as malicious. Without this important feature, emails with malicious attachments will likely be delivered to inboxes where they can be opened by employees. All it takes is for one employee to open a malicious file for malware to be installed that gives a threat actor the foothold they need for a comprehensive attack on the network.
What is an Email Sandbox?
In cybersecurity terms, a sandbox is an isolated, virtual machine where potentially unsafe code can be executed in safety, files can be subjected to deep analysis, and URLs can be visited without risk. In the sandbox, the behavior of files, code, and URLs is inspected, and since the sandbox is not networked and there is no access to real data or applications, there is no risk of causing any damage. Email sandboxing is used to identify malicious code and URLs in emails. The email sandbox mirrors standard endpoints to trick malicious actors into thinking that they have reached their intended target. Emails may pass front-end tests that look at the reputation of the sender, email headers, the content of the messages, and subject attachments to signature-based anti-virus tests, but there is no guarantee that the emails are safe without sandbox-based behavioral analysis.
Why is Email Sandboxing Important?
Cyber threat actors have been developing techniques for bypassing standard email security solutions such as embedding malicious URLs in PDF attachments, hiding malicious content in compressed files, using multiple redirects on hyperlinks, and including links to legitimate cloud-based platforms such as SharePoint for distributing malware. Traditional email security solutions can filter out spam and phishing emails, but they often fail to block more sophisticated threats, especially zero-day malware threats. Email sandboxing provides an extra layer of protection against sophisticated threats such as spear-phishing emails, advanced persistent threats (APTs), and novel malware variants.
A few years ago, new malware variants were released at a fairly slow pace; however, threat actors are now using automation and artificial intelligence to generate new malware variants at an alarming rate. Malware samples are used that deviate sufficiently from a known threat to be able to bypass signature-based detection mechanisms, ensuring they reach their intended targets. Rather than just using one version of malware in their email campaigns, dozens of versions are created on a daily basis. While security awareness training will help employees identify and avoid suspicious emails, threat actors have become adept at social engineering and often hoodwink employees.
The SpamTitan Email Sandbox
The SpamTitan email sandbox is a powerful next-generation security feature with award-winning machine-learning and behavioral analysis technologies. Powered by Bitdefender, the SpamTitan sandbox for email allows files to be safely detonated where they can do no harm. Email attachments that pass the barrage of checks performed by SpamTitan are sent to the sandbox for deep analysis. The sandbox is a virtual environment that is configured to appear to be a typical endpoint and incorporates purpose-built, advanced machine learning algorithms, decoys and anti-evasion techniques, anti-exploit, and aggressive behavior analysis. Files are also subjected to checks across an extensive array of online repositories, with the sandbox checks taking just a few minutes. That ensures that genuine emails are not unduly delayed. If malicious properties are detected in the sandbox, the threat intelligence is passed to Bitdefender’s Global Protective Network (cloud threat intelligence service). If the threat is encountered again, it will be detected and blocked without having to be analyzed again in the sandbox.
The SpamTitan sandbox is used for a wide range of attachments, including office documents to check for malicious URLs, macros, and scripts, and all executable and application files. The sandbox allows SpamTitan to detect polymorphic malware and other threats that have been designed for use in undetectable targeted attacks. If a malicious file is detected, the email is not sent to a spam folder where it could be opened by an end user, it is quarantined in a directory on the local email server which only an administrator can access. Administrators may wish to conduct further investigations to gain insights into how their organization is being targeted.
Threat actors are conducting increasingly sophisticated attacks, so email security solutions need to be deployed that are capable of detecting these advanced threats. With zero-day threats on the rise, now is the ideal time to improve your email defenses with SpamTitan. Why not sign up for a free trial of SpamTitan today to put the solution to the test to see the difference the advanced threat detection capabilities make to your security posture? Product demonstrations can also be requested by contacting TitanHQ, and our friendly sales team will be more than happy to discuss SpamTitan with you and the best deployment options to meet the needs of your business.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Sep 15, 2023 | Phishing & Email Spam, Spam Software |
Commonly asked questions about email sandboxing so you know what to expect from an email security solution with a sandbox, and why this advanced feature is vital for email security.
What is an Email Sandbox?
One of the commonly asked questions about email sandboxing is what is an email sandbox? Like the children’s equivalent, it is a safe space for building, destroying, and experimenting. In cybersecurity terms, it is an isolated environment where harm cannot be caused to anything outside of that environment. An email sandbox is an isolated virtual machine that is used for performing risky actions, such as opening unknown attachments and analyzing files and URLs in depth, rather than using a real machine where there is a risk of harm being caused such as file encryption by ransomware, theft of sensitive information, or wiping of data.
Why is an Email Sandbox Important?
Email is the most common vector used in cyberattacks. Through emails, cyber threat actors can gain initial access to a protected network from where they can steal sensitive data or move laterally for a more comprehensive attack. One of the most common ways of gaining remote access is through malware. Once malware is downloaded, an attacker can remotely perform commands and gain full control of an infected device. While businesses use antivirus software to detect and remove malware, these solutions are signature-based. In order to detect malware, the signature of the malware must be in the definition list used by the anti-virus solution, which means the malware must have previously been encountered. Novel malware variants that have not yet been determined to be malicious will not be identified as such and will therefore be delivered to inboxes where they can be executed by employees. An email sandbox is used to safely detonate suspicious files and inspect their behaviors. The behavioral analysis allows previously unknown malware samples can be identified and blocked. This is important due to the volume of new malware samples that are now being released.
How Does an Email Sandbox Protect Against Malware?
Email security solutions with sandboxing perform the same front-end checks as traditional email security solutions and will identify and block many malicious messages. If the initial checks are passed, and the messages are determined to potentially pose a risk, they will be sent to the sandbox for behavioral analysis. Once inside the safety of the sandbox, the attachments will be opened and subjected to various tests. The sandbox is configured to appear to be a normal endpoint, so any malware will be tricked into running malicious commands as it would if it had reached its intended target. The actions of the file are assessed, and if they are determined to be malicious they will be sent to a quarantine folder. By performing these checks, new malware variants can be identified and blocked before any harm is caused.
Will Sandboxing Delay Message Delivery?
Performing standard checks of messages is a quick process, often causing imperceptible delays in mail delivery. Performing in-depth analysis takes longer, so there will be a delay in message delivery. Many emails will not need to be sent to the sandbox and will be delivered immediately, but if sandboxing is required, there will be a delay while the behaviors of the email and attachments are analyzed. Some malware has built-in anti-analysis capabilities and will delay any malicious processes to combat sandboxing. Time is therefore required to ensure full analysis. With SpamTitan, the delay will be no longer than 20 minutes.
How Can I Avoid Message Delivery Delays?
SpamTitan incorporates artificial intelligence and machine learning capabilities which minimize the number of emails that are sent to the sandbox, and SpamTitan will check every 15 seconds to ensure that emails are delivered as soon as the sandbox analysis is complete. SpamTitan’s sandbox is part of Bitdefender’s Global Protective Network, which ensures rapid checks of suspicious messages. To avoid delays, certain email addresses and domains can be added to a whitelist, which means they will not be sent to the sandbox for analysis, ensuring rapid delivery.
What are the Benefits of Email Sandboxing?
The sandbox provides an important extra layer of protection against malware threats and malicious links. It will detect advanced attacks early and prevent breaches, reduce incident response costs and efforts, reduce the threat-hunting burden, and increase the detection rate of elusive threats in the pre-execution stage, including APTs, targeted attacks, evasion techniques, obfuscated malware, custom malware, ransomware.
How Does the SpamTitan Sandbox Work?
SpamTitan will subject all inbound emails to a battery of front-end tests, and if these are passed but the email is still suspicious, the message and attachment will be sent to the sandbox and the user will be informed that the message is in the sandbox for review. The email and attachments will then be opened in an isolated cloud platform or a secure customer virtual environment. If malware is detected, the email is blocked and assigned ATP.Sandbox and will be listed under “Viruses” in the relevant quarantine report and the intelligence gathered will be used to protect all users from that threat in the future. After twenty minutes of interrogation, if no malicious actions are identified, the file is marked clean and the email is passed onto the recipient.
How Can I Find Out More About Email Security and Sandboxing?
If you have unacceptable numbers of spam and malicious messages being delivered to inboxes, are receiving large numbers of queries about suspicious emails from your employees, or if you have experienced a malware infection via email recently, you should speak with TitanHQ about improving email security with SpamTitan.
SpamTitan has artificial intelligence and machine learning capabilities, a next-gen email sandbox, and a 99.99% detection rate with a very low false positive rate. Further, SpamTitan is very competitively priced, easy to use, and requires little maintenance. The solution is also available on a 100% free trial, with full product support provided for the duration of the trial.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Sep 10, 2023 | Phishing & Email Spam, Spam Software |
Email sandboxing is important for security, as it will block threats that traditional email filters fail to detect. While sandboxing is now considered to be an essential element of email security, one disadvantage is that it will delay the delivery of emails. In this post, we will explain why that is and how email delivery delays can be minimized or avoided altogether.
What Does Queued for Sandbox Mean?
If you use SpamTitan or another email security solution with email sandboxing, you may see the message “email queued for sandbox” from time to time. The queued for sandbox meaning is the message has been determined to warrant further inspection and it has been sent to the sandbox for deeper analysis. This is most likely because the email includes an attachment that is determined to be risky, even though it has passed the initial antivirus scans.
While email sandboxing is important for security, there is a downside, and that is processing messages in a sandbox and conducting behavioral inspection takes a little time. That means there will be a delay in delivering messages that have been sandboxed while behavioral checks are performed. Messages will only be delivered once all sandbox checks have been passed. If a large volume of suspicious emails are received at the same time, messages will be queued for analysis, hence the queued for sandbox message being displayed.
Sandbox Delays for Inbound Emails
The processing of messages in a sandbox can take a little time. Cyber threat actors do not want their malware and malicious code analyzed in a sandbox, as it will allow their malware to be identified. Further, once a malware sample has been identified, details will be shared with all other users of that security solution, which means no user will have that malicious file delivered to their inbox. SpamTitan’s email sandbox is powered by Bitdefender, so all members of the Bitdefender network who subscribe to its feeds will also be protected.
Many malware samples now have anti-sandbox technologies to prevent this. When the malware is dropped on a device it will analyze the environment it is in before launching any malicious actions. If it senses it is in a sandbox it will terminate and may attempt to self-delete to prevent analysis. One technique often seen is delaying any malicious processes for a set time after the payload is delivered. Many sandboxes will only analyze files for a short period, and the delay may be sufficient to trick the sandbox into releasing the file. It is therefore necessary to give the sandbox sufficient time for a full analysis.
Are Your Sandbox Delays Too Long?
Conducting analyses of emails in a sandbox is resource-intensive and can take several minutes and there may be delays to email delivery that are too long for some businesses. There are ways to avoid this, which we will discuss next, but it may be due to the email security solution you are using. The SpamTitan email sandbox is part of Bitdefender’s Global Protective Network, which was chosen not only for cutting-edge threat detection but also the speed of analysis. If you are experiencing long delays receiving emails, you should take advantage of the free trial of SpamTitan to see the difference the solution makes to the speed of email delivery for emails that require sandbox analysis.
How the SpamTitan Sandbox for Email Minimizes Delays
SpamTitan does not send all messages to the sandbox to avoid unnecessary email delays. If a message is suspicious and the decision is taken to send it to the sandbox for analysis, SpamTitan will check to see if the analysis has been completed every 15 seconds to ensure it is released in the shortest possible time frame. Employees will be aware that they have received a message that has been sent to the sandbox as the message delivery status is displayed in their history. Provided all sandbox checks are passed, the email will be delivered. This process will take no longer than 20 minutes. If a file is determined to be legitimate, details are retained by SpamTitan so if the attachment or message is encountered again, it will not be subjected to further analysis in the sandbox.
How to Avoid Sandbox Delays to Message Delivery
There are ways to avoid messages being placed in the queue for sandbox inspection. While it is not always advisable for security reasons, it is possible to whitelist specific email addresses and domains. This will ensure that emails from important clients that need a rapid response will be delivered without delay and will not be sent to the sandbox. The problem with this approach is that if a whitelisted email address or a domain is compromised and used to send malicious messages, they will be delivered.
What Happens if a Message is Misclassified as Malicious?
False positives do occur with spam and phishing emails as email filtering is not an exact science. While this is rare with SpamTitan, any misclassified emails will not be deleted as they will be sent to a quarantine folder. That folder can be configured to be accessible only by an administrator. The administrator can then check the validity of the quarantined messages and release any false positives. Since SpamTitan has artificial intelligence and machine learning capabilities, it will learn from any false positives, thus reducing the false positive rate in the future.
Talk with TitanHQ About Improving Email Security
If you are not currently using an email security solution with sandboxing or if your current email security solution is not AI-driven, contact TitanHQ to find out more about how SpamTitan can improve protection against sophisticated email threats. SpamTitan is available on a free trial to allow you to put the product to the test before deciding on a purchase, and product demonstrations can be arranged on request. If you proceed with a purchase, you will also benefit from TitanHQ’s industry-leading customer service. If you ever have a problem or a query, help is rapidly at hand.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Sep 5, 2023 | Phishing & Email Spam, Spam Software |
You may have heard that email sandboxing is an important security feature, but how does an email sandbox block malware and why is this security feature necessary? In this post, we explain what an email sandbox is, why it is now an important element of email security, and how email sandboxes work.
An email sandbox is a secure and isolated environment where emails and their attachments are subjected to behavioral analysis. In the sandbox, malicious files and code can be safely detonated where no harm can be caused. Say an email is received that contains malicious code that is used to drop and execute ransomware on a device. Executing that code on a standard machine would initiate the process that ends with file encryption. Execute that code in an email sandbox and the malicious behavior would be detected and no harm would be caused. The email and code will then be eradicated from the email system, and the threat intelligence gathered will be sent to a global network to ensure that if the email or code is encountered again it will be immediately blocked.
Many Email Security Solutions Fail to Detect the Most Serious Threats
Traditional email security solutions perform many tests on emails to determine the likelihood of them being spam or malicious. DMARC and SPF are used to check the legitimacy of the sender, checks are performed on the reputation of an IP address/domain, and the subject, title, and body of a message are analyzed for signs of phishing and spam. Email attachments are also subject to anti-virus checks, which will identify and block all known malware variants. The result? Filtered emails contain no known spam, no known malicious hyperlinks, and no known malware.
The problem with traditional email security solutions is they are unable to detect unknown spam, phishing attempts, and malware. If a threat actor uses a previously unseen phishing email, which includes either a link to a fresh URL or a site with a good reputation, that email will most likely be delivered. If a new malware variant is sent via email, its signature will not be present in any virus or malware definition list and will similarly be delivered to an end user’s inbox. Threat intelligence is shared with email security solutions and they are constantly updated as new threats are found but there is a lag, during which time these threats will be delivered to inboxes. That is why an email sandbox is needed.
How an Email Sandbox Works
Antivirus scans will block the majority of malware, but not novel (zero-day) malware threats. When an email security solution has email sandboxing, the same checks are initially performed, and if they are passed, emails are sent to the sandbox for further analysis. The email sandbox is an isolated environment on a virtual machine that is configured to look like a genuine endpoint. As far as the threat actor is concerned, their email will have reached their intended target and the file should execute as it would on a standard machine.
In the sandbox, emails and attachments are opened and links are followed and behavior is analyzed in detail to determine if any malicious or suspicious actions occur such as a command-and-control center callbacks, attempted file encryption, or scans for running processes. If a Word document is opened that contains no hyperlinks, no macros, and no malicious scripts, and nothing suspicious occurs in the time it is present in the sandbox, the file will be determined as benign and the email will then be delivered to the intended recipient. If any malicious actions are detected, the file will be sent to a local quarantine directory where it can only be accessed by the administrator. The intelligence gathered will be sent to the global network and all users will be protected almost instantly. All copies of that message and the attachment will also be removed from the entire mail system.
Email Sandboxing and AI-Driven Threat Detection are Now Vital
Email sandboxing is now vital for email security as new malware variants are being released at an incredible rate and signature-based detection methods cannot detect new malware threats. In addition to email sandboxing, artificial intelligence must be leveraged to look for novel phishing messages, as phishing attempts are also increasing in sophistication. These AI-based checks look for messages that deviate from the typical messages received by a company, and greatly reduce the volume of spam and phishing emails that reach inboxes.
The threat landscape is constantly changing so advanced email defenses are now essential. If you are still using an email security solution without email sandboxing and AI-driven threat detection, your company is at risk. Speak to the team at TitanHQ to find out more about SpamTitan and how the award-winning email security solution can enhance your company’s security posture.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Sep 1, 2023 | Network Security, Spam Software |
SpamTitan is a next-generation anti-spam, anti-phishing, and anti-malware solution for businesses that incorporates AI-based threat detection, email sandboxing, and many other advanced email security features. Some of the most important and best-loved features of SpamTitan are explained below:
Email Sandboxing in SpamTitan
Email sandboxing is a vital element of email security, yet many email security solutions lack this feature. An email sandbox is a secure, virtual machine where links can be followed and attachments opened where they cannot cause any harm. A malicious link that leads to an automatic malware download can be followed in safety, and even the nastiest piece of malware can be executed without risk as the sandbox is isolated, not connected to any network, and contains no real data.
The sandbox is configured to appear to be a genuine endpoint in order to trick malicious actors into thinking malware has reached its intended target. When a file is opened in the sandbox it is subject to deep analysis, and any malicious or suspicious actions are detected. Emails are subject to a battery of front-end checks, including scans using two anti-virus engines, and any emails that pass these checks but are determined to potentially pose a risk are sent to the sandbox for behavioral analysis. That includes emails along with any attached documents, spreadsheets, and executable files.
Sandboxing for email is important because of the speed at which novel malware samples are used in attacks. Rather than just use one version of a keylogger in a campaign, a threat actor will use dozens of versions of that keylogger, each differing slightly to evade signature-based detection mechanisms. AI and automation are used by threat actors to churn out new malware variants rapidly, and signature-based detection alone is no longer good enough. With sandboxing, email protection is greatly improved against these zero-day threats which would otherwise be delivered to end users’ inboxes.
Pattern Filtering in SpamTitan
One of the most loved features of SpamTitan is Pattern Filtering. It saves IT security teams a considerable amount of their precious time by ensuring spammy and phishy emails are not delivered. The Pattern Filtering feature allows administrators to use their own terminology to block inbound emails. Simply set a word or phrase through Pattern Filtering, and SpamTitan will search the subject line and message body and can be configured to generate a warning or quarantine the email if the word or phrase is found.
An example of where this can be useful is combating the Nigerian scam/419 fraud, a type of advanced fee fraud. The 419 comes from Section 419 of the Nigerian Criminal Code which prohibits this kind of scam. While the scam is common with Nigerian cybercriminals, cybercriminal groups in many different countries also conduct this type of scam. While the themes of the emails vary, they all have the same aim. An example would be a prominent person who has substantial funds in their account has been unable to transfer the funds out of the country due to unfair restrictions. They offer to transfer these funds to the user’s account to get the money out of the country in exchange for a percentage of those funds as payment, which may be as high as 20%, which is a life-changing amount of money. The catch? In order to proceed, charges need to be covered and they must be paid in advance. The Pattern Filtering option can be used to block these emails by incorporating phrases commonly used in these emails.
Geo-Filtering in SpamTitan
SpamTitan also incorporates geo-filtering, which allows users to block emails from specific countries. If you never do business with countries in Africa, for example, you can simply block all emails coming from African IP addresses with a few clicks of a mouse, rather than manually blocking IP addresses from which you get a lot of spam emails. This feature saves IT teams a considerable amount of time. One user who has benefited greatly from this feature is Benjamin Jeffrey, IT manager at M&M Golf Cars. His company was receiving many requests from countries that the company does not do business with and was getting flooded with spam emails from a specific IP subnet in a country. He configured the geo-filtering and instantly blocked all those messages. When he checked 6 months after configuring that feature, around 12,000 emails had been blocked. Geo-blocking is also useful for blocking malware quickly. Malware distribution campaigns are often launched from a handful of countries, and geo-filtering can be used to block those messages with ease.
AI and Machine Learning in SpamTitan
SpamTitan has AI and machine learning capabilities to improve the detection of spam and phishing emails. These technologies learn about the emails that are typically received by a company and create a baseline against which new emails can be measured. When emails deviate from the norms, they are flagged as risky and are subjected to more stringent security checks or are quarantined for manual inspection. These technologies greatly improve spam and phishing email catch rates and allow SpamTitan to improve day-by-day. These technologies are a vital defense against zero-day phishing threats – new threats that have not been encountered on the 500+ million endpoints from which threat intelligence is gathered.
Find out More About SpamTitan
These are just some of the most loved and most beneficial features of SpamTitan. In addition to having a high catch-rate and low false positive rate, SpamTitan is one of the most affordable email security solutions on the market, it’s quick and easy to set up, and requires little maintenance. The features, price, and ease of use are why it is loved by thousands of small- and medium-sized businesses, enterprises, and managed service providers. To find out more, give the TitanHQ team a call. The product is available on a 100% free trial if you want to put it to the test, and product demonstrations can be arranged on request.
Additional Articles Related to Email Sandboxing
Email Sandboxing
Email Sandboxing Service
Sandboxing Blocking Malware Threats
Email Sandboxing Pattern Filtering
How does an email sandbox block malware?
Email Sandboxing and Message Delivery Delays
Commonly Asked Questions about Email Sandboxing
What is sandbox security?
How does a sandbox work?
How to sandbox email attachments
What is message sandboxing?
What is malware sandboxing for email?
What is sandboxing in cybersecurity?
What are the advantages and disadvantages of email sandboxing?
Sandboxing Technology for Email
What is a malicious file sandbox for email?
by Jennifer Marsh | Jul 25, 2023 | Industry News, Internet Security, Security Awareness, Spam Software, Website Filtering |
TitanHQ has made several enhancements to its suite of cybersecurity solutions this month, including an update to the SafeTitan security awareness training and phishing simulation platform to better meet the needs of Managed Service Providers (MSPs) and the release of a new version of the WebTitan DNS-based web filtering solution – Version 5.03, which is now being rolled out for all customers. SpamTitan spam-filter users are also due to get an upgrade, with version 9.01 of the platform due to be released.
The SafeTitan update added a new Auto Campaigns feature for MSPs to better meet the needs of their SMB clients and protect them against increasingly sophisticated phishing threats. While it is vital to have an email security solution such as SpamTitan in place to block email-based threats, workforces also need to be provided with security awareness training to ensure they have the skills to recognize and avoid the full range of cyber threats.
The SafeTitan platform can be used by SMBs for training their workforces and giving them practice at identifying threats and also by MSPs to meet the training needs of their clients. The new Auto Campaigns feature is an automation tool that allows MSPs to reduce the time spent planning and managing security awareness and phishing simulation campaigns for their SMB clients. The AI-driven feature helps MSPs streamline the security training process and improve efficiency while saving time and resources. The Auto Campaigns feature allows MSPs to create an annual set of phishing simulation campaigns for all clients within minutes.
WebTitan is an award-winning web filtering solution that is used by thousands of SMBs, enterprises, and MSPs for controlling access to the Internet and blocking web-based cyber threats. The latest version of the platform includes several new features and bug fixes.
Users now benefit from a new summary report page, the custom block page has a new layout, and several new features have been added. These include support for the customization of the global default policy on the MSP level, which allows the application of a custom default policy on the creation of a customer account. Support has been added for the customization of the default policy on the customer level, it is now possible to inherit the allowed & blocked domains from the customer default policy, and support has been added for allowing/blocking a top-level domain (TLD) on a customer policy and global domains.
SpamTitan is due for an imminent upgrade which will include several new, advanced MSP features. Version 9.01 will have a new history/quarantine feature for MSPs, that will allow them to quickly act on customer emails at the MSP level. Link Lock inheritance has been added at the MSP level to avoid having to drill down to individual domains to make changes, and a new pattern filtering feature has been added which simplifies SpamTitan administration for MSPs and allows them to secure all customers from one place. There is also a simplified mail view, which improves the user experience and makes email analysis simpler.
MSPs also have an Other Products option, which allows them to easily offer other products in the TitanSecure bundle to customers – ArcTitan email archiving, WebTitan web filtering, and SafeTitan security awareness training – and provide a comprehensive, multi-layered security defense system to customers.