Cybercriminals are increasingly offering services that make it easy for anyone to conduct an attack. Skilled malware developers can concentrate on writing their malware and making it available for others to use for a fee, ransomware-as-a-service allows hackers who are skilled at breaching networks to conduct lucrative ransomware attacks without having to develop encryptors and pay for the infrastructure to their support attacks, and phishing-as-a-service provides a platform for conducting attacks to steal credentials and access accounts. These services benefit all parties and allow even more attacks to be conducted.
Phishing campaigns may appear simple, but they require a lot of time and skill to set up. Stephanie Carruthers, who leads an IBM X-Force phishing research project, said it takes her team about 16 hours to craft a phishing email, not including the time it takes to set up all the necessary infrastructure to send the email and steal credentials. Setting up the infrastructure is time-consuming and costly, and many businesses now have multi-factor authentication (MFA) to thwart attacks.
With phishing-as-a-service (PhaaS), anyone who wants to run a phishing campaign can simply pay a subscription and will be provided with all the tools they need to conduct attacks. They do not need to craft the phishing emails, they just need to set a few parameters and provide the email addresses for the campaign. PhaaS makes conducting sophisticated attacks simple and significantly lowers the bar for conducting campaigns.
Take LabHost, for example, a PhaaS platform that recently introduced functionality for targeting financial institutions and banks in North America and Canada. Since this new functionality was included in the first half of 2023, attacks have increased considerably. A monthly subscription is paid, and customers are provided with a turnkey phishing kit, which includes the infrastructure for hosting phishing pages, a content generator for creating phishing emails, and a portal for monitoring the progress of campaigns. Customers can choose to pay $179 per month to target Canadian banks, $249 per month to expand the targets to North America, and $300 a month to also target 70 financial institutions worldwide. Customers are also provided with phishing pages for collecting credentials or a variety of other companies, including music streaming sites, delivery services, and telecommunications companies.
Important to the success of any campaign is the ability to defeat multi-factor authentication. The LabHost phishing kit incorporates LabRat, a phishing tool that allows real-time management of phishing campaigns and allows adversary-in-the-middle attacks where two-factor authentication codes and cookies are obtained in addition to usernames and passwords. That means the additional security processes on the online portals of banks can be circumvented. The platform also allows SMS-based attacks to be conducted.
PhaaS allows unskilled hackers to conduct effective campaigns that they otherwise would not be able to conduct. Further, with the use of AI to craft convincing phishing emails, phishing emails are becoming much harder for humans and security solutions to detect, and even MFA and other security measures can be bypassed.
Defending against attacks is therefore challenging, and there is no single cybersecurity solution that will block all attacks. What is needed is a defense-in-depth approach, with multiple, overlapping layers of protection. Cybersecurity solutions are required to block the phishing emails. SpamTitan is an advanced email security solution with AI and machine learning capabilities for identifying novel phishing threats. SpamTitan blocks known malware through AV controls and unknown malware through sandboxing. The message sandboxing feature uses pattern filtering to identify malware from its behavior, which allows zero-day malware threats to be identified and blocked. Malware sandboxing is vital for email security since so many novel malware threats are now being released. SpamTitan is also capable of identifying even machine-crafted phishing content.
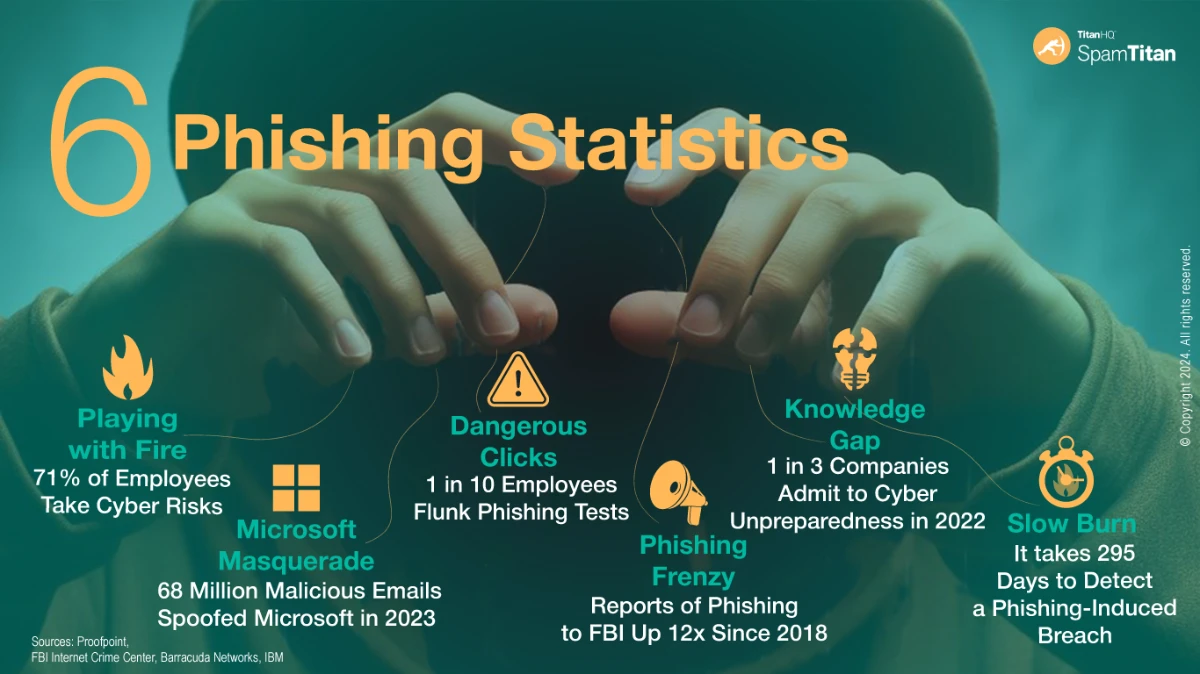
End user training is also vital, as no email security solution will block all email threats without also blocking an unacceptable number of genuine emails. End users should be trained on how to identify, avoid, and report phishing emails. The SafeTitan security awareness training platform makes security awareness training simple, and the constantly updated content allows businesses to respond to changing phishing tactics and conduct phishing simulations on the workforce to reinforce training and identify knowledge gaps.
Given the number of phishing kits that are capable of bypassing multi-factor authentication, simply enabling MFA on accounts is no longer sufficient to protect against unauthorized access. Phishing-resistant multi-factor authentication is required – FIDO/ WebAuthn authentication or Public key infrastructure (PKI)-based MFA – to block adversary-in-the-middle attacks that can be conducted through PhaaS.
If you want to improve your defenses against phishing and other cybercriminal services, give the TitanHQ team a call to discuss your options.
